Information System Security
... • no single mechanism that will support all functions required • however one particular element underlies many of the security mechanisms in use: cryptographic techniques • hence our focus on this area ...
... • no single mechanism that will support all functions required • however one particular element underlies many of the security mechanisms in use: cryptographic techniques • hence our focus on this area ...
slides
... important than features and performance” (Bill Gates) – “The missing component in most security products is what Global 5000 buyers most want, the ability to manage business risk, innovation, and agility. Despite this, security suppliers continue to focus their efforts on honing technical access con ...
... important than features and performance” (Bill Gates) – “The missing component in most security products is what Global 5000 buyers most want, the ability to manage business risk, innovation, and agility. Despite this, security suppliers continue to focus their efforts on honing technical access con ...
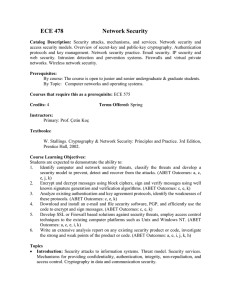
Course Learning Objectives:
... 5. Develop SSL or Firewall based solutions against security threats, employ access control techniques to the existing computer platforms such as Unix and Windows NT. (ABET Outcomes: a, c, e, i, k) 6. Write an extensive analysis report on any existing security product or code, investigate the strong ...
... 5. Develop SSL or Firewall based solutions against security threats, employ access control techniques to the existing computer platforms such as Unix and Windows NT. (ABET Outcomes: a, c, e, i, k) 6. Write an extensive analysis report on any existing security product or code, investigate the strong ...
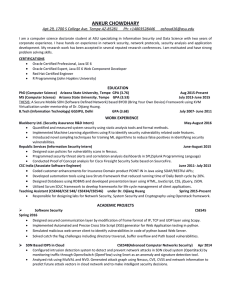
Curriculum Vitae - ASU People Search
... Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and Path based vulnerabilities. ...
... Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and Path based vulnerabilities. ...
Global Information Assurance Certification (GIAC) develops and administers the premier
... MANAGEMENT, LEGAL AND AUDIT The leadership and management of security teams and risk analysis techniques to conduct a technical audit of essential information systems. SANS Training Courses: 14 | GIAC Certifications: 6 ...
... MANAGEMENT, LEGAL AND AUDIT The leadership and management of security teams and risk analysis techniques to conduct a technical audit of essential information systems. SANS Training Courses: 14 | GIAC Certifications: 6 ...
Licens
... • There is urgent need to enhance information sharing to improve incidence response capabilities. ...
... • There is urgent need to enhance information sharing to improve incidence response capabilities. ...
Computersikkerhed
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
Countering Evolving Threats in Distributed Applications
... • Distributed applications need to be protected • Three emerging trends 1. Attack at the point of least resistance 2. Exploit zero-day vulnerabilities in any constituent service 3. Set up a covert channel for leaking sensitive information ...
... • Distributed applications need to be protected • Three emerging trends 1. Attack at the point of least resistance 2. Exploit zero-day vulnerabilities in any constituent service 3. Set up a covert channel for leaking sensitive information ...
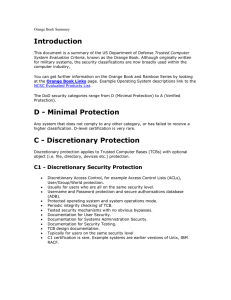
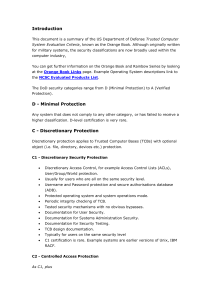
Orange Book Summary - UMBC Center for Information Security and
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
Orange
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
Click here to access the presentation.
... − Customized ‘apps’ w/ analytical algorithms − Artificial Intelligence (AI) to aid human analysis − Bandwidth compression; Quality of Service ICT Industry Revolution ...
... − Customized ‘apps’ w/ analytical algorithms − Artificial Intelligence (AI) to aid human analysis − Bandwidth compression; Quality of Service ICT Industry Revolution ...
Visualization
... to collect and analyze vast amounts of security alert data. More specifically, SIM solutions collect, analyze and correlate – in real-time – all security device information across an entire enterprise. Correlated results are then displayed on a centralized real-time console that is part of an intuit ...
... to collect and analyze vast amounts of security alert data. More specifically, SIM solutions collect, analyze and correlate – in real-time – all security device information across an entire enterprise. Correlated results are then displayed on a centralized real-time console that is part of an intuit ...
Phishing Scams - Corner Stone Credit Union
... to an alleged security update, system maintenance, or an update in technology. Financial institutions will never send unsolicited e-mails requesting anyone to provide, update or verify account or personal information, such as passwords, Social Security numbers, PINs, credit or check card numbers, or ...
... to an alleged security update, system maintenance, or an update in technology. Financial institutions will never send unsolicited e-mails requesting anyone to provide, update or verify account or personal information, such as passwords, Social Security numbers, PINs, credit or check card numbers, or ...
Phishing and whaling – Don`t get hooked!
... So how can your organisation stay safe? There is no guaranteed checklist but the following are some key protection measures: 1. Awareness training – Ensure everyone in your team is made aware of the risks. The more people are aware of the dangers, the less likelihood of being fooled by such attacks ...
... So how can your organisation stay safe? There is no guaranteed checklist but the following are some key protection measures: 1. Awareness training – Ensure everyone in your team is made aware of the risks. The more people are aware of the dangers, the less likelihood of being fooled by such attacks ...
NITC yearly Work Plan FY2065/66
... Endorsed – The policy has the support of management. Relevant - The policy is applicable to the organization Realistic – The policy makes sense Attainable – The policy can be successfully implemented Adaptable – The policy can accommodate change Enforceable – The policy is statutory. I ...
... Endorsed – The policy has the support of management. Relevant - The policy is applicable to the organization Realistic – The policy makes sense Attainable – The policy can be successfully implemented Adaptable – The policy can accommodate change Enforceable – The policy is statutory. I ...
Marine Center for Advanced Operational Culture Training
... culture based courses for 17 regions around the world. The training will range from one-hour briefings to scenario based e-learning and exercises. ...
... culture based courses for 17 regions around the world. The training will range from one-hour briefings to scenario based e-learning and exercises. ...
NetDay Cyber Security Kit for Schools
... community directors and finance managers, as well as school-level administrators, such as principals, guidance counselors and libraries. Safeguarding computers in the schools is not just for technology professionals: it is every administrator’s responsibility. While most school districts have securi ...
... community directors and finance managers, as well as school-level administrators, such as principals, guidance counselors and libraries. Safeguarding computers in the schools is not just for technology professionals: it is every administrator’s responsibility. While most school districts have securi ...