Why we need IT security - Department of Computer Science and
... Countermeasures – Firewall • A firewall can be software (e.g. Windows Firewall), hardware or a combination of hardware and software • A firewall is used to: – Inspect all inbound and outbound internet messages (Uses packet filtering to distinguish between legitimate messages that are responses to v ...
... Countermeasures – Firewall • A firewall can be software (e.g. Windows Firewall), hardware or a combination of hardware and software • A firewall is used to: – Inspect all inbound and outbound internet messages (Uses packet filtering to distinguish between legitimate messages that are responses to v ...
SE 4C03 Winter 2004
... design process could be created, counter measures are still available for your disposal. The trivial defence to attacks is simply having your network connection unplugged. When there is absolutely no connection whatsoever, regardless how skilful an attacker is, he or she can not penetrate this barri ...
... design process could be created, counter measures are still available for your disposal. The trivial defence to attacks is simply having your network connection unplugged. When there is absolutely no connection whatsoever, regardless how skilful an attacker is, he or she can not penetrate this barri ...
Security strategy
... documents and computer files. Organisations have a duty to protect the privacy of data which they hold about members of the public and their staff, and to process this data only in the manner for which it was intended. ...
... documents and computer files. Organisations have a duty to protect the privacy of data which they hold about members of the public and their staff, and to process this data only in the manner for which it was intended. ...
IIDPS: An Internal Intrusion Detection and
... Over the past several years, the Internet environment has become more complex and untrusted. Enterprise networked systems are inevitably exposed to the increasing threats posed by hackers as well as malicious users internal to a network. IDS technology is one of the important tools used now-a-days, ...
... Over the past several years, the Internet environment has become more complex and untrusted. Enterprise networked systems are inevitably exposed to the increasing threats posed by hackers as well as malicious users internal to a network. IDS technology is one of the important tools used now-a-days, ...
Taking Control of Advanced Threats
... firewalls ▸IPS component rated “most important” for securing data ...
... firewalls ▸IPS component rated “most important” for securing data ...
Basic Marketing, 16e
... Worm – virus that spreads itself from computer to computer usually via e-mail Denial-of-service (DoS) attack – floods a Web site with so many requests for service that it slows down or crashes ...
... Worm – virus that spreads itself from computer to computer usually via e-mail Denial-of-service (DoS) attack – floods a Web site with so many requests for service that it slows down or crashes ...
Computer Ethics
... program that can copy itself and infect a computer. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. ...
... program that can copy itself and infect a computer. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. ...
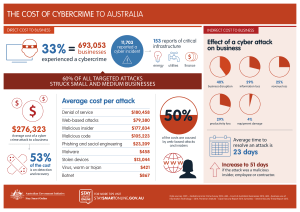
the cost of cybercrime to australia $276323
... Data sources: PWC – Global Economic Crime Survey 2014; ABS – Count of Australian Businesses 2014; ABS – Business use of Information Technology – 2014; Ponemon Institute – Cyber Security Report 2014; Symantec – Internet Security Threat Report 2015. ...
... Data sources: PWC – Global Economic Crime Survey 2014; ABS – Count of Australian Businesses 2014; ABS – Business use of Information Technology – 2014; Ponemon Institute – Cyber Security Report 2014; Symantec – Internet Security Threat Report 2015. ...
OnLinePrivacy - Cal State LA
... Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves by infecting other programs on your computer. ...
... Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves by infecting other programs on your computer. ...
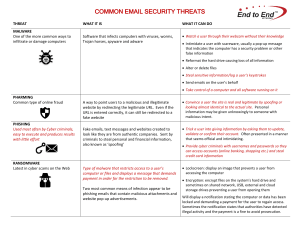
COMMON EMAIL SECURITY THREATS
... computer or files and displays a message that demands payment in order for the restriction to be removed. ...
... computer or files and displays a message that demands payment in order for the restriction to be removed. ...
security_6
... cyber-criminals who use email, popup messages or an imitation or copy of an existing legitimate webpage to trick users into providing sensitive personal information such as credit card numbers, bank account numbers, and passwords. ...
... cyber-criminals who use email, popup messages or an imitation or copy of an existing legitimate webpage to trick users into providing sensitive personal information such as credit card numbers, bank account numbers, and passwords. ...
Module F - Columbus State University
... without the announcement of yet another serious overflowtriggered vulnerability. Overflows occur when a program tries to store more data than the allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. ...
... without the announcement of yet another serious overflowtriggered vulnerability. Overflows occur when a program tries to store more data than the allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. ...
