Quick History of Open Source
... Unix History Continued… • Ken Thomson created a new language ‘B’and rewrote the whole Unix code in this high level language • Dennis Ritchie shifted the inadequacies of B and modified it to a new language ‘C’ • By mid 80s there were more than a hundred thousand Unix installations running on anythin ...
... Unix History Continued… • Ken Thomson created a new language ‘B’and rewrote the whole Unix code in this high level language • Dennis Ritchie shifted the inadequacies of B and modified it to a new language ‘C’ • By mid 80s there were more than a hundred thousand Unix installations running on anythin ...
Network Security
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
No Slide Title
... • Reads the contents of a file from disk into memory. • Sends a document to the printer and activates the ...
... • Reads the contents of a file from disk into memory. • Sends a document to the printer and activates the ...
Introduction to Operating System Concepts Free books Specialist
... different types of operating systems (Windows, Mac OS X, Unix, GNU/Linux) - many variations of all these ...
... different types of operating systems (Windows, Mac OS X, Unix, GNU/Linux) - many variations of all these ...
What is Penetration Testing?
... Often, several of these testing techniques are used together to gain more comprehensive assessment of the overall network security posture. ...
... Often, several of these testing techniques are used together to gain more comprehensive assessment of the overall network security posture. ...
D`Amo - softfarm
... Federal Information Processing Standard (FIPS) is a set of standards required by the United States Federal Government for use in computer systems used by government agencies and contractors. • Well-known FIPS standards include the Data Encryption Standard (DES) and the Advanced Encryption Standard ( ...
... Federal Information Processing Standard (FIPS) is a set of standards required by the United States Federal Government for use in computer systems used by government agencies and contractors. • Well-known FIPS standards include the Data Encryption Standard (DES) and the Advanced Encryption Standard ( ...
Chapter 6
... task, usually related to managing or maintaining the system. Many utilities are built into operating systems as well as being available as standalone programs. File management programs—allow you to look at and manage the files stored on your PC (copy, move, organize into folders, etc.). Antivirus pr ...
... task, usually related to managing or maintaining the system. Many utilities are built into operating systems as well as being available as standalone programs. File management programs—allow you to look at and manage the files stored on your PC (copy, move, organize into folders, etc.). Antivirus pr ...
Q10 Study Guide - FSU Computer Science
... a. It provides security at the data-link layer. b. It is a simple protocol with limited options. c. It is commonly used for secure communication on the Internet. d. It was designed by Microsoft. ESSAY QUESTIONS (will not be on quiz but good exam questions) 1. What are the four levels of security mea ...
... a. It provides security at the data-link layer. b. It is a simple protocol with limited options. c. It is commonly used for secure communication on the Internet. d. It was designed by Microsoft. ESSAY QUESTIONS (will not be on quiz but good exam questions) 1. What are the four levels of security mea ...
virtual machine
... – OS should take the appropriate action to ensure correct and consistent computing – OS should provide debugging facilities ...
... – OS should take the appropriate action to ensure correct and consistent computing – OS should provide debugging facilities ...
Software: Operating Systems and Utilities
... OS/2 Operating Systems IBM’s OS/2 GUI operating system was developed to compete with Microsoft Windows and the Apple Mac OS. The latest version, OS/2Warp, can run programs written for both DOS and Windows systems. A network server version also has been developed. ...
... OS/2 Operating Systems IBM’s OS/2 GUI operating system was developed to compete with Microsoft Windows and the Apple Mac OS. The latest version, OS/2Warp, can run programs written for both DOS and Windows systems. A network server version also has been developed. ...
Trusted Operating Systems
... “I don't know how to to be confident even of a digital signature I make on my own PC, and I've worked in security for over fifteen years. Checking all of the software in the critical path between the display and the signature software is way beyond my patience. ” ...
... “I don't know how to to be confident even of a digital signature I make on my own PC, and I've worked in security for over fifteen years. Checking all of the software in the critical path between the display and the signature software is way beyond my patience. ” ...
Network Device Security Options
... standard widely used in TCP/IP environments. SNMP provides a method of managing network hosts such as printers, scanners, workstation or server computers, and groups’ bridges and hubs together into a “community” from a centrally-located computer running network management software. It allows adminis ...
