Mucho Big Data y ¿La Seguridad para cuándo?
... Manager is a good choice for organizations that require high-performance analytics under high-event-rate conditions. Customer references have validated very high scalability and query performance levels for the McAfee Enterprise Security Manager event data store. ...
... Manager is a good choice for organizations that require high-performance analytics under high-event-rate conditions. Customer references have validated very high scalability and query performance levels for the McAfee Enterprise Security Manager event data store. ...
Chapter04
... An open mail relay occurs when a mail server processes mail messages when neither the sender nor the recipient is a local user. The mail server is used to “bounce” e-mail from one outside source to other sources. In this case the mail server becomes an entirely unrelated third party. Spammers use op ...
... An open mail relay occurs when a mail server processes mail messages when neither the sender nor the recipient is a local user. The mail server is used to “bounce” e-mail from one outside source to other sources. In this case the mail server becomes an entirely unrelated third party. Spammers use op ...
Comparison of Routing Metrics for a Static Multi
... greater bandwidth utilization, and 40-60% less latency CS577: Advanced Computer Networks ...
... greater bandwidth utilization, and 40-60% less latency CS577: Advanced Computer Networks ...
ACCESS CONTROL OPTIONS FOR WIRED NETWORKS
... This has led to wired access controls being overshadowed or not configured at all, leading to security gaps in many organizations. And as IT Security experts are well aware, networks are only as strong as their weakest link. As the modern workplace is full of external personnel such as temporary wor ...
... This has led to wired access controls being overshadowed or not configured at all, leading to security gaps in many organizations. And as IT Security experts are well aware, networks are only as strong as their weakest link. As the modern workplace is full of external personnel such as temporary wor ...
Security Risks
... – Network host software application • Intermediary between external and internal networks • Screens all incoming and outgoing traffic ...
... – Network host software application • Intermediary between external and internal networks • Screens all incoming and outgoing traffic ...
Its_time_to_go_hunting_-_IOC_vs_IOA_
... • In 2015, these standards have been transitioned to the Organization for the Advancement of Structured Information Standards (OASIS), which has the role to develop them and promote their adoption, enabling cyber threat intelligence to be analyzed and shared among partners and communities worldwide. ...
... • In 2015, these standards have been transitioned to the Organization for the Advancement of Structured Information Standards (OASIS), which has the role to develop them and promote their adoption, enabling cyber threat intelligence to be analyzed and shared among partners and communities worldwide. ...
Orange Earth - Central Ohio ISSA
... optionally supported when Hadoop services are accessed through RPC and HTTP, while the actual HDFS blocks are transferred unencrypted. Hadoop assumes network involved in HDFS block transfer is secure and not publicly accessible for sniffing, which is not a bad assumption for private enterprise ...
... optionally supported when Hadoop services are accessed through RPC and HTTP, while the actual HDFS blocks are transferred unencrypted. Hadoop assumes network involved in HDFS block transfer is secure and not publicly accessible for sniffing, which is not a bad assumption for private enterprise ...
High Assurance MLS File Service - Center for Computer Systems
... release packets to interfaces with sensitivity matching their sealed labels. The seal is a Message Authentication Code (MAC) created by using the Cipher-BlockChaining (CBC) mode of a symmetric encryption operation. Packet contents and the canonical representation of the source network sensitivity le ...
... release packets to interfaces with sensitivity matching their sealed labels. The seal is a Message Authentication Code (MAC) created by using the Cipher-BlockChaining (CBC) mode of a symmetric encryption operation. Packet contents and the canonical representation of the source network sensitivity le ...
Introduction - Computer Science
... Model for Network Access Security Using this model requires us to implement: 1. Authentication select appropriate gatekeeper functions to identify users ...
... Model for Network Access Security Using this model requires us to implement: 1. Authentication select appropriate gatekeeper functions to identify users ...
Cyber Solutions for NEI 08-09 Whitepaper 119 KB
... Cyber Asset Protection (CAP) Software Update Subscription and SecurityST Appliance This solution set provides multiple capabilities to support cyber security best practices. Functionality includes centralized patch management, anti-virus/host intrusion detection updates, centralized account manageme ...
... Cyber Asset Protection (CAP) Software Update Subscription and SecurityST Appliance This solution set provides multiple capabilities to support cyber security best practices. Functionality includes centralized patch management, anti-virus/host intrusion detection updates, centralized account manageme ...
Secure Deduplication with Efficient and Reliable
... We propose Dekey, a new construction in which users do not need to manage any keys on their own but instead securely distribute the convergent key shares across multiple servers. Dekey using the Ramp secret sharing scheme and demonstrate that Dekey incurs limited overhead in realistic environments w ...
... We propose Dekey, a new construction in which users do not need to manage any keys on their own but instead securely distribute the convergent key shares across multiple servers. Dekey using the Ramp secret sharing scheme and demonstrate that Dekey incurs limited overhead in realistic environments w ...
