The Advanced Penetration Testing Boot Camp
... • Organizations of all sizes are finding that today’s mobile and collaborative workforce needs access to information inside and outside the office, along with the ability to share data with co-workers and partners. • Users are routinely using and sharing data without giving thought to confidentialit ...
... • Organizations of all sizes are finding that today’s mobile and collaborative workforce needs access to information inside and outside the office, along with the ability to share data with co-workers and partners. • Users are routinely using and sharing data without giving thought to confidentialit ...
Phishing and whaling – Don`t get hooked!
... So what are phishing and whaling? Phishing is an attempt to obtain sensitive information such as usernames, passwords, credit card details or money transfers usually by masquerading as a trustworthy entity or person. Like the word fishing, it is a technique that uses bait to catch the victim. Phishi ...
... So what are phishing and whaling? Phishing is an attempt to obtain sensitive information such as usernames, passwords, credit card details or money transfers usually by masquerading as a trustworthy entity or person. Like the word fishing, it is a technique that uses bait to catch the victim. Phishi ...
Information Assurance Awareness, Training, Education at the U.S.
... Communicate security requirements • Policy, rules of behavior ...
... Communicate security requirements • Policy, rules of behavior ...
What is the HIPAA Security Rule? - Illinois Department of Human
... IIHI, PCI, SSN, FTI) that you are emailing, saving to a portable electronic device (CD, DVD, removable storage device) or sending through a file transfer, it MUST BE encrypted • Encrypting the confidential information will encode the information in such a way that only authorized parties can read it ...
... IIHI, PCI, SSN, FTI) that you are emailing, saving to a portable electronic device (CD, DVD, removable storage device) or sending through a file transfer, it MUST BE encrypted • Encrypting the confidential information will encode the information in such a way that only authorized parties can read it ...
What is the HIPAA Security Rule? - Illinois Department of Human
... IIHI, PCI, SSN, FTI) that you are emailing, saving to a portable electronic device (CD, DVD, removable storage device) or sending through a file transfer, it MUST BE encrypted • Encrypting the confidential information will encode the information in such a way that only authorized parties can read it ...
... IIHI, PCI, SSN, FTI) that you are emailing, saving to a portable electronic device (CD, DVD, removable storage device) or sending through a file transfer, it MUST BE encrypted • Encrypting the confidential information will encode the information in such a way that only authorized parties can read it ...
Key To Personal Information Security
... • Attackers can sometimes get data without having to directly use your computers • Exploit Internet services that are intended to give out information • Induce these services to reveal extra information or to give it out to unauthorized people • Many services designed for use on local area networks ...
... • Attackers can sometimes get data without having to directly use your computers • Exploit Internet services that are intended to give out information • Induce these services to reveal extra information or to give it out to unauthorized people • Many services designed for use on local area networks ...
Lecture 8 - Bhecker.com
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
01 Computer security overview
... – Attack = someone intentionally causes the bad thing to happen – Vulnerability = weakness in an information system that enables an attack – Exploit = implementation of an attack – Risk = probability of an attack × damage in dollars ...
... – Attack = someone intentionally causes the bad thing to happen – Vulnerability = weakness in an information system that enables an attack – Exploit = implementation of an attack – Risk = probability of an attack × damage in dollars ...
Social engineering - Information Systems
... Delete e-mails from unknown sources If your computer gets a virus… ...
... Delete e-mails from unknown sources If your computer gets a virus… ...
Introduction to Information Security
... Forces of nature, force majeure, or acts of God pose some of the most dangerous threats, because they are unexpected and can occur with very little warning. Fire: In this context, a structural fire that damages the building housing the computing equipment that comprises all or part of the informatio ...
... Forces of nature, force majeure, or acts of God pose some of the most dangerous threats, because they are unexpected and can occur with very little warning. Fire: In this context, a structural fire that damages the building housing the computing equipment that comprises all or part of the informatio ...
Introduction (Powerpoint)
... A definition of general and specific roles and responsibilities for the various aspects of information security program in business an explanation of the requirement and process for reporting suspected security incidents, and the process, including roles and responsibilities, for maintaining the ...
... A definition of general and specific roles and responsibilities for the various aspects of information security program in business an explanation of the requirement and process for reporting suspected security incidents, and the process, including roles and responsibilities, for maintaining the ...
Network Security
... system resource • Addresses the security concerns raised by denial-of-service attack. ...
... system resource • Addresses the security concerns raised by denial-of-service attack. ...
Breach Detection in Healthcare
... Digital records of patients have become part of our daily reality. In hospitals, doctors’ offices, insurance companies, and other related organizations, many people need access to patient records to do their jobs. However, how do we know someone else cannot gain unauthorized access to these files? P ...
