Building an in-depth defense with Vectra and sandbox security
... Once the exploit is downloaded and activated, it will initiate communication with the command-and-control (C&C) servers that the attacker uses to remotely control each phase of the cyber attack. The attacker uses the C&C servers to send commands to and receive responses from hosts under his control ...
... Once the exploit is downloaded and activated, it will initiate communication with the command-and-control (C&C) servers that the attacker uses to remotely control each phase of the cyber attack. The attacker uses the C&C servers to send commands to and receive responses from hosts under his control ...
01 - Quick Heal
... More Resilient and Dangerous The most notable botnet incident of 2013 was the birth of the CryptoLocker. While PC users are becoming more and more aware of fake anti-virus and alerts, CryptoLocker took all by surprise. Delivered by botnets and devised to extort money by encrypting files and holding ...
... More Resilient and Dangerous The most notable botnet incident of 2013 was the birth of the CryptoLocker. While PC users are becoming more and more aware of fake anti-virus and alerts, CryptoLocker took all by surprise. Delivered by botnets and devised to extort money by encrypting files and holding ...
Architecting High-Security Systems for Multilateral
... attackers with great technical expertise and extensive resources are more than just an abstract threat. It is possible to analyse systems to find so-called zero-day threats which are unknown to system vendors and undetectable by current anti-malware products. General purpose systems are usually defe ...
... attackers with great technical expertise and extensive resources are more than just an abstract threat. It is possible to analyse systems to find so-called zero-day threats which are unknown to system vendors and undetectable by current anti-malware products. General purpose systems are usually defe ...
File - IT Essentials Pc: Hardware/ software
... 18. What is InPrivate browsing and what are two ways to activate it in Internet Explorer? InPrivate browsing prevents the web browser from storing the following information: Usernames Passwords 19. What is SPAM? Spam, also known as junk mail, is unsolicited email. In most cases, spam is used as a me ...
... 18. What is InPrivate browsing and what are two ways to activate it in Internet Explorer? InPrivate browsing prevents the web browser from storing the following information: Usernames Passwords 19. What is SPAM? Spam, also known as junk mail, is unsolicited email. In most cases, spam is used as a me ...
Attacks and Mitigations
... user into running a Trojan horse program, possibly in an email attachment. It will typically install modules which allow the computer to be commanded and controlled by the botnet's owner. The Trojan may delete itself, or may remain present to update and maintain the modules. – The controller (aka ma ...
... user into running a Trojan horse program, possibly in an email attachment. It will typically install modules which allow the computer to be commanded and controlled by the botnet's owner. The Trojan may delete itself, or may remain present to update and maintain the modules. – The controller (aka ma ...
Security Requirements
... that looks like a normal program hidden inside another program. Once the valid program runs the hidden code starts and may damaged or delete files remember “Melissa” ...
... that looks like a normal program hidden inside another program. Once the valid program runs the hidden code starts and may damaged or delete files remember “Melissa” ...
From Russia with Love: Behind the Trend Micro
... I was recently invited by NBC News to take part in an experiment with their chief foreign correspondent, Richard Engel, that took place in Moscow, Russia. For this experiment, we created a honeypot environment to emulate a user currently in Russia for the Sochi Olympics performing basic tasks such a ...
... I was recently invited by NBC News to take part in an experiment with their chief foreign correspondent, Richard Engel, that took place in Moscow, Russia. For this experiment, we created a honeypot environment to emulate a user currently in Russia for the Sochi Olympics performing basic tasks such a ...
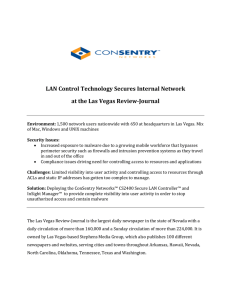
LVRJ Case study
... Environment: 1,500 network users nationwide with 650 at headquarters in Las Vegas. Mix of Mac, Windows and UNIX machines Security Issues: • Increased exposure to malware due to a growing mobile workforce that bypasses perimeter security such as firewalls and intrusion prevention systems as they trav ...
... Environment: 1,500 network users nationwide with 650 at headquarters in Las Vegas. Mix of Mac, Windows and UNIX machines Security Issues: • Increased exposure to malware due to a growing mobile workforce that bypasses perimeter security such as firewalls and intrusion prevention systems as they trav ...
Unit 2 - Intan Viona
... up by the sender’s server into uniform sized chunks of data known as packets; at any point along a packet’s trip from source to destination, a user can identify and read packets for a certain network or user. A tool known as a packet sniffer or sniffer program, allows a user to monitor and analyze n ...
... up by the sender’s server into uniform sized chunks of data known as packets; at any point along a packet’s trip from source to destination, a user can identify and read packets for a certain network or user. A tool known as a packet sniffer or sniffer program, allows a user to monitor and analyze n ...
Endpoint Security Device Control (formerly Sanctuary)
... the network. But the potential impact of data loss, be it accidental or malicious, is a very real concern. And today, removable media / devices are the most common data leakage routes – no file copy limits, no encryption, no audit trails and no central management. The information contained in custom ...
... the network. But the potential impact of data loss, be it accidental or malicious, is a very real concern. And today, removable media / devices are the most common data leakage routes – no file copy limits, no encryption, no audit trails and no central management. The information contained in custom ...
C.2. Vulnerabilities
... software deletion. Is your control effective against all possible causes of software deletion? If not, what threats does it not cover? Suppose a program to print paychecks secretly leaks a list of names of employees earning more than a certain amount each month. What controls could be instituted to ...
