* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Zero day timebomb infographic3
Security-focused operating system wikipedia , lookup
Outlook.com wikipedia , lookup
Next-Generation Secure Computing Base wikipedia , lookup
Microsoft Security Essentials wikipedia , lookup
Operation Payback wikipedia , lookup
Mobile security wikipedia , lookup
Cross-site scripting wikipedia , lookup
Cyberwarfare wikipedia , lookup
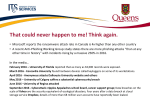
Cyber-security regulation wikipedia , lookup
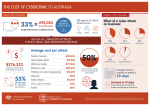
Infographic THE ZERO DAY TIMEBOMB 97% Pie chart 22 DAYS of IT pros rely on AV to develop exploit 1/3 of exploits 50% developed in one week 7 attacks in 2016 linked to Flash Days THE RISING THREAT “ An ever-increasing amount of new code and a robust underworld economy will be stoking the market in 2017 for zero-day vulnerabilities, John P. Mello, Jr - Cybersecurity Ventures 400 Newly reported One-per-day 350 ” zero-day attacks 300 250 200 2021 150 100 2015 One-per-week 50 0 $10,000 78% of C-levels black market value of Word or Excel RCE flaw say cyber attacks will increase in year ahead 0110010100101001011010111001010111101010110110010100110 1010110100011010001010100011101010011100010100100100 1100101001010010110101110010101111010101101100101001101 01011110001101000101010001110101001110001010010010011 0010100101001011010111001010111101010110110010100110101 01111000110100010101000111010100111000101001001001101 0101001010010110101110010101111010101101100101001101010 1111000110100010101000111010100111000101001001000110 0101001010010110101110010101111010101101100101001101010 11110001101000101010001110101001110001010010010011001 111 billion new lines of software code every year MICROSOFT VULNERABILITIES IN 2016 530 overall “ 395 Windows 10 The rise of... advanced, yet easy-to-use malware means we will begin to see significant attacks from a much broader range of attackers, Tom Corn, Senior Vice President of security products at VMware. ” BEING PROACTIVE PAYS 94% 100% of Critical Microsoft vulnerabilities in 2016 of IE and Edge vulnerabilities in 2016 would be mitigated by removing admin rights. “ “ Target threats are easily bypassing traditional, signature-based security solutions... the protection strategy must be one that further strengthens prevention capabilities, ” Neil MacDonald, Gartner: Effective tactics to protect midmarket enterprises from advanced threats. Very often, the endpoint device was the initial point of compromise that allowed for lateral movement into the network, creating additional damage, Dr Eric Cole, Cyber security expert and SANS fellow. ” TOP 6 CRITICAL SECURITY CONTROLS Inventory of Authorized and Unauthorized Devices Inventory of Authorized and Unauthorized Software Secure Configurations for Hardware and Software Continuous Vulnerability Assessment and Remediation Controlled Use of Administrative Privileges Maintenance, Monitoring and Analysis of Audit Logs HOW DEFENDPOINT CAN STOP ZERO DAY ATTACKS £ Phishing email Fake invoice isolated Payload isolated & blocked Data protected WE STOP CYBER ATTACKS A powerful multi-layered prevention engine that stops cyber attacks at the endpoint List of sources http://www.rand.org/pubs/research_reports/RR1751.html http://www.computing.co.uk/ctg/news/2452094/ninety-seven-per-cent-of-it-professionals-think-standard-antivirus-softwarewill-stop-zero-day-attacks http://cybersecurityventures.com/zero-day-vulnerabilities-attacks-exploits-report-2017/ https://www.mcafee.com/ca/resources/reports/rp-quarterly-threats-dec-2016.pdf https://go.kaspersky.com/rs/802-IJN-240/images/Financial_Survey_Report_eng_final.pdf https://www.vmware.com/radius/five-things-to-come-for-security/ http://searchsecurity.techtarget.com/tip/Six-ways-to-improve-endpoint-device-security http://www.baesystems.com/en/cybersecurity/article/new-research-reveals-business-disconnect-in-defending-againstcyber-attacks https://www.avecto.com/resources/reports/microsoft-vulnerabilities-report-2016/ Americas / UK / Germany avecto.com / [email protected]