Before You Begin: Assign Information Classification
... is manufactured. An EPROM chip can be erased with exposure to UV light. Special equipment is required. Information is written to an EEPROM chip after it is manufactured. EEPROM chips are also called Flash ROMs. An EEPROM chip can be erased and re-written without having to remove the chip from the co ...
... is manufactured. An EPROM chip can be erased with exposure to UV light. Special equipment is required. Information is written to an EEPROM chip after it is manufactured. EEPROM chips are also called Flash ROMs. An EEPROM chip can be erased and re-written without having to remove the chip from the co ...
MS5104 Computer Security
... • We continue our example. A user wants to execute an operation requiring supervisor mode, e.g. write to memory. • To deal with this request, the processor has to switch between modes, but how should this switch be performed? • Simply changing the status bit to supervisor mode would give all privile ...
... • We continue our example. A user wants to execute an operation requiring supervisor mode, e.g. write to memory. • To deal with this request, the processor has to switch between modes, but how should this switch be performed? • Simply changing the status bit to supervisor mode would give all privile ...
U A
... The enrollments and graduation rates have been strong through out its availability. Most CNT students looking for employment find an IT position before the end of their second year. The program provides employers with skilled IT employees. According to the Department of Labor and Workforce Developme ...
... The enrollments and graduation rates have been strong through out its availability. Most CNT students looking for employment find an IT position before the end of their second year. The program provides employers with skilled IT employees. According to the Department of Labor and Workforce Developme ...
pipemaster - Magnatech LLC
... changes must be made. A sensor in the weld Head provides position information. All welding parameters may be changed at each level. ...
... changes must be made. A sensor in the weld Head provides position information. All welding parameters may be changed at each level. ...
- Govt Online Exam Covers
... 144) India launched I-LTEO programme to monitor 8 different biomes 145) Beijing issued first-ever Red Alert on Air Pollution 146) The much-delayed first phase of SmartCity Kochi, a joint venture of SmartCity Dubai and the Kerala Government, is ready for opening and will most likely take place in Jan ...
... 144) India launched I-LTEO programme to monitor 8 different biomes 145) Beijing issued first-ever Red Alert on Air Pollution 146) The much-delayed first phase of SmartCity Kochi, a joint venture of SmartCity Dubai and the Kerala Government, is ready for opening and will most likely take place in Jan ...
Data security - E
... 1. Hardware: The term hardware refers to machinery. This category includes the computer itself, which is often referred to as the central processing unit (CPU), and all of its support equipments. Among the support equipments are input and output devices, storage devices and communications devices. 2 ...
... 1. Hardware: The term hardware refers to machinery. This category includes the computer itself, which is often referred to as the central processing unit (CPU), and all of its support equipments. Among the support equipments are input and output devices, storage devices and communications devices. 2 ...
Pic Programmer by Myke Predko
... changes are. I am anticipating that this is the last modification to the El Cheapo circuit design. This does not mean that the programmer will remain static. Over the next few weeks, I will be releasing the Gerber files for a "Bare Board" version of the programmer and I will be creating a Visual Bas ...
... changes are. I am anticipating that this is the last modification to the El Cheapo circuit design. This does not mean that the programmer will remain static. Over the next few weeks, I will be releasing the Gerber files for a "Bare Board" version of the programmer and I will be creating a Visual Bas ...
CS61C - Lecture 13 - EECS Instructional Support Group Home Page
... CS61C: So what's in it for me? ° Learn some of the big ideas in CS & engineering: • 5 Classic components of a Computer • Data can be anything (integers, floating point, characters): a program determines what it is • Stored program concept: instructions just data • Principle of Locality, exploited v ...
... CS61C: So what's in it for me? ° Learn some of the big ideas in CS & engineering: • 5 Classic components of a Computer • Data can be anything (integers, floating point, characters): a program determines what it is • Stored program concept: instructions just data • Principle of Locality, exploited v ...
CS6461 – Computer Architecture Spring 2012 Stephen H. Kaisler, D
... (Partially based on notes from David Patterson, UC Berkeley) ...
... (Partially based on notes from David Patterson, UC Berkeley) ...
Chapter 9 - Automation Direct
... The RUN indicator is blinking: the PLC firmware needs to be upgraded. Both of the programming devices, Handheld Programmer and DirectSOFT 5, will return an error message describing the problem. Depending on the error, there may also be an AUX function you can use to help diagnose the problem. The mo ...
... The RUN indicator is blinking: the PLC firmware needs to be upgraded. Both of the programming devices, Handheld Programmer and DirectSOFT 5, will return an error message describing the problem. Depending on the error, there may also be an AUX function you can use to help diagnose the problem. The mo ...
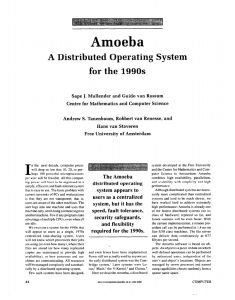
Amoeba--A Distributed Operating System for the 1990s,
... four components: workstations, pool processors, specialized servers, and gateways. The workstations execute only processes that require intense user interaction - for example, window managers, command interpreters, editors, and CAD/CAM graphical front ends. Most applications, however, do not interac ...
... four components: workstations, pool processors, specialized servers, and gateways. The workstations execute only processes that require intense user interaction - for example, window managers, command interpreters, editors, and CAD/CAM graphical front ends. Most applications, however, do not interac ...
Access Control - Cambridge Computer Laboratory
... ways of ensuring that employees’ laptops don’t pick up malware at home, so it makes sense to have one partition (or virtual machine) for work and another for play. Undoing the damage done by many years of information-sharing promiscuity will be hard, but in the medium term we might reasonably hope f ...
