Sams Teach Yourself Networking in 24 Hours
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
Personal Area Networking Bluetooth Profile
... The Personal Area Networking (PAN) Profile describe how two or more Bluetooth enabled devices can form an ad-hoc network and how the same mechanism can be used to access a remote network through a network access point. The profile roles contained in this document are the Network Access Point, Group ...
... The Personal Area Networking (PAN) Profile describe how two or more Bluetooth enabled devices can form an ad-hoc network and how the same mechanism can be used to access a remote network through a network access point. The profile roles contained in this document are the Network Access Point, Group ...
vipersat file streamer user guide
... protocol rather than using TCP, a common standard for computer communications. The advantages that TCP/IP provides for typical internet communications can become limitations when passing traffic over a satellite network, where inherent delays can be mistaken for congestion or low bandwidth, resultin ...
... protocol rather than using TCP, a common standard for computer communications. The advantages that TCP/IP provides for typical internet communications can become limitations when passing traffic over a satellite network, where inherent delays can be mistaken for congestion or low bandwidth, resultin ...
Mixed SpaceWire - SpaceFibre Networks
... • SpaceWire supports bi-directional traffic of up to 200Mbit/sec over a distance up to 10m. • SpaceFibre shall be capable to improve to both figures by at least a factor of 10: – Data rates ≥ 2.5Gbit/sec – Distance ≥ 100m – Provide additional features like galvanic isolation • This requires a number ...
... • SpaceWire supports bi-directional traffic of up to 200Mbit/sec over a distance up to 10m. • SpaceFibre shall be capable to improve to both figures by at least a factor of 10: – Data rates ≥ 2.5Gbit/sec – Distance ≥ 100m – Provide additional features like galvanic isolation • This requires a number ...
IPsec - Allied Telesis
... create multiple SAs within the tunnel, so that different streams of traffic within the tunnel are encrypted by different SAs. The latter case is necessitated by connections with some legacy devices that may not support route based VPNs. It may instead attempt to negotiate the use of IP address traff ...
... create multiple SAs within the tunnel, so that different streams of traffic within the tunnel are encrypted by different SAs. The latter case is necessitated by connections with some legacy devices that may not support route based VPNs. It may instead attempt to negotiate the use of IP address traff ...
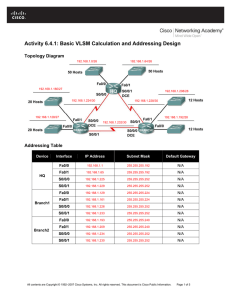
Activity 6.4.1: Basic VLSM Calculation and Addressing Design
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
Model FVL328 ProSafe High-Speed VPN Firewall Reference
... Voluntary Control Council for Interference (VCCI) Statement This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment ...
... Voluntary Control Council for Interference (VCCI) Statement This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment ...
Application Note: How to Evaluate WirelessHART Network and Device Performance
... the bandwidth. By default, the SmartMesh WirelessHART manager uses a 256-slot superframe, and the set of frame sizes is called a profile, here P1. P2 changes the downstream frame to 2048 slots to save power in cases where little or no downstream traffic is expected. A longer frame means fewer downst ...
... the bandwidth. By default, the SmartMesh WirelessHART manager uses a 256-slot superframe, and the set of frame sizes is called a profile, here P1. P2 changes the downstream frame to 2048 slots to save power in cases where little or no downstream traffic is expected. A longer frame means fewer downst ...
Oracle EDR InfiniBand Fabric Data Sheet
... Unlike traditional software-based transport protocol processing, InfiniBand provides hardware support for all of the services required to move data between hosts. By providing reliable end-to-end transport protocols in hardware and user-level RDMA capability, interconnected systems have more cycles ...
... Unlike traditional software-based transport protocol processing, InfiniBand provides hardware support for all of the services required to move data between hosts. By providing reliable end-to-end transport protocols in hardware and user-level RDMA capability, interconnected systems have more cycles ...
