Compatible Systems Reference Guides
... which was shipped with their router for configuration and management information. Each device is shipped with an Installation Guide which includes installation instructions and offers basic configuration parameters which will be appropriate for many network applications. For the latest documentation ...
... which was shipped with their router for configuration and management information. Each device is shipped with an Installation Guide which includes installation instructions and offers basic configuration parameters which will be appropriate for many network applications. For the latest documentation ...
PDF
... a service that combines IP multicast with a low-latency service class enables video conferencing within ...
... a service that combines IP multicast with a low-latency service class enables video conferencing within ...
Ip Addressing and Subnetting Workbook
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
Distributed Objects - Pages supplied by users
... Jini Event Model • Jini objects may also be interested in changes in other Jini objects i.e. want to be listeners for such changes. • Networked nature of Jini means need a different event model: – Network delivery is unreliable – Network delivery is time-dependent – A remote listener may have ...
... Jini Event Model • Jini objects may also be interested in changes in other Jini objects i.e. want to be listeners for such changes. • Networked nature of Jini means need a different event model: – Network delivery is unreliable – Network delivery is time-dependent – A remote listener may have ...
TL1 History - ManageEngine
... 1.2 TL1 and OSMINE One of the challenges NE vendors who target the RBOCs face is obtaining the OSMINE3 certification. This is a process to ensure that their equipment can reliably interwork with Telcordia4 OSSs in the targeted service provider network(s). OSMINE is a service offered by Telcordia and ...
... 1.2 TL1 and OSMINE One of the challenges NE vendors who target the RBOCs face is obtaining the OSMINE3 certification. This is a process to ensure that their equipment can reliably interwork with Telcordia4 OSSs in the targeted service provider network(s). OSMINE is a service offered by Telcordia and ...
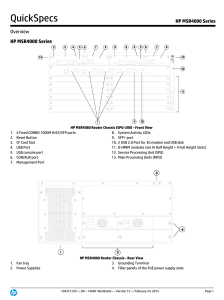
HP MSR4000 Series
... The HP MSR4000 Router Series, the next generation of router from HP, is a component of the HP FlexBranch solution, which is a part of the comprehensive HP FlexNetwork architecture. These routers feature a modular design that delivers unmatched application services for extra-large branch offices, hea ...
... The HP MSR4000 Router Series, the next generation of router from HP, is a component of the HP FlexBranch solution, which is a part of the comprehensive HP FlexNetwork architecture. These routers feature a modular design that delivers unmatched application services for extra-large branch offices, hea ...
Chapter 1 - Introduction
... – describes the format of packets that are sent across the Internet – discusses the key concepts of datagram encapsulation, forwarding, and fragmentation and reassembly ...
... – describes the format of packets that are sent across the Internet – discusses the key concepts of datagram encapsulation, forwarding, and fragmentation and reassembly ...
Advanced CCIE Routing & Switching
... tunnel source FastEthernet0/0 tunnel mode gre multipoint end Actually we can see two problems in the above configuration, the first problem is that the configuration does not provide support for Multicast traffic. The second problem is that the wrong IPv6 address is mapped to the NBMA-IP. In IPv6, t ...
... tunnel source FastEthernet0/0 tunnel mode gre multipoint end Actually we can see two problems in the above configuration, the first problem is that the configuration does not provide support for Multicast traffic. The second problem is that the wrong IPv6 address is mapped to the NBMA-IP. In IPv6, t ...
NFV - Oasis
... and distributed, in whole or in part, without restriction of any kind, provided that the above copyright notice and this section are included on all such copies and derivative works. However, this document itself may not be modified in any way, including by removing the copyright notice or reference ...
... and distributed, in whole or in part, without restriction of any kind, provided that the above copyright notice and this section are included on all such copies and derivative works. However, this document itself may not be modified in any way, including by removing the copyright notice or reference ...
Nortel Networks L2/3 Ethernet Switch Module for
... improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time without notice. Any references in this information to non-IBM Web sites are provided for convenience only and do not in any manner serve as an endorsement of those Web sites. The materials a ...
... improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time without notice. Any references in this information to non-IBM Web sites are provided for convenience only and do not in any manner serve as an endorsement of those Web sites. The materials a ...
