GNU/Linux Basic - Free Technology Academy
... reluctant to adopt it, GNU/Linux has proven to be up to the task as well as any other operating system in existence. The objective of this course is to introduce us to the world of GNU/Linux. It will also provide us with the keys to understanding the philosophy of free software, teaching us how to u ...
... reluctant to adopt it, GNU/Linux has proven to be up to the task as well as any other operating system in existence. The objective of this course is to introduce us to the world of GNU/Linux. It will also provide us with the keys to understanding the philosophy of free software, teaching us how to u ...
maclnkum
... MACREL (MACro-RELocatable) is a PDP/8 based assembler that allows you to write a program using macro coding and relocatable program sections. Macros are generalized instruction sequences that can, if desired, be modified by arguments (data) when the macro is used. Relocatable program sections allow ...
... MACREL (MACro-RELocatable) is a PDP/8 based assembler that allows you to write a program using macro coding and relocatable program sections. Macros are generalized instruction sequences that can, if desired, be modified by arguments (data) when the macro is used. Relocatable program sections allow ...
Arduino & E-Health/M
... Where( can you ) to get (obtain) Hardware & Software? (rhtaorical) How can I get? ...
... Where( can you ) to get (obtain) Hardware & Software? (rhtaorical) How can I get? ...
E2600 Manual
... Chapter 7: Using Your Software. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63 Adjusting the volume . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64 Playing music and movies . . . . . . . . . . . . . . ...
... Chapter 7: Using Your Software. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63 Adjusting the volume . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64 Playing music and movies . . . . . . . . . . . . . . ...
View PDF - CiteSeerX
... Software is at the heart of the development of information and communication technologies (ICTs). It engages with a system of communication in which it is embedded and gives meaning to this sytem through its implementation. This feature denotes that ICTs are particularly mobile and mutable compared ...
... Software is at the heart of the development of information and communication technologies (ICTs). It engages with a system of communication in which it is embedded and gives meaning to this sytem through its implementation. This feature denotes that ICTs are particularly mobile and mutable compared ...
the ZoneAlarm User Manual. - Clear Creek Communications
... © 2009 Check Point Software Technologies Ltd. All rights reserved. This product and related documentation are protected by copyright and distributed under licensing restricting their use, copying, distribution, and decompilation. No part of this product or related documentation may be reproduced i ...
... © 2009 Check Point Software Technologies Ltd. All rights reserved. This product and related documentation are protected by copyright and distributed under licensing restricting their use, copying, distribution, and decompilation. No part of this product or related documentation may be reproduced i ...
The Quest for Artificial Intelligence
... publisher, Cambridge University Press, in February 2009. Some things still need to be added, such as dates associated with people. (The stand-ins for some of these are now written as “19[[xx]]– ”.) Also, I need to get permissions for most of the illustrations and photographs. (The sources for the fi ...
... publisher, Cambridge University Press, in February 2009. Some things still need to be added, such as dates associated with people. (The stand-ins for some of these are now written as “19[[xx]]– ”.) Also, I need to get permissions for most of the illustrations and photographs. (The sources for the fi ...
Unix and Linux System Administration and Shell
... The shell is extremely useful for programming. Even when a programmer uses a graphical integrated development environment (IDE), the programmer is likely to still heavily use the shell for programming support. Some IDEs even have shell access built-in. Shell scripts are widely used by system ...
... The shell is extremely useful for programming. Even when a programmer uses a graphical integrated development environment (IDE), the programmer is likely to still heavily use the shell for programming support. Some IDEs even have shell access built-in. Shell scripts are widely used by system ...
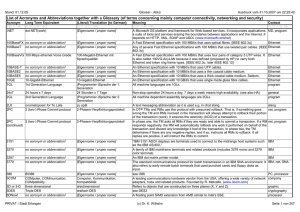
List of Acronyms and Abbreviations together with a Glossary (of
... In DTP TMs and RMs use this protocol with presumed rollback. That is, if something goes wrong the TM and RMs involved in the transaction will always attempt to rollback their portion of the transaction (work). It ensures the atomicity (ACID) of a transaction. In phase one, the TM asks all RMs if the ...
... In DTP TMs and RMs use this protocol with presumed rollback. That is, if something goes wrong the TM and RMs involved in the transaction will always attempt to rollback their portion of the transaction (work). It ensures the atomicity (ACID) of a transaction. In phase one, the TM asks all RMs if the ...
v7 user manual
... There are a few pre-installation checks you should run through before you install AB Tutor to make sure that the software runs correctly: 1. For installing, activating the software and for setting and changing passwords you need administrative rights on the tutor and the student computers. 2. You ha ...
