Import Settings:
... 28. Describe how Mac OS X is considered a hybrid system. 29. Describe how Android uses a unique virtual machine for running Java programs. True/False 30. KDE and GNOME desktops are available under open-source licenses. 31. Many operating system merge I/O devices and files into a combined file becaus ...
... 28. Describe how Mac OS X is considered a hybrid system. 29. Describe how Android uses a unique virtual machine for running Java programs. True/False 30. KDE and GNOME desktops are available under open-source licenses. 31. Many operating system merge I/O devices and files into a combined file becaus ...
NT Security Overview
... organization will have access to the network. In most businesses or organizations there are employees, staff, management and officers. Some can be trusted to access all of the network and others do not have the trust level to access any of the network. The administrator must decide who has access an ...
... organization will have access to the network. In most businesses or organizations there are employees, staff, management and officers. Some can be trusted to access all of the network and others do not have the trust level to access any of the network. The administrator must decide who has access an ...
monitor
... Block everything that is not explicitly allow Use host-based firewalls, port-filtering and scanning tools Configure services to limit remote remote access Disallow automatic software installation Move servers behaind the firewall unless required ...
... Block everything that is not explicitly allow Use host-based firewalls, port-filtering and scanning tools Configure services to limit remote remote access Disallow automatic software installation Move servers behaind the firewall unless required ...
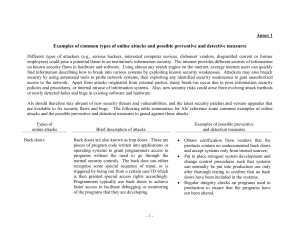
Annex 1
... Examples of common types of online attacks and possible preventive and detective measures Different types of attackers (e.g., serious hackers, interested computer novices, dishonest vendors, disgruntled current or former employees) could pose a potential threat to an institution's information securi ...
... Examples of common types of online attacks and possible preventive and detective measures Different types of attackers (e.g., serious hackers, interested computer novices, dishonest vendors, disgruntled current or former employees) could pose a potential threat to an institution's information securi ...
pdf
... • Requires memory protection hardware for isolation • Optimizes for response time at the cost of throughput ...
... • Requires memory protection hardware for isolation • Optimizes for response time at the cost of throughput ...
Chapter 8 Operating Systems and Utility Programs
... What are other program management features of operating systems? ...
... What are other program management features of operating systems? ...
CSC221 COMPUTER ORGANZIATION AND ASSEMBLY LANGUAGE
... What is an Operating System? • A program that acts as an intermediary between a user of a computer and the computer hardware.` • An operating system is a software that manages the computer hardware and provides basis for application programs. • The main goals of operating system are: • Execute user ...
... What is an Operating System? • A program that acts as an intermediary between a user of a computer and the computer hardware.` • An operating system is a software that manages the computer hardware and provides basis for application programs. • The main goals of operating system are: • Execute user ...
Support Notes for SUSE LINUX Enterprise Servers HP Part Number: 5900-0402
... has been installed. To use the USB mouse in the installed system, remove the file /etc/X11/xorg.conf and restart the X11 server. Note that if this is done, only the USB mouse will function and any iLO 2 vKVM mouse that has been configured, will be ignored. The vKVM mouse enabled in the Integrity Int ...
... has been installed. To use the USB mouse in the installed system, remove the file /etc/X11/xorg.conf and restart the X11 server. Note that if this is done, only the USB mouse will function and any iLO 2 vKVM mouse that has been configured, will be ignored. The vKVM mouse enabled in the Integrity Int ...
Bandura® Releases REACT™ Software to Integrate Internal
... security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providing a critical element of secure network architecture. PoliWall is an in‐line appliance (physical ...
... security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providing a critical element of secure network architecture. PoliWall is an in‐line appliance (physical ...
Unix History, and Background
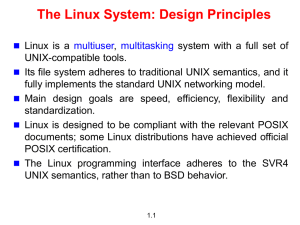
... compliant mechanisms, it can run software regardless of the actual variant used. • POSIX standard (1003) is administered by IEEE (Institute of Electrical and Electronics Engineers) • The standard is also recognized by the International Organization for Standardization ...
... compliant mechanisms, it can run software regardless of the actual variant used. • POSIX standard (1003) is administered by IEEE (Institute of Electrical and Electronics Engineers) • The standard is also recognized by the International Organization for Standardization ...
