Reference Manual for the MR814v2 Cable/DSL Wireless Router
... Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwarding Entry ............................ ...
... Configuring for Port Forwarding to Local Servers ..........................................................6-1 Adding a Custom Service .........................................................................................6-2 Editing or Deleting a Port Forwarding Entry ............................ ...
Lab – Configuring IPv6 Static and Default Routes
... class. This table includes identifiers for the possible combinations of Ethernet and Serial interfaces in the device. The table does not include any other type of interface, even though a specific router may contain one. An example of this might be an ISDN BRI interface. The string in parenthesis is ...
... class. This table includes identifiers for the possible combinations of Ethernet and Serial interfaces in the device. The table does not include any other type of interface, even though a specific router may contain one. An example of this might be an ISDN BRI interface. The string in parenthesis is ...
WR - Computer Science and Engineering
... • Distributed RAN architecture saves backhaul cost (less than half of the cost of existing architecture ) • Distributed RAN architecture supports 99.999% service-level availability compared to conventional network. In fact, full mesh is not required for realizing the 99.999% availability. Even parti ...
... • Distributed RAN architecture saves backhaul cost (less than half of the cost of existing architecture ) • Distributed RAN architecture supports 99.999% service-level availability compared to conventional network. In fact, full mesh is not required for realizing the 99.999% availability. Even parti ...
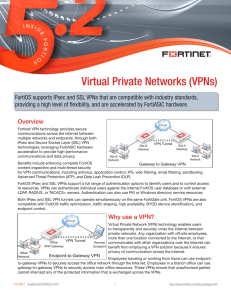
Virtual Private Networks (VPNs)
... VPN is the only workaround in this situation, since the HTTPS protocol used for SSL VPN is a standard Internet protocol required for many applications and is almost never blocked. SSL VPN is the best solution for endpoint-to-gateway VPNs. Remote users can securely log into the SSL VPN web portal fro ...
... VPN is the only workaround in this situation, since the HTTPS protocol used for SSL VPN is a standard Internet protocol required for many applications and is almost never blocked. SSL VPN is the best solution for endpoint-to-gateway VPNs. Remote users can securely log into the SSL VPN web portal fro ...
Kyocera KR1 Mobile Router
... Thank you for choosing the Mobile Router for 3.5G/WiMAX Broadband. The Mobile Router is a universal communication device for professional permanent use in the office, at home or as a mobile hotspot – wherever no fast DSL or Cable connection is available. The Mobile Router supports uses a 32-bit PC C ...
... Thank you for choosing the Mobile Router for 3.5G/WiMAX Broadband. The Mobile Router is a universal communication device for professional permanent use in the office, at home or as a mobile hotspot – wherever no fast DSL or Cable connection is available. The Mobile Router supports uses a 32-bit PC C ...
Employing a secure Virtual Private Network (VPN)
... Internet medium or across unsecured networks. ...
... Internet medium or across unsecured networks. ...
Cross-Domain and Cross-Layer Coarse Grained Quality of
... load and its rising usage for time and loss critical services, such as voice over IP, video streaming and gaming, consists of about 30,000 interconnected service provider networks. Those interconnections are based on the Internet Protocol (IP) and do not distinguish the mixed traffic types within th ...
... load and its rising usage for time and loss critical services, such as voice over IP, video streaming and gaming, consists of about 30,000 interconnected service provider networks. Those interconnections are based on the Internet Protocol (IP) and do not distinguish the mixed traffic types within th ...
ieee 2014 java .net titles be, b.tech, msc, mca projects institute cost
... Toward Transcoding as a Service in a Multimedia Cloud Energy-Efficient Job- ...
... Toward Transcoding as a Service in a Multimedia Cloud Energy-Efficient Job- ...
SonicWALL PRO 5060 Getting Started Guide
... SonicWALL PRO 5060 correctly. 2. If you cannot view the SonicWALL home page, try a second URL. 3. If you still cannot view a Web page, try one of these solutions: Restart your Management Station Your management station may need to restart to accept new network settings from the DHCP server in the So ...
... SonicWALL PRO 5060 correctly. 2. If you cannot view the SonicWALL home page, try a second URL. 3. If you still cannot view a Web page, try one of these solutions: Restart your Management Station Your management station may need to restart to accept new network settings from the DHCP server in the So ...
Ubee DDW366 Dual-Band Concurrent Advanced
... 1. 2.4G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D2-2.4G 2. 5G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D3-5G If the subscriber changes the SSID, the device does not revert to this default SSID when the device is reset, except when a factory reset is p ...
