USER MANUAL PROLiNK® Wireless
... 192.168.10.253 to be compatible with the Wireless Portable Router's default IP Address of 192.168.10.254. Also, the Network Mask must be set to 255.255.255.0. See Chapter 4 - PC Configuration for details on checking your PC's TCP/IP settings. ...
... 192.168.10.253 to be compatible with the Wireless Portable Router's default IP Address of 192.168.10.254. Also, the Network Mask must be set to 255.255.255.0. See Chapter 4 - PC Configuration for details on checking your PC's TCP/IP settings. ...
Assortativity and Mixing Complex Networks, Course 303A, Spring, 2009 Prof. Peter Dodds .
... cover much territory but do not represent all networks. Moving away from pure random networks was a key first step. ...
... cover much territory but do not represent all networks. Moving away from pure random networks was a key first step. ...
Chapter 5 Advanced Configuration
... to recognize some of these applications and to work properly with them, but there are other applications that may not function well. In some cases, one local computer can run the application properly if that computer’s IP address is entered as the default DMZ server. Incoming traffic from the Intern ...
... to recognize some of these applications and to work properly with them, but there are other applications that may not function well. In some cases, one local computer can run the application properly if that computer’s IP address is entered as the default DMZ server. Incoming traffic from the Intern ...
The Pulse Protocol: Energy Efficient Infrastructure Access
... The routing metric is tracked at the speed of the data flow Changes to the metric are only reported locally Routes are continuously adjusted as the metrics change High speed accurate route tracking is essentially an on-demand decompression of the topology ...
... The routing metric is tracked at the speed of the data flow Changes to the metric are only reported locally Routes are continuously adjusted as the metrics change High speed accurate route tracking is essentially an on-demand decompression of the topology ...
IP Networking Guide - Plantec Distribuidora
... VLANs are logical segments within a corporate LAN. By assigning VLAN settings to IP telephones, it is possible to separate the packets transmitted by an IP telephone according to the type of data and specify which VLAN each data type will be sent over. This allows you to avoid generating unnecessary ...
... VLANs are logical segments within a corporate LAN. By assigning VLAN settings to IP telephones, it is possible to separate the packets transmitted by an IP telephone according to the type of data and specify which VLAN each data type will be sent over. This allows you to avoid generating unnecessary ...
ZXHN H108N - Movistar.
... Describe the advanced configuration of wireless, port forwarding, DMZ, SAMBA, 3G WAN, parental control, filtering options, QoS, firewall, DNS, DDNS, network tools, rooting, schedules, NAT, DLNA, and IP tunnel. ...
... Describe the advanced configuration of wireless, port forwarding, DMZ, SAMBA, 3G WAN, parental control, filtering options, QoS, firewall, DNS, DDNS, network tools, rooting, schedules, NAT, DLNA, and IP tunnel. ...
Application Notes for Configuring QuesCom 400 IP/GSM Gateway
... These Application Notes describe a compliance-tested configuration consisting of a QuesCom 400 IP/GSM gateway networked with Avaya Communication Manager 3.1 using H.323 trunks. The QuesCom 400 IP/GSM is an IP-GSM-gateway, supporting outgoing and incoming GSM calls. All calls made from Avaya Communic ...
... These Application Notes describe a compliance-tested configuration consisting of a QuesCom 400 IP/GSM gateway networked with Avaya Communication Manager 3.1 using H.323 trunks. The QuesCom 400 IP/GSM is an IP-GSM-gateway, supporting outgoing and incoming GSM calls. All calls made from Avaya Communic ...
paper
... optimization. We can evaluate how often Tor’s default random relay selection produces high latency paths and whether different path selection approaches might be more difficult to deanonymize. By taking advantage of Tor as a system that is representative of volunteer-administered overlay, we can als ...
... optimization. We can evaluate how often Tor’s default random relay selection produces high latency paths and whether different path selection approaches might be more difficult to deanonymize. By taking advantage of Tor as a system that is representative of volunteer-administered overlay, we can als ...
IP Networks Curriculum
... Understanding Voice Communications: a Technical Introduction™.................................................................................................. 8 Springfield: An Introduction to Telecommunications™....................................................................................... ...
... Understanding Voice Communications: a Technical Introduction™.................................................................................................. 8 Springfield: An Introduction to Telecommunications™....................................................................................... ...
PDF
... Cisco Performance Routing removes this complexity from network operators and provides needed application performance when the network is operational but parts of the network are experiencing performance-degradation problems. Cisco PfR in its truest form is “application routing based on network perfo ...
... Cisco Performance Routing removes this complexity from network operators and provides needed application performance when the network is operational but parts of the network are experiencing performance-degradation problems. Cisco PfR in its truest form is “application routing based on network perfo ...
Name Resolution
... Where companies register their names with a name registration company Gives the company authority to create subdomains to further divide the domain ...
... Where companies register their names with a name registration company Gives the company authority to create subdomains to further divide the domain ...
Repeaters, Switches and Routers
... They buffer the complete packet before making a forwarding decision Error detection occurs on the header Traditionally used to interconnect two dissimilar LANs (eg ATM and Token Ring). More recently have lost this role to Switches. ...
