The United States Secret Service - Federal Reserve Bank of San
... The mission of the National Computer Forensic Institute (NCFI) is to provide state and local law enforcement, prosecutors and judicial officials a national standard of training in electronic crimes investigations, network intrusion response, computer forensics and high tech crime prosecution ...
... The mission of the National Computer Forensic Institute (NCFI) is to provide state and local law enforcement, prosecutors and judicial officials a national standard of training in electronic crimes investigations, network intrusion response, computer forensics and high tech crime prosecution ...
what is ec security?
... information assurance (IA) The protection of information systems against unauthorized access to or modification of information whether in storage, processing, or transit, and against the denial of service to authorized users, including those measures necessary to Copyright © 2010 Pearson Education, ...
... information assurance (IA) The protection of information systems against unauthorized access to or modification of information whether in storage, processing, or transit, and against the denial of service to authorized users, including those measures necessary to Copyright © 2010 Pearson Education, ...
Intrusion Detection Technique by using K
... • Experimental results shows that our proposed new approach do better than BPNN, multiclass SVM and other well-known methods such as decision trees and Columbia model in terms of sensitivity, specificity and in particular detection accuracy. ...
... • Experimental results shows that our proposed new approach do better than BPNN, multiclass SVM and other well-known methods such as decision trees and Columbia model in terms of sensitivity, specificity and in particular detection accuracy. ...
Crypto in data security
... • The science of codes and passwords • Need to prove the identity of the sender and the recipient • The message In the meantime • Should not change the content of the message to make sure ...
... • The science of codes and passwords • Need to prove the identity of the sender and the recipient • The message In the meantime • Should not change the content of the message to make sure ...
What are SNMP Messages
... Management Information Base (MIB) SNMP Agent Network Management System (NMS) Structure of Management Information (SMI) messages between mangers and agent 23.What does the communication model specifies ? The SNMPvI communication model defines specifications of four aspects of SNMP communica ...
... Management Information Base (MIB) SNMP Agent Network Management System (NMS) Structure of Management Information (SMI) messages between mangers and agent 23.What does the communication model specifies ? The SNMPvI communication model defines specifications of four aspects of SNMP communica ...
FTAA Joint Public-Private Sector Committee of Experts
... especially since the discussion centers on the reach and strength of restrictions on the export of encryption technology. Validity of Digital Signatures International business transactions raise questions regarding the conditions and requirements for the recognition, effect and enforceability of dig ...
... especially since the discussion centers on the reach and strength of restrictions on the export of encryption technology. Validity of Digital Signatures International business transactions raise questions regarding the conditions and requirements for the recognition, effect and enforceability of dig ...
john p. carlin - AFCEA International
... Mr. Carlin is an inaugural fellow of Harvard Kennedy School’s Belfer Center for Science and International Affairs’ Homeland Security Project, focused on the unique challenges and choices around protecting the American homeland. He also chairs the Aspen Institute’s Cybersecurity and Technology policy ...
... Mr. Carlin is an inaugural fellow of Harvard Kennedy School’s Belfer Center for Science and International Affairs’ Homeland Security Project, focused on the unique challenges and choices around protecting the American homeland. He also chairs the Aspen Institute’s Cybersecurity and Technology policy ...
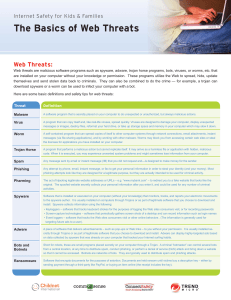
The Basics of Web Threats
... Install products and solutions that protect you whether you’re surfing the Internet or downloading files directly to your computer. Ensure that Web protection software extends beyond email protection to encompass peer-to-peer networks and the entire range of home computing applications, and can prov ...
... Install products and solutions that protect you whether you’re surfing the Internet or downloading files directly to your computer. Ensure that Web protection software extends beyond email protection to encompass peer-to-peer networks and the entire range of home computing applications, and can prov ...
William Stallings, Cryptography and Network Security 5/e
... • Initially the development and deployment of malware required considerable technical skill by software authors • This changed with the development of virus-creation toolkits in the early 1990s and more general attack kits in the 2000s • These toolkits are often known as crimeware • Include a variet ...
... • Initially the development and deployment of malware required considerable technical skill by software authors • This changed with the development of virus-creation toolkits in the early 1990s and more general attack kits in the 2000s • These toolkits are often known as crimeware • Include a variet ...
William Stallings, Cryptography and Network Security 3/e
... • The outside router advertises only the existence of the screened subnet to the Internet; therefore, the internal network is invisible to the Internet. • Similarly, the inside router advertises only the existence of the screened subnet to the internal network; therefore, the systems on the inside n ...
... • The outside router advertises only the existence of the screened subnet to the Internet; therefore, the internal network is invisible to the Internet. • Similarly, the inside router advertises only the existence of the screened subnet to the internal network; therefore, the systems on the inside n ...
Chapter 4
... giving over information, such as the location of files or passwords, the process of hacking is made much easier. • Phishing: • A type of social engineering attack that involves using e-mail in an attempt to trick others into providing sensitive information, such as credit card numbers or passwords. ...
