Computer Security Presentation
... offices. Drivers and applicants endured sometimes long waits at the newly overhauled New Jersey Motor Vehicle Commission's (MVC) offices on three days last week after a hard charging computer virus struck its statewide system. A survey conducted by Internet service provider America Online Inc. found ...
... offices. Drivers and applicants endured sometimes long waits at the newly overhauled New Jersey Motor Vehicle Commission's (MVC) offices on three days last week after a hard charging computer virus struck its statewide system. A survey conducted by Internet service provider America Online Inc. found ...
Tenable Malware Detection
... Audit Effectiveness of Deployed Security Products The ability to verify the effectiveness of your existing security solutions, including AV and AM defenses, is becoming increasingly important because of the two trends described above. Tenable SCCV has the capability to audit hosts and servers for no ...
... Audit Effectiveness of Deployed Security Products The ability to verify the effectiveness of your existing security solutions, including AV and AM defenses, is becoming increasingly important because of the two trends described above. Tenable SCCV has the capability to audit hosts and servers for no ...
How to Detect Zero-Day Malware And Limit Its Impact
... There has been a “seismic shift” in how malware is developed and distributed, says Andrew Brandt, director of threat research at Solera Networks. Malware developers are increasingly crafting one-time-use malware, so by the time an antivirus vendor has released a signature to detect the malware sampl ...
... There has been a “seismic shift” in how malware is developed and distributed, says Andrew Brandt, director of threat research at Solera Networks. Malware developers are increasingly crafting one-time-use malware, so by the time an antivirus vendor has released a signature to detect the malware sampl ...
Acceptable Use Policy (AUP)
... With the use of electronic networks, including both the Internet and the Intranet, the Council Grove Middle School is expanding learning access for students, staff, parents and the entire Council Grove community. With this opportunity comes the responsibility for appropriate use. ...
... With the use of electronic networks, including both the Internet and the Intranet, the Council Grove Middle School is expanding learning access for students, staff, parents and the entire Council Grove community. With this opportunity comes the responsibility for appropriate use. ...
PowerPoint 簡報
... know of holes within systems and the reasons for such holes. Hackers constantly seek further knowledge, freely share what they have discovered, and never, ever intentionally damage data. ...
... know of holes within systems and the reasons for such holes. Hackers constantly seek further knowledge, freely share what they have discovered, and never, ever intentionally damage data. ...
Security Risks
... damaging computer systems. It locates the virus program code and then quarantines (locks it away from the rest of the system) and deletes it. There are many anti-virus programs available but they all operate in similar ways. Virus scans are performed as often as the user requires (hourly, daily week ...
... damaging computer systems. It locates the virus program code and then quarantines (locks it away from the rest of the system) and deletes it. There are many anti-virus programs available but they all operate in similar ways. Virus scans are performed as often as the user requires (hourly, daily week ...
Chapter 2: Attackers and Their Attacks
... dormant until triggered by a specific event, for example: ...
... dormant until triggered by a specific event, for example: ...
Viruses - Bozonline
... Computer Viruses, Worms, and Trojan Horses What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
... Computer Viruses, Worms, and Trojan Horses What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
Session2
... Malware, short for malicious software, is a software designed to harm or secretly access a computer system without the owner's informed consent. ...
... Malware, short for malicious software, is a software designed to harm or secretly access a computer system without the owner's informed consent. ...
networkworld - Sift Security
... There's a powerful new generation of security tools coming to market designed to help security operations (SecOps) teams find and react to threats much quicker than before. The best of these tools also enable security analysts to proactively hunt for threats that might be present in their enterprise ...
... There's a powerful new generation of security tools coming to market designed to help security operations (SecOps) teams find and react to threats much quicker than before. The best of these tools also enable security analysts to proactively hunt for threats that might be present in their enterprise ...
Chapter 13
... to spy upon someone else’s computer • Takes advantage of loopholes in the Windows security systems and allows a stranger to witness and record another person’s every mouse click and keystroke on the monitor as it occurs. • For the spy, it looks as if a ghost is moving the mouse and typing in e-mail ...
