Introduction to Database Systems
... either all succeed, or all fail • E.g. Transfer $100 BEGIN TRANSACTION; UPDATE Accounts SET amount = amount - 100 WHERE number = 4662 UPDATE Accounts SET amount = amount + 100 WHERE number = 7199 COMMIT ...
... either all succeed, or all fail • E.g. Transfer $100 BEGIN TRANSACTION; UPDATE Accounts SET amount = amount - 100 WHERE number = 4662 UPDATE Accounts SET amount = amount + 100 WHERE number = 7199 COMMIT ...
Transactions and Locks PowerPoint
... • A deadlock is a situation when two (or more) users, each having a lock on one piece of data, attempt to acquire a lock on the other’s piece. • Unless one of the user processes is terminated, each user would wait indefinitely for the other to release the lock. • SQL Server detects deadlocks and ter ...
... • A deadlock is a situation when two (or more) users, each having a lock on one piece of data, attempt to acquire a lock on the other’s piece. • Unless one of the user processes is terminated, each user would wait indefinitely for the other to release the lock. • SQL Server detects deadlocks and ter ...
A transaction
... In the following examples, think of a transaction as meaning a procedure. A transaction commits when it ends successfully. A transaction rolls back when it aborts. ...
... In the following examples, think of a transaction as meaning a procedure. A transaction commits when it ends successfully. A transaction rolls back when it aborts. ...
ObjectRank: A System for Authority-based Search
... is that the distribution of ObjectRank values is more skewed when the size of the base set increases, because the top objects tend to receive more references. For example, consider two results for the query “XML Index” shown in Figure 4. Result (b) corresponds to the situation described above. It no ...
... is that the distribution of ObjectRank values is more skewed when the size of the base set increases, because the top objects tend to receive more references. For example, consider two results for the query “XML Index” shown in Figure 4. Result (b) corresponds to the situation described above. It no ...
here
... levels of control using data management rules based on instantaneous correctness, and then integrated all results into a complete differential control algorithm. In particular, the following tasks pertaining to the new methods of differential concurrency control have been undertaken in this research ...
... levels of control using data management rules based on instantaneous correctness, and then integrated all results into a complete differential control algorithm. In particular, the following tasks pertaining to the new methods of differential concurrency control have been undertaken in this research ...
Click to Unit 4 of DDB
... partitioning. If the network is partitioned, the sites in each partition may continue to operate. In this case, executing transactions that access data stored in multiple partitions becomes a major issue. Network partitions point to a unique aspect of failures in distributed computer systems. In cen ...
... partitioning. If the network is partitioned, the sites in each partition may continue to operate. In this case, executing transactions that access data stored in multiple partitions becomes a major issue. Network partitions point to a unique aspect of failures in distributed computer systems. In cen ...
BLS 2215 DATABASE MANAGEMENT SYSTEMS
... manipulation languages; programming in a database environment: database security, integrity, recovery, and concurrence; file organization: sequential, random, indexed sequential, hierarchical, heap, inverted; Database administration; Distributed database systems. Assessment method - Coursework and E ...
... manipulation languages; programming in a database environment: database security, integrity, recovery, and concurrence; file organization: sequential, random, indexed sequential, hierarchical, heap, inverted; Database administration; Distributed database systems. Assessment method - Coursework and E ...
HAT, not CAP: Towards Highly Available Transactions
... is not achievable with high availability [36]. However, most ACID and “NewSQL” databases provide weaker forms of isolation—usually by default, and often as the only options offered (§2). Databases have provided these weak guarantees for decades [43], suggesting that they are useful to application pr ...
... is not achievable with high availability [36]. However, most ACID and “NewSQL” databases provide weaker forms of isolation—usually by default, and often as the only options offered (§2). Databases have provided these weak guarantees for decades [43], suggesting that they are useful to application pr ...
A transaction
... • This causes the system to “abort” the transaction – The database returns to the state without any of the previous changes made by activity of the transaction ...
... • This causes the system to “abort” the transaction – The database returns to the state without any of the previous changes made by activity of the transaction ...
Class 3
... Result: Database state no longer corresponds to real-world state, integrity constraint violated. ...
... Result: Database state no longer corresponds to real-world state, integrity constraint violated. ...
