Advanced Operating Systems
... Example: Creates a program which changes the invoking user's file permissions so that the files are readable by any user. Example: Author induces users to run the program by placing it in a common directory and naming it such that it appears to be a useful utility: e.g. format and print utility. ...
... Example: Creates a program which changes the invoking user's file permissions so that the files are readable by any user. Example: Author induces users to run the program by placing it in a common directory and naming it such that it appears to be a useful utility: e.g. format and print utility. ...
Leaders` Forum, March 16, 2006 - University of Western Ontario
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
Overview of Operating Systems Security Features
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
Its_time_to_go_hunting_-_IOC_vs_IOA_
... • IoC’s are known, universal bad news, while IoA’s only become bad based on what they mean to you and the situation ...
... • IoC’s are known, universal bad news, while IoA’s only become bad based on what they mean to you and the situation ...
security threats: a guide for small and medium
... we do not hear of small or medium-sized businesses becoming victims of such infections because it is not in their interest to publicize these incidents. Many small or medium-sized business networks cannot afford to employ prevention mechanisms such as network segregation. These factors simply make i ...
... we do not hear of small or medium-sized businesses becoming victims of such infections because it is not in their interest to publicize these incidents. Many small or medium-sized business networks cannot afford to employ prevention mechanisms such as network segregation. These factors simply make i ...
How to Identify Advanced Persistent, Targeted Malware Threats with Multidimensional Analysis
... This paper introduces multidimensional analysis of malware as an approach to identify advanced persistent, targeted threats. Most cyber threats originate from outside networks and exploit known vulnerabilities. These attacks have been responded to via conventional security methods, such as with anti ...
... This paper introduces multidimensional analysis of malware as an approach to identify advanced persistent, targeted threats. Most cyber threats originate from outside networks and exploit known vulnerabilities. These attacks have been responded to via conventional security methods, such as with anti ...
Network Access Control
... connection. Do not reconnect the computer until all steps have been completed, or you run the risk of being compromised again. 2. Backup your personal files. If you do not take this step, you will lose all of your data when you perform step #3. 3. Perform a New Install of Windows XP or Vista. Make s ...
... connection. Do not reconnect the computer until all steps have been completed, or you run the risk of being compromised again. 2. Backup your personal files. If you do not take this step, you will lose all of your data when you perform step #3. 3. Perform a New Install of Windows XP or Vista. Make s ...
SubVirt: Implementing malware with virtual machines
... Experimental setup: All experiments for the VMware-based VMBR run on a Dell Optiplex Workstation with a 2.8 GHz Pentium 4 and 1 GB of RAM. All experiments for the Virtual PC-based VMBR run on a Compaq Deskpro EN with a 1 GHz Pentium 4 and 256 MB of RAM. Our VMware-based VMBR compromises a RedHat Ent ...
... Experimental setup: All experiments for the VMware-based VMBR run on a Dell Optiplex Workstation with a 2.8 GHz Pentium 4 and 1 GB of RAM. All experiments for the Virtual PC-based VMBR run on a Compaq Deskpro EN with a 1 GHz Pentium 4 and 256 MB of RAM. Our VMware-based VMBR compromises a RedHat Ent ...
Computer GEEK - Ideas
... I have been working on a style of writing the installation notes. For menu selections I used bold, if I need to get clarification on something in the next install I put notes in brackets. Do NOT assume you will remember anything, because sometimes it can be a long time between installs. ...
... I have been working on a style of writing the installation notes. For menu selections I used bold, if I need to get clarification on something in the next install I put notes in brackets. Do NOT assume you will remember anything, because sometimes it can be a long time between installs. ...
Securing Information Systems
... – Phishing- Setting up fake Web sites or sending email messages that look legitimate, and using them to ask for confidential data – Eviltwins are wireless networks that pretend to offer trustworthy Wi-Fi connections to the Internet, such as those in airport lounges, hotels, or coffee shops. – Pharmi ...
... – Phishing- Setting up fake Web sites or sending email messages that look legitimate, and using them to ask for confidential data – Eviltwins are wireless networks that pretend to offer trustworthy Wi-Fi connections to the Internet, such as those in airport lounges, hotels, or coffee shops. – Pharmi ...
Computer Security and Safety, Ethics, and Privacy
... A password is a private combination of characters associated with the user name that allows access to certain computer resources. A CAPTCHA, which stands for Completely Automated Public Turing test to tell Computers and Humans Apart, is a program developed at CMU to verify that user input is not ...
... A password is a private combination of characters associated with the user name that allows access to certain computer resources. A CAPTCHA, which stands for Completely Automated Public Turing test to tell Computers and Humans Apart, is a program developed at CMU to verify that user input is not ...
Epidemics
... • You may visually notice extra pop ups and extra programs that seem to be running on your computer. ...
... • You may visually notice extra pop ups and extra programs that seem to be running on your computer. ...
Lecture 11.2
... A process of analyzing threats to and vulnerabilities of an information system and the potential impact the loss of information or capabilities of a system would have ...
... A process of analyzing threats to and vulnerabilities of an information system and the potential impact the loss of information or capabilities of a system would have ...
