Cisco Catalyst 3550 Series Switches for Metro Access
... through the service provider’s network. The 802.1Q tunneling feature enables service providers to use a single VLAN (up to 4096 VLAN IDs) to support customers who have multiple VLANs. In addition, the feature preserves customers’ original VLAN IDs and segregates traffic from different customers with ...
... through the service provider’s network. The 802.1Q tunneling feature enables service providers to use a single VLAN (up to 4096 VLAN IDs) to support customers who have multiple VLANs. In addition, the feature preserves customers’ original VLAN IDs and segregates traffic from different customers with ...
PPT
... generations of Ethernet and show how it has evolved. We discuss other wired networks that we encounter in the Internet today, such as point-to-point networks and switched networks. We discuss connecting devices used in the lower three layers of the TCP/IP protocol such as hubs, link-layer switch ...
... generations of Ethernet and show how it has evolved. We discuss other wired networks that we encounter in the Internet today, such as point-to-point networks and switched networks. We discuss connecting devices used in the lower three layers of the TCP/IP protocol such as hubs, link-layer switch ...
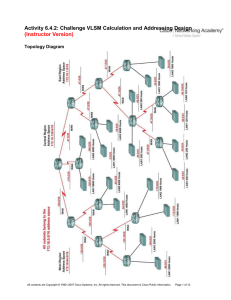
2e_06_6_4_2_vlsm_instr
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
EH34803812
... Tappen Morris, was the first known worm that had malicious intent. According to the author, the worm was not suppose to cause any damage and was intended to gauge the size of the internet. It however, did cause DoS attacks. The worm exploited the vulnerabilities of Unix sendmail, rsh/rexec and weak ...
... Tappen Morris, was the first known worm that had malicious intent. According to the author, the worm was not suppose to cause any damage and was intended to gauge the size of the internet. It however, did cause DoS attacks. The worm exploited the vulnerabilities of Unix sendmail, rsh/rexec and weak ...
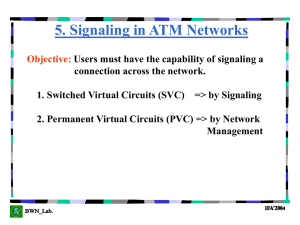
ATM End User
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
The Gartner Glossary of Information Technology Acronyms and Terms
... differs from traditional cost accounting in explicitly recognizing that not all cost objects place an equal demand on support resources. ABEND (abnormal end) A type of system error in which a task or program fails to execute properly (i.e., “abnormally ends”). The term is also used as the name for a ...
... differs from traditional cost accounting in explicitly recognizing that not all cost objects place an equal demand on support resources. ABEND (abnormal end) A type of system error in which a task or program fails to execute properly (i.e., “abnormally ends”). The term is also used as the name for a ...
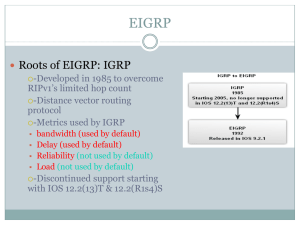
EIGRP
... routing tables for each Network layer protocol. • The IP-EIGRP module is responsible for sending and receiving EIGRP packets that are encapsulated in IP and for using DUAL to build and maintain the IP routing table. • The IPX EIGRP module is responsible for exchanging routing information about IPX n ...
... routing tables for each Network layer protocol. • The IP-EIGRP module is responsible for sending and receiving EIGRP packets that are encapsulated in IP and for using DUAL to build and maintain the IP routing table. • The IPX EIGRP module is responsible for exchanging routing information about IPX n ...
view pdf - Christoph Sommer and Falko Dressler: Vehicular
... Copyright © 2009‐2015 Christoph Sommer, but made available to you under a Creative Commons Attribution‐ShareAlike 4.0 International License. ▪ In brief, this means you can share and adapt the slides as long as you follow the terms set out in this license [1]. If you split this slide deck into mult ...
... Copyright © 2009‐2015 Christoph Sommer, but made available to you under a Creative Commons Attribution‐ShareAlike 4.0 International License. ▪ In brief, this means you can share and adapt the slides as long as you follow the terms set out in this license [1]. If you split this slide deck into mult ...
Effective communication - Docbox
... Where Smart Grids meet M2M Smart grids needs a reliable and gridwide monitoring infrastructure “Most utilities don't know that users have lost power until customers pick up the phone and call them” WASA: Monitoring and display of power-system components and performance across interconnections ...
... Where Smart Grids meet M2M Smart grids needs a reliable and gridwide monitoring infrastructure “Most utilities don't know that users have lost power until customers pick up the phone and call them” WASA: Monitoring and display of power-system components and performance across interconnections ...
chapter 5 - BWN-Lab
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
XBee® 865/868LP RF Modules
... The choice of antenna and antenna location is very important for optimal performance. With the exception of the RF Pad variant, XBees do not require additional ground planes on the host PCB. In general, antenna elements radiate perpendicular to the direction they point. Thus a vertical antenna emits ...
... The choice of antenna and antenna location is very important for optimal performance. With the exception of the RF Pad variant, XBees do not require additional ground planes on the host PCB. In general, antenna elements radiate perpendicular to the direction they point. Thus a vertical antenna emits ...
TD-W8961NB 300Mbps Wireless N ADSL2+ Modem Router - TP-Link
... The device is designed to provide a simple and cost-effective ADSL Internet connection for a private Ethernet or IEEE 802.11n/ IEEE 802.11g/ IEEE 802.11b wireless network. The TD-W8961NB connects to an Ethernet LAN or computers via standard Ethernet ports. The ADSL connection is made using ordinary ...
... The device is designed to provide a simple and cost-effective ADSL Internet connection for a private Ethernet or IEEE 802.11n/ IEEE 802.11g/ IEEE 802.11b wireless network. The TD-W8961NB connects to an Ethernet LAN or computers via standard Ethernet ports. The ADSL connection is made using ordinary ...
High Availability WLANs Based on Software-Defined
... communication technology and a huge amount of research has been conducted in this area. However, most of these existing research works only provide theoretical SDN concepts and they hardly show any implementation or testbed results. In order to market the SDN technology, useful real-time practical a ...
... communication technology and a huge amount of research has been conducted in this area. However, most of these existing research works only provide theoretical SDN concepts and they hardly show any implementation or testbed results. In order to market the SDN technology, useful real-time practical a ...
Document
... cases. Where in case of explicit-path case, along with source and destination information we need to input the next-hop addresses along the path to the destination. Advantages: This idea solves certain network administrative problems involved with RSVP in networks where RSVP is used. Today due to R ...
... cases. Where in case of explicit-path case, along with source and destination information we need to input the next-hop addresses along the path to the destination. Advantages: This idea solves certain network administrative problems involved with RSVP in networks where RSVP is used. Today due to R ...
Duplicate Address Detection in IPv6 Mobile Ad Hoc Network
... Nodes that are not on a selected path don’t maintain routing information or participate in routing table exchanges. ...
... Nodes that are not on a selected path don’t maintain routing information or participate in routing table exchanges. ...
NOTE - Surveillance System, Security Cameras, CCTV Articles
... Can I use IPMaps with my PPPoE or PPPoA connection? . . . . . 77 Will IPMaps allow IP addresses from different subnets to be assigned to my Gateway? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77 IPMaps Block Diagram. . . . . . . . . . . . . . . . . . . . . . ...
... Can I use IPMaps with my PPPoE or PPPoA connection? . . . . . 77 Will IPMaps allow IP addresses from different subnets to be assigned to my Gateway? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77 IPMaps Block Diagram. . . . . . . . . . . . . . . . . . . . . . ...
cis185-ROUTE-lecture6-BGP-Part1
... Suppose, for example, that through some misconfiguration you advertise 207.46.0.0/16 to your ISP. On the receiving side, the ISP does not filter out this incorrect route, allowing it to be advertised to the rest of the Internet. This particular CIDR block belongs to Microsoft, and you have jus ...
... Suppose, for example, that through some misconfiguration you advertise 207.46.0.0/16 to your ISP. On the receiving side, the ISP does not filter out this incorrect route, allowing it to be advertised to the rest of the Internet. This particular CIDR block belongs to Microsoft, and you have jus ...
Title Subtitle - Aalborg Universitet
... • Top one or two labels are contained in the VPI/VCI fields of ATM header — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL i ...
... • Top one or two labels are contained in the VPI/VCI fields of ATM header — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL i ...
TR 0006 - oneM2M
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
International Technical Support Organization Asynchronous
... Take Note! Before using this information and the product it supports, be sure to read the general information under “Special Notices” on page xv. ...
... Take Note! Before using this information and the product it supports, be sure to read the general information under “Special Notices” on page xv. ...
twamp - rfc-5357 - H
... Based on RFC-5357 standard, TWAMP use the methodology and the architecture of OWAMP (One Way Active Measurement Protocol based on RFC-4656) foundation, where Round Trip or Two Way Measurement has been added to have additional tool to isolate Network issue and for Network Performance optimization. Th ...
... Based on RFC-5357 standard, TWAMP use the methodology and the architecture of OWAMP (One Way Active Measurement Protocol based on RFC-4656) foundation, where Round Trip or Two Way Measurement has been added to have additional tool to isolate Network issue and for Network Performance optimization. Th ...
3346 Software User Guide V6.3
... Netopia and Cayman are registered trademarks, and “Making Broadband Work” is a trademark of Netopia, Inc. All rights reserved. Ethernet is a registered trademark of Xerox Corporation. Microsoft and Windows are registered trademarks of Microsoft Corporation. All other trademarks are the property of t ...
... Netopia and Cayman are registered trademarks, and “Making Broadband Work” is a trademark of Netopia, Inc. All rights reserved. Ethernet is a registered trademark of Xerox Corporation. Microsoft and Windows are registered trademarks of Microsoft Corporation. All other trademarks are the property of t ...
Document - Fortinet Document Library
... This feature is used to "hint" to upstream DCHPv6 servers a desired prefix length for their subnet to be assigned in response to its request. There is a possibility of duplicate prefixes being sent by ISP when using a /64 bit subnet because the first 64 bits of the address are derived from the mac a ...
... This feature is used to "hint" to upstream DCHPv6 servers a desired prefix length for their subnet to be assigned in response to its request. There is a possibility of duplicate prefixes being sent by ISP when using a /64 bit subnet because the first 64 bits of the address are derived from the mac a ...
source code - Gaming Standards Association
... • Schema validation will catch all misspellings • Schema validation will catch all commands missing required values • Schema validation provides a sieve that strains out errors in commands • The result is that these errors will not reach the field. This means more reliable communication software GLI ...
... • Schema validation will catch all misspellings • Schema validation will catch all commands missing required values • Schema validation provides a sieve that strains out errors in commands • The result is that these errors will not reach the field. This means more reliable communication software GLI ...
Exploration CCNA4 - College of DuPage
... –Service providers sometimes sell more capacity than they have on the assumption that not everyone will demand their entitled capacity all of the time. –Because of oversubscription, there will be instances when the sum of CIRs from multiple PVCs to a given location is higher than the port or access ...
... –Service providers sometimes sell more capacity than they have on the assumption that not everyone will demand their entitled capacity all of the time. –Because of oversubscription, there will be instances when the sum of CIRs from multiple PVCs to a given location is higher than the port or access ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.