Signaling Solution Description
... Software and Hardware Redundancy - Redundancy can be provided by using at least two hardware servers Unmatched In-Service-Performance (ISP) - With HD it is possible to add or remove servers dynamically without bringing the whole system down Customer applications may be co-located on the same server ...
... Software and Hardware Redundancy - Redundancy can be provided by using at least two hardware servers Unmatched In-Service-Performance (ISP) - With HD it is possible to add or remove servers dynamically without bringing the whole system down Customer applications may be co-located on the same server ...
- Webcollage.net
... Dynamic Security for the Global Network Our vision is simple: we believe security solutions should be “smart” enough to adapt as organizations evolve and as threats evolve—dynamically and globally. We believe customers around the world should have the ability to control, manage and protect their glo ...
... Dynamic Security for the Global Network Our vision is simple: we believe security solutions should be “smart” enough to adapt as organizations evolve and as threats evolve—dynamically and globally. We believe customers around the world should have the ability to control, manage and protect their glo ...
(Backup) MDR
... there exists a bidirectional neighbor that does not satisfy condition (a) or (b). If a Backup MDR receives a new LSA, it waits BackupWaitInterval seconds, and then floods the LSA back out the receiving interface if there exists a bidirectional neighbor that does not satisfy condition (a) or (b). An ...
... there exists a bidirectional neighbor that does not satisfy condition (a) or (b). If a Backup MDR receives a new LSA, it waits BackupWaitInterval seconds, and then floods the LSA back out the receiving interface if there exists a bidirectional neighbor that does not satisfy condition (a) or (b). An ...
12.4 was released in May of 2005
... data, voice, and video access to small remote office and teleworkers that need secure Internet and corporate network connectivity • Provide a wide range of integrated security & advanced QoS features for high-quality applications • Offer easy deployment and remote management features with Cisco IOS ...
... data, voice, and video access to small remote office and teleworkers that need secure Internet and corporate network connectivity • Provide a wide range of integrated security & advanced QoS features for high-quality applications • Offer easy deployment and remote management features with Cisco IOS ...
IPv6 and the Security of Your Network and Systems
... you’re currently supporting, they may search for and find “ad hoc” approaches which they can try without “having to bother you.” • Sometimes there’s a hope that obscurity or technical difficulty will keep users from trying some work-arounds, but I wouldn’t count on “security through obscurity” in th ...
... you’re currently supporting, they may search for and find “ad hoc” approaches which they can try without “having to bother you.” • Sometimes there’s a hope that obscurity or technical difficulty will keep users from trying some work-arounds, but I wouldn’t count on “security through obscurity” in th ...
20088-2 CCNA3 3.1-02 Questions OSPF
... The link-state database is stored in a designated router and is accessed by each router in the area as needed. ...
... The link-state database is stored in a designated router and is accessed by each router in the area as needed. ...
Chapter 8: Virtual LAN (VLAN)
... Routers in VLAN topologies provide broadcast filtering, security, and traffic flow management. Switches may not bridge any traffic between VLANs, as this would violate the integrity of the VLAN broadcast domain. Traffic should only be routed between VLANs. ...
... Routers in VLAN topologies provide broadcast filtering, security, and traffic flow management. Switches may not bridge any traffic between VLANs, as this would violate the integrity of the VLAN broadcast domain. Traffic should only be routed between VLANs. ...
EIGRP - Information Systems Technology
... ID number (autonomous-system number) Most likely reason PCs can’t talk across routers is that these numbers are NOT identical. ...
... ID number (autonomous-system number) Most likely reason PCs can’t talk across routers is that these numbers are NOT identical. ...
Cisco Application Control Engine and Cisco Nexus 7000 Series Integration White Paper
... significantly due to lower utilization, while costs increased due to higher management and capital expenditures. The Cisco multitenant architecture addresses these concerns through a secure, isolated multitenant solution at every network layer. In addition to multitenant architecture adoption, today ...
... significantly due to lower utilization, while costs increased due to higher management and capital expenditures. The Cisco multitenant architecture addresses these concerns through a secure, isolated multitenant solution at every network layer. In addition to multitenant architecture adoption, today ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.