Lottery`s Log Management Business Objectives
... • Keep you and your director from getting fired! • Consistent with business objectives ...
... • Keep you and your director from getting fired! • Consistent with business objectives ...
information system
... People rely on modern information systems to communicate with each other using a variety of physical devices (hardware), information processing instructions and procedures (software), communications channels (networks), and stored data (data resources). ...
... People rely on modern information systems to communicate with each other using a variety of physical devices (hardware), information processing instructions and procedures (software), communications channels (networks), and stored data (data resources). ...
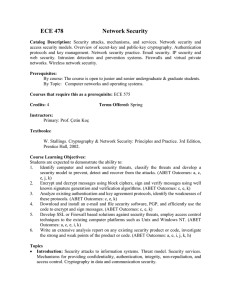
William Stallings, Cryptography and Network Security 3/e
... • given system has identified a user • determine what resources they can access • general model is that of access matrix with – subject - active entity (user, process) – object - passive entity (file or resource) – access right – way object can be accessed ...
... • given system has identified a user • determine what resources they can access • general model is that of access matrix with – subject - active entity (user, process) – object - passive entity (file or resource) – access right – way object can be accessed ...
2001-10-11-AIC-SecurityForEducation
... • Use one-to-one NAT for externally accessible hosts or special clients (or where you have room) • Use many-to-one (PAT, IP Masquerading, overloaded nat) for client access to the Internet • NAT can break a lot of software, so be aware of address translation issues –anything that requires a host-to-h ...
... • Use one-to-one NAT for externally accessible hosts or special clients (or where you have room) • Use many-to-one (PAT, IP Masquerading, overloaded nat) for client access to the Internet • NAT can break a lot of software, so be aware of address translation issues –anything that requires a host-to-h ...
Chapter 05
... ◦ Public: less sensitive. ◦ Proprietary: less sensitive than internal. ◦ Internal: sensitive. ...
... ◦ Public: less sensitive. ◦ Proprietary: less sensitive than internal. ◦ Internal: sensitive. ...
Exam 1
... CPU (Central Processing Unit) and memory Computer Performance – The speed of main memory – The speed and width of the data bus ...
... CPU (Central Processing Unit) and memory Computer Performance – The speed of main memory – The speed and width of the data bus ...
Course Learning Objectives:
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
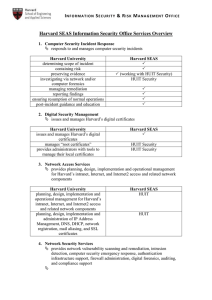
Harvard SEAS Information Security Office Services Overview
... may indicate computer attack, compromised machine, data breach, etc Harvard University monitors network traffic in real-time aggregates and correlates security data from network and system infrastructure ...
... may indicate computer attack, compromised machine, data breach, etc Harvard University monitors network traffic in real-time aggregates and correlates security data from network and system infrastructure ...
Network and Systems - University of Glasgow
... The Universal Access and Information Security working groups have produced a set of draft Policies and Guidelines for consultation These are not meant to place unnecessary barriers in the way of users doing their legitimate work They are not tablets of stone but rather starting points that will evol ...
... The Universal Access and Information Security working groups have produced a set of draft Policies and Guidelines for consultation These are not meant to place unnecessary barriers in the way of users doing their legitimate work They are not tablets of stone but rather starting points that will evol ...
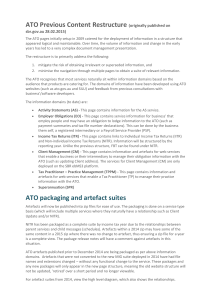
here - Standard Business Reporting
... employ people and may have an obligation to lodge information to the ATO (such as payment summaries and tax file number declarations). This can be done by the business them self, a registered intermediary or a Payroll Service Provider (PSP). Income Tax Returns (ITR) - This page contains links to Ind ...
... employ people and may have an obligation to lodge information to the ATO (such as payment summaries and tax file number declarations). This can be done by the business them self, a registered intermediary or a Payroll Service Provider (PSP). Income Tax Returns (ITR) - This page contains links to Ind ...
(2)
... Information is distributed from the CARD network entity (assumed to be located in access routers) to the mobile nodes. ...