LN5 - WSU EECS
... NoSQL while retaining the support for SQL queries and/or ACID, or to improve performance for appropriate workloads.” -- 451 Group ...
... NoSQL while retaining the support for SQL queries and/or ACID, or to improve performance for appropriate workloads.” -- 451 Group ...
oNTRAK - Turner Scale, Inc.
... oNTRAK™ OnTrak provides simple ticketing automation to enterprises that currently have manual ticketing systems. OnTrak is intuitive, reliable, compatible with the most popular operating systems, adaptable to a wide variety of industries, configurable and does not require an in-house IT staff to kee ...
... oNTRAK™ OnTrak provides simple ticketing automation to enterprises that currently have manual ticketing systems. OnTrak is intuitive, reliable, compatible with the most popular operating systems, adaptable to a wide variety of industries, configurable and does not require an in-house IT staff to kee ...
Document
... transaction has completed (i.e., the transfer of the $50 has taken place), the updates to the database by the transaction must persist despite failures. ...
... transaction has completed (i.e., the transfer of the $50 has taken place), the updates to the database by the transaction must persist despite failures. ...
Slide 1
... database during the lifecycle of business application development. Embedded database can lead to cost reduction in software development & software maintenance, with financial benefits. ...
... database during the lifecycle of business application development. Embedded database can lead to cost reduction in software development & software maintenance, with financial benefits. ...
Transaction processing systems
... database ,i.e. those changes must not be lost because of any failure. (It is the responsibility of recovery) IS 533 - Transactions ...
... database ,i.e. those changes must not be lost because of any failure. (It is the responsibility of recovery) IS 533 - Transactions ...
Document
... Consistency. Execution of a transaction in isolation preserves the consistency of the database. Isolation. Although multiple transactions may execute concurrently, each transaction must be unaware of other concurrently executing transactions. Intermediate transaction results must be hidden from ...
... Consistency. Execution of a transaction in isolation preserves the consistency of the database. Isolation. Although multiple transactions may execute concurrently, each transaction must be unaware of other concurrently executing transactions. Intermediate transaction results must be hidden from ...
4D2a – Data Engineering
... Information systems management course runs over the entire 1st Semester. In each week, there are three one-hour lectures. However, tutorials are scheduled in place of a lecture every two weeks. Alongside the lectures, a full online course on the application of database language SQL is delivered. Thi ...
... Information systems management course runs over the entire 1st Semester. In each week, there are three one-hour lectures. However, tutorials are scheduled in place of a lecture every two weeks. Alongside the lectures, a full online course on the application of database language SQL is delivered. Thi ...
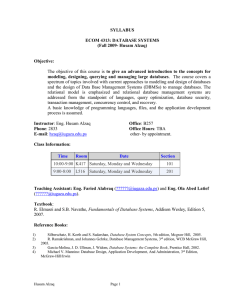
Syllabus
... prohibited. If you arrive at least 5 minutes late, you will be considered absent even if you attend the lecture. Please come to the lecture on time. Respect office hours as listed above. Do not come to the office outside office hours. If the office hours conflict with your schedule, you can arrange ...
... prohibited. If you arrive at least 5 minutes late, you will be considered absent even if you attend the lecture. Please come to the lecture on time. Respect office hours as listed above. Do not come to the office outside office hours. If the office hours conflict with your schedule, you can arrange ...
Sullbus
... aspect of a database system, create some innovative application, or investigate or evaluate a database management system or tool. This is to give opportunity to the students who want to try some hands on database experience that this course does not otherwise offer. The instructor is completely open ...
... aspect of a database system, create some innovative application, or investigate or evaluate a database management system or tool. This is to give opportunity to the students who want to try some hands on database experience that this course does not otherwise offer. The instructor is completely open ...
Indexes (AKA Indices) - Prof. Yitz Rosenthal
... • A rollback command forces whatever was done in the transaction so far to become "undone". • Similar to the "undo" command on your word processor. • This is used both with "stored procedures" and application programs that interact with the database. When the program encounters a condition after it ...
... • A rollback command forces whatever was done in the transaction so far to become "undone". • Similar to the "undo" command on your word processor. • This is used both with "stored procedures" and application programs that interact with the database. When the program encounters a condition after it ...