Storing Organizational Information—Databases
... O A well-designed database should O Handle changes quickly and easily O Provide users with different views O Have only one physical view O Physical view – Deals with the physical ...
... O A well-designed database should O Handle changes quickly and easily O Provide users with different views O Have only one physical view O Physical view – Deals with the physical ...
AtomicEye Attack Surface Manager
... The concept is simple—if you patch all possible vulnerabilities and manage all application and operating system configurations in accordance with your custom security profile, your attack surface will remain small. However, without trusted automation, the change management overlaid with configurati ...
... The concept is simple—if you patch all possible vulnerabilities and manage all application and operating system configurations in accordance with your custom security profile, your attack surface will remain small. However, without trusted automation, the change management overlaid with configurati ...
Cybersecurity and Information Assurance PPT
... • Shared key-SSID plus WEP encrypted key required, subject to man-in-the middle attacks • Many wireless networks do not contain adequate authentication mechanisms • Both Open and Shared are considered weak ...
... • Shared key-SSID plus WEP encrypted key required, subject to man-in-the middle attacks • Many wireless networks do not contain adequate authentication mechanisms • Both Open and Shared are considered weak ...
Chap007
... that might be stored in Wikipedia’s database 2. Explain why database technology is so important to Wikipedia’s business model 3. Explain the difference between logical and physical views and why logical views are important to Wikipedia’s customers ...
... that might be stored in Wikipedia’s database 2. Explain why database technology is so important to Wikipedia’s business model 3. Explain the difference between logical and physical views and why logical views are important to Wikipedia’s customers ...
System Management Issues for the Future Real
... regression testing software • ITCS is experimenting with dynamic provisioning and end-to-end monitoring software • Dormitory scanning software is under study for possible wider deployment • ADC working on data access policies and role-based security frameworks • Identity management system replacemen ...
... regression testing software • ITCS is experimenting with dynamic provisioning and end-to-end monitoring software • Dormitory scanning software is under study for possible wider deployment • ADC working on data access policies and role-based security frameworks • Identity management system replacemen ...
INTRODUCTION TO INFORMATION SYSTEMS TECHNOLOGY
... A cracker is an intruder who breaks into a computer system to cause damage and/or to steal information ...
... A cracker is an intruder who breaks into a computer system to cause damage and/or to steal information ...
CIS 450 – Network Security
... of most operating systems has large number of services running and ports open Application-level Attacks – take advantage of less-than-perfect security found in most of today’s software Scripts & Sample Program Attacks – Sample files and scripts that come with operating systems/applications ...
... of most operating systems has large number of services running and ports open Application-level Attacks – take advantage of less-than-perfect security found in most of today’s software Scripts & Sample Program Attacks – Sample files and scripts that come with operating systems/applications ...
S p
... hold However, for every a and b, there is a lowest upper bound u for which u ≥ a and u ≥ b, and a greatest lower bound l for which a ≥ l and b ≥ l There are also two elements U and L that dominate/are dominated by all levels In example, U = (“Top Secret”, {“Soviet Union”, “East Germany”}) L = (“Un ...
... hold However, for every a and b, there is a lowest upper bound u for which u ≥ a and u ≥ b, and a greatest lower bound l for which a ≥ l and b ≥ l There are also two elements U and L that dominate/are dominated by all levels In example, U = (“Top Secret”, {“Soviet Union”, “East Germany”}) L = (“Un ...
Relational Databases
... Integrity constraints – rules that help ensure the quality of information Operational integrity constraints – rules that enforce basic and fundamental information-based constraints Business-critical integrity constraints – rules that enforce business rules vital to an organization’s success and ...
... Integrity constraints – rules that help ensure the quality of information Operational integrity constraints – rules that enforce basic and fundamental information-based constraints Business-critical integrity constraints – rules that enforce business rules vital to an organization’s success and ...
Data - Federated Archaeological Information Management Systems
... So this step is about defining the INTEREST that communities have in defining the actions to care for values This information is generally less sensitive, and more appropriately discussed in public forums like ...
... So this step is about defining the INTEREST that communities have in defining the actions to care for values This information is generally less sensitive, and more appropriately discussed in public forums like ...
Chapter 5 - Department of Computer Science and Information Systems
... Security measures for commerce servers: • Access control and authentication ...
... Security measures for commerce servers: • Access control and authentication ...
E-Commerce and Bank Security
... “Total eCommerce sales for 2006 were estimated at $108.7 billion. This represents an increase of 23.5% over 2005,” according to the U.S. Census Bureau’s E-Commerce Survey. ...
... “Total eCommerce sales for 2006 were estimated at $108.7 billion. This represents an increase of 23.5% over 2005,” according to the U.S. Census Bureau’s E-Commerce Survey. ...
SANDS CORP CYBER JOB
... Experience configuring and installing information security applications. Hands-on experience with security applications is preferred. Fundamental understanding of encryption technologies. Understanding of common network traffic, i.e., Transmission Control Protocol/Internet Protocol (TCP/IP), Interne ...