... Information is distributed from the CARD network entity (assumed to be located in access routers) to the mobile nodes. ...
www.itgovernance.co.uk/training
... People are your weakest link – Strengthen awareness to improve the robustness of your ISMS Training aids are a tool for getting general staff involved in discussing and understanding the sometimes complex data security issues which might impinge on how they work – and to do so in a low impact, low p ...
... People are your weakest link – Strengthen awareness to improve the robustness of your ISMS Training aids are a tool for getting general staff involved in discussing and understanding the sometimes complex data security issues which might impinge on how they work – and to do so in a low impact, low p ...
Faculty of Correspondence, Evening and Distance
... Today BSUIR is a large scientific and educational center in Belarus. It has highly qualified staff, considerable scientific and methodological potential, advanced laboratory and informational infrastructure, all necessary conditions to organize teaching and educational process, scientific research, ...
... Today BSUIR is a large scientific and educational center in Belarus. It has highly qualified staff, considerable scientific and methodological potential, advanced laboratory and informational infrastructure, all necessary conditions to organize teaching and educational process, scientific research, ...
download soal
... 1. What are the four types of architecture for multi user systems? 2. What are the four categories of controls discussed in this text ? Birefly describe each category 3. Why is IT planning important to an organization? 4. Briefly describe three important controls related to organizing the IT functio ...
... 1. What are the four types of architecture for multi user systems? 2. What are the four categories of controls discussed in this text ? Birefly describe each category 3. Why is IT planning important to an organization? 4. Briefly describe three important controls related to organizing the IT functio ...
Lecture 1 - WordPress.com
... Data Confidentiality –protection of data from unauthorized disclosure Data Integrity - assurance that data received is as sent by an authorized entity Non-Repudiation - protection against denial by one of the parties in a communication Availability – resource accessible/usable ...
... Data Confidentiality –protection of data from unauthorized disclosure Data Integrity - assurance that data received is as sent by an authorized entity Non-Repudiation - protection against denial by one of the parties in a communication Availability – resource accessible/usable ...
Confidentiality
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
download
... – Something that enhances the security of the data processing systems and the information transfers of an organization – Intended to counter security attacks – Make use of one or more security mechanisms to provide the service – Replicate functions normally associated with physical documents • eg. h ...
... – Something that enhances the security of the data processing systems and the information transfers of an organization – Intended to counter security attacks – Make use of one or more security mechanisms to provide the service – Replicate functions normally associated with physical documents • eg. h ...
Document
... Privacy concerns is losing control of personal information to people who claim to need it Security concerns is fear of unauthorized access and manipulation of data by people who does not have a legitimate need of it ...
... Privacy concerns is losing control of personal information to people who claim to need it Security concerns is fear of unauthorized access and manipulation of data by people who does not have a legitimate need of it ...
Document
... Technical Security Prevent security breaches Detect security breaches Recover from security breaches ...
... Technical Security Prevent security breaches Detect security breaches Recover from security breaches ...
Lecture 10 - The University of Texas at Dallas
... Summary of Developments in MLS/DBMS Early Efforts 1975 – 1982; example: Hinke-Shafer approach ...
... Summary of Developments in MLS/DBMS Early Efforts 1975 – 1982; example: Hinke-Shafer approach ...
10.2 BASIC E-COMMERCE SECURITY ISSUES AND LANDSCAPE
... - Measures taken to protect information systems and their processes against all risks. In other words assure the systems’ availability when needed. The assurance includes all tools and defense methods. ...
... - Measures taken to protect information systems and their processes against all risks. In other words assure the systems’ availability when needed. The assurance includes all tools and defense methods. ...
Network Security Manager - Harris
... Harris-Stowe State University’s Department of IT Services is seeking candidates for a full-time Network Security Manager. The Network Security Manager (NSM) will be responsible for the daily activities of personnel who support network functions and ensure that the network and client computing system ...
... Harris-Stowe State University’s Department of IT Services is seeking candidates for a full-time Network Security Manager. The Network Security Manager (NSM) will be responsible for the daily activities of personnel who support network functions and ensure that the network and client computing system ...