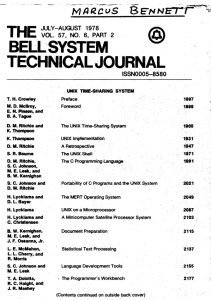
Bell System Technical Journal - PDP
... help in data compression or cryptography; mailing lists turn into maps. The prevalence of free-format text, even in "data" files, makes the text-processing utilities useful for many strictly data processing functions such as shuffling fields, counting, or collating. (iii) The UNIX system and the C l ...
... help in data compression or cryptography; mailing lists turn into maps. The prevalence of free-format text, even in "data" files, makes the text-processing utilities useful for many strictly data processing functions such as shuffling fields, counting, or collating. (iii) The UNIX system and the C l ...
A Survey on Automated Dynamic Malware Analysis Techniques and Tools
... attacks (DDOS) [Kanich et al. 2008], where multiple worm infected computers try to exhaust the system resources or the available network bandwith of a target in a coordinated manner. Virus. “A virus is a piece of code that adds itself to other programs, including operating systems. It cannot run ind ...
... attacks (DDOS) [Kanich et al. 2008], where multiple worm infected computers try to exhaust the system resources or the available network bandwith of a target in a coordinated manner. Virus. “A virus is a piece of code that adds itself to other programs, including operating systems. It cannot run ind ...
Configuration Quick Start Guidelines Summary
... appropriate voltage operating ranges. In this example, using a 5V, 3.3V, and 2.5V device in a single JTAG chain, although not as typical, allows consideration for a mixed voltage chain to be discussed. To accommodate both the XC9500 (5V) and XC9500XV (2.5V) devices, the VCCIO signals should be tied ...
... appropriate voltage operating ranges. In this example, using a 5V, 3.3V, and 2.5V device in a single JTAG chain, although not as typical, allows consideration for a mixed voltage chain to be discussed. To accommodate both the XC9500 (5V) and XC9500XV (2.5V) devices, the VCCIO signals should be tied ...
Chapter 1
... 13. A proprietary control system allows the system to be connected easily to devices and programs made by other manufacturers. ANS: 14. A PLC uses an optical isolator to electrically isolate the internal components from the input and output terminals. ANS: MULTIPLE CHOICE 1. A _______ PLC applicati ...
... 13. A proprietary control system allows the system to be connected easily to devices and programs made by other manufacturers. ANS: 14. A PLC uses an optical isolator to electrically isolate the internal components from the input and output terminals. ANS: MULTIPLE CHOICE 1. A _______ PLC applicati ...
Basic PLC 1
... The main function of the microprocessor is to analyze data coming from field sensors through input modules, make decisions based on the user’s defined control program and return signal back through output modules to the field devices. Field sensors: switches, flow, level, pressure, temp. transmitter ...
... The main function of the microprocessor is to analyze data coming from field sensors through input modules, make decisions based on the user’s defined control program and return signal back through output modules to the field devices. Field sensors: switches, flow, level, pressure, temp. transmitter ...
- University of Huddersfield Repository
... works, for example graphs and tables (“Reproductions”), which may be described in this thesis, may not be owned by the author and may be owned by third parties. Such Intellectual Property Rights and Reproductions cannot and must not be made available for use without the prior written permission of t ...
... works, for example graphs and tables (“Reproductions”), which may be described in this thesis, may not be owned by the author and may be owned by third parties. Such Intellectual Property Rights and Reproductions cannot and must not be made available for use without the prior written permission of t ...
Apple Remote Desktop Administrator`s Guide
... Before performing remote installations, you can send an ARD text message to notify users, perhaps letting them know that you’ll be using ARD to lock their screens at a particular time before you start the installation. Using Network Install Images You can also distribute and install software, includ ...
... Before performing remote installations, you can send an ARD text message to notify users, perhaps letting them know that you’ll be using ARD to lock their screens at a particular time before you start the installation. Using Network Install Images You can also distribute and install software, includ ...
Apple Remote Desktop Administrator’s Guide Version 2.2
... Before performing remote installations, you can send an ARD text message to notify users, perhaps letting them know that you’ll be using ARD to lock their screens at a particular time before you start the installation. Using Network Install Images You can also distribute and install software, includ ...
