William Stallings, Cryptography and Network Security 5/e
... of a resource Data Confidentiality –protection of data from unauthorized disclosure Data Integrity - assurance that data received is as sent by an authorized entity Non-Repudiation - protection against denial by one of the parties in a communication Availability – resource accessible/usable ...
... of a resource Data Confidentiality –protection of data from unauthorized disclosure Data Integrity - assurance that data received is as sent by an authorized entity Non-Repudiation - protection against denial by one of the parties in a communication Availability – resource accessible/usable ...
Chap013
... What two issues does the article suggest about Credibility? Why would Enron (or any) executives engage in such activities? How can people be encouraged to follow acceptable ethical/moral business practices? ...
... What two issues does the article suggest about Credibility? Why would Enron (or any) executives engage in such activities? How can people be encouraged to follow acceptable ethical/moral business practices? ...
Department of Information Resources, State
... Supports the corporate vision statement Practical Enforceable Concise as it can be (they tend to run long) • Defines how the policy itself can change. ...
... Supports the corporate vision statement Practical Enforceable Concise as it can be (they tend to run long) • Defines how the policy itself can change. ...
Are Clouds Secure? - San Francisco Bay Area ISSA Chapter
... What We’re Not Going to Discuss • Existing aspects of information security which are not impacted by ‘cloud computing’ • There are plenty of existing sources of useful information about information security, and we will not attempt to recreate those sources, nor ...
... What We’re Not Going to Discuss • Existing aspects of information security which are not impacted by ‘cloud computing’ • There are plenty of existing sources of useful information about information security, and we will not attempt to recreate those sources, nor ...
Are Clouds Secure?
... What We’re Not Going to Discuss • Existing aspects of information security which are not impacted by ‘cloud computing’ • There are plenty of existing sources of useful information about information security, and we will not attempt to recreate those sources, nor ...
... What We’re Not Going to Discuss • Existing aspects of information security which are not impacted by ‘cloud computing’ • There are plenty of existing sources of useful information about information security, and we will not attempt to recreate those sources, nor ...
African Marine Biodiversity
... • International Ocean Institute, University of the Western Cape, South Africa • University of Cape Town in co-operation with Marine and Coastal Management, South Africa • University of Stockholm, Sweden • University of Namibia ...
... • International Ocean Institute, University of the Western Cape, South Africa • University of Cape Town in co-operation with Marine and Coastal Management, South Africa • University of Stockholm, Sweden • University of Namibia ...
D`Amo - softfarm
... encryption/decryption privileges, and application of access policies to internal and external users. ...
... encryption/decryption privileges, and application of access policies to internal and external users. ...
Something Security
... • Common critiques: (i) over-extended definitions ‘meaningless’ and/or ‘too complicated’ (eg for comparative risk assessment, executive handling); (ii) critique of ‘securitization’ • BUT: - main risks for West objectively moving down the spectrum; non-securitizing can also mean ignoring/downplaying ...
... • Common critiques: (i) over-extended definitions ‘meaningless’ and/or ‘too complicated’ (eg for comparative risk assessment, executive handling); (ii) critique of ‘securitization’ • BUT: - main risks for West objectively moving down the spectrum; non-securitizing can also mean ignoring/downplaying ...
Siveillance Vantage
... business continuity From protecting employees, local communities or corporate reputation to preventing financial losses due to production disruptions, today’s companies are faced with a multitude of security-related challenges: any disruption to production, business processes or services, whether it ...
... business continuity From protecting employees, local communities or corporate reputation to preventing financial losses due to production disruptions, today’s companies are faced with a multitude of security-related challenges: any disruption to production, business processes or services, whether it ...
Slides
... areas of traditional systems engineering, probabilistic failure models do not suffice to capture the complexity of intelligent adversaries with undetermined capabilities and motives. However, critical physical infrastructure systems offer opportunities for powerful approaches to security, since they ...
... areas of traditional systems engineering, probabilistic failure models do not suffice to capture the complexity of intelligent adversaries with undetermined capabilities and motives. However, critical physical infrastructure systems offer opportunities for powerful approaches to security, since they ...
Curriculum Vitae - ASU People Search
... Designed secured communication layer by modification of frame format of IP, TCP and UDP layer using Scapy. Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of pyt ...
... Designed secured communication layer by modification of frame format of IP, TCP and UDP layer using Scapy. Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of pyt ...
Orange Book Summary - UMBC Center for Information Security and
... System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the Orange Book and Rainbow Series by looking at the Orange Book Links page. Exam ...
... System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the Orange Book and Rainbow Series by looking at the Orange Book Links page. Exam ...
Orange
... System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the Orange Book and Rainbow Series by looking at the Orange Book Links page. Exam ...
... System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the Orange Book and Rainbow Series by looking at the Orange Book Links page. Exam ...
Introduction to Data Integrity
... Database security is the system, processes, and procedures that protect a database from unintended activity. Unintended activity can be categorized as authenticated misuse, malicious attacks or unintentional mistakes made by authorized individuals or processes. ...
... Database security is the system, processes, and procedures that protect a database from unintended activity. Unintended activity can be categorized as authenticated misuse, malicious attacks or unintentional mistakes made by authorized individuals or processes. ...