SECURITY
... information warfare of the information age. Information warfare is a war of decisions and control, a war of knowledge, and a war of intellect. The aim of information warfare will be gradually changed from ‘preserving oneself and wiping out the enemy’ to ‘preserving oneself and controlling the oppone ...
... information warfare of the information age. Information warfare is a war of decisions and control, a war of knowledge, and a war of intellect. The aim of information warfare will be gradually changed from ‘preserving oneself and wiping out the enemy’ to ‘preserving oneself and controlling the oppone ...
Introduction CS 239 Security for Networks and System
... • Processes belong to some domain – Can change domains, under careful restrictions • Only types available to that domain are accessible – And only in ways specified for that domain CS 236 Online ...
... • Processes belong to some domain – Can change domains, under careful restrictions • Only types available to that domain are accessible – And only in ways specified for that domain CS 236 Online ...
Introduction to Linux Winelfred G. Pasamba Dec 9, 2005 Finster Hall
... RedHat – one of the first most successful ...
... RedHat – one of the first most successful ...
Chapter 02: Operating System Overview
... • Multiple users simultaneously access the system through terminals ...
... • Multiple users simultaneously access the system through terminals ...
Word
... Software that supports multiple operating systems on a single computer. Each operating system is it’s own “virtual machine” with it’s own: ...
... Software that supports multiple operating systems on a single computer. Each operating system is it’s own “virtual machine” with it’s own: ...
DOCSpec
... Compare and Contrast the 3 platforms J2EE, .NET, and CORBA. Evaluate the three in 4 areas: databases, security, web services, and parallel processing/multi-threading. GOAL: To determine in which areas J2EE or .NET is better suited to be used. Also to determine in which areas CORBA can be beneficial. ...
... Compare and Contrast the 3 platforms J2EE, .NET, and CORBA. Evaluate the three in 4 areas: databases, security, web services, and parallel processing/multi-threading. GOAL: To determine in which areas J2EE or .NET is better suited to be used. Also to determine in which areas CORBA can be beneficial. ...
CS 377: Operating Systems Outline
... processors and on PC hardware, had extremely limited device-drive support, and supported only the Minix file system • Version 2.6.34 (Summer 2010): most common OS for servers, supports dozens of file systems, runs on anything from cell phones to super computers ...
... processors and on PC hardware, had extremely limited device-drive support, and supported only the Minix file system • Version 2.6.34 (Summer 2010): most common OS for servers, supports dozens of file systems, runs on anything from cell phones to super computers ...
the case for embedded linux
... Linux Hits Prime Time The Linux operating system has received a lot of Press lately as an alternative to Microsoft Windows. However, it has also found a place in the network applications, acting as an office router, Internet firewall or as web and mail servers. Several Internet service providers hav ...
... Linux Hits Prime Time The Linux operating system has received a lot of Press lately as an alternative to Microsoft Windows. However, it has also found a place in the network applications, acting as an office router, Internet firewall or as web and mail servers. Several Internet service providers hav ...
Course Syllabus
... This course will cover the basic principles of operating system design and implementation. Concurrent processes, inter-process communication, job and process scheduling; deadlock. Issues in memory management (virtual memory, segmentation, and paging) and auxiliary storage management (file systems, d ...
... This course will cover the basic principles of operating system design and implementation. Concurrent processes, inter-process communication, job and process scheduling; deadlock. Issues in memory management (virtual memory, segmentation, and paging) and auxiliary storage management (file systems, d ...
Unit OS1: The Evolution of Operating Systems
... These materials are part of the Windows Operating System Internals Curriculum Development Kit, developed by David A. Solomon and Mark E. Russinovich with Andreas Polze Microsoft has licensed these materials from David Solomon Expert Seminars, Inc. for distribution to academic organizations solely fo ...
... These materials are part of the Windows Operating System Internals Curriculum Development Kit, developed by David A. Solomon and Mark E. Russinovich with Andreas Polze Microsoft has licensed these materials from David Solomon Expert Seminars, Inc. for distribution to academic organizations solely fo ...
Operating System Overview
... • Multiple users simultaneously access the system through terminals ...
... • Multiple users simultaneously access the system through terminals ...
Are Clouds Secure? - San Francisco Bay Area ISSA Chapter
... logs logs that may be • Monitor application available – No standard vulnerabilities using your preferred tool ...
... logs logs that may be • Monitor application available – No standard vulnerabilities using your preferred tool ...