Chapter 3. Summary of Linux and Unix Security
... This book provides a set of design and implementation guidelines for writing secure programs for Linux and Unix systems. Such programs include application programs used as viewers of remote data, web applications (including CGI scripts), network servers, and setuid/setgid programs. Specific guidelin ...
... This book provides a set of design and implementation guidelines for writing secure programs for Linux and Unix systems. Such programs include application programs used as viewers of remote data, web applications (including CGI scripts), network servers, and setuid/setgid programs. Specific guidelin ...
700 Series Color Mobile Computer User`s Manual
... Gen2, JANUS, LabelShop, MobileLAN, Picolink, Ready-to-Work, RoutePower, Sabre, ScanPlus, ShopScan, Smart Mobile Computing, TE 2000, Trakker Antares, and Vista Powered are either trademarks or registered trademarks of Intermec Technologies Corporation. There are U.S. and foreign patents as well as U. ...
... Gen2, JANUS, LabelShop, MobileLAN, Picolink, Ready-to-Work, RoutePower, Sabre, ScanPlus, ShopScan, Smart Mobile Computing, TE 2000, Trakker Antares, and Vista Powered are either trademarks or registered trademarks of Intermec Technologies Corporation. There are U.S. and foreign patents as well as U. ...
Programming with Java, Swing and Squint
... constructed, and software, the programs that determine how the machine will behave. Everything described above can be accomplished by changing the software used without changing the machine’s actual circuitry in any way. In fact, the changes that occur when you switch to a new program are often grea ...
... constructed, and software, the programs that determine how the machine will behave. Everything described above can be accomplished by changing the software used without changing the machine’s actual circuitry in any way. In fact, the changes that occur when you switch to a new program are often grea ...
Answer Sheet
... This book is designed to provide information about taking and passing the CompTIA A+ exam and about how to be a successful PC technician. Every effort has been made to make this book as complete and as accurate as possible, but no warranty or fitness is implied. The information is provided on an “as ...
... This book is designed to provide information about taking and passing the CompTIA A+ exam and about how to be a successful PC technician. Every effort has been made to make this book as complete and as accurate as possible, but no warranty or fitness is implied. The information is provided on an “as ...
Diskeeper Administrator 9 User`s Manual
... package, it can be installed on one or more computers that are easily accessible by the people who need to use Diskeeper Administrator. ...
... package, it can be installed on one or more computers that are easily accessible by the people who need to use Diskeeper Administrator. ...
Windows-2000 and system Administration
... a lot more than just a simple upgrade. It's almost a total rewrite of the Windows NT Operating System, with hundreds of new features and fixes. Q2. What is windows 2000 family? Explain. Ans. Windows 2000 family consists of four operating systems: Windows 2000 Professional Windows 2000 Server Wind ...
... a lot more than just a simple upgrade. It's almost a total rewrite of the Windows NT Operating System, with hundreds of new features and fixes. Q2. What is windows 2000 family? Explain. Ans. Windows 2000 family consists of four operating systems: Windows 2000 Professional Windows 2000 Server Wind ...
I T ' S E L E M... L O G I C P R O...
... system requirements and the system would automatically fulfill them. If requirements changed, or if the system deviated from requirements, the system would change itself to converge with requirements. Current specialized tools for convergent system administration already provide some ability to do t ...
... system requirements and the system would automatically fulfill them. If requirements changed, or if the system deviated from requirements, the system would change itself to converge with requirements. Current specialized tools for convergent system administration already provide some ability to do t ...
A General Model for Component-based Software
... spent on revising my thesis. Without his brilliant ideas and his help, this thesis would not be finished. I would like to thank Dr. T. Smedley and Dr. R. Giles for their serving as members in my examining committee. I sincerely appreciate their time, interest, and suggestions. The financial support ...
... spent on revising my thesis. Without his brilliant ideas and his help, this thesis would not be finished. I would like to thank Dr. T. Smedley and Dr. R. Giles for their serving as members in my examining committee. I sincerely appreciate their time, interest, and suggestions. The financial support ...