TDC 563-98-301/302, Spring 2002 2-14 TDC 563-98
... •Database Description: When a router just came up, it cannot wait for all link state packets. Neighbors will send it a database description (not the full database but like an outline). From this, the router can then ask for information it does not have. Describes the contents of the topological data ...
... •Database Description: When a router just came up, it cannot wait for all link state packets. Neighbors will send it a database description (not the full database but like an outline). From this, the router can then ask for information it does not have. Describes the contents of the topological data ...
TDMoIP : IPR
... since ATM switches do not participate in IP routing protocols every IP router must be logically adjacent to every other and we need ~ N2 ATM VCs ! if only the ATM switches could understand IP routing protocols! ...
... since ATM switches do not participate in IP routing protocols every IP router must be logically adjacent to every other and we need ~ N2 ATM VCs ! if only the ATM switches could understand IP routing protocols! ...
V1.0.0 vom 15.10.2014
... International Freephone Services ............................................................................... 19 ...
... International Freephone Services ............................................................................... 19 ...
FortiOS™ Handbook - Advanced Routing for FortiOS 5.2
... network equipment is moved without warning, and other such events happen that prevent static routes from reaching their destinations. When any changes such as these happen along a static route, traffic can no longer reach the destination — the route goes down. Dynamic routing can address these chang ...
... network equipment is moved without warning, and other such events happen that prevent static routes from reaching their destinations. When any changes such as these happen along a static route, traffic can no longer reach the destination — the route goes down. Dynamic routing can address these chang ...
lim-previous-version
... established for verification of full routing path through dual stack network. For verifying end-to-end connection, multiple IPv6 special zone will be activated by multiple ISPs. ISP must enable IPv6 network on its backbone and access network for providing IPv6 connectivity at IPv6 special zone. Each ...
... established for verification of full routing path through dual stack network. For verifying end-to-end connection, multiple IPv6 special zone will be activated by multiple ISPs. ISP must enable IPv6 network on its backbone and access network for providing IPv6 connectivity at IPv6 special zone. Each ...
D23 - Report on Integrated Test Scenarios
... marketplace: mobile operators monitor and measure their network, but these data are highly confidential, since they reflect the strengths and weaknesses of their network and could be used against them by competing operators. ...
... marketplace: mobile operators monitor and measure their network, but these data are highly confidential, since they reflect the strengths and weaknesses of their network and could be used against them by competing operators. ...
TL-WR542G 54M Wireless Router
... administrators can establish restricted access policies for children or staff. It has built-in NAT and DHCP server supporting static IP address distributing. It also supports Virtual Server and DMZ host for Port Triggering needs, and remote management and log so that network administrators can manag ...
... administrators can establish restricted access policies for children or staff. It has built-in NAT and DHCP server supporting static IP address distributing. It also supports Virtual Server and DMZ host for Port Triggering needs, and remote management and log so that network administrators can manag ...
Multicast Virtual Private Networks
... than having to send a stream to each server, which is the case with unicast, a source can send one stream and let the network do the work in getting that stream to anyone who wants to receive it. Multicast also keeps track of where the interested receivers are, so unlike broadcast, the stream only g ...
... than having to send a stream to each server, which is the case with unicast, a source can send one stream and let the network do the work in getting that stream to anyone who wants to receive it. Multicast also keeps track of where the interested receivers are, so unlike broadcast, the stream only g ...
Hack Attacks Revealed
... feel nothing matters… that the world is rigged. Perhaps, this is why we always look for conspiracies, and when they don’t exist, we create them ourselves. Maybe I will tap another military switch… Why are we like this? We are different from other people, and those others cannot always accept this. W ...
... feel nothing matters… that the world is rigged. Perhaps, this is why we always look for conspiracies, and when they don’t exist, we create them ourselves. Maybe I will tap another military switch… Why are we like this? We are different from other people, and those others cannot always accept this. W ...