... Before performing remote installations, you can send an ARD text message to notify users, perhaps letting them know that you’ll be using ARD to lock their screens at a particular time before you start the installation. Using Network Install Images You can also distribute and install software, includ ...
Curry: A Tutorial Introduction
... variables it has done to compute this value. In general, there is more than one possibility to instantiate the arguments, e.g., the Boolean variables x and y can be instantiated to True or False. This leads to different solutions which are printed one after the other as shown above: there is one ins ...
... variables it has done to compute this value. In general, there is more than one possibility to instantiate the arguments, e.g., the Boolean variables x and y can be instantiated to True or False. This leads to different solutions which are printed one after the other as shown above: there is one ins ...
the Experience Developing Operating
... Further details of the design of the RP3 PME and system organuation can be found in [1] and [6]. RP3x, our working64-way prototype, differed from the published design in the following respects: . The I/O and Support Processors, or ISP's, in RP3x were simple IBM PC/AT's rather than the elaborate cust ...
... Further details of the design of the RP3 PME and system organuation can be found in [1] and [6]. RP3x, our working64-way prototype, differed from the published design in the following respects: . The I/O and Support Processors, or ISP's, in RP3x were simple IBM PC/AT's rather than the elaborate cust ...
Lenovo - Product Review
... • Use a quality carrying case that provides adequate cushioning and protection. • Do not pack your computer in a tightly packed suitcase or bag. • Before putting your computer in a carrying case, make sure that it is off, in sleep mode, or in hibernation mode. Do not put a computer in a carrying cas ...
... • Use a quality carrying case that provides adequate cushioning and protection. • Do not pack your computer in a tightly packed suitcase or bag. • Before putting your computer in a carrying case, make sure that it is off, in sleep mode, or in hibernation mode. Do not put a computer in a carrying cas ...
... No other generation in history has been able to lavish twelve, sixteen, or even twenty years on the education of its young, (nor been as little satisfied with the result). As recently as a hundred years ago, only a tiny elite could aspire to such an indulgence. For most that much time would have rep ...
DOWNLOAD computer fundamentals by anita goel full
... Tablet Computer has features of the notebook computer but it can accept input from a stylus or a pen instead of the keyboard or mouse. It is a portable computer. Tablet computer are the new kind of PCs. Handheld Computer or Personal Digital Assistant (PDA) is a small computer that can be held on the ...
... Tablet Computer has features of the notebook computer but it can accept input from a stylus or a pen instead of the keyboard or mouse. It is a portable computer. Tablet computer are the new kind of PCs. Handheld Computer or Personal Digital Assistant (PDA) is a small computer that can be held on the ...
PDF - Picaxe
... Using LEDs. LEDs only require a small amount of current to work, which makes them much more efficient than bulbs (this means, for instance, that if powered by batteries the LEDs will light for a much longer time than a bulb would). If too much current is passed through an LED it will be damaged, and ...
... Using LEDs. LEDs only require a small amount of current to work, which makes them much more efficient than bulbs (this means, for instance, that if powered by batteries the LEDs will light for a much longer time than a bulb would). If too much current is passed through an LED it will be damaged, and ...
answers to problems
... able to define program modules, and to create, destroy, and alter the size of modules dynamically. Protection and access control: Sharing of memory, at any level of the memory hierarchy, creates the potential for one program to address the memory space of another. This is desirable when sharing is n ...
... able to define program modules, and to create, destroy, and alter the size of modules dynamically. Protection and access control: Sharing of memory, at any level of the memory hierarchy, creates the potential for one program to address the memory space of another. This is desirable when sharing is n ...
operating- system concepts
... through the computer as a group by an operator or automatic job sequencer. Performance is increased by attempting to keep CPU and I/O devices busy at all times through buffering, off-line operation, spooling, and multiprogramming. Batch is good for executing large jobs that need little interaction; ...
... through the computer as a group by an operator or automatic job sequencer. Performance is increased by attempting to keep CPU and I/O devices busy at all times through buffering, off-line operation, spooling, and multiprogramming. Batch is good for executing large jobs that need little interaction; ...
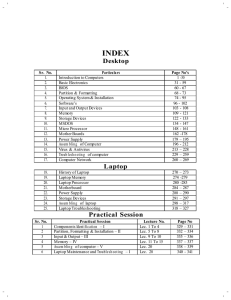
View Hardware - Itech Computer Education
... performs calculations. Hardware items such as your monitor, ke yboard, mouse, printer, and other items are often called hardware devices, or devices. Software refers to the instructions, or programs, that tell the hardware what to do. A word process ing program that you can use to write letters on y ...