... 1. 2.4G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D2-2.4G 2. 5G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D3-5G If the subscriber changes the SSID, the device does not revert to this default SSID when the device is reset, except when a factory reset is p ...
publish subscribe - Department of Information Technology
... MOTIVATION • Interworking of SIP event framework with the generic publish/subscribe system ...
... MOTIVATION • Interworking of SIP event framework with the generic publish/subscribe system ...
The Gartner Glossary - SUNY Center for Professional Development
... A3 (Adaptive Application Architecture) A Gartner reference model for an application platform that can adapt to a variety device types and networks (notably mobile devices and wireless data transmission), and that can support all types of data transactions. The A3 goes beyond the limitations of netwo ...
... A3 (Adaptive Application Architecture) A Gartner reference model for an application platform that can adapt to a variety device types and networks (notably mobile devices and wireless data transmission), and that can support all types of data transactions. The A3 goes beyond the limitations of netwo ...
Business Ready Branch Solutions for Enterprise and Small
... These attributes influence the use of specific features and require special considerations when designing a branch office. For example, if a branch office is connected to the Internet, an IPSec VPN may be required for data privacy between branch and home offices or mobile workers. Another example is ...
... These attributes influence the use of specific features and require special considerations when designing a branch office. For example, if a branch office is connected to the Internet, an IPSec VPN may be required for data privacy between branch and home offices or mobile workers. Another example is ...
p2p
... Streaming live bandwidth-intensive media from a single source to a large quantity of receivers on the Internet. Solution: ...
... Streaming live bandwidth-intensive media from a single source to a large quantity of receivers on the Internet. Solution: ...
Reorder Density (RD): A Formal, Comprehensive Metric for Packet Reordering
... i.e., the number of duplicate ACKs to be allowed before classifying a following nonacknowledged packet as lost [19]. In delay sensitive applications based on UDP, e.g., IP telephony, an out-of-order packet that arrives after the elapse of playback time is treated as lost thereby decreasing the perce ...
... i.e., the number of duplicate ACKs to be allowed before classifying a following nonacknowledged packet as lost [19]. In delay sensitive applications based on UDP, e.g., IP telephony, an out-of-order packet that arrives after the elapse of playback time is treated as lost thereby decreasing the perce ...
Document
... synaptic weights of the network should be updated only if the absolute error on the training sample currently being processed by the network is greater than some prescribed criterion; ...
... synaptic weights of the network should be updated only if the absolute error on the training sample currently being processed by the network is greater than some prescribed criterion; ...
IPv6 Addressing
... conservation efforts PPP/DHCP address sharing NAT (network address translation) CIDR (classless interdomain routing) plus some address reclamation IPv6 and Semantic Interoperability ...
... conservation efforts PPP/DHCP address sharing NAT (network address translation) CIDR (classless interdomain routing) plus some address reclamation IPv6 and Semantic Interoperability ...
Understanding Simple Network Management Protocol
... Simple Network Management Protocol (SNMP), an application layer protocol, facilitates the exchange of management information among network devices, such as nodes, routers, and so on. As part of the TCP/IP protocol suite, SNMP enables administrators to remotely manage network performance, find and so ...
... Simple Network Management Protocol (SNMP), an application layer protocol, facilitates the exchange of management information among network devices, such as nodes, routers, and so on. As part of the TCP/IP protocol suite, SNMP enables administrators to remotely manage network performance, find and so ...
Campus Network Design
... Why do we need an EGP? • Scaling to large network Hierarchy Limit scope of failure Fast convergence No manual reconfig (static routes) - high maintenance ...
... Why do we need an EGP? • Scaling to large network Hierarchy Limit scope of failure Fast convergence No manual reconfig (static routes) - high maintenance ...
What is Sockets
... transmit a message to another socket. send() can be used only when the socket is in a connected state. return: the number of bytes that has been delivered or -1. sd: socket descriptor (from the socket() system call) buf: the message you send. buf_len: the data length of buf ...
... transmit a message to another socket. send() can be used only when the socket is in a connected state. return: the number of bytes that has been delivered or -1. sd: socket descriptor (from the socket() system call) buf: the message you send. buf_len: the data length of buf ...
ch4
... • The probability that there is no other traffic during a time slot is e-G, where G is the number of packet attempts per unit time. • Slotted ALOHA peaks at G= 1, with a throughput of S= 1/e or about 37%, which is twice that of pure ALOHA. • Optimal is 37% empty slots, 37% successful transmissions a ...
... • The probability that there is no other traffic during a time slot is e-G, where G is the number of packet attempts per unit time. • Slotted ALOHA peaks at G= 1, with a throughput of S= 1/e or about 37%, which is twice that of pure ALOHA. • Optimal is 37% empty slots, 37% successful transmissions a ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.