... There are a few pre-installation checks you should run through before you install AB Tutor to make sure that the software runs correctly: 1. For installing, activating the software and for setting and changing passwords you need administrative rights on the tutor and the student computers. 2. You ha ...
Inside Mac OS X: System Overview
... Inside Mac OS X: System Overview is intended for anyone who wants to develop software for Mac OS X. But it is also a resource for people who are just curious about Mac OS X as a development and deployment platform. Whether your background is software development for Mac OS 9, UNIX, Windows, Java, or ...
... Inside Mac OS X: System Overview is intended for anyone who wants to develop software for Mac OS X. But it is also a resource for people who are just curious about Mac OS X as a development and deployment platform. Whether your background is software development for Mac OS 9, UNIX, Windows, Java, or ...
Assembly Language for the 68000 Family
... form of text editor. It really doesn’t matter which editor you use as long as you can create a source file for input to the assembler. An assembler is similar to a compiler in that it “translates” a source language into machine language. The output from an assembler is called the object code. Normal ...
... form of text editor. It really doesn’t matter which editor you use as long as you can create a source file for input to the assembler. An assembler is similar to a compiler in that it “translates” a source language into machine language. The output from an assembler is called the object code. Normal ...
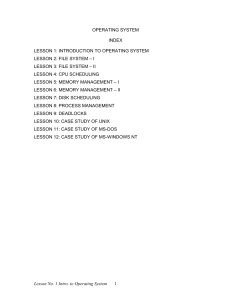
Operating System - Directorate of Distance Education
... resources that must be managed by the OS & using the process viewpoint, we indicate when the corresponding resource manager comes into play. We now answer the question, “How are these resource managers activated, & where do they reside?” Does memory manager ever invoke the process scheduler? Does sc ...
... resources that must be managed by the OS & using the process viewpoint, we indicate when the corresponding resource manager comes into play. We now answer the question, “How are these resource managers activated, & where do they reside?” Does memory manager ever invoke the process scheduler? Does sc ...
Bit
... series of letters, numbers and/or symbols by which the Internet identifies you or a location where information is stored. Through the use of addresses people can send you e-mail, look at your Web site, and send or receive information. As an e-mail identifier it looks something like username@hostname ...
... series of letters, numbers and/or symbols by which the Internet identifies you or a location where information is stored. Through the use of addresses people can send you e-mail, look at your Web site, and send or receive information. As an e-mail identifier it looks something like username@hostname ...
A Guidebook In pc Hardware, Maintenance And repair
... Identify major components and sub-systems of an IBM-class microcomputer by visual examination alone; Understand what takes place with the computer's hardware when the computer operates in a normal fashion; Use diagnostic and evaluation software (such as Checkit or Norton Utilities) to analyze or tro ...
... Identify major components and sub-systems of an IBM-class microcomputer by visual examination alone; Understand what takes place with the computer's hardware when the computer operates in a normal fashion; Use diagnostic and evaluation software (such as Checkit or Norton Utilities) to analyze or tro ...
eBook - Seeing this instead of the website you expected?
... programmers never learn, and we'll see how to use them to create simple and elegant solutions to programming problems. For example, one recurring theme in the book is the concept of a monoid. It turns out that monoids (more than, for example, groups and semigroups) are ubiquitous in the data types ...
... programmers never learn, and we'll see how to use them to create simple and elegant solutions to programming problems. For example, one recurring theme in the book is the concept of a monoid. It turns out that monoids (more than, for example, groups and semigroups) are ubiquitous in the data types ...
Management of Object-Oriented Action
... This thesis addresses the problem of managing the runtime behaviour of distributed programs. The thesis of this work is that management is fundamentally an information processing activity and that the object model, as applied to actionbased distributed systems and database systems, is an appropriate ...
... This thesis addresses the problem of managing the runtime behaviour of distributed programs. The thesis of this work is that management is fundamentally an information processing activity and that the object model, as applied to actionbased distributed systems and database systems, is an appropriate ...
Inside Mac OS X: System Overview
... revolutionary operating system to hit the computer scene in many years. With Mac OS X, Apple is reasserting its leadership not only in operating systems but in the technological sophistication and design sensibility that are the hallmarks of the company. While preserving the famed ease-of-use and pe ...
... revolutionary operating system to hit the computer scene in many years. With Mac OS X, Apple is reasserting its leadership not only in operating systems but in the technological sophistication and design sensibility that are the hallmarks of the company. While preserving the famed ease-of-use and pe ...
