chapter quiz
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Advanced Engine Performance Diagnosis, 4/e By James D. Halderman ...
... 4. Computer input sensors include engine speed (RPM), MAP, MAF, ECT, O2S, TP, and VS. 5. A computer can only turn a device on or turn a device off, but it can do the operation very rapidly. Advanced Engine Performance Diagnosis, 4/e By James D. Halderman ...
Econometric Software: The first Fifty Years in Perspective*
... -4Surprising as it sometimes seems to those who have spent years working with computers, we are still in the early days of econometric computing. The first development of software was essentially an outgrowth of the local needs of particular research projects. During the period prior to 1985, there ...
... -4Surprising as it sometimes seems to those who have spent years working with computers, we are still in the early days of econometric computing. The first development of software was essentially an outgrowth of the local needs of particular research projects. During the period prior to 1985, there ...
Recitation 10 Threads
... Both terms describe interleaving operations to make it appear that multiple things are happening in parallel ...
... Both terms describe interleaving operations to make it appear that multiple things are happening in parallel ...
TOSHIBA PORTÉGÉ Z930/Satellite Z930 Series
... the interference by one or more of the following measures: Reorient or relocate the receiving antenna. Increase the separation between the equipment and receiver. Connect the equipment into an outlet on a circuit different from that to which the receiver is connected. Consult the dealer or an experi ...
... the interference by one or more of the following measures: Reorient or relocate the receiving antenna. Increase the separation between the equipment and receiver. Connect the equipment into an outlet on a circuit different from that to which the receiver is connected. Consult the dealer or an experi ...
Course Syllabus for Advanced PC Configuration
... Students are strongly encouraged to build (or obtain) a PC during the scope of this class, and to use that PC to learn about the highly technical aspects of PC configuration and troubleshooting. There will be numerous opportunities to test non-working and problematic computers, but the student may n ...
... Students are strongly encouraged to build (or obtain) a PC during the scope of this class, and to use that PC to learn about the highly technical aspects of PC configuration and troubleshooting. There will be numerous opportunities to test non-working and problematic computers, but the student may n ...
Click here
... FIGURE 22-8 Typical headlight circuit diagram. Note that the headlight switch is represented by a dotted outline indicating that other circuits (such as dash lights) also operate from the switch. ...
... FIGURE 22-8 Typical headlight circuit diagram. Note that the headlight switch is represented by a dotted outline indicating that other circuits (such as dash lights) also operate from the switch. ...
Computer Engineering Technology - Florida Department Of Education
... engineer; provides technical skill proficiency, and includes competency-based applied learning that contributes to the academic knowledge, higherorder reasoning and problem-solving skills, work attitudes, general employability skills, technical skills, and occupation-specific skills, and knowledge o ...
... engineer; provides technical skill proficiency, and includes competency-based applied learning that contributes to the academic knowledge, higherorder reasoning and problem-solving skills, work attitudes, general employability skills, technical skills, and occupation-specific skills, and knowledge o ...
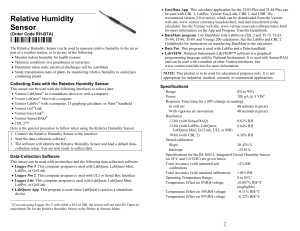
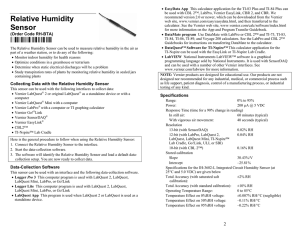
Relative Humidity Sensor
... cases, you may want to create air currents (by moving the sensor or using a fan) to speed up the response of the sensor. The sensor is slightly light sensitive. The housing is designed to minimize the amount of light that can penetrate the sensor opening. The calibration of the sensor is somewhat af ...
... cases, you may want to create air currents (by moving the sensor or using a fan) to speed up the response of the sensor. The sensor is slightly light sensitive. The housing is designed to minimize the amount of light that can penetrate the sensor opening. The calibration of the sensor is somewhat af ...