Creating high-performance, statically type
... network, malicious attacks and electronic crime began to necessitate additional security measures. Rather than rewriting existing applications, additional layers of cryptography were introduced in 1994 to encapsulate the traffic such as SNP [286] and the now-ubiquitous Secure Sockets Layer (SSL) [93 ...
... network, malicious attacks and electronic crime began to necessitate additional security measures. Rather than rewriting existing applications, additional layers of cryptography were introduced in 1994 to encapsulate the traffic such as SNP [286] and the now-ubiquitous Secure Sockets Layer (SSL) [93 ...
2. Overview of Operating Systems
... Information is also kept only where it is needed and is accessible only in certain ways, so bugs affecting that data are limited to a specific module or layer. Mechanisms and Policies The policies what is to be done while the mechanism specifies how it is to be done. For instance, the timer construc ...
... Information is also kept only where it is needed and is accessible only in certain ways, so bugs affecting that data are limited to a specific module or layer. Mechanisms and Policies The policies what is to be done while the mechanism specifies how it is to be done. For instance, the timer construc ...
Survey of Cyber Moving Targets Lincoln Laboratory Technical Report 1166
... limited [78, 87] by the architecture machine width (i.e., number of bits: 32 or 64). In this case, they do get very close to that limit with 29 bits of entropy for the heap location, 28 bits for the stack location, 20 bits in mmap(), and 20 bits within the data and code segments. This far exceeds ot ...
... limited [78, 87] by the architecture machine width (i.e., number of bits: 32 or 64). In this case, they do get very close to that limit with 29 bits of entropy for the heap location, 28 bits for the stack location, 20 bits in mmap(), and 20 bits within the data and code segments. This far exceeds ot ...
Windows 7 Advanced Training Manual
... scanners, mice, keyboard, speakers, digital cameras and audio devices, game controllers, and modems. You can also modify AutoPlay options for removable media, adjust sound and power usage options, and change display settings. Devices and Printers AutoPlay Sound Power Options Display ...
... scanners, mice, keyboard, speakers, digital cameras and audio devices, game controllers, and modems. You can also modify AutoPlay options for removable media, adjust sound and power usage options, and change display settings. Devices and Printers AutoPlay Sound Power Options Display ...
Lab # 05: Building IP internetwork
... (replicated) to the other backup domain controllers in the domain. These backup domain controllers keep copies of the SAM that is stored on the PDC, and assist in validating user logon requests. The domain concept attempts to solve the issues of management and security, by providing a central point ...
... (replicated) to the other backup domain controllers in the domain. These backup domain controllers keep copies of the SAM that is stored on the PDC, and assist in validating user logon requests. The domain concept attempts to solve the issues of management and security, by providing a central point ...
CPM2A OPERATION MANUAL
... Section 4 describes SYSMAC and SYSMAC-CPT Support Software capabilities, how to connect the Programming Console, and how to perform the various programming operations. Section 5 describes how to perform a test run and how to diagnose and correct the hardware and software errors that can occur during ...
... Section 4 describes SYSMAC and SYSMAC-CPT Support Software capabilities, how to connect the Programming Console, and how to perform the various programming operations. Section 5 describes how to perform a test run and how to diagnose and correct the hardware and software errors that can occur during ...
Operating System-I
... mode of operation is common for the simple evaluation boards that are sometimes used in introductory microprocessor design and interfacing courses. Programs for the bare machine can be developed by manually translating sequences of instructions into binary or some other code whose base is usually an ...
... mode of operation is common for the simple evaluation boards that are sometimes used in introductory microprocessor design and interfacing courses. Programs for the bare machine can be developed by manually translating sequences of instructions into binary or some other code whose base is usually an ...
Programming from the Ground Up Jonathan Bartlett Dominick Bruno, Jr. Edited by
... others require you to simply analyze your options and explain a best solution. Many of the questions don’t have right or wrong answers, but that doesn’t mean they are unimportant. Learning the issues involved in programming, learning how to research answers, and learning how to look ahead are all a ...