A novel methodology for dynamically reconfigurable embedded
... Configurable FPGA-Based Hardware Architecture for Adaptive Processing of Noisy Signals for Target Detection based on Constant False Alarm Rate (CFAR) Algorithms . ...
... Configurable FPGA-Based Hardware Architecture for Adaptive Processing of Noisy Signals for Target Detection based on Constant False Alarm Rate (CFAR) Algorithms . ...
Software Performance Estimation Methods for System
... by annotating application source code with timing information. We developed a SLS approach called SciSim (Source code instrumentation based Simulation). Compared to other existing SLS approaches, SciSim allows for more accurate performance simulation by taking important timing effects such as the p ...
... by annotating application source code with timing information. We developed a SLS approach called SciSim (Source code instrumentation based Simulation). Compared to other existing SLS approaches, SciSim allows for more accurate performance simulation by taking important timing effects such as the p ...
PDF
... Benchmarking has become one of the most important methods for quantitative performance evaluation of processor and computer system designs. Benchmarking of modern multiprocessors such as chip multiprocessors is challenging because of their application domain, scalability and parallelism requirements ...
... Benchmarking has become one of the most important methods for quantitative performance evaluation of processor and computer system designs. Benchmarking of modern multiprocessors such as chip multiprocessors is challenging because of their application domain, scalability and parallelism requirements ...
Python Programming : An Introduction to Computer
... 1.6 The Magic of Python . . . . 1.7 Inside a Python Program . . 1.8 Chaos and Computers . . . 1.9 Chapter Summary . . . . . 1.10 Exercises . . . . . . . . . . . ...
... 1.6 The Magic of Python . . . . 1.7 Inside a Python Program . . 1.8 Chaos and Computers . . . 1.9 Chapter Summary . . . . . 1.10 Exercises . . . . . . . . . . . ...
Secure Programming for Linux and Unix HOWTO
... This book provides a set of design and implementation guidelines for writing secure programs for Linux and Unix systems. Such programs include application programs used as viewers of remote data, web applications (including CGI scripts), network servers, and setuid/setgid programs. Specific guidelin ...
... This book provides a set of design and implementation guidelines for writing secure programs for Linux and Unix systems. Such programs include application programs used as viewers of remote data, web applications (including CGI scripts), network servers, and setuid/setgid programs. Specific guidelin ...
Building a Secure Computer System
... information from unauthorized disclosure, or information secrecy. You may find it disconcerting, as you read this book, that information integrity-protecting information from unauthorized modification or destruction-seems to be receiving no sustained attention. There are two reasons for this seeming ...
... information from unauthorized disclosure, or information secrecy. You may find it disconcerting, as you read this book, that information integrity-protecting information from unauthorized modification or destruction-seems to be receiving no sustained attention. There are two reasons for this seeming ...
software takes command - Software Studies Initiative
... not included considerations of software in their overwise highly influential accounts of modern media and technology. In the present decade, the number of students in media art, design, architecture, and humanities who use programming or scripting in their work has grown substantially – at least in ...
... not included considerations of software in their overwise highly influential accounts of modern media and technology. In the present decade, the number of students in media art, design, architecture, and humanities who use programming or scripting in their work has grown substantially – at least in ...
Computer program

A computer program or app is a sequence of instructions, written to perform a specified task on a computer. A computer requires programs to function, typically executing the program's instructions in a central processor. The program has an executable form that the computer can use directly to execute the instructions. The same program in its human-readable source code form, from which executable programs are derived (e.g., compiled), enables a programmer to study and develop its algorithms. A collection of computer programs and related data is referred to as the software.Computer source code is typically written by computer programmers. Source code is written in a programming language that usually follows one of two main paradigms: imperative or declarative programming. Source code may be converted into an executable file (sometimes called an executable program or a binary) by a compiler and later executed by a central processing unit. Alternatively, computer programs may be executed with the aid of an interpreter, or may be embedded directly into hardware.Computer programs may be ranked along functional lines: system software and application software. Two or more computer programs may run simultaneously on one computer from the perspective of the user, this process being known as multitasking.A computer program can be deemed an industrial or commercial product when that is useful for the concerns of a business model, which involves such aspects as labor, markets, profitability, and quality-control. This is how most proprietary software is classified, though open-source software can also be regarded as a product if a commercial entity specializes in it; e.g. Red Hat, Inc. or SUSE, as both which develop and maintain open-source software products.