NION CobraNet Hardware Manual Version 1.7.1.0 July 23, 2014
... commercial audio and communications applications. The product features an internal processing core supported by a wide range of features, including a scalable I/O architecture. A range of plug-in cards is available that allow audio input and output, plus advanced features like echo cancellation. Aud ...
... commercial audio and communications applications. The product features an internal processing core supported by a wide range of features, including a scalable I/O architecture. A range of plug-in cards is available that allow audio input and output, plus advanced features like echo cancellation. Aud ...
Ingate Firewall & SIParator Training
... 10 Years in SIP Protocol Audience – Show of Hands How many of you are familiar with the SIP Protocol? How many of you own an Ingate? Are you planning to buy an Ingate in the near future? Are you concerned about SIP Interop? Are you concerned about SIP Security? ...
... 10 Years in SIP Protocol Audience – Show of Hands How many of you are familiar with the SIP Protocol? How many of you own an Ingate? Are you planning to buy an Ingate in the near future? Are you concerned about SIP Interop? Are you concerned about SIP Security? ...
Lawrence E. Hughes - The Second Internet
... Unit 801, Skyrise Bldg #3, AsiaTown IT Park, Lahug, Cebu City, Cebu 6000 PHILIPPINES Copyright © 2010, Lawrence E. Hughes. All Rights Reserved Worldwide. This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/ In short, th ...
... Unit 801, Skyrise Bldg #3, AsiaTown IT Park, Lahug, Cebu City, Cebu 6000 PHILIPPINES Copyright © 2010, Lawrence E. Hughes. All Rights Reserved Worldwide. This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/ In short, th ...
NAT Virtual Interface - Cisco Support Community
... NAT Virtual Interface Feature Design The NAT Virtual Interface feature allows all NAT traffic flows on the virtual interface, eliminating the need to specify inside and outside domains. When a domain is specified, the translation rules are applied either before or after route decisions depending on ...
... NAT Virtual Interface Feature Design The NAT Virtual Interface feature allows all NAT traffic flows on the virtual interface, eliminating the need to specify inside and outside domains. When a domain is specified, the translation rules are applied either before or after route decisions depending on ...
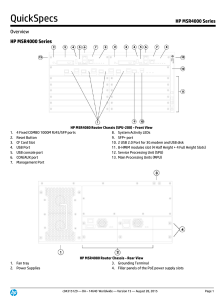
HP MSR4000 Series
... Virtual Private LAN Service (VPLS) delivers a point-to-multipoint L2VPN service over an MPLS or IP backbone. The backbone is transparent to the customer sites, which can communicate with each other as if they were on the same LAN. The following protocols support on MSRs, RFC4447, RFC4761 and RFC4762 ...
... Virtual Private LAN Service (VPLS) delivers a point-to-multipoint L2VPN service over an MPLS or IP backbone. The backbone is transparent to the customer sites, which can communicate with each other as if they were on the same LAN. The following protocols support on MSRs, RFC4447, RFC4761 and RFC4762 ...
Serial Server Installation Guide
... TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in smaller packet headers, no session overhead, and the ability to send to multiple hosts. The MSS also supports the use of Domain Name Servers (DNS), allowing a network nameserver to translate text node nam ...
... TCP/IP login session. UDP (User Datagram Protocol) is a connectionless protocol that results in smaller packet headers, no session overhead, and the ability to send to multiple hosts. The MSS also supports the use of Domain Name Servers (DNS), allowing a network nameserver to translate text node nam ...
TL-WR642G 108M Wireless Router - TP-Link
... It adopts 2x to 3x eXtended Range™ WLAN transmission technology so that transmission distance is 2-3 times of traditional IEEE 802.11g and IEEE 802.11b solutions, up to 855.36m tested in China. The transmission range is extended to 4-9 times. It is compatible with all IEEE 802.11g and IEEE 802.11b p ...
