The wild world of malware: Keeping your
... traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download applications. As the number and severity of cyber-crimes continues to grow, it’s important to understand th ...
... traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download applications. As the number and severity of cyber-crimes continues to grow, it’s important to understand th ...
Emsisoft Internet Security
... This makes Emsisoft Internet Security a perfect fit for home users and small businesses, who frequently travel beyond their home network and who want something simple-yet-intelligent that will keep their information secure, no matter where they go. ...
... This makes Emsisoft Internet Security a perfect fit for home users and small businesses, who frequently travel beyond their home network and who want something simple-yet-intelligent that will keep their information secure, no matter where they go. ...
slides - University of Cambridge Computer Laboratory
... – BLP engineering and opsec costs would not be sustainable – Middle way: train sysadmins, take all the Secret stuff offline ...
... – BLP engineering and opsec costs would not be sustainable – Middle way: train sysadmins, take all the Secret stuff offline ...
OWN YOUR SPACE
... more than just one attack. It could include a virus, worm and Trojan horse. Causes more damage than just one piece of malware ...
... more than just one attack. It could include a virus, worm and Trojan horse. Causes more damage than just one piece of malware ...
CH 8 – Review - WordPress.com
... A good defense to prevent your computer from becoming a zombie is to – install and run antivirus software Bluetooth is an – electronics standard The typical range for consumer Bluetooth devices is 600 feet - False One way to protect yourself from risks of Bluetooth devices is to – disable Bluetooth ...
... A good defense to prevent your computer from becoming a zombie is to – install and run antivirus software Bluetooth is an – electronics standard The typical range for consumer Bluetooth devices is 600 feet - False One way to protect yourself from risks of Bluetooth devices is to – disable Bluetooth ...
File
... Trojan programs conceal malicious code within a seemingly useful application. The game, utility, or other application typically performs its stated task, but sooner or later it does something harmful. This type of threat spreads when users or Web sites inadvertently share it with others. Threats Def ...
... Trojan programs conceal malicious code within a seemingly useful application. The game, utility, or other application typically performs its stated task, but sooner or later it does something harmful. This type of threat spreads when users or Web sites inadvertently share it with others. Threats Def ...
Computer Systems Security
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...
Do you know someone may be watching you?
... Internet malware detection, defense, and analysis Intrusion detection and anomaly detections Network security Web and social networking security ...
... Internet malware detection, defense, and analysis Intrusion detection and anomaly detections Network security Web and social networking security ...
Remote Domain Security Awareness Training
... Worm is a standalone computer program and it replicates itself in order to spread to other computers It exploits security hole in software or the operating system. It uses computer network to spread itself Unlike a virus, it does not attach itself to an existing program ...
... Worm is a standalone computer program and it replicates itself in order to spread to other computers It exploits security hole in software or the operating system. It uses computer network to spread itself Unlike a virus, it does not attach itself to an existing program ...
Open ended challenge rationale
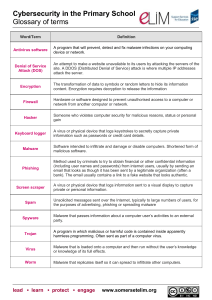
... Someone who violates computer security for malicious reasons, status or personal ...
... Someone who violates computer security for malicious reasons, status or personal ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.