The most important program that runs on a computer
... The most important program that runs on a computer. Every general-purpose computer must have an operating system to run other programs. Operating systems perform basic tasks, such as recognizing input from the keyboard, sending output to the display screen, keeping track of files and directories on ...
... The most important program that runs on a computer. Every general-purpose computer must have an operating system to run other programs. Operating systems perform basic tasks, such as recognizing input from the keyboard, sending output to the display screen, keeping track of files and directories on ...
King Saud University College of Computer and Information Sciences
... 5. The guidelines for the morally acceptable use of computers in society are a) computer ethics b) privacy c) morality d) legal systems 6. The issues that deal with the collection and use of data about individuals is a) access ...
... 5. The guidelines for the morally acceptable use of computers in society are a) computer ethics b) privacy c) morality d) legal systems 6. The issues that deal with the collection and use of data about individuals is a) access ...
Slides
... • typically by one or more of: – prevention - block virus infection mechanism – detection - of viruses in infected system – reaction - restoring system to clean state ...
... • typically by one or more of: – prevention - block virus infection mechanism – detection - of viruses in infected system – reaction - restoring system to clean state ...
University of Arizona
... • However, the ease with which these applications can be downloaded and run has provided a new vehicle for inflicting damage • Vandals can take on the form of a software application or applet that causes destruction of various degrees • A vandal can destroy a single file or a major portion of a comp ...
... • However, the ease with which these applications can be downloaded and run has provided a new vehicle for inflicting damage • Vandals can take on the form of a software application or applet that causes destruction of various degrees • A vandal can destroy a single file or a major portion of a comp ...
Lecture 3.1 - Host
... drivers are generally not written by Microsoft, but by vendors. This means that the vendor selling the O.S. is not in complete control of the security of privileged mode software. (In Vista device drivers are no longer permitted to run with such high privilege.) Apple’s OSX operating system is far m ...
... drivers are generally not written by Microsoft, but by vendors. This means that the vendor selling the O.S. is not in complete control of the security of privileged mode software. (In Vista device drivers are no longer permitted to run with such high privilege.) Apple’s OSX operating system is far m ...
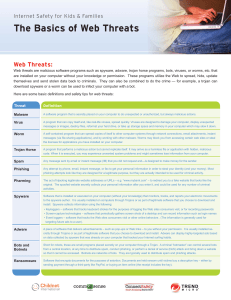
The Basics of Web Threats
... • Keyloggers – software that tracks keyboard strokes for the purposes of logging the Web sites consumers visit, or for recording passwords • Screen-capture technologies – software that periodically gathers screen shots of a desktop and can record information such as login names • Event loggers – sof ...
... • Keyloggers – software that tracks keyboard strokes for the purposes of logging the Web sites consumers visit, or for recording passwords • Screen-capture technologies – software that periodically gathers screen shots of a desktop and can record information such as login names • Event loggers – sof ...
Guide to Security - Cal Poly Pomona Foundation, Inc.
... • However, the ease with which these applications can be downloaded and run has provided a new vehicle for inflicting damage • Vandals can take on the form of a software application or applet that causes destruction of various degrees • A vandal can destroy a single file or a major portion of a comp ...
... • However, the ease with which these applications can be downloaded and run has provided a new vehicle for inflicting damage • Vandals can take on the form of a software application or applet that causes destruction of various degrees • A vandal can destroy a single file or a major portion of a comp ...
Kraig Welsh Resume
... Administrator, Help Desk Technician, Microsoft Office , Windows 7, 8 and 10, Network Administrator, Network Support Specialist, Network Technician, Remote Desktop Support, Security Consultant, Security Specialist, Security Systems Administrator, Server Administrator, Server Support Technician, Stora ...
... Administrator, Help Desk Technician, Microsoft Office , Windows 7, 8 and 10, Network Administrator, Network Support Specialist, Network Technician, Remote Desktop Support, Security Consultant, Security Specialist, Security Systems Administrator, Server Administrator, Server Support Technician, Stora ...
A Primer on Computer Security
... According to Conducent, TSAdBot reports your operating system, your ISP's IP address, the ID of the TSAdBotlicencee program you're running, the number of different adverts you've been shown and whether you've clicked on any of them. ...
... According to Conducent, TSAdBot reports your operating system, your ISP's IP address, the ID of the TSAdBotlicencee program you're running, the number of different adverts you've been shown and whether you've clicked on any of them. ...
Reading Organizer Instructor Version
... or knowledge. This information is sent to advertisers or others on the Internet and can include passwords and account numbers. Spyware is usually installed unknowingly when downloading a file, installing another program or clicking a popup. It can slow down a computer and make changes to internal se ...
... or knowledge. This information is sent to advertisers or others on the Internet and can include passwords and account numbers. Spyware is usually installed unknowingly when downloading a file, installing another program or clicking a popup. It can slow down a computer and make changes to internal se ...
business computer and network check list
... from temporary files. It does not have unnecessary programs slowing it down . The internet connection is reliable and does not go down I have a second internet connection for 100% up time I have clean power. Power surges and sudden outages will not damage my servers and essential network equipment. ...
... from temporary files. It does not have unnecessary programs slowing it down . The internet connection is reliable and does not go down I have a second internet connection for 100% up time I have clean power. Power surges and sudden outages will not damage my servers and essential network equipment. ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.