pps - AquaLab - Northwestern University
... • Check if references are to inside sandbox – Dynamic jumps require dynamic checks (inserting code) – Systems calls through a reference monitor (interposition) ...
... • Check if references are to inside sandbox – Dynamic jumps require dynamic checks (inserting code) – Systems calls through a reference monitor (interposition) ...
Document
... • A computer virus is a program that attaches itself to another computer program and attempts to spread to other computers when files are exchanged • Not just limited to computer – Smartphones, tablets, other devices ...
... • A computer virus is a program that attaches itself to another computer program and attempts to spread to other computers when files are exchanged • Not just limited to computer – Smartphones, tablets, other devices ...
Information Privacy What is information privacy?
... Identify ways to safeguard against computer viruses, worms, Trojan horses, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use ...
... Identify ways to safeguard against computer viruses, worms, Trojan horses, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use ...
NS2-M3C22S1_-_Computers_and_the_Internet
... simulate mathematical calculations or physical behavior by analogous current or fluid flow through an array of components, gear rotations or scale manipulations. Digital computers are far superior. ...
... simulate mathematical calculations or physical behavior by analogous current or fluid flow through an array of components, gear rotations or scale manipulations. Digital computers are far superior. ...
Appendix *J* - Credit Plus
... Implement and follow current best security practices for computer anti-Spyware scanning services and procedures: o Use, implement and maintain a current, commercially available computer anti-spyware scanning product on all computers, systems and networks. o If you suspect actual or potential Spyware ...
... Implement and follow current best security practices for computer anti-Spyware scanning services and procedures: o Use, implement and maintain a current, commercially available computer anti-spyware scanning product on all computers, systems and networks. o If you suspect actual or potential Spyware ...
Security on the Internet - Australian Federal Police
... Do not open any emails from someone you do not know and trust. Do not open attachments unless they are expected and the contents are known. Install, activate and maintain a firewall on your computer. Install and maintain reputable anti-virus and antispyware software. Keep your operating sy ...
... Do not open any emails from someone you do not know and trust. Do not open attachments unless they are expected and the contents are known. Install, activate and maintain a firewall on your computer. Install and maintain reputable anti-virus and antispyware software. Keep your operating sy ...
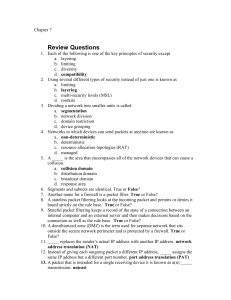
Chapter07
... A rootkit is a set of software tools used by an attacker to break into a computer and obtain special operating system privileges in order to both perform unauthorized functions and also hide all traces of its existence. A rootkit often includes several programs designed to monitor traffic, create a ...
... A rootkit is a set of software tools used by an attacker to break into a computer and obtain special operating system privileges in order to both perform unauthorized functions and also hide all traces of its existence. A rootkit often includes several programs designed to monitor traffic, create a ...
NetDay Cyber Security Kit for Schools
... anti-virus software. Anti-virus software protects computers from viruses that destroy data and require costly repairs to computer systems. For optimal use, anti-virus software should be scanning all documents on a computer, as well as all incoming emails, on a daily basis. You should also check to m ...
... anti-virus software. Anti-virus software protects computers from viruses that destroy data and require costly repairs to computer systems. For optimal use, anti-virus software should be scanning all documents on a computer, as well as all incoming emails, on a daily basis. You should also check to m ...
answer-sheet-7540-040-7630-345-b_
... servers are safe from random people in the office going in and damaging the servers. Also locking office doors at the end of the day to reduce the change of theft. Also there are physical locks such as Kensington locks, there can go on laptops to secure them and only the owner can open them up and u ...
... servers are safe from random people in the office going in and damaging the servers. Also locking office doors at the end of the day to reduce the change of theft. Also there are physical locks such as Kensington locks, there can go on laptops to secure them and only the owner can open them up and u ...
PowerPoint Presentation - Lead
... • Is the process of preventing and detecting unauthorized use of your computer • Prevention measures help you to stop unauthorized users from accessing any part of your computer system. • Detection helps you to determine whether or not someone attempted to break into your system, if they were succes ...
... • Is the process of preventing and detecting unauthorized use of your computer • Prevention measures help you to stop unauthorized users from accessing any part of your computer system. • Detection helps you to determine whether or not someone attempted to break into your system, if they were succes ...
FAKEM RAT: Malware Disguised as Windows Messenger and
... The perpetrators of targeted attacks aim to maintain persistent presence in a target network in order to extract sensitive data when needed. To maintain persistent presence, attackers seek to blend in with normal network traffic and use ports that are typically allowed by firewalls. As a result, man ...
... The perpetrators of targeted attacks aim to maintain persistent presence in a target network in order to extract sensitive data when needed. To maintain persistent presence, attackers seek to blend in with normal network traffic and use ports that are typically allowed by firewalls. As a result, man ...
