Dave`s AusNOG 02 talk - Locator/ID Separation Protocol
... • Use 32-bit EIDs for IPv4 from registry allocation • Use 128-bit EIDs for IPv6 from registry allocation • Use topological addresses for Locators from ISP address block allocations • Two types of Tunnel Routers – Ingress Tunnel Router (ITR) – Encaps packets at the sender – Egress Tunnel Router (ETR) ...
... • Use 32-bit EIDs for IPv4 from registry allocation • Use 128-bit EIDs for IPv6 from registry allocation • Use topological addresses for Locators from ISP address block allocations • Two types of Tunnel Routers – Ingress Tunnel Router (ITR) – Encaps packets at the sender – Egress Tunnel Router (ETR) ...
ug_niosedk.pdf
... A network-interface daughter card that can plug directly into the Nios development board. An SOPC Builder library component that defines the logic and interface signals necessary to use the daughter card in a Nios system. A C language library that provides a network-protocol stack. This library incl ...
... A network-interface daughter card that can plug directly into the Nios development board. An SOPC Builder library component that defines the logic and interface signals necessary to use the daughter card in a Nios system. A C language library that provides a network-protocol stack. This library incl ...
Corporate Presentation Template
... Edge connections to core works with Multi-Chassis Trunking (MCT) for module, link, and chassis LAG redundancy ...
... Edge connections to core works with Multi-Chassis Trunking (MCT) for module, link, and chassis LAG redundancy ...
TCP/IP Illustrated - UTN
... (Numerous fine points are missing from this figure that will be discussed in the appropriate chapter. For example, both the DNS and RPC use TCP, which we don't show.) We take a bottom-up approach to the TCP/IP protocol suite. After providing a basic introduction to TCP/IP in Chapter 1, we will start ...
... (Numerous fine points are missing from this figure that will be discussed in the appropriate chapter. For example, both the DNS and RPC use TCP, which we don't show.) We take a bottom-up approach to the TCP/IP protocol suite. After providing a basic introduction to TCP/IP in Chapter 1, we will start ...
Segment Routing and Path Computation Element
... required to instruct ingress routers which paths to use through the network, and for which services. This intelligence is delivered by an external traffic engineering controller, which, among other things, functions as a stateful active Path Computation Element (PCE), providing end-to-end control of ...
... required to instruct ingress routers which paths to use through the network, and for which services. This intelligence is delivered by an external traffic engineering controller, which, among other things, functions as a stateful active Path Computation Element (PCE), providing end-to-end control of ...
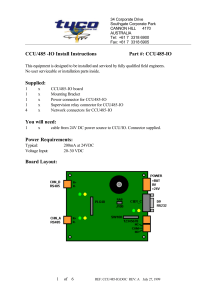
485-CCU HUB - Tyco Safety Products ANZ
... If you want to configure the address in software you can use any address from 1 to 65534 (except 255) (The CCU Network does not support more than 65534 nodes). You will need to use a laptop to program the network address. Software configuration requires that a laptop be connected to port CHN-C using ...
... If you want to configure the address in software you can use any address from 1 to 65534 (except 255) (The CCU Network does not support more than 65534 nodes). You will need to use a laptop to program the network address. Software configuration requires that a laptop be connected to port CHN-C using ...
1 Goals of the meeting
... FG IPTV-ID-31: It proposes architectural and functional requirements for IMS-based IPTV service including service control functions, which is in relationship with the IMS-based NGN requirements, new requirements including navigation, content distribution, content locating, etc. It is generally agree ...
... FG IPTV-ID-31: It proposes architectural and functional requirements for IMS-based IPTV service including service control functions, which is in relationship with the IMS-based NGN requirements, new requirements including navigation, content distribution, content locating, etc. It is generally agree ...
Leonard Kleinrock`s Keynote speech at
... UCLA puts out Press Release 8/29 BBN sends first switch (IMP) to UCLA ...
... UCLA puts out Press Release 8/29 BBN sends first switch (IMP) to UCLA ...
PDF - Complete Book (2.38 MB)
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
here - BITS Embryo
... – Initiator executes “SendTargets” command after establishing the session • This is the only command supported for a Discovery session ...
... – Initiator executes “SendTargets” command after establishing the session • This is the only command supported for a Discovery session ...
MSS485 Installation Guide
... Support includes Telnet, Rlogin, UDP, and DNS. The Telnet terminal protocol, supported on most UNIX systems, is an easyto-use interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagr ...
