PowerPoint Presentation - Provider Backbone Transport
... a) Frame Loss Ratio (FLR) parameter is the number of service frames marked green on a per {VID, P, CoS} basis that are delivered by the Provider network versus the total sent. b) Frame Delay (FD) Measurement of round trip frame delay by ultiizing the OAM frames as defined in 802.1ag c) Frame Delay V ...
... a) Frame Loss Ratio (FLR) parameter is the number of service frames marked green on a per {VID, P, CoS} basis that are delivered by the Provider network versus the total sent. b) Frame Delay (FD) Measurement of round trip frame delay by ultiizing the OAM frames as defined in 802.1ag c) Frame Delay V ...
u1(z)=p1 z00000+p1{2}
... hostile environment, the ability of a system to tolerate both the impact of external factors (attack) and internal causes (accidental failures or errors) should be considered. The measure of this ability is referred to as system survivability. An external factors usually cause failures of group of s ...
... hostile environment, the ability of a system to tolerate both the impact of external factors (attack) and internal causes (accidental failures or errors) should be considered. The measure of this ability is referred to as system survivability. An external factors usually cause failures of group of s ...
Code-Red: a case study on the spread and victims of an Intemet worm
... router to reduce congestion caused by the worm blocked all external traffic to this network. Because this filter was put into place upstream of the monitor, we were unable to capture IP packet headers after 16:30 UTC. However, a backup data set consisting of sampled netflow [15] output from the filt ...
... router to reduce congestion caused by the worm blocked all external traffic to this network. Because this filter was put into place upstream of the monitor, we were unable to capture IP packet headers after 16:30 UTC. However, a backup data set consisting of sampled netflow [15] output from the filt ...
Service Definitions - text for CSA
... the set of attributes defined in the SD. The SD defines which attributes must be explicitly specified by the requester (i.e. they have no default value specified in the SD), and which may be omitted by the requester (the SD specifies a default value for the attribute.) The SD specifies the range of ...
... the set of attributes defined in the SD. The SD defines which attributes must be explicitly specified by the requester (i.e. they have no default value specified in the SD), and which may be omitted by the requester (the SD specifies a default value for the attribute.) The SD specifies the range of ...
A Dynamic Bulk Provisioning Framework for Concurrent
... hungry nature of NGN applications, these connections require the capacity of an entire wavelength along the path (referred to as a lightpath) and they are provisioned in the form of optical labeled switch paths (optical LSPs) [2]. In the remainder of this paper, use of the term LSP always refers a l ...
... hungry nature of NGN applications, these connections require the capacity of an entire wavelength along the path (referred to as a lightpath) and they are provisioned in the form of optical labeled switch paths (optical LSPs) [2]. In the remainder of this paper, use of the term LSP always refers a l ...
thesis_talk_mar5
... Ensuring/improving QoS – Network provisioning (voice traffic aggregation) Efficient, but may be expensive to deploy and manage – End-to-End (FEC > LBR, PLC) Easier to deploy, but must control overhead of FEC ...
... Ensuring/improving QoS – Network provisioning (voice traffic aggregation) Efficient, but may be expensive to deploy and manage – End-to-End (FEC > LBR, PLC) Easier to deploy, but must control overhead of FEC ...
Pi: A Path Identification Mechanism to Defend against DDoS attacks
... section of the field mark. Figure 2 shows the C code for the Pi basic marking scheme where the markingbits function simply returns the IP address that is passed to it. Figure 3 shows an example marking scenario, using 1-bit marking 1 Savage et al. [28, 29] were the first to argue that the IP Identif ...
... section of the field mark. Figure 2 shows the C code for the Pi basic marking scheme where the markingbits function simply returns the IP address that is passed to it. Figure 3 shows an example marking scenario, using 1-bit marking 1 Savage et al. [28, 29] were the first to argue that the IP Identif ...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 202-10099-01, April 2005
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
Ubee DDW365 Advanced Wireless Gateway
... Use only the power cable supplied with the device. Do not attach the power supply cable to building surfaces or floorings. Rest the power cable freely without any obstacles. Do not place heavy items on top of the power cable. Do not abuse, step, or walk on the cable. Do not place heavy objects o ...
... Use only the power cable supplied with the device. Do not attach the power supply cable to building surfaces or floorings. Rest the power cable freely without any obstacles. Do not place heavy items on top of the power cable. Do not abuse, step, or walk on the cable. Do not place heavy objects o ...
Ubee DDW365 Advanced Wireless Gateway
... Use only the power cable supplied with the device. Do not attach the power supply cable to building surfaces or floorings. Rest the power cable freely without any obstacles. Do not place heavy items on top of the power cable. Do not abuse, step, or walk on the cable. Do not place heavy objects o ...
... Use only the power cable supplied with the device. Do not attach the power supply cable to building surfaces or floorings. Rest the power cable freely without any obstacles. Do not place heavy items on top of the power cable. Do not abuse, step, or walk on the cable. Do not place heavy objects o ...
Achieving WAN Operational Efficiency with the Cisco ASR 1000 Series
... Routers, a new line of midrange routers that establish a new price-to-performance class offering, benefiting both enterprises and service providers. Cisco ASR 1000 Series Routers provide a great opportunity for simplifying the WAN edge and significantly decreasing network operating expenses (OpEx). ...
... Routers, a new line of midrange routers that establish a new price-to-performance class offering, benefiting both enterprises and service providers. Cisco ASR 1000 Series Routers provide a great opportunity for simplifying the WAN edge and significantly decreasing network operating expenses (OpEx). ...