... ways of ensuring that employees’ laptops don’t pick up malware at home, so it makes sense to have one partition (or virtual machine) for work and another for play. Undoing the damage done by many years of information-sharing promiscuity will be hard, but in the medium term we might reasonably hope f ...
A MAGNETIC DEVICE FOR COMPUTER GRAPHIC INPUT
... any pen position, the head can be located over, at most, one boundary between sectors. For these reasons, it would appear that a conventional binary coding scheme should not be used because the pen point may be positioned over more than one indecision boundary. However, the addition of a small amoun ...
... any pen position, the head can be located over, at most, one boundary between sectors. For these reasons, it would appear that a conventional binary coding scheme should not be used because the pen point may be positioned over more than one indecision boundary. However, the addition of a small amoun ...
chapter quiz
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Automotive Fuel and Emissions Control Systems, 2/e By James D. Halderman and Jim Linder ...
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Automotive Fuel and Emissions Control Systems, 2/e By James D. Halderman and Jim Linder ...
Operating System Security Erik Poll
... which program code it is executing which memory has been allocated to it value of program counter (pc) of that process value of registers for that process execution stack for that process (which records outstanding subroutine calls and local parameters) – other resources allocated to that process, e ...
... which program code it is executing which memory has been allocated to it value of program counter (pc) of that process value of registers for that process execution stack for that process (which records outstanding subroutine calls and local parameters) – other resources allocated to that process, e ...
Computer/Information Security Chapter-1
... program or data file, or malfunction of an operating system file manager so that it cannot find a particular disk file. ...
... program or data file, or malfunction of an operating system file manager so that it cannot find a particular disk file. ...
Information Technology Competency Model of Core Learning
... recommendations specifically addressing courses for other disciplines. The present report is the first to make such recommendations” (Klee, Austing, Impagliazzo, Currie Little, & Chlopan, 1993). Two decades later information technology has become interdisciplinary and is an integral part of every fi ...
... recommendations specifically addressing courses for other disciplines. The present report is the first to make such recommendations” (Klee, Austing, Impagliazzo, Currie Little, & Chlopan, 1993). Two decades later information technology has become interdisciplinary and is an integral part of every fi ...
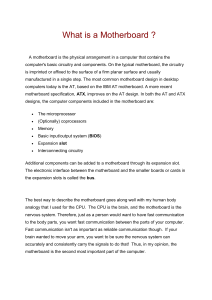
What is a Motherboard
... The motherboard has been an integral part of most personal computers for more than 20 years. Think of a motherboard as a scale model of a futuristic city with many modular plug-in buildings, each using power from a common electrical system. Multiple-lane highways of various widths transport data bet ...
... The motherboard has been an integral part of most personal computers for more than 20 years. Think of a motherboard as a scale model of a futuristic city with many modular plug-in buildings, each using power from a common electrical system. Multiple-lane highways of various widths transport data bet ...
AN98555 - High Reliability Programming Methodology for Floating
... other rights. Cypress products are not warranted nor intended to be used for medical, life support, life saving, critical control or safety applications, unless pursuant to an express written agreement with Cypress. Furthermore, Cypress does not authorize its products for use as critical components ...
... other rights. Cypress products are not warranted nor intended to be used for medical, life support, life saving, critical control or safety applications, unless pursuant to an express written agreement with Cypress. Furthermore, Cypress does not authorize its products for use as critical components ...
AN-722 APPLICATION NOTE
... INTRODUCTION The ADM106x family of fully programmable supply sequencers can be used as complete supply management solutions in systems utilizing multiple voltage supplies. Applications include line cards in telecommunications infrastructure equipment (central office, base stations) and blade cards i ...
... INTRODUCTION The ADM106x family of fully programmable supply sequencers can be used as complete supply management solutions in systems utilizing multiple voltage supplies. Applications include line cards in telecommunications infrastructure equipment (central office, base stations) and blade cards i ...
radio frequency identification based smart security
... many other functions. Coded signals are sent through the home's wiring to switches and outlets that are programmed to operate appliances and electronic devices in every part of the house. A smart home appears "intelligent" because its computer systems can monitor many aspects of daily living. As the ...
... many other functions. Coded signals are sent through the home's wiring to switches and outlets that are programmed to operate appliances and electronic devices in every part of the house. A smart home appears "intelligent" because its computer systems can monitor many aspects of daily living. As the ...
pic lecture
... Typical development circuit adds: RS232 interface (typically with a MAX2.. Chip) LED’s / switches / etc ...
... Typical development circuit adds: RS232 interface (typically with a MAX2.. Chip) LED’s / switches / etc ...
Microcontrollers: Inputs and outputs
... and a set of input and output pins which can be used to interact with an external circuit. The microcontroller IC is a digital device and, since the processor operates on “transistor to transistor” logic (TTL), only two logic states are acceptable: HIGH (~ +5 V) and LOW (~0 V). The microcontrollers ...
... and a set of input and output pins which can be used to interact with an external circuit. The microcontroller IC is a digital device and, since the processor operates on “transistor to transistor” logic (TTL), only two logic states are acceptable: HIGH (~ +5 V) and LOW (~0 V). The microcontrollers ...
Lecture 2: Fundamentals and Trends
... TPC-W a transactional web benchmark TPC-App application server and web services benchmark ...
... TPC-W a transactional web benchmark TPC-App application server and web services benchmark ...
ppt
... To be used with S. Dandamudi, “Fundamentals of Computer Organization and Design,” Springer, 2003. ...
... To be used with S. Dandamudi, “Fundamentals of Computer Organization and Design,” Springer, 2003. ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.