Computer Components
... Understanding Memory Types of memory include the following: 1. Random access memory (RAM) – temporarily holds programs and data while the computer is on and allows the computer to access that information randomly. Consists of chips on cards that plug into the ...
... Understanding Memory Types of memory include the following: 1. Random access memory (RAM) – temporarily holds programs and data while the computer is on and allows the computer to access that information randomly. Consists of chips on cards that plug into the ...
SYSTEM SOFTWARE
... The provision of mechanisms for deadlock handling (deadlock is a situation in which each process in a set of processes is waiting for an event that only another process in the set can cause. since all the process are waiting, the system enters a deadlocked condition ...
... The provision of mechanisms for deadlock handling (deadlock is a situation in which each process in a set of processes is waiting for an event that only another process in the set can cause. since all the process are waiting, the system enters a deadlocked condition ...
Chapter 5 Protecting Information Resources
... Programming routine built into a system by its designer or programmer Enables the designer or programmer to bypass system security and sneak back into the system later to access programs or files System users aren’t aware a backdoor has ...
... Programming routine built into a system by its designer or programmer Enables the designer or programmer to bypass system security and sneak back into the system later to access programs or files System users aren’t aware a backdoor has ...
- Scholarly Commons
... toxicology. Instead of poisons, we have malware and hacker tools. Instead of the Marsh test and its modern replacement, gas chromatography, we have antivirus scanners and lists of hash values. But in many ways the goal is still the same. The forensic examiner scans for that which does not belong. Su ...
... toxicology. Instead of poisons, we have malware and hacker tools. Instead of the Marsh test and its modern replacement, gas chromatography, we have antivirus scanners and lists of hash values. But in many ways the goal is still the same. The forensic examiner scans for that which does not belong. Su ...
Breaking Trust On The Internet
... • A computer virus is a small software program that spreads from one computer to another and interferes with computer operation. • A computer virus might corrupt or delete data on a computer, use an email program to spread the virus to other computers, or even delete everything on the hard disk. ...
... • A computer virus is a small software program that spreads from one computer to another and interferes with computer operation. • A computer virus might corrupt or delete data on a computer, use an email program to spread the virus to other computers, or even delete everything on the hard disk. ...
BitDefenDer Active virus control:
... Compounding the problem is the fact that both malware and the mechanisms used to deliver it have become increasingly sophisticated. Trusted websites can be compromised and used to launch complex script-based attacks that cycle through multiple exploits, advanced packaging methods ...
... Compounding the problem is the fact that both malware and the mechanisms used to deliver it have become increasingly sophisticated. Trusted websites can be compromised and used to launch complex script-based attacks that cycle through multiple exploits, advanced packaging methods ...
Information Systems and Networks
... access, abuse, or fraud is not limited to a single location but can occur at any access point in the network Security refers to the policies, procedures, and technical measures used to prevent unauthorized access, alteration, theft, or physical damage to information systems. Controls are methods, po ...
... access, abuse, or fraud is not limited to a single location but can occur at any access point in the network Security refers to the policies, procedures, and technical measures used to prevent unauthorized access, alteration, theft, or physical damage to information systems. Controls are methods, po ...
Social Studies
... Identify safe and responsible ways to use technology systems, the Internet including but not limited to social/professional networking, communication tools, and applications. Identify safe and responsible practices of social networking and electronic communication. Understand the meaning of legal ve ...
... Identify safe and responsible ways to use technology systems, the Internet including but not limited to social/professional networking, communication tools, and applications. Identify safe and responsible practices of social networking and electronic communication. Understand the meaning of legal ve ...
Research Scientist – Prague, Czech Republic Cisco Systems
... Cisco Systems, Security Cloud Operations (SCO) develops innovative products in the domain of Network Behavior Analysis (NBA) in order to fight against modern sophisticated attacks in today's cyberspace which include Advanced Persistent Threats (APT), exploit kits, zero-day attacks, polymorphic malwa ...
... Cisco Systems, Security Cloud Operations (SCO) develops innovative products in the domain of Network Behavior Analysis (NBA) in order to fight against modern sophisticated attacks in today's cyberspace which include Advanced Persistent Threats (APT), exploit kits, zero-day attacks, polymorphic malwa ...
PPT - pantherFILE
... • Early and good worms: intend to create useful programs that would utilize any otherwise idle machines. • Worms infiltrate computers usually by exploiting holes in the security of networked systems. • Worms usually attack programs that are already running. – The attack might result in creation of n ...
... • Early and good worms: intend to create useful programs that would utilize any otherwise idle machines. • Worms infiltrate computers usually by exploiting holes in the security of networked systems. • Worms usually attack programs that are already running. – The attack might result in creation of n ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.