Using Your Gateway WGR
... Insert the CD into the disc drive on the computer attached to your broadband modem. If the The Gateway Wireless-G Access Point/Router Setup Wizard opens, go to Step 5. - OR If the wizard does not start automatically, go to Step 2. ...
... Insert the CD into the disc drive on the computer attached to your broadband modem. If the The Gateway Wireless-G Access Point/Router Setup Wizard opens, go to Step 5. - OR If the wizard does not start automatically, go to Step 2. ...
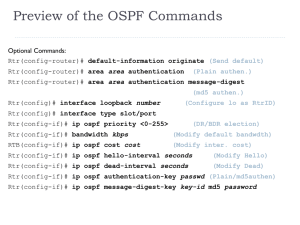
OSPF
... Note: In the context of BGP, a gateway is nothing else but an IP router that connects autonomous systems. Interdomain routing protocol for routing between autonomous systems Uses TCP to send routing messages BGP is neither a link state, nor a distance vector protocol. Routing messages in BGP contain ...
... Note: In the context of BGP, a gateway is nothing else but an IP router that connects autonomous systems. Interdomain routing protocol for routing between autonomous systems Uses TCP to send routing messages BGP is neither a link state, nor a distance vector protocol. Routing messages in BGP contain ...
Set Partitioning and Applications
... Finally in order to get integer solutions we need to “encapsulate” the column generation in a branch and bound framework. The total setup is often called Branch and Price. J. Larsen (DTU Mgmt Eng) ...
... Finally in order to get integer solutions we need to “encapsulate” the column generation in a branch and bound framework. The total setup is often called Branch and Price. J. Larsen (DTU Mgmt Eng) ...
Seminar Steganography
... as means to protect information Cryptographic techniques "scramble" messages so if intercepted, the messages cannot be understood Steganography, in an essence, "camouflages" a message to hide its existence and make it seem "invisible" thus concealing the fact that a message ...
... as means to protect information Cryptographic techniques "scramble" messages so if intercepted, the messages cannot be understood Steganography, in an essence, "camouflages" a message to hide its existence and make it seem "invisible" thus concealing the fact that a message ...
Paper Title (use style: paper title)
... communications where the number of sources could be very large. For scalability reasons, interactive multimedia applications could not be implemented as multiple instances of one-to-many. To receive multicast traffic, an interested receiver requires a mechanism to join the multicast group. The recei ...
... communications where the number of sources could be very large. For scalability reasons, interactive multimedia applications could not be implemented as multiple instances of one-to-many. To receive multicast traffic, an interested receiver requires a mechanism to join the multicast group. The recei ...
IPv6 (modified version)
... IPv6 Introduction Routing and Addressing Plug and Play Security/QoS Supports IPv4/Ipv6 Transition Mechanisms ...
... IPv6 Introduction Routing and Addressing Plug and Play Security/QoS Supports IPv4/Ipv6 Transition Mechanisms ...
PPP and Frame Relay
... – Routing technique that reduces the chance of routing loops on a network – Prevents routing update information received on one physical interface from being rebroadcast to other devices through that same physical interface – People also refer to this rule as nonbroadcast ...
... – Routing technique that reduces the chance of routing loops on a network – Prevents routing update information received on one physical interface from being rebroadcast to other devices through that same physical interface – People also refer to this rule as nonbroadcast ...
2920 Switch Series PDF
... administration by using a password authentication server • IEEE 802.1X, MAC, or Web authentication provides concurrent network access control and Web authentication of up to 24 clients per port • Secure shell encrypts all transmitted data for secure remote CLI access over IP networks • Secure Socket ...
... administration by using a password authentication server • IEEE 802.1X, MAC, or Web authentication provides concurrent network access control and Web authentication of up to 24 clients per port • Secure shell encrypts all transmitted data for secure remote CLI access over IP networks • Secure Socket ...
Patch Management Integration November 11, 2014 (Revision 20)
... Auditing TEM-Managed Linux Systems Package reporting is supported by RPM-based and Debian-based distributions that IBM TEM officially supports. This includes Red Hat derivatives such as RHEL, CentOS, Scientific Linux, and Oracle Linux, as well as Debian and Ubuntu. Other distributions may also work, ...
... Auditing TEM-Managed Linux Systems Package reporting is supported by RPM-based and Debian-based distributions that IBM TEM officially supports. This includes Red Hat derivatives such as RHEL, CentOS, Scientific Linux, and Oracle Linux, as well as Debian and Ubuntu. Other distributions may also work, ...
Module 8: Virtual LANs
... VLANs logically segment switched networks based on the functions, project teams, or applications of the organization regardless of the physical location or connections to the network. All workstations and servers used by a particular workgroup share the same VLAN, regardless of the physical connecti ...
... VLANs logically segment switched networks based on the functions, project teams, or applications of the organization regardless of the physical location or connections to the network. All workstations and servers used by a particular workgroup share the same VLAN, regardless of the physical connecti ...
DARD: Distributed Adaptive Routing for Datacenter
... those instances will be placed depends on machine availability, and is not guaranteed to be close to the application’s other instances. Therefore, it is important for a datacenter network to have high bisection bandwidth to avoid hot spots between any pair of hosts. To achieve this goal, today’s dat ...
... those instances will be placed depends on machine availability, and is not guaranteed to be close to the application’s other instances. Therefore, it is important for a datacenter network to have high bisection bandwidth to avoid hot spots between any pair of hosts. To achieve this goal, today’s dat ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.