... They buffer the complete packet before making a forwarding decision Error detection occurs on the header Traditionally used to interconnect two dissimilar LANs (eg ATM and Token Ring). More recently have lost this role to Switches. ...
Code-Red: a case study on the spread and victims of an
... router to reduce congestion caused by the worm blocked all external traffic to this network. Because this filter was put into place upstream of the monitor, we were unable to capture IP packet headers after 16:30 UTC. However, a backup data set consisting of sampled netflow [15] output from the filt ...
... router to reduce congestion caused by the worm blocked all external traffic to this network. Because this filter was put into place upstream of the monitor, we were unable to capture IP packet headers after 16:30 UTC. However, a backup data set consisting of sampled netflow [15] output from the filt ...
transparencies - Indico
... Based on 1 Gigabit payload the total bandwidth with upcoding and overhead should not be more than 1.2 Gigabit. The Gigabit Ethernet community struggled a long time with technological problems on the physical link level. Finally The Gigabit Ethernet group adapted the 1 Gigabit Fibre Channel Technolog ...
... Based on 1 Gigabit payload the total bandwidth with upcoding and overhead should not be more than 1.2 Gigabit. The Gigabit Ethernet community struggled a long time with technological problems on the physical link level. Finally The Gigabit Ethernet group adapted the 1 Gigabit Fibre Channel Technolog ...
here - Campaign[x]
... Next-day-ship hardware replacement on Cisco Catalyst® 3750-X, Catalyst 3560-X, and Catalyst 2960-S ...
... Next-day-ship hardware replacement on Cisco Catalyst® 3750-X, Catalyst 3560-X, and Catalyst 2960-S ...
Ubee DVW32CB
... Using the Parental Control User Setup Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . Using the Basic Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Using the ToD Filter Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... Using the Parental Control User Setup Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . Using the Basic Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Using the ToD Filter Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
Assortativity and Mixing Complex Networks CSYS/MATH 303, Spring, 2011 Prof. Peter Dodds
... These findings are intuitively reasonable. If the network mixes assortatively, then the high-degree vertices will tend to stick together in a subnetwork or core group of higher mean degree than the network as a whole. It is reasonable to suppose that percolation would occur earlier within such a sub ...
... These findings are intuitively reasonable. If the network mixes assortatively, then the high-degree vertices will tend to stick together in a subnetwork or core group of higher mean degree than the network as a whole. It is reasonable to suppose that percolation would occur earlier within such a sub ...
The CELTIC Office Workplan
... • Challenges with inter-PDN-GW and inter-ePDG mobility – Re-authentication in handovers involves multiple protocols (IKEv2 and EAP) of different layers (L3 and L2, respectfully) currently – The above mentioned protocols induce extensive amount of signaling – Distributed GWs mean more handovers and r ...
... • Challenges with inter-PDN-GW and inter-ePDG mobility – Re-authentication in handovers involves multiple protocols (IKEv2 and EAP) of different layers (L3 and L2, respectfully) currently – The above mentioned protocols induce extensive amount of signaling – Distributed GWs mean more handovers and r ...
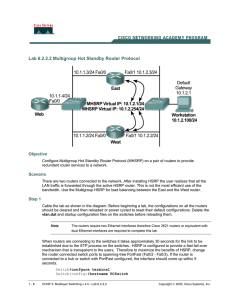
Lab 6.2.2.2 Multigroup Hot Standby Router Protocol
... should be cleared and then reloaded or power cycled to reset their default configurations. Delete the vlan.dat and startup configuration files on the switches before reloading them. Note ...
... should be cleared and then reloaded or power cycled to reset their default configurations. Delete the vlan.dat and startup configuration files on the switches before reloading them. Note ...
DSL-300G ADSL Modem User’s Guide
... (“Software”) will substantially conform to D-Link Australia’s then current functional specifications for the Software, as set forth in the application documentation, from the date of original delivery of the Software for the period of Ninety (90) days (“Warranty Period”), if the Software is properly ...
... (“Software”) will substantially conform to D-Link Australia’s then current functional specifications for the Software, as set forth in the application documentation, from the date of original delivery of the Software for the period of Ninety (90) days (“Warranty Period”), if the Software is properly ...
What is an IP address?
... What Do We Mean by “Ethernet”? A physical layer; the most widely used interconnect standard for LANs ...
... What Do We Mean by “Ethernet”? A physical layer; the most widely used interconnect standard for LANs ...
Guide to TCP/IP, Third Edition
... NetBIOS and DNS Name Resolution • To convert NetBIOS name into name that is recognizable and routable by DNS – NetBIOS name had to become a usable host name – Domain portion of the name had to be added ...
... NetBIOS and DNS Name Resolution • To convert NetBIOS name into name that is recognizable and routable by DNS – NetBIOS name had to become a usable host name – Domain portion of the name had to be added ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.








![here - Campaign[x]](http://s1.studyres.com/store/data/008744944_1-0f4fd57a8eb108cf9826822f0ba0b000-300x300.png)