... It adopts 2x to 3x eXtended Range™ WLAN transmission technology so that transmission distance is 2-3 times of traditional IEEE 802.11g and IEEE 802.11b solutions, up to 855.36m tested in China. The transmission range is extended to 4-9 times. It is compatible with all IEEE 802.11g and IEEE 802.11b p ...
IPv6 Hosts - Surfnet IPv6
... – Intranet service. IPv4 tunneled in IPv6. DNS, DHCPv6 servers could be provided by the SP. Needs dual stack on host, however. www.interweave-consulting.com ...
... – Intranet service. IPv4 tunneled in IPv6. DNS, DHCPv6 servers could be provided by the SP. Needs dual stack on host, however. www.interweave-consulting.com ...
Introducing TCP/IP
... renewal process to determine if it can keep the address past the lease time • If the client cannot renew the address from that DHCP server within the stipulated lease period, that client must begin the more desperate process of renewing the address from another DHCP server • This is called the rebin ...
... renewal process to determine if it can keep the address past the lease time • If the client cannot renew the address from that DHCP server within the stipulated lease period, that client must begin the more desperate process of renewing the address from another DHCP server • This is called the rebin ...
Ayodele Damola
... Thanks to my industrial supervisor at Ericsson Mr. Hans Mickelsson first for selecting me for this thesis project and for his continuous help and support along the whole way. Thank you Hans. Thanks to Mr. Jan Söderström for the opportunity to do my project at Ericsson Research. Thanks to Mr. Torbjör ...
... Thanks to my industrial supervisor at Ericsson Mr. Hans Mickelsson first for selecting me for this thesis project and for his continuous help and support along the whole way. Thank you Hans. Thanks to Mr. Jan Söderström for the opportunity to do my project at Ericsson Research. Thanks to Mr. Torbjör ...
david-meyer-lisp-network-grow-ietf72-2008
... – Currently deployed LISP network elements are 1RU PCs (“titanium”) running a LISP-capable version of NXOS – There are both an IOS and Open Source ...
... – Currently deployed LISP network elements are 1RU PCs (“titanium”) running a LISP-capable version of NXOS – There are both an IOS and Open Source ...
VoIP
... audio VOIP PDU’s divided into smaller units, e.g. four 5 msec units per 20 msec audio VOIP PDU PDU contains small units from different VOIP PDU’s if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
... audio VOIP PDU’s divided into smaller units, e.g. four 5 msec units per 20 msec audio VOIP PDU PDU contains small units from different VOIP PDU’s if PDU lost, still have most of every original VOIP PDU no redundancy overhead, but increases playout delay ...
PDF
... 10/100-Mbps ports for desktop, wireless access point, printer, and IP phone connectivity, as well as available 10/100/1000BASE-T Gigabit Ethernet and SFP optical connectivity options. All switches in the Cisco Catalyst Express 520 Series also feature head-of-line blocking prevention to help ensure t ...
... 10/100-Mbps ports for desktop, wireless access point, printer, and IP phone connectivity, as well as available 10/100/1000BASE-T Gigabit Ethernet and SFP optical connectivity options. All switches in the Cisco Catalyst Express 520 Series also feature head-of-line blocking prevention to help ensure t ...
Architectures and Algorithms for IPv4/IPv6
... to the core nodes including the burst assembly, switching and routing tasks. We present several new solutions to problems of the OBS networks, namely, a new burst assembly machine concept named Internet Protocol Packet Aggregator and Converter (IP-PAC), with a new burst assembly algorithm, dynamic a ...
... to the core nodes including the burst assembly, switching and routing tasks. We present several new solutions to problems of the OBS networks, namely, a new burst assembly machine concept named Internet Protocol Packet Aggregator and Converter (IP-PAC), with a new burst assembly algorithm, dynamic a ...
Basic Router Configuration
... The TTY lines are asynchronous lines used for inbound or outbound modem and terminal connections and can be seen in a router or access server configuration as line x. The specific line numbers are a function of the hardware built into or installed on the router or access server. In Cisco ISR G2 seri ...
