Security Fundamentals
... • Goal is to separate network traffic so that no network segment carries traffic not required on the segment • Performance will also be more efficient • Security zones: – Areas of the network that contain resources with similar security requirements – Group computers and devices according to securit ...
... • Goal is to separate network traffic so that no network segment carries traffic not required on the segment • Performance will also be more efficient • Security zones: – Areas of the network that contain resources with similar security requirements – Group computers and devices according to securit ...
TNS03%20Introduction%20to%20Network%20Security
... Worms are programs that replicate themselves from system to system without the use of a host file. This is in contrast to viruses, which requires the spreading of an infected host file. Use e-mail and network facilities to spread to other resources. ...
... Worms are programs that replicate themselves from system to system without the use of a host file. This is in contrast to viruses, which requires the spreading of an infected host file. Use e-mail and network facilities to spread to other resources. ...
Computer Network
... A computer network or data network is a telecommunications network that allows computers to exchange data. In computer networks, networked computing devices pass data to each other along data connections. The connections (network links) between nodes are established using either cable media or wirel ...
... A computer network or data network is a telecommunications network that allows computers to exchange data. In computer networks, networked computing devices pass data to each other along data connections. The connections (network links) between nodes are established using either cable media or wirel ...
A Survey of Energy efficient Network Protocols for Wireless Networks
... – Use flash memory and disk spin down. By using flash memory to cache files in memory instead of hard drive, the hard drive can be stopped from spinning. Power can be saved up to 30%. One of the complexities is asynchronously updating the hard drive blocks with t he flash memory. ...
... – Use flash memory and disk spin down. By using flash memory to cache files in memory instead of hard drive, the hard drive can be stopped from spinning. Power can be saved up to 30%. One of the complexities is asynchronously updating the hard drive blocks with t he flash memory. ...