... Digital records of patients have become part of our daily reality. In hospitals, doctors’ offices, insurance companies, and other related organizations, many people need access to patient records to do their jobs. However, how do we know someone else cannot gain unauthorized access to these files? P ...
WelcometoCISandCybercorps
... certificates, and public key infrastructure (PKI). Legal and national policy electronic commerce issues. ...
... certificates, and public key infrastructure (PKI). Legal and national policy electronic commerce issues. ...
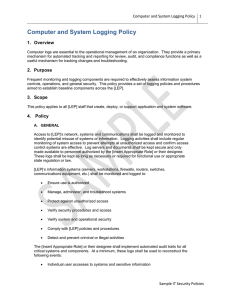
Computer and System Logging Policy
... Procedures that specify audit controls, hardware, software, and/or procedural mechanisms that record and examine activity in information systems ...
... Procedures that specify audit controls, hardware, software, and/or procedural mechanisms that record and examine activity in information systems ...
Database Security - University of Scranton: Computing Sciences Dept.
... Databases often store data which is sensitive in nature Incorrect data or loss of data could negatively affect business operations Databases can be used as bases to attack other systems from ...
... Databases often store data which is sensitive in nature Incorrect data or loss of data could negatively affect business operations Databases can be used as bases to attack other systems from ...
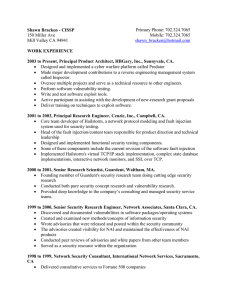
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" which handled the more difficult and time-consuming calls. Most customers were large production systems requiring high uptime. 1997 to 1998, Network Securi ...
... Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" which handled the more difficult and time-consuming calls. Most customers were large production systems requiring high uptime. 1997 to 1998, Network Securi ...
Ceffarati Hold for View Authorization
... I understand that I have the right to cancel this authorization, in writing, at any time by presenting my written cancellation to: Hospital/Doctor listed above. I understand that a cancellation will not apply to information that has already been released under this authorization. I also understand t ...
... I understand that I have the right to cancel this authorization, in writing, at any time by presenting my written cancellation to: Hospital/Doctor listed above. I understand that a cancellation will not apply to information that has already been released under this authorization. I also understand t ...
Network Security
... system resource • Addresses the security concerns raised by denial-of-service attack. ...
... system resource • Addresses the security concerns raised by denial-of-service attack. ...
Lecture27 - The University of Texas at Dallas
... Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters Steganograophy makes the task of the Cyber crime expert difficult as he/she ahs to analyze for hidden information ...
... Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters Steganograophy makes the task of the Cyber crime expert difficult as he/she ahs to analyze for hidden information ...
Incident Handling Applied Risk Management September 2002
... An Information Security event is: • potential harm creating potential risk • threats attempting to exploit vulnerabilities • unexplained anomalous behavior • tangible attacks upon assets ...
... An Information Security event is: • potential harm creating potential risk • threats attempting to exploit vulnerabilities • unexplained anomalous behavior • tangible attacks upon assets ...
Network and Systems Security
... Produce and maintain Risk register and associated Risk reduction measures Agree set of Policies and Guidelines that would address specific areas of concern Agree a Network Architecture that would reduce the exposure of Networked systems and provide Inherent containment measures Establish a Computer ...
... Produce and maintain Risk register and associated Risk reduction measures Agree set of Policies and Guidelines that would address specific areas of concern Agree a Network Architecture that would reduce the exposure of Networked systems and provide Inherent containment measures Establish a Computer ...
Computer and Information Security
... communication to • Impersonate legitimate parties • Modify the content in transit • Launch denial of service attacks ...
... communication to • Impersonate legitimate parties • Modify the content in transit • Launch denial of service attacks ...
The Top Ten of Security
... as in a DDOS attack, you could be liable. • Using industry Best Practices can protect you from lawsuits. ...
... as in a DDOS attack, you could be liable. • Using industry Best Practices can protect you from lawsuits. ...
MSMIS Core Course Learning Outcomes Updated 9/26/15 MIS
... • evaluate problems in the planning and implementation of organizational change as related to an organization's information and enterprise systems • effectively communicate with project team members, client, users, and others associated with development, operation, and maintenance of systems MIS-740 ...
... • evaluate problems in the planning and implementation of organizational change as related to an organization's information and enterprise systems • effectively communicate with project team members, client, users, and others associated with development, operation, and maintenance of systems MIS-740 ...