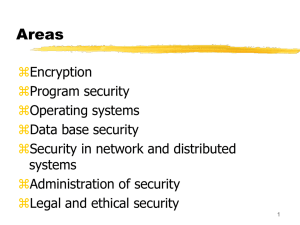
Operating System Security Fundamentals
... FTP (File Transfer Protocol): Internet service for transferring files from one computer to another Transmits usernames and passwords in plaintext Root account cannot be used with FTP Anonymous FTP: ability to log on to the FTP server without being authenticated ...
... FTP (File Transfer Protocol): Internet service for transferring files from one computer to another Transmits usernames and passwords in plaintext Root account cannot be used with FTP Anonymous FTP: ability to log on to the FTP server without being authenticated ...
Topics
... Unauthorized access: using a computer, network, or other resource without permission Hacker: an individual who accesses a network without permission hacking: activities involved in gaining unauthorized entry into a network’s resources white hats: hackers with good intentions that attempt to ...
... Unauthorized access: using a computer, network, or other resource without permission Hacker: an individual who accesses a network without permission hacking: activities involved in gaining unauthorized entry into a network’s resources white hats: hackers with good intentions that attempt to ...
Jaden Terry CIS 280 Final Network Security From browsing the
... this event push users away from the PlayStation and affected the business in the long run. Finally, Operation Shady RAT was a recent hack against the government that siphoned off data from government computers. This happened by using what is ...
... this event push users away from the PlayStation and affected the business in the long run. Finally, Operation Shady RAT was a recent hack against the government that siphoned off data from government computers. This happened by using what is ...
PowerPoint Slides
... Right to use software Single-user license agreement allows user to install software on one computer, make backup copy, and sell software after removing from computer ...
... Right to use software Single-user license agreement allows user to install software on one computer, make backup copy, and sell software after removing from computer ...
Introduction to management of Information Technologies
... attack messages to a server to the point that the server began to operate very slowly. Which of the following does the attacker attempt? a) b) c) d) ...
... attack messages to a server to the point that the server began to operate very slowly. Which of the following does the attacker attempt? a) b) c) d) ...
CMP2204 Operating System Technologies
... Identify some contributors to operating systems and relate their achievements to the knowledge area; provide some reasons for a computer to have an operating system; describe concurrency and reasons for its importance; describe scheduling and illustrate how it works to improve computer performance; ...
... Identify some contributors to operating systems and relate their achievements to the knowledge area; provide some reasons for a computer to have an operating system; describe concurrency and reasons for its importance; describe scheduling and illustrate how it works to improve computer performance; ...
Figure 6-1
... too large for the next router to handle be divided into fragments. The fragment packet identifies an offset to the beginning of the first packet that enables the entire packet to be reassembled by the receiving system. In the teardrop attack, the attacker's IP puts a confusing offset value in the se ...
... too large for the next router to handle be divided into fragments. The fragment packet identifies an offset to the beginning of the first packet that enables the entire packet to be reassembled by the receiving system. In the teardrop attack, the attacker's IP puts a confusing offset value in the se ...
Computersikkerhed
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
Discovering Computers Fundamentals 3rd Edition
... What is information privacy? Right of individuals and companies to restrict collection and use of information about them Difficult to maintain today because data is stored online Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
... What is information privacy? Right of individuals and companies to restrict collection and use of information about them Difficult to maintain today because data is stored online Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
Curriculum Vitae
... - Phones – VoIP with Asterisk - LDAP based authentication with OpenLDAP - Mail servers with Postfix or Zimbra - Websites development (PHP, SQL) - Deployment of websites ( Joomla and Zencart based ) - Thin-Clients for Windows and Linux – energy saving - Rock Cluster installation/management - Scientif ...
... - Phones – VoIP with Asterisk - LDAP based authentication with OpenLDAP - Mail servers with Postfix or Zimbra - Websites development (PHP, SQL) - Deployment of websites ( Joomla and Zencart based ) - Thin-Clients for Windows and Linux – energy saving - Rock Cluster installation/management - Scientif ...
Security+ Guide to Network Security Fundamentals
... Almost impossible to detect until after triggered Often the work of former employees For example: macro virus ...
... Almost impossible to detect until after triggered Often the work of former employees For example: macro virus ...
Competencies for ITSE 1294.doc
... 8. List typical e-mail software package features 9. Explain how an e-mail system works and the difference between POP mail and Webbased mail 10. Explain why most computers are digital and how that relates to the binary number system 11. Describe the role of a microprocessor’s ALU, control unit, regi ...
... 8. List typical e-mail software package features 9. Explain how an e-mail system works and the difference between POP mail and Webbased mail 10. Explain why most computers are digital and how that relates to the binary number system 11. Describe the role of a microprocessor’s ALU, control unit, regi ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.