... Experience configuring and installing information security applications. Hands-on experience with security applications is preferred. Fundamental understanding of encryption technologies. Understanding of common network traffic, i.e., Transmission Control Protocol/Internet Protocol (TCP/IP), Interne ...
policies - NY Capital Region Chapter
... Log Monitoring can show when an event occurred, and show trends over time, e.g. SPLUNK ...
... Log Monitoring can show when an event occurred, and show trends over time, e.g. SPLUNK ...
C.2. Vulnerabilities
... little monitoring or management. Consider that the typical university research or teaching lab is managed by a faculty member who has many other responsibilities or by a student manager who may have had little training. Universities are havens for free exchange of ideas. Thus, their access controls ...
... little monitoring or management. Consider that the typical university research or teaching lab is managed by a faculty member who has many other responsibilities or by a student manager who may have had little training. Universities are havens for free exchange of ideas. Thus, their access controls ...
Addressing security threats and vulnerabilities
... Addressing security threats and vulnerabilities – Goals of security – Risks, threats and vulnerabilities – Risk assessment – Common threats – Types of attacks – Common defences – Basic security guidelines ...
... Addressing security threats and vulnerabilities – Goals of security – Risks, threats and vulnerabilities – Risk assessment – Common threats – Types of attacks – Common defences – Basic security guidelines ...
INFORMATION TYPE - McGraw Hill Higher Education
... DATA WAREHOUSING Data warehouse – A logical collection of information – gathered from many different operational databases – that supports business analysis activities and decisionmaking tasks The primary purpose of a data warehouse is to aggregate information throughout an organization into a s ...
... DATA WAREHOUSING Data warehouse – A logical collection of information – gathered from many different operational databases – that supports business analysis activities and decisionmaking tasks The primary purpose of a data warehouse is to aggregate information throughout an organization into a s ...
Protection
... Definition of the object of protection (ISIR) and categories of protected information; Description of the process (simulation) of information security ISIR; Programming the required level of information security; Setting the required level of information security; Identification of measures to prote ...
... Definition of the object of protection (ISIR) and categories of protected information; Description of the process (simulation) of information security ISIR; Programming the required level of information security; Setting the required level of information security; Identification of measures to prote ...
*What is the unit of Security?* Eerke Boiten, university of Kent, UK
... There’s no unit of security! (More precisely: the unit of functional composition isn’t a unit of security.) More practically: functional decomposition may not be security decomposition [and UC is complex] – 1st point of caution ...
... There’s no unit of security! (More precisely: the unit of functional composition isn’t a unit of security.) More practically: functional decomposition may not be security decomposition [and UC is complex] – 1st point of caution ...
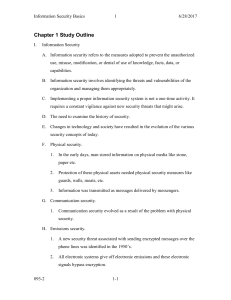
Chapter 1 Study Outline
... use, misuse, modification, or denial of use of knowledge, facts, data, or capabilities. B. Information security involves identifying the threats and vulnerabilities of the organization and managing them appropriately. C. Implementing a proper information security system is not a one-time activity. I ...
... use, misuse, modification, or denial of use of knowledge, facts, data, or capabilities. B. Information security involves identifying the threats and vulnerabilities of the organization and managing them appropriately. C. Implementing a proper information security system is not a one-time activity. I ...
Information Systems and Networks
... Information systems controls are both manual and automated and consist of both general controls and application controls General controls govern the design, security, and use of computer programs and the security of data files in general throughout the organization’s information technology infrastru ...
... Information systems controls are both manual and automated and consist of both general controls and application controls General controls govern the design, security, and use of computer programs and the security of data files in general throughout the organization’s information technology infrastru ...
TMDE Web Site
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
Call for Papers The 4th International Workshop on Security and
... challenging problem for computer scientists, social scientists, law experts and policy makers. Appropriate healthcare provision requires specialized knowledge, is information intensive and much patient information is of a particularly sensitive nature. Electronic health record systems provide opport ...
... challenging problem for computer scientists, social scientists, law experts and policy makers. Appropriate healthcare provision requires specialized knowledge, is information intensive and much patient information is of a particularly sensitive nature. Electronic health record systems provide opport ...
Relational Database Model - McGraw Hill Higher Education
... of objects (inventory), events (transactions), people (employees), and places (warehouses) • Database models include: – Hierarchical Database Model—Information is organized into tree-like structure (using parent/child relationships) in such a way that it cannot have too many relationships – Network ...
... of objects (inventory), events (transactions), people (employees), and places (warehouses) • Database models include: – Hierarchical Database Model—Information is organized into tree-like structure (using parent/child relationships) in such a way that it cannot have too many relationships – Network ...
Assessment and Authorization for Cloud Computing
... (2): No more than 90 days. (3): 90 Days for User Level Accounts - as per contractor system determination for nonuser level accounts (device, token, smart cards, etc) ...
... (2): No more than 90 days. (3): 90 Days for User Level Accounts - as per contractor system determination for nonuser level accounts (device, token, smart cards, etc) ...