- TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
- TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
Understanding KaZaA
... Many users today use KaZaA-Lite [11], an unofficial copy of KMD, rather than the KaZaA client(KMD) distributed by Sharman. Each KaZaA-Lite client emulates Sharman’s KMD and participates in the KaZaA network. During the search process, a KaZaA-Lite ON first sends its query to the SN to which it is co ...
... Many users today use KaZaA-Lite [11], an unofficial copy of KMD, rather than the KaZaA client(KMD) distributed by Sharman. Each KaZaA-Lite client emulates Sharman’s KMD and participates in the KaZaA network. During the search process, a KaZaA-Lite ON first sends its query to the SN to which it is co ...
Web Page Configuration
... Primarily configuration is done using the MConfig Software however configurations can be made by connecting to the modules internal web pages. Please Note : It is recomeneded the configuration be done solely byone or the other. Try to avoid configuring modules using both config software and web page ...
... Primarily configuration is done using the MConfig Software however configurations can be made by connecting to the modules internal web pages. Please Note : It is recomeneded the configuration be done solely byone or the other. Try to avoid configuring modules using both config software and web page ...
TUCAA: The Ultimate Computer Acronyms Archive
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
... «I'm sitting in a coffee shop in Milford, NH. In the booth next to me are two men, a father and a son. Over coffee, the father is asking his son about modems, and the son is holding forth pretty well on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The ...
PDF - Complete Book (3.05 MB)
... An access control list (ACL) consists of one or more access control entries (ACE) that collectively define the network traffic profile. This profile can then be referenced by Cisco IOS XR software features such as traffic filtering, route filtering, QoS classification, and access control. There are ...
... An access control list (ACL) consists of one or more access control entries (ACE) that collectively define the network traffic profile. This profile can then be referenced by Cisco IOS XR software features such as traffic filtering, route filtering, QoS classification, and access control. There are ...
ORAN: OpenFlow Routers for Academic Networks
... in a cooperation among a large number of telecommunication equipment vendors and providers with the coordination of the PCI Industrial Computers Manufacturers Group (PICMG) [11]. The specifications, denoted as PICMG 3.X, are aimed at addressing the requirements of telecommunication equipment provide ...
... in a cooperation among a large number of telecommunication equipment vendors and providers with the coordination of the PCI Industrial Computers Manufacturers Group (PICMG) [11]. The specifications, denoted as PICMG 3.X, are aimed at addressing the requirements of telecommunication equipment provide ...
www.comcom.govt.nz
... transmission system to carry many calls (known as trunking). The telephone exchange becomes a collection point, which aggregates tens, hundreds, or thousands of calls onto a single transmission link between exchanges. The same need exists for data networks like the Internet. Customer traffic is aggr ...
... transmission system to carry many calls (known as trunking). The telephone exchange becomes a collection point, which aggregates tens, hundreds, or thousands of calls onto a single transmission link between exchanges. The same need exists for data networks like the Internet. Customer traffic is aggr ...
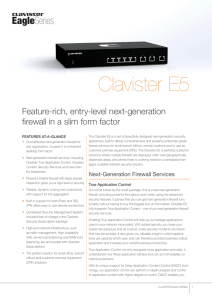
Clavister E5
... like High Availability (HA) is fully supported, as well as Fast Route Failover technologies and link aggregation, which ensures that your business is not affected by network downtime caused by link failure or hardware problem. It also support flood protection technologies to increase uptime in case ...
... like High Availability (HA) is fully supported, as well as Fast Route Failover technologies and link aggregation, which ensures that your business is not affected by network downtime caused by link failure or hardware problem. It also support flood protection technologies to increase uptime in case ...
FiOS Gateway USER GUIDE - Frontier Communications
... • Ethernet LAN - connects devices to your Gateway using Ethernet cables to join the local area network (LAN). The four Ethernet LAN ports are 10/100/1000 Mbps auto-sensing and can be used with either straight-through or crossover Ethernet cables. • HAN Expansion Port - provides for future hardware ...
... • Ethernet LAN - connects devices to your Gateway using Ethernet cables to join the local area network (LAN). The four Ethernet LAN ports are 10/100/1000 Mbps auto-sensing and can be used with either straight-through or crossover Ethernet cables. • HAN Expansion Port - provides for future hardware ...
Tricha Anjali of - BWN-Lab
... LSP and lSP Setup Problem - “Optimal Policy for LSP Setup in MPLS Networks,” Computer Networks Journal, June 2002 - “LSP and lSP Setup in GMPLS Networks,” Proceedings of IEEE INFOCOM, March 2004 ...
... LSP and lSP Setup Problem - “Optimal Policy for LSP Setup in MPLS Networks,” Computer Networks Journal, June 2002 - “LSP and lSP Setup in GMPLS Networks,” Proceedings of IEEE INFOCOM, March 2004 ...
Top-Down Network Design
... Priscilla Oppenheimer has been developing data communications and networking systems since 1980 when she earned her master’s degree in information science from the University of Michigan. After many years as a software developer, she became a technical instructor and training developer and has taugh ...
... Priscilla Oppenheimer has been developing data communications and networking systems since 1980 when she earned her master’s degree in information science from the University of Michigan. After many years as a software developer, she became a technical instructor and training developer and has taugh ...
ccna3-mod4-SwitchingConcept
... This situation is analogous to a number of cars all trying to access a one-lane road at the same time. Because the road has only one lane, only one car can access it at a time. The introduction of hubs into a network resulted in more users competing for the same bandwidth. Collisions are a by-produc ...
... This situation is analogous to a number of cars all trying to access a one-lane road at the same time. Because the road has only one lane, only one car can access it at a time. The introduction of hubs into a network resulted in more users competing for the same bandwidth. Collisions are a by-produc ...
SoftRouter Plus User Guide
... modem, xDSL modem or a router, the SoftRouter Plus computer requires a separate Ethernet interface for this connection. This may be the built-in Ethernet interface on the Macintosh or a plug-in Ethernet card. One or more local area network (LAN) connections are required on the SoftRouter Plus Macint ...
... modem, xDSL modem or a router, the SoftRouter Plus computer requires a separate Ethernet interface for this connection. This may be the built-in Ethernet interface on the Macintosh or a plug-in Ethernet card. One or more local area network (LAN) connections are required on the SoftRouter Plus Macint ...
Layer 2 Technologies
... Benefits of LAN Switch • No collision domain, because of microsegmentation. • Low latency levels and a high rate of speed for frame forwarding • Increases the bandwidth available on a network ...
... Benefits of LAN Switch • No collision domain, because of microsegmentation. • Low latency levels and a high rate of speed for frame forwarding • Increases the bandwidth available on a network ...
Understanding IPv6
... Coexistence mechanisms Tunneling configurations 6over4 6to4 ISATAP PortProxy Migrating to IPv6 Understanding IPv6 ...
... Coexistence mechanisms Tunneling configurations 6over4 6to4 ISATAP PortProxy Migrating to IPv6 Understanding IPv6 ...
Addressing Context Dependency using Profile Context in Overlay
... computing has picked up pace in recent times. Though, various types of traits can be utilized to characterize a situation, applications leveraging location are the most common in mainstream pervasive services. The use of context information in the form of user availability to start a conversation ha ...
... computing has picked up pace in recent times. Though, various types of traits can be utilized to characterize a situation, applications leveraging location are the most common in mainstream pervasive services. The use of context information in the form of user availability to start a conversation ha ...
Querying Network Graphs with Recursive Queries
... commonly-used recursive queries using PIER. These queries are variants of the transitive closure query, which can be used to compute reachability information within a graph. We will further show how our execution techniques can be generalized to support dynamic graphs, and to facilitate work sharing ...
... commonly-used recursive queries using PIER. These queries are variants of the transitive closure query, which can be used to compute reachability information within a graph. We will further show how our execution techniques can be generalized to support dynamic graphs, and to facilitate work sharing ...
What Is a Virtual Private Network?
... The Secure Sockets Layer (SSL)—SSL is a security protocol that was originally developed by Netscape Communications (SSL versions 1, 2, and 3), and it provides secure remote access for mobile users or home users. Functionality may be limited (when compared with L2F, PPTP, L2TPv2, or IPsec) if clientl ...
... The Secure Sockets Layer (SSL)—SSL is a security protocol that was originally developed by Netscape Communications (SSL versions 1, 2, and 3), and it provides secure remote access for mobile users or home users. Functionality may be limited (when compared with L2F, PPTP, L2TPv2, or IPsec) if clientl ...
Network Working Group G. Bernstein Request for
... An MPLS network consists of MPLS nodes called Label Switch Routers (LSRs) connected via Label Switched Paths (LSPs). An LSP is unidirectional and could be of several different types such as pointto-point, point-to-multipoint, and multipoint-to-point. Border LSRs in an MPLS network act as either ingr ...
... An MPLS network consists of MPLS nodes called Label Switch Routers (LSRs) connected via Label Switched Paths (LSPs). An LSP is unidirectional and could be of several different types such as pointto-point, point-to-multipoint, and multipoint-to-point. Border LSRs in an MPLS network act as either ingr ...
User`s Manual
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate ...
CT-500S ADSL Router User`s Manual
... An RS232 straight-through cable to connect to the Console PortAn RS232, DB9-to-DB9 straight-through cable is required to connect the terminal to the device. An AC power adapter cord to connect to the Power jackA suitable AC-to-AC power adapter cord is shipped with the device. It is used to provide t ...
... An RS232 straight-through cable to connect to the Console PortAn RS232, DB9-to-DB9 straight-through cable is required to connect the terminal to the device. An AC power adapter cord to connect to the Power jackA suitable AC-to-AC power adapter cord is shipped with the device. It is used to provide t ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.