... others require you to simply analyze your options and explain a best solution. Many of the questions don’t have right or wrong answers, but that doesn’t mean they are unimportant. Learning the issues involved in programming, learning how to research answers, and learning how to look ahead are all a ...
Microsoft Computer Dictionary, Fifth Edition eBook
... Although this book covers nearly every aspect of computing, it does not include entries on most companies or on most makes and models of computers, nor does it contain entries on most application software products. The few exceptions to this rule of thumb are key companies and products that have a h ...
... Although this book covers nearly every aspect of computing, it does not include entries on most companies or on most makes and models of computers, nor does it contain entries on most application software products. The few exceptions to this rule of thumb are key companies and products that have a h ...
Programming from the Ground Up by Jonathan Bartlett
... I love programming. I enjoy the challenge to not only make a working program, but to do so with style. Programming is like poetry. It conveys a message, not only to the computer, but to those who modify and use your program. With a program, you build your own world with your own rules. You create yo ...
... I love programming. I enjoy the challenge to not only make a working program, but to do so with style. Programming is like poetry. It conveys a message, not only to the computer, but to those who modify and use your program. With a program, you build your own world with your own rules. You create yo ...
PowerLab SP Owner`s Guide
... PowerLab can and cannot do, but this is not a service manual: only an authorised ADInstruments distributor should attempt repairs. If you modify the recording unit yourself, you void any rights you have under warranty. The user’s guides for the Chart and Scope application programs provide detailed i ...
... PowerLab can and cannot do, but this is not a service manual: only an authorised ADInstruments distributor should attempt repairs. If you modify the recording unit yourself, you void any rights you have under warranty. The user’s guides for the Chart and Scope application programs provide detailed i ...
Begin - Marcel Bresink
... © Copyright 2003 – 2016 by Marcel Bresink Software-Systeme Marcel Bresink Software-Systeme Ringstr. 21 56630 Kretz Germany All rights reserved. No part of this publication may be redistributed, translated in other languages, or transmitted, in any form or by any means, electronic, mechanical, record ...
... © Copyright 2003 – 2016 by Marcel Bresink Software-Systeme Marcel Bresink Software-Systeme Ringstr. 21 56630 Kretz Germany All rights reserved. No part of this publication may be redistributed, translated in other languages, or transmitted, in any form or by any means, electronic, mechanical, record ...
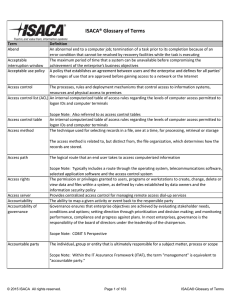
ISACA® Glossary of Terms
... perceptions of others and can be influenced by improper actions or associations. A program written in a portable, platform‐independent computer language, such as Java, JavaScript or Visual Basic Scope Note: An applet is usually embedded in an HyperText Markup Language (HTML) page downloaded from ...
... perceptions of others and can be influenced by improper actions or associations. A program written in a portable, platform‐independent computer language, such as Java, JavaScript or Visual Basic Scope Note: An applet is usually embedded in an HyperText Markup Language (HTML) page downloaded from ...
INFORMATION TECHNOLOGY
... reading data from the main memory. Only if the data is not in the cache does it need to access main memory, but in the process it copies whatever it finds into the cache so that it is there ready for the next time it is needed. The whole process is controlled by a group of logic circuits called the ...
... reading data from the main memory. Only if the data is not in the cache does it need to access main memory, but in the process it copies whatever it finds into the cache so that it is there ready for the next time it is needed. The whole process is controlled by a group of logic circuits called the ...
The Illustrated Guide to Assistive Technology and Devices: Tools
... word as it was spoken, making it an ideal reading tool for users with dyslexia and other learning disabilities. In 2000, we renamed our nonprofit company Benetech, which stands for “beneficial technology.” Benetech is a collection of social enterprises, hybrids that combine the best aspects of busin ...
... word as it was spoken, making it an ideal reading tool for users with dyslexia and other learning disabilities. In 2000, we renamed our nonprofit company Benetech, which stands for “beneficial technology.” Benetech is a collection of social enterprises, hybrids that combine the best aspects of busin ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.