Prevent Online Fraud and Identity Theft
... Internet scams such as Phishing and Spoofing are becoming more prevalent, and protecting your personal information from Identity Theft is crucial. There are many ways the unscrupulous can gain access to information such as your name, Social Security Number, credit card or bank account numbers, or ot ...
... Internet scams such as Phishing and Spoofing are becoming more prevalent, and protecting your personal information from Identity Theft is crucial. There are many ways the unscrupulous can gain access to information such as your name, Social Security Number, credit card or bank account numbers, or ot ...
Donor Privacy Policy
... to assume all donations are not to be publicly announced unless the donor explicitly indicates otherwise. Comments given in donor forms are published in public lists and may be used in promotional materials while comments sent to us via email, fax or telephone are kept strictly confidential. Financi ...
... to assume all donations are not to be publicly announced unless the donor explicitly indicates otherwise. Comments given in donor forms are published in public lists and may be used in promotional materials while comments sent to us via email, fax or telephone are kept strictly confidential. Financi ...
download soal
... 2. Over the last 10 years businesses have come to rely on information management in ways that could not have been foreseen. Information systems are a critical part of the business landscape. Being able to convert data or raw facts and figures into information, that is, meaningful and useful is impor ...
... 2. Over the last 10 years businesses have come to rely on information management in ways that could not have been foreseen. Information systems are a critical part of the business landscape. Being able to convert data or raw facts and figures into information, that is, meaningful and useful is impor ...
Network Security Overview
... Reconnaissance is the unauthorized discovery and mapping of systems, services, or vulnerabilities. It is also called information gathering. In most cases, it precedes an actual access or DoS attack. The malicious intruder typically ping-sweeps the target network first to determine what IP addresses ...
... Reconnaissance is the unauthorized discovery and mapping of systems, services, or vulnerabilities. It is also called information gathering. In most cases, it precedes an actual access or DoS attack. The malicious intruder typically ping-sweeps the target network first to determine what IP addresses ...
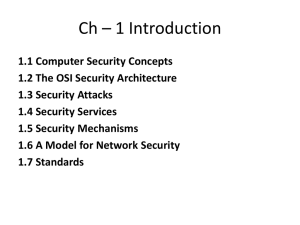
Ch – 1 Introduction
... • The NIST Computer Security Handbook [NIST95] defines the term computer security as • “The protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability, and confidentiality of information system resources (includes har ...
... • The NIST Computer Security Handbook [NIST95] defines the term computer security as • “The protection afforded to an automated information system in order to attain the applicable objectives of preserving the integrity, availability, and confidentiality of information system resources (includes har ...
2001-09-07-AIC-SecurityForEducation
... • Use one-to-one NAT for externally accessible hosts or special clients (or where you have room) • Use many-to-one (PAT, IP Masquerading, overloaded nat) for client access to the Internet • NAT can break a lot of software, so be aware of address translation issues –anything that requires a host-to-h ...
... • Use one-to-one NAT for externally accessible hosts or special clients (or where you have room) • Use many-to-one (PAT, IP Masquerading, overloaded nat) for client access to the Internet • NAT can break a lot of software, so be aware of address translation issues –anything that requires a host-to-h ...
Introduction to Lifecycle - Manchester Metropolitan University
... • There is no universally accepted definition of a system • Properties that are generally considered part of a good definition – An organised or complex whole – An entity that consists of independent parts – These parts are affected by being part of the system and are changed by being removed from t ...
... • There is no universally accepted definition of a system • Properties that are generally considered part of a good definition – An organised or complex whole – An entity that consists of independent parts – These parts are affected by being part of the system and are changed by being removed from t ...
Introduction
... An asset is the resource being protected, including: physical assets: devices, computers, people; logical assets: information, data (in transmission, storage, or processing), and intellectual property; system assets: any software, hardware, data, administrative, physical, communications, or personn ...
... An asset is the resource being protected, including: physical assets: devices, computers, people; logical assets: information, data (in transmission, storage, or processing), and intellectual property; system assets: any software, hardware, data, administrative, physical, communications, or personn ...
Network Improvement Project
... Configuration and Asset Management Infrastructure for Window, Mac, and Linux systems - $60,000 Provides us the ability to manage the security of over 5000 desktops, servers and other computers and to discover in detail what software is loaded and functioning on each machine. Software is provided ...
... Configuration and Asset Management Infrastructure for Window, Mac, and Linux systems - $60,000 Provides us the ability to manage the security of over 5000 desktops, servers and other computers and to discover in detail what software is loaded and functioning on each machine. Software is provided ...
Threats and Attacks
... § Authorization: determining whether an entity (person, program, computer) has access to object § Can be implicit (email account access) or explicit (attributes specifying users/groups who can read/write/execute file) ...
... § Authorization: determining whether an entity (person, program, computer) has access to object § Can be implicit (email account access) or explicit (attributes specifying users/groups who can read/write/execute file) ...
Chapter 1 - Mecca Hosting
... processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. In a computing context, the term security implies cybersecurity. The goal of cybersecurity is to protect and ensure security of data. Some of the measures include access con ...
... processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. In a computing context, the term security implies cybersecurity. The goal of cybersecurity is to protect and ensure security of data. Some of the measures include access con ...