... standard widely used in TCP/IP environments. SNMP provides a method of managing network hosts such as printers, scanners, workstation or server computers, and groups’ bridges and hubs together into a “community” from a centrally-located computer running network management software. It allows adminis ...
10 March 2009 - Computer Science
... Technology has developed a method to create rogue CA (Certification Authority) certificates from commercial CA certificates which are trusted by all common web browsers. ...
... Technology has developed a method to create rogue CA (Certification Authority) certificates from commercial CA certificates which are trusted by all common web browsers. ...
Introduction to Linux
... ■ sh (Bourne Shell) The sh shell was the earliest shell, being developed for UNIX back in the late 1970s. ■ bash (Bourne-Again Shell) The bash shell is an improved version of the sh shell and is one of the most popular shells today. It’s the default shell used by most Linux distributions. ■ csh (C S ...
... ■ sh (Bourne Shell) The sh shell was the earliest shell, being developed for UNIX back in the late 1970s. ■ bash (Bourne-Again Shell) The bash shell is an improved version of the sh shell and is one of the most popular shells today. It’s the default shell used by most Linux distributions. ■ csh (C S ...
Course number and name CSC 345 – Operating Systems Credits
... An introduction to operating systems concepts. Topics include processor management, storage management, device management, performance, security, and case studies of common operating systems. Prerequisites or co-requisites CSC 222 Indicate whether a required, elective, or selected elective (as per T ...
... An introduction to operating systems concepts. Topics include processor management, storage management, device management, performance, security, and case studies of common operating systems. Prerequisites or co-requisites CSC 222 Indicate whether a required, elective, or selected elective (as per T ...
System Security - Wright State engineering
... insert backdoors, install Trojans, and patch existing programs.’’ ...
... insert backdoors, install Trojans, and patch existing programs.’’ ...
Rimini Street Technology Solution Brief-Oracle Security-LT
... addressing changes to the dynamic environment of security challenges, client and desktop software migrations, and database upgrades. Encapsulation techniques — such as server and client virtualization, browser plugins, and PCI tokenizing — keep core systems operating while enabling necessary changes ...
... addressing changes to the dynamic environment of security challenges, client and desktop software migrations, and database upgrades. Encapsulation techniques — such as server and client virtualization, browser plugins, and PCI tokenizing — keep core systems operating while enabling necessary changes ...
Securing IT Assets with Linux
... - Up-to-date security vulnerability database. We mostly focus on the development of security checks for recent security holes. Our security checks database is updated on a daily basis. - Client-server architecture. The Nessus Security Scanner is made up of two parts : a server, which performs the at ...
... - Up-to-date security vulnerability database. We mostly focus on the development of security checks for recent security holes. Our security checks database is updated on a daily basis. - Client-server architecture. The Nessus Security Scanner is made up of two parts : a server, which performs the at ...
Ch2 OS Structures 1
... – Resource allocation ‐ When multiple users or multiple jobs running concurrently, resources must be allocated to each of them • Many types of resources ‐ CPU cycles, main memory, file storage, I/O devices. – Accounting ‐ To keep track of which users use how much and what kinds of computer resou ...
... – Resource allocation ‐ When multiple users or multiple jobs running concurrently, resources must be allocated to each of them • Many types of resources ‐ CPU cycles, main memory, file storage, I/O devices. – Accounting ‐ To keep track of which users use how much and what kinds of computer resou ...
Homeland Security
... • helping protect critical infrastructure and cyber networks from attack •detecting agents of biological warfare ...
... • helping protect critical infrastructure and cyber networks from attack •detecting agents of biological warfare ...
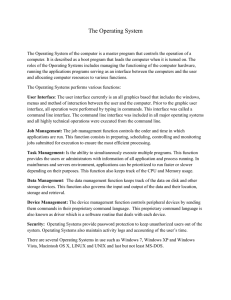
The Operating System The Operating System of the computer is a
... Throughout the history of computers, the operating systems have continuously evolved as the needs of the users and the capabilities of the computer system changes. The earliest computers were mainframe that had no form of an operating system. In the first generation of computers, programs were ente ...
... Throughout the history of computers, the operating systems have continuously evolved as the needs of the users and the capabilities of the computer system changes. The earliest computers were mainframe that had no form of an operating system. In the first generation of computers, programs were ente ...