... The TTY lines are asynchronous lines used for inbound or outbound modem and terminal connections and can be seen in a router or access server configuration as line x. The specific line numbers are a function of the hardware built into or installed on the router or access server. In Cisco ISR G2 seri ...
Multicast Over Wireless Networks
... Multicast routing using mesh: Use multiple redundant routes for rubost handling of link failure and node mobility during a multicast session. It may have looping problem. Multicast routing using other structures: Multicast routing provides stateless topologyindependent routing. Forwardin ...
... Multicast routing using mesh: Use multiple redundant routes for rubost handling of link failure and node mobility during a multicast session. It may have looping problem. Multicast routing using other structures: Multicast routing provides stateless topologyindependent routing. Forwardin ...
Exploring and Improving BitTorrent Swarm Topologies
... • Blocking peers: a peer might decide to block us while we scan either as a result of our behavior or the fact that we use University owned IP addresses. One such example is the Azureus SafePeer plugin which loads the PeerGuardian blocklists. • Torrent removed: as soon as a torrent has been removed ...
... • Blocking peers: a peer might decide to block us while we scan either as a result of our behavior or the fact that we use University owned IP addresses. One such example is the Azureus SafePeer plugin which loads the PeerGuardian blocklists. • Torrent removed: as soon as a torrent has been removed ...
IPv6 Advantages March 2000
... Rules for constructing the NEXTHOP attribute: When two peers share a common subnet the NEXTHOP information is formed by a global address and a link local address. Redirects in IPv6 are restricted to the usage of link local addresses. Redistribution from and to protocols that use link ...
... Rules for constructing the NEXTHOP attribute: When two peers share a common subnet the NEXTHOP information is formed by a global address and a link local address. Redirects in IPv6 are restricted to the usage of link local addresses. Redistribution from and to protocols that use link ...
ns-3 tutorial
... Two key abstractions are maintained: 1) applications use an (asynchronous, for now) sockets API 2) the boundary between IP and layer 2 mimics the boundary at the deviceindependent sublayer in Linux i.e., Linux Packet Sockets ...
... Two key abstractions are maintained: 1) applications use an (asynchronous, for now) sockets API 2) the boundary between IP and layer 2 mimics the boundary at the deviceindependent sublayer in Linux i.e., Linux Packet Sockets ...
Random Early Detection Gateways for Congestion Avoidance
... drop probability. This is discussed as a rough initial implementation. Hashem [11] stresses that in future imple- Early descriptions of IP Source Quench messages sugmentations the drop level and the drop probability should gest that gateways could send Source Quench messages be adjusted dynamically, ...
... drop probability. This is discussed as a rough initial implementation. Hashem [11] stresses that in future imple- Early descriptions of IP Source Quench messages sugmentations the drop level and the drop probability should gest that gateways could send Source Quench messages be adjusted dynamically, ...
TCPware for OpenVMS Network Control Utility
... following disclaimer in the documentation and/or other materials provided with the distribution. 3. All advertising materials mentioning features or use of this software must display the following acknowledgement: This product includes software developed by Niels Provos. 4. The name of the author ma ...
... following disclaimer in the documentation and/or other materials provided with the distribution. 3. All advertising materials mentioning features or use of this software must display the following acknowledgement: This product includes software developed by Niels Provos. 4. The name of the author ma ...
DNSCatProxy: A Pluggable Transport based on DNS Tunneling Irvin Zhan Abstract
... UDP-based, such throttling will not affect its usability. We thus propose a pluggable transport designed to work using a DNS channel through DNS queries and replies. Using a technique known as DNS tunneling, these individuals will likely be able to bypass the proxy. If that individual too is in an a ...
... UDP-based, such throttling will not affect its usability. We thus propose a pluggable transport designed to work using a DNS channel through DNS queries and replies. Using a technique known as DNS tunneling, these individuals will likely be able to bypass the proxy. If that individual too is in an a ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.