... Support includes Telnet, Rlogin, UDP, and DNS. The Telnet terminal protocol, supported on most UNIX systems, is an easyto-use interface that creates terminal connections to any network host supporting Telnet. Rlogin is a protocol that allows users to initiate a TCP/IP login session. UDP (User Datagr ...
Planning Guide version 6.0
... requirements than an environment that is mostly used for extensive calculations. • One Fuel Master node can manage multiple environments. If you need to support applications with very different hardware needs, consider deploying separate environments that are targeted to these needs; for example, de ...
... requirements than an environment that is mostly used for extensive calculations. • One Fuel Master node can manage multiple environments. If you need to support applications with very different hardware needs, consider deploying separate environments that are targeted to these needs; for example, de ...
Wireless Application Development Issues
... Next we describe the paging infrastructure in some detail. Many application developers are prone to believe that the infrastructure is simply a wireless pipe or connection between people and machines. The infrastructure has characteristics that must be understood in order to write successful applica ...
... Next we describe the paging infrastructure in some detail. Many application developers are prone to believe that the infrastructure is simply a wireless pipe or connection between people and machines. The infrastructure has characteristics that must be understood in order to write successful applica ...
Perfect Storm – Wireless/VoIP Payam Maveddat AVP of
... These presentation materials describe Tekelec's present plans to develop and make available to its customers certain products, features and functionality. Tekelec is only obligated to provide those deliverables specifically included in a written agreement signed by Tekelec and customer. ...
... These presentation materials describe Tekelec's present plans to develop and make available to its customers certain products, features and functionality. Tekelec is only obligated to provide those deliverables specifically included in a written agreement signed by Tekelec and customer. ...
Comtech CDM 570/570L Vipersat
... Manual Revision 0 Firmware Version 1.5.x ©2008 by Comtech EF Data, Inc. All rights reserved. No part of this manual may be copied or reproduced without prior written permission of Comtech EF Data, Inc. Comtech reserves the right to revise this publication at any time without obligation to provide no ...
... Manual Revision 0 Firmware Version 1.5.x ©2008 by Comtech EF Data, Inc. All rights reserved. No part of this manual may be copied or reproduced without prior written permission of Comtech EF Data, Inc. Comtech reserves the right to revise this publication at any time without obligation to provide no ...
Study on a Fast OSPF Route Reconstruction Method Under Network
... reconstruct robust networks against disasters. Networks require high reliability and fast recovery. One of the important problems for these requirements is that of routing, since considerable time is required to reroute paths on IP networks, when multiple routers have ceased operation due to failure ...
... reconstruct robust networks against disasters. Networks require high reliability and fast recovery. One of the important problems for these requirements is that of routing, since considerable time is required to reroute paths on IP networks, when multiple routers have ceased operation due to failure ...
Network Security
... “Because of user input going directly into a format string for a *printf function, it is possible to overwrite important data, such as a return address, on the stack. When this is accomplished, the function can jump into shell code pointed to by the overwritten eip and execute arbitrary commands as ...
... “Because of user input going directly into a format string for a *printf function, it is possible to overwrite important data, such as a return address, on the stack. When this is accomplished, the function can jump into shell code pointed to by the overwritten eip and execute arbitrary commands as ...
Implementation of IS-IS Routing Protocol for IP versions 4 and 6
... originally intended to be used with Connectionless Network Protocol (CLNP). Internet Engineering Task Force (IETF) also wanted a link-state routing protocol for their Internet Protocol (IPv4) and began to develop the Open Shortest Path First (OSPF) protocol. At the same time IS-IS was extended to su ...
... originally intended to be used with Connectionless Network Protocol (CLNP). Internet Engineering Task Force (IETF) also wanted a link-state routing protocol for their Internet Protocol (IPv4) and began to develop the Open Shortest Path First (OSPF) protocol. At the same time IS-IS was extended to su ...
TR-0024-3GPP_Rel13_IWK-V2_0_1 - FTP
... © 2016, oneM2M Partners Type 1 (ARIB, ATIS, CCSA, ETSI, TIA, TSDSI, TTA, TTC). ...
... © 2016, oneM2M Partners Type 1 (ARIB, ATIS, CCSA, ETSI, TIA, TSDSI, TTA, TTC). ...
Sams Teach Yourself Networking in 24 Hours
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.