... software deletion. Is your control effective against all possible causes of software deletion? If not, what threats does it not cover? Suppose a program to print paychecks secretly leaks a list of names of employees earning more than a certain amount each month. What controls could be instituted to ...
Presentation on Security Flaws in Windows XP
... Victim sent a malicious e-mail message Message, when opened, would try to connect to a server run by the attacker Steal network authentication credentials from the victim, used to gain access to the victim's machine. Attack cannot be made across the firewall, only the machines in your local ...
... Victim sent a malicious e-mail message Message, when opened, would try to connect to a server run by the attacker Steal network authentication credentials from the victim, used to gain access to the victim's machine. Attack cannot be made across the firewall, only the machines in your local ...
Slajd 1 - CONFidence 2016
... linkedin: https://www.linkedin.com/groups/4865474 e-mail: [email protected] ...
... linkedin: https://www.linkedin.com/groups/4865474 e-mail: [email protected] ...
Data Confidentiality
... make it something others can’t guess – not personal make sure no one is looking when you type it in ...
... make it something others can’t guess – not personal make sure no one is looking when you type it in ...
Access Control, Operations Security, and Computer Forensics
... surveillance cameras, badges and magnetic card keys all allow monitoring of individuals. ...
... surveillance cameras, badges and magnetic card keys all allow monitoring of individuals. ...
CompTIA Strata™ Fundamentals of IT Technology
... ▪ Anti-virus software ▪ Ensure proper security certificate are used (SSL) ▪ Wireless encryption (WPA/WEP) ▪ Anti-spyware ▪ File encryption ▪ Firewalls ▪ Anti-spam software ▪ Password best practice • Complexity (password construction) • Password confidentiality • Change frequency • Re-use • Utilizati ...
... ▪ Anti-virus software ▪ Ensure proper security certificate are used (SSL) ▪ Wireless encryption (WPA/WEP) ▪ Anti-spyware ▪ File encryption ▪ Firewalls ▪ Anti-spam software ▪ Password best practice • Complexity (password construction) • Password confidentiality • Change frequency • Re-use • Utilizati ...
Lect 1 - Intro
... A program that attaches itself to a program or file so it can spread from one computer to another, leaving infections as it travels Worm: A program that takes advantage of file or information transport features on your system, which allows it to travel unaided. The biggest danger with a worm is its ...
... A program that attaches itself to a program or file so it can spread from one computer to another, leaving infections as it travels Worm: A program that takes advantage of file or information transport features on your system, which allows it to travel unaided. The biggest danger with a worm is its ...
file - ScholarSphere
... and mitigate the risks to an organization’s digital assets, and provide strategies for sustaining the security of those assets. [5] Risk assessment involves the use of an evaluative and often functional methodology to assess the type and level of risks that an organization must mitigate. How many of ...
... and mitigate the risks to an organization’s digital assets, and provide strategies for sustaining the security of those assets. [5] Risk assessment involves the use of an evaluative and often functional methodology to assess the type and level of risks that an organization must mitigate. How many of ...
Chapter 24 - William Stallings, Data and Computer
... additional processing overhead on each connection ...
... additional processing overhead on each connection ...
Computer Crimes - Crime Prevention HQ
... their local Secret Service office ● More information at FDLE website: ...
... their local Secret Service office ● More information at FDLE website: ...
Strategies Simplified Australian Signals Directorate
... Top Mitigation Strategy Number Six. Flash, Java, Acrobat Adobe and certain features in Microsoft Office (eg OLE), whilst useful for many business operations, can be vectors for malware or intruders to enter your network. Disabling these applications – and blocking online ads - removes any opportunit ...
... Top Mitigation Strategy Number Six. Flash, Java, Acrobat Adobe and certain features in Microsoft Office (eg OLE), whilst useful for many business operations, can be vectors for malware or intruders to enter your network. Disabling these applications – and blocking online ads - removes any opportunit ...
LECTURE NOTES - Ohio County Schools
... An operating system is the most important piece of software on a personal computer. The location of the operating system identifies the boot drive for the personal computer, which is typically the hard drive. Once started, the operating system manages the computer system and performs functions relat ...
... An operating system is the most important piece of software on a personal computer. The location of the operating system identifies the boot drive for the personal computer, which is typically the hard drive. Once started, the operating system manages the computer system and performs functions relat ...
"rooting"?
... CyanogenMod ROMs are one of the most popular aftermarket replacement firmware in the Android world. More comprehensive device specific firmwares, flashing guides, rooting tools and patch details can be referenced from the homepage. ClockWorkMod is a custom recovery option for Android phones and tabl ...
... CyanogenMod ROMs are one of the most popular aftermarket replacement firmware in the Android world. More comprehensive device specific firmwares, flashing guides, rooting tools and patch details can be referenced from the homepage. ClockWorkMod is a custom recovery option for Android phones and tabl ...
Android Reverse Engineering
... Malware is a piece of code which changes the behavior of either the operating system kernel or some security sensitive applications, without a user consent and in such a way that it is then impossible to detect those changes using a documented features of the operating system or the application.[2] ...
... Malware is a piece of code which changes the behavior of either the operating system kernel or some security sensitive applications, without a user consent and in such a way that it is then impossible to detect those changes using a documented features of the operating system or the application.[2] ...
Chapter11
... Computer Viruses, Worms, and Trojan Horses What are viruses, worms, and Trojan horses? Virus is a potentially damaging computer program ...
... Computer Viruses, Worms, and Trojan Horses What are viruses, worms, and Trojan horses? Virus is a potentially damaging computer program ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.