... to spy upon someone else’s computer • Takes advantage of loopholes in the Windows security systems and allows a stranger to witness and record another person’s every mouse click and keystroke on the monitor as it occurs. • For the spy, it looks as if a ghost is moving the mouse and typing in e-mail ...
Unit 1- Computers and Operating Systems
... ■ 1981 IBM PC released – Bill Gates worked for IBM – Used DOS ...
... ■ 1981 IBM PC released – Bill Gates worked for IBM – Used DOS ...
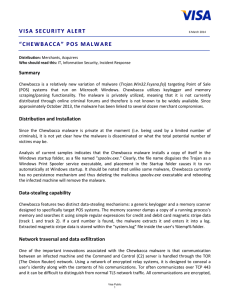
“CHEWBACCA” POS Malware
... Upon execution Chewbacca performs an external IP lookup by doing a GET request to ekiga[.]net, a legitimate service that replies with the IP address the request is sent from. The GET request is constructed with a non-standard User-Agent. Tor v0.2.3.25 is dropped as "tor.exe" to the user's Temp and r ...
... Upon execution Chewbacca performs an external IP lookup by doing a GET request to ekiga[.]net, a legitimate service that replies with the IP address the request is sent from. The GET request is constructed with a non-standard User-Agent. Tor v0.2.3.25 is dropped as "tor.exe" to the user's Temp and r ...
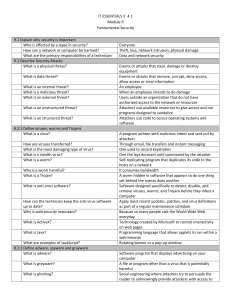
IT ESSENTIALS V. 4.1 Module 9 Fundamental Security 9.1 Explain
... Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instant messaging One used to record keystrokes One ...
... Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instant messaging One used to record keystrokes One ...
Emerging Threats to Business Security
... Spyware remains a growing concern for businesses. In light of recently introduced data protection legislation in Europe and the United States, the danger to businesses in terms of liability for data theft/loss will remain high for the foreseeable future. The various versions of "Storm Worm" still pr ...
... Spyware remains a growing concern for businesses. In light of recently introduced data protection legislation in Europe and the United States, the danger to businesses in terms of liability for data theft/loss will remain high for the foreseeable future. The various versions of "Storm Worm" still pr ...
TNS03%20Introduction%20to%20Network%20Security
... Appears to be benign (良好) software but secretly downloading a virus or other malware. For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
... Appears to be benign (良好) software but secretly downloading a virus or other malware. For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
Victims who were Hacked PowerPoint Presentation
... What Is An Anti-Virus Software? A software designed to be used on your computer to find, treat, remove and keep malwares away. It will keep all your computer data safe! ...
... What Is An Anti-Virus Software? A software designed to be used on your computer to find, treat, remove and keep malwares away. It will keep all your computer data safe! ...
Medical_Informatics_-_Computer_Networks
... communication). DoS (Denial of service attack; overloading a network by flooding it with useless traffic. Two types, this normal type and DDoS (Distributed DoS) where several computers flood a system with packets in a co-ordinated ...
... communication). DoS (Denial of service attack; overloading a network by flooding it with useless traffic. Two types, this normal type and DDoS (Distributed DoS) where several computers flood a system with packets in a co-ordinated ...
module 2 network security unit 1
... Data encryption and identity authentication are especially important to securing a VPN. Any open network connection is a vulnerability hackers can exploit to sneak onto your network. Moreover, data is particularly vulnerable while it is traveling over the Internet. Review the documentation for your ...
... Data encryption and identity authentication are especially important to securing a VPN. Any open network connection is a vulnerability hackers can exploit to sneak onto your network. Moreover, data is particularly vulnerable while it is traveling over the Internet. Review the documentation for your ...
Current Issues in Maintaining a Secure System
... Malware Prevention • Many companies are blocking employees from nonbusiness related web browsing with technology rather than policy. – General Electric bars instant messaging, file sharing programs, and access to personal email. – JP Morgan Chase blocks any traffic it can’t trace and analyze includ ...
... Malware Prevention • Many companies are blocking employees from nonbusiness related web browsing with technology rather than policy. – General Electric bars instant messaging, file sharing programs, and access to personal email. – JP Morgan Chase blocks any traffic it can’t trace and analyze includ ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.