... giving over information, such as the location of files or passwords, the process of hacking is made much easier. • Phishing: • A type of social engineering attack that involves using e-mail in an attempt to trick others into providing sensitive information, such as credit card numbers or passwords. ...
Network Perimeter Defense
... • New processes are being transformed into electronic forms • New vulnerabilities and patches emerge • Event logs must be analyzed • Appropriate actions must be taken • Etc. ...
... • New processes are being transformed into electronic forms • New vulnerabilities and patches emerge • Event logs must be analyzed • Appropriate actions must be taken • Etc. ...
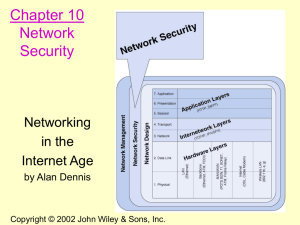
Chapter 1. Introduction to Data Communications
... • Once the threats are identified they are then ranked according to their occurrence. • Figure 10-5 summarizes the most common threats to security. • For example, the average cost to clean up a virus that slips through a security system and infects an average number of computers is $150,000/virus. ...
... • Once the threats are identified they are then ranked according to their occurrence. • Figure 10-5 summarizes the most common threats to security. • For example, the average cost to clean up a virus that slips through a security system and infects an average number of computers is $150,000/virus. ...
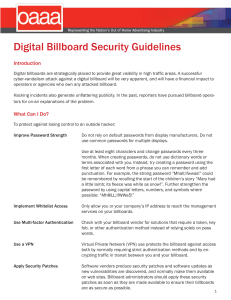
Digital Billboard Security Guidelines
... Virtual Private Network (VPN): A VPN is either a program or a physical device that connects to a remote endpoint to connect two networks securely. The link between both endpoints of a VPN should be encrypted, and the endpoint programs or devices should have a method to positively validate the identi ...
... Virtual Private Network (VPN): A VPN is either a program or a physical device that connects to a remote endpoint to connect two networks securely. The link between both endpoints of a VPN should be encrypted, and the endpoint programs or devices should have a method to positively validate the identi ...
Powerpoint Slides
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
Application Service Provider Security Requirements
... Protected data are any information that the University has deemed to be confidential or sensitive in nature and therefore require additional safeguards in its handling and use. This includes information protected by law such as social security number or credit card numbers. Also included is informat ...
... Protected data are any information that the University has deemed to be confidential or sensitive in nature and therefore require additional safeguards in its handling and use. This includes information protected by law such as social security number or credit card numbers. Also included is informat ...
COEN 152 Computer Forensics - Santa Clara University's
... Details are sensitive to national security. If you get clearance, I can tell you who to ask. Email scams Internet auction fraud Computer is used for intrusion of another system. ...
... Details are sensitive to national security. If you get clearance, I can tell you who to ask. Email scams Internet auction fraud Computer is used for intrusion of another system. ...
www.homepages.dsu.edu
... Simulation of various OS at the Feature increases realism of emulation by deceiving ...
... Simulation of various OS at the Feature increases realism of emulation by deceiving ...
Hardware Building Blocks and Encoding
... A PPP communication begins with a handshake which involves a negotiation between the client and the RAS to settle the transmission and security issues before the transfer of data could begin. This negotiation is done using the Link Control Protocol (LCP). Since PPP does not require authenticatio ...
... A PPP communication begins with a handshake which involves a negotiation between the client and the RAS to settle the transmission and security issues before the transfer of data could begin. This negotiation is done using the Link Control Protocol (LCP). Since PPP does not require authenticatio ...
Network Infrastructure Security
... retrieval of programs and data used by a group of people. LAN software and practices also need to provide for the security of these programs and data. ...
... retrieval of programs and data used by a group of people. LAN software and practices also need to provide for the security of these programs and data. ...
spear-phishing attacks
... been targeted. This kind of real-time defensive response is the most effective way to stop advanced targeted attacks. Organizations can further protect their corporate networks with systems that detect threats across many protocols and throughout the protocol stack, including the network layer, oper ...
... been targeted. This kind of real-time defensive response is the most effective way to stop advanced targeted attacks. Organizations can further protect their corporate networks with systems that detect threats across many protocols and throughout the protocol stack, including the network layer, oper ...
NS2-M3C22S1_-_Computers_and_the_Internet
... • Breaking into financial networks to steal personal information(identify theft) or divert funds for their own gain ...
... • Breaking into financial networks to steal personal information(identify theft) or divert funds for their own gain ...
security in the post-Internet era
... thesis • the Open Internet is history -- “get over it” • destroyed by predictable reaction to recent attacks --but not without significant collateral damage • replaced by the Indeterminate Internet --that most people haven’t and won’t notice • we can and must protect the needs of the few --while sti ...
... thesis • the Open Internet is history -- “get over it” • destroyed by predictable reaction to recent attacks --but not without significant collateral damage • replaced by the Indeterminate Internet --that most people haven’t and won’t notice • we can and must protect the needs of the few --while sti ...
Identify Security Risks and Threats
... Segment the network Encrypt network communications Restrict traffic even when it is segmented Sign network packets Implement IPSec port filters to restrict traffic to servers ...
... Segment the network Encrypt network communications Restrict traffic even when it is segmented Sign network packets Implement IPSec port filters to restrict traffic to servers ...