DSL-G624T Wireless ADSL Router User Guide
... One DSL-G624T ADSL Ethernet Router One CD-ROM containing the User’s Guide and Quick Installation Guide One twisted-pair telephone cable used for ADSL connection One straight-through Ethernet cable One power adapter suitable for your electric service One Quick Installation Guide ...
... One DSL-G624T ADSL Ethernet Router One CD-ROM containing the User’s Guide and Quick Installation Guide One twisted-pair telephone cable used for ADSL connection One straight-through Ethernet cable One power adapter suitable for your electric service One Quick Installation Guide ...
Hack Attacks Revealed
... feel nothing matters… that the world is rigged. Perhaps, this is why we always look for conspiracies, and when they don’t exist, we create them ourselves. Maybe I will tap another military switch… Why are we like this? We are different from other people, and those others cannot always accept this. W ...
... feel nothing matters… that the world is rigged. Perhaps, this is why we always look for conspiracies, and when they don’t exist, we create them ourselves. Maybe I will tap another military switch… Why are we like this? We are different from other people, and those others cannot always accept this. W ...
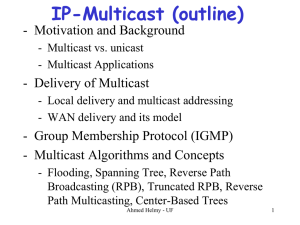
Multicast Routing
... (IANA) registers IP multicast groups. • The block of multicast addresses ranging from (224.0.0.1) to (224.0.0.255) is reserved for local LAN multicast: – used by routing protocols and other low-level topology discovery or maintenance protocols – E.g., "all-hosts" group (224.0.0.1), "all-routers” gro ...
... (IANA) registers IP multicast groups. • The block of multicast addresses ranging from (224.0.0.1) to (224.0.0.255) is reserved for local LAN multicast: – used by routing protocols and other low-level topology discovery or maintenance protocols – E.g., "all-hosts" group (224.0.0.1), "all-routers” gro ...
Routing Information Protocol
... Update Timer (default 30 seconds) – indicates how often the router will send out a routing table update. Invalid Timer (default 180 seconds) – indicates how long a route will remain in a routing table before being marked as invalid, if no new updates are heard about this route. The invalid timer wil ...
... Update Timer (default 30 seconds) – indicates how often the router will send out a routing table update. Invalid Timer (default 180 seconds) – indicates how long a route will remain in a routing table before being marked as invalid, if no new updates are heard about this route. The invalid timer wil ...
Where is the collision domain?
... switches Isolates collision domains (each LAN segment is a separate collision domain), THIS WILL REDUCE THE POSSIBILITY OF COLLISIONS AND result in higher total max throughput (see next slide) switch forwards a frame with broadcast address to all devices attached to the whole network (single broadca ...
... switches Isolates collision domains (each LAN segment is a separate collision domain), THIS WILL REDUCE THE POSSIBILITY OF COLLISIONS AND result in higher total max throughput (see next slide) switch forwards a frame with broadcast address to all devices attached to the whole network (single broadca ...
Before You Begin: Assign Information Classification
... 10 Gigabit Ethernet environment with a unified fabric for the LAN and SAN Cisco Nexus 5010 Switches that support Fiber Channel over Ethernet Cisco Nexus 7010 Switches to connect to the IP network and Cisco MDS 9509 Multilayer Director to connect to the SAN ...
... 10 Gigabit Ethernet environment with a unified fabric for the LAN and SAN Cisco Nexus 5010 Switches that support Fiber Channel over Ethernet Cisco Nexus 7010 Switches to connect to the IP network and Cisco MDS 9509 Multilayer Director to connect to the SAN ...
Access your control systems via the Internet
... systems including Windows, Macintosh and Linux - which means you don’t have to install or pay for any extra software. An example of the PremiseGateway™ Configuration Tools ...
... systems including Windows, Macintosh and Linux - which means you don’t have to install or pay for any extra software. An example of the PremiseGateway™ Configuration Tools ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.