Virtualized Broadband Network Gateway
... IP edge routing features, and can be extended with additional service options as needed: • Carrier-grade Network Address Translation (CG-NAT) to manage the transition to IPv6 • Application Assurance, for powerful application QoS, analytics and security policy enforcement • Advanced features such ...
... IP edge routing features, and can be extended with additional service options as needed: • Carrier-grade Network Address Translation (CG-NAT) to manage the transition to IPv6 • Application Assurance, for powerful application QoS, analytics and security policy enforcement • Advanced features such ...
An Immucor Technical Support Solution
... complete patient confidentiality maintained at all times ...
... complete patient confidentiality maintained at all times ...
How does it get written up?
... • Vulnerabilities for which there are exploits in active circulation ...
... • Vulnerabilities for which there are exploits in active circulation ...
DDoS Attacks: What You Can`t See Can Hurt You Dave Larson
... The Attackers are Getting Smarter Researchers are finding an uptick in the number of new techniques Attackers defeating traditional protection (Firewall, ACL, Blackhole) Attackers are developing new methods of bypassing defenses ...
... The Attackers are Getting Smarter Researchers are finding an uptick in the number of new techniques Attackers defeating traditional protection (Firewall, ACL, Blackhole) Attackers are developing new methods of bypassing defenses ...
Manage security settings with Action Center
... Real-time protection. Windows Defender alerts you when spyware attempts to install itself or to run on your computer. It also alerts you when programs attempt to change important Windows settings. ...
... Real-time protection. Windows Defender alerts you when spyware attempts to install itself or to run on your computer. It also alerts you when programs attempt to change important Windows settings. ...
Final bits of OS - Department of Computer Science
... • Result: a transport allowing hosts to send IP event notification messages to syslog servers – provides a very general message format – allowing processes and applications to use suitable conventions for ...
... • Result: a transport allowing hosts to send IP event notification messages to syslog servers – provides a very general message format – allowing processes and applications to use suitable conventions for ...
BIO-ELECTRO-INFO TECHNOLOGIES TO COMBAT TERRORISM
... when the U.S. would use cyber attacks, who would authorize it, what constitutes legitimate targets, and what kinds of attacks -- Denial of Service, hacking, worms -- could be used. ...
... when the U.S. would use cyber attacks, who would authorize it, what constitutes legitimate targets, and what kinds of attacks -- Denial of Service, hacking, worms -- could be used. ...
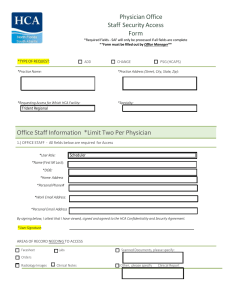
Physician Office Staff Security Access Form Office Staff Information
... 18. I understand that I will be assigned a unique identifier (e.g., 3-4 User ID) to track my access and use of Confidential Information and that the identifier is associated with my personal data provided as part of the initial and/or periodic credentialing and/or employment verification processes. ...
... 18. I understand that I will be assigned a unique identifier (e.g., 3-4 User ID) to track my access and use of Confidential Information and that the identifier is associated with my personal data provided as part of the initial and/or periodic credentialing and/or employment verification processes. ...
Discovering Computers 2006
... Chapter 11 Objectives Describe the types of computer security risks ...
... Chapter 11 Objectives Describe the types of computer security risks ...
Introduction to Information Security Chapter N
... Deliberate Acts of Theft Illegal taking of another’s physical, electronic, or intellectual property Physical theft is controlled relatively easily Electronic theft is more complex problem; evidence of crime not readily apparent ...
... Deliberate Acts of Theft Illegal taking of another’s physical, electronic, or intellectual property Physical theft is controlled relatively easily Electronic theft is more complex problem; evidence of crime not readily apparent ...
Unix Network Security - LSU Computer Science
... internet grows rapidly, network services gain more importance in terms of operational and business requirements. This makes security concept one of the key points for the quality and availability of the running service. Basic idea behind secure environments is to decrease the probability for being c ...
... internet grows rapidly, network services gain more importance in terms of operational and business requirements. This makes security concept one of the key points for the quality and availability of the running service. Basic idea behind secure environments is to decrease the probability for being c ...
10 March 2009 - Computer Science
... algorithm used and then together with the recovered session key to decrypt to plain text. Of course the algorithm used for encryption is dependant on the protocol used and the algorithms that were negotiated between client and server. Investigate sensible means to store symmetric keys for later use. ...
... algorithm used and then together with the recovered session key to decrypt to plain text. Of course the algorithm used for encryption is dependant on the protocol used and the algorithms that were negotiated between client and server. Investigate sensible means to store symmetric keys for later use. ...
Best Practices for Better Security
... provides auditing and reporting so that you can control user access to network resources. The VPN provides built-in encryption via IP Security (IPSec) or Secure Sockets Layer (SSL) technology standards. For additional protection, you may consider encrypting data on laptops in order to prevent data l ...
... provides auditing and reporting so that you can control user access to network resources. The VPN provides built-in encryption via IP Security (IPSec) or Secure Sockets Layer (SSL) technology standards. For additional protection, you may consider encrypting data on laptops in order to prevent data l ...