Computer Science Programming Basics with Ruby
... another computer science course. If that is the case, this book provides them with an overview of the field and an understanding of at least one popular programming lan‐ guage that happens to be useful from both a practical and a pedagogical standpoint. Concepts taught in this book provide students ...
... another computer science course. If that is the case, this book provides them with an overview of the field and an understanding of at least one popular programming lan‐ guage that happens to be useful from both a practical and a pedagogical standpoint. Concepts taught in this book provide students ...
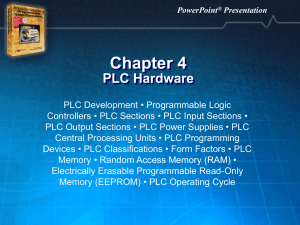
Chapter 4 — PLC Hardware - benchmark
... signals to the voltage level required by the CPU, and the internal circuitry of an output section converts signals from the CPU to the voltage level required by output devices. ...
... signals to the voltage level required by the CPU, and the internal circuitry of an output section converts signals from the CPU to the voltage level required by output devices. ...
Network Layer
... the destinations to determine the set of output lines for forwarding the packet. An output line is selected if it is the best route to at least one of the destinations. The router generates a new copy of the packet for selected output line, with a set of destinations that are to use the line. ...
... the destinations to determine the set of output lines for forwarding the packet. An output line is selected if it is the best route to at least one of the destinations. The router generates a new copy of the packet for selected output line, with a set of destinations that are to use the line. ...
B.Tech Course Syllabus
... Algorithm Complexity and Time-Space trade-off Arrays: Array Definition, Representation and Analysis, Single and Multidimensional Arrays, address calculation, application of arrays, Character String in C++, Character string operation, Array as Parameters, Ordered List, Sparse Matrices and Vectors. St ...
... Algorithm Complexity and Time-Space trade-off Arrays: Array Definition, Representation and Analysis, Single and Multidimensional Arrays, address calculation, application of arrays, Character String in C++, Character string operation, Array as Parameters, Ordered List, Sparse Matrices and Vectors. St ...
Relative Humidity Sensor
... error, you can create different calibration files for different temperatures. In most cases, this is unnecessary. This sensor is equipped with circuitry that supports auto-ID. When used with LabQuest 2, LabQuest, LabQuest Mini, LabPro, Go! Link, SensorDAQ, EasyLink, TI-Nspire™ Lab Cradle, or CBL 2™, ...
... error, you can create different calibration files for different temperatures. In most cases, this is unnecessary. This sensor is equipped with circuitry that supports auto-ID. When used with LabQuest 2, LabQuest, LabQuest Mini, LabPro, Go! Link, SensorDAQ, EasyLink, TI-Nspire™ Lab Cradle, or CBL 2™, ...
course-file-distributed-system
... computational entities are called computers or nodes. A distributed system may have a common goal, such as solving a large computational problem. Alternatively, each computer may have its own user with individual needs, and the purpose of the distributed system is to coordinate the use of shared res ...
... computational entities are called computers or nodes. A distributed system may have a common goal, such as solving a large computational problem. Alternatively, each computer may have its own user with individual needs, and the purpose of the distributed system is to coordinate the use of shared res ...
pipemaster - Magnatech LLC
... preferred for weld Heads making simple fusion welds. Multipass pipe weld Heads are operated using position-based programming, eliminating calculations to determine when parameter changes must be made. A sensor in the weld Head provides position information. All welding parameters may be changed at e ...
... preferred for weld Heads making simple fusion welds. Multipass pipe weld Heads are operated using position-based programming, eliminating calculations to determine when parameter changes must be made. A sensor in the weld Head provides position information. All welding parameters may be changed at e ...
ITE_PC_v40_Chapter1
... Electrically erasable EEPROM programmable read-only memory ITE PC v4.0 Chapter 1 ...
... Electrically erasable EEPROM programmable read-only memory ITE PC v4.0 Chapter 1 ...
6.6 Malicious Code Protection
... Malicious codes protection typically is provided at two places in the architecture: at the gateway and at workstations that access information services. Malicious code can infiltrate and destroy data through network connections if allowed beyond the gateway or through individual user workstations. T ...
... Malicious codes protection typically is provided at two places in the architecture: at the gateway and at workstations that access information services. Malicious code can infiltrate and destroy data through network connections if allowed beyond the gateway or through individual user workstations. T ...
doctorfeda.files.wordpress.com
... Serial ATA is a serial link -- a single cable with a minimum of four wires creates a point-to-point connection between devices. Transfer rates for Serial ATA begin at 150MBps. One of the main design advantages of Serial ATA is that the thinner serial cables facilitate more efficient airflow inside a ...
... Serial ATA is a serial link -- a single cable with a minimum of four wires creates a point-to-point connection between devices. Transfer rates for Serial ATA begin at 150MBps. One of the main design advantages of Serial ATA is that the thinner serial cables facilitate more efficient airflow inside a ...
ppt - EECS Instructional Support Group Home Page
... CS61C: So what's in it for me? ° Learn some of the big ideas in CS & engineering: • 5 Classic components of a Computer • Data can be anything (integers, floating point, characters): a program determines what it is • Stored program concept: instructions just data • Principle of Locality, exploited v ...
... CS61C: So what's in it for me? ° Learn some of the big ideas in CS & engineering: • 5 Classic components of a Computer • Data can be anything (integers, floating point, characters): a program determines what it is • Stored program concept: instructions just data • Principle of Locality, exploited v ...
AVR910: In-System Programming
... example, where two consecutive commands are sent to the target. Notice how all bytes returned equal the bytes just received. Some commands return one byte from the target’s memory. This byte is always returned in the last byte (byte 4). Data is always sent on MOSI and MISO lines with the most signif ...
... example, where two consecutive commands are sent to the target. Notice how all bytes returned equal the bytes just received. Some commands return one byte from the target’s memory. This byte is always returned in the last byte (byte 4). Data is always sent on MOSI and MISO lines with the most signif ...
ANSI C Programming study guide
... Operating systems that permit each user to run multiple programs are referred to as both multiprogrammed and multitasking systems. Multiuser systems are able to handle multiple users concurrently. The output produced by the compiler is called an object program, which is a machine language ver ...
... Operating systems that permit each user to run multiple programs are referred to as both multiprogrammed and multitasking systems. Multiuser systems are able to handle multiple users concurrently. The output produced by the compiler is called an object program, which is a machine language ver ...
Effective
... Host-based malware detectors have the advantage that they can observe the complete set of actions that a malware program performs. It is even possible to identify malicious code before it is executed at all. Unfortunately, current host-based detection approaches have significant shortcomings. An impo ...
... Host-based malware detectors have the advantage that they can observe the complete set of actions that a malware program performs. It is even possible to identify malicious code before it is executed at all. Unfortunately, current host-based detection approaches have significant shortcomings. An impo ...
OMS JDM - One Byte CPU
... circuit serial programmer. It only produces enough power to adequately power the PIC chip by itself. Ideally, you should arrange to have the PIC placed in a board specifically designed for programming or development with PIC chips. In such cases, make sure the power, if any, is disconnected and that ...
... circuit serial programmer. It only produces enough power to adequately power the PIC chip by itself. Ideally, you should arrange to have the PIC placed in a board specifically designed for programming or development with PIC chips. In such cases, make sure the power, if any, is disconnected and that ...
Overview of Computer Science - CSE User Home Pages
... at the University of Minnesota-Twin Cities. More information about that class and these notes are in the opening chapter. The original version of these notes was used in the Spring 2014 offering of that class. This current version, Version 1.2, is a small update, containing some minor clarifications ...
... at the University of Minnesota-Twin Cities. More information about that class and these notes are in the opening chapter. The original version of these notes was used in the Spring 2014 offering of that class. This current version, Version 1.2, is a small update, containing some minor clarifications ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.