... performs calculations. Hardware items such as your monitor, ke yboard, mouse, printer, and other items are often called hardware devices, or devices. Software refers to the instructions, or programs, that tell the hardware what to do. A word process ing program that you can use to write letters on y ...
AVR ISP Userguide
... When AVR Studio is scanning for connected devices, it searches through the COM ports in a sequential manner. The first device encountered, will gain control over the COM port. It is not possible to control both, a STK500 and an AVRISP, from AVR Studio simultaneously. To do this two instances of AVR ...
... When AVR Studio is scanning for connected devices, it searches through the COM ports in a sequential manner. The first device encountered, will gain control over the COM port. It is not possible to control both, a STK500 and an AVRISP, from AVR Studio simultaneously. To do this two instances of AVR ...
Examensarbete utfört i Datorteknik av Fredrik Sandvik och Olle Tingstam LiTH-ISY-EX--15/4891--SE Linköping 2015
... terms of hardware and embedded software, which incorporates support to implement new state-ofthe-art functions. The platform must support a wide range of contactors from basic ones with only core functions to advanced contactors using modern microcontrollers to provide efficient, quick and reliable ...
... terms of hardware and embedded software, which incorporates support to implement new state-ofthe-art functions. The platform must support a wide range of contactors from basic ones with only core functions to advanced contactors using modern microcontrollers to provide efficient, quick and reliable ...
Document
... memory, memory positions become available for reading on a sequential fashion. Therefore to read an specific memory position, the reader must wait a variable time delay for the memory position to became available. In principle, in a RAM, all positions of the memory can be read on a random fashion wi ...
... memory, memory positions become available for reading on a sequential fashion. Therefore to read an specific memory position, the reader must wait a variable time delay for the memory position to became available. In principle, in a RAM, all positions of the memory can be read on a random fashion wi ...
Teaching Guide 6
... Today computer science is an academic subject in its own right, governed by scientific and mathematical principles. Due to its increasing importance, computer studies have become an essential part of the education curriculum around the world, including in Pakistan. However, the trend has been to fav ...
... Today computer science is an academic subject in its own right, governed by scientific and mathematical principles. Due to its increasing importance, computer studies have become an essential part of the education curriculum around the world, including in Pakistan. However, the trend has been to fav ...
Test Plan1
... The power supply should be tested to ensure correct input voltage for each device. How: The power supply circuit should first be simulated using Cadence Pspice. The circuitry should be built and applied to the RFID system. Specific points in the circuit should be tested to ensure proper input voltag ...
... The power supply should be tested to ensure correct input voltage for each device. How: The power supply circuit should first be simulated using Cadence Pspice. The circuitry should be built and applied to the RFID system. Specific points in the circuit should be tested to ensure proper input voltag ...
Example Connection between USB Host and Android
... This is the format of developing program that is Application for external devices; so, Android device can communicate and command various Input/output with external devices. In this case, user can apply cheap Android devices in the market for many applications; it seems to increase unlimited Input/O ...
... This is the format of developing program that is Application for external devices; so, Android device can communicate and command various Input/output with external devices. In this case, user can apply cheap Android devices in the market for many applications; it seems to increase unlimited Input/O ...
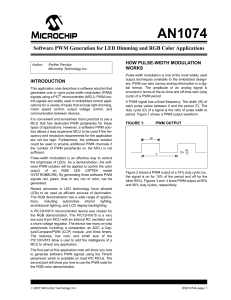
AN1074 - EE Times Asia
... Red, Green and Blue LED emitters have different luminous efficiencies as they do not generate the same luminous intensity given the same input current. Also, the forward voltage across each LED changes so that the amount of current across each LED will be different given the same series resistor val ...
... Red, Green and Blue LED emitters have different luminous efficiencies as they do not generate the same luminous intensity given the same input current. Also, the forward voltage across each LED changes so that the amount of current across each LED will be different given the same series resistor val ...
chapter quiz
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Advanced Engine Performance Diagnosis, 4/e By James D. Halderman ...
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Advanced Engine Performance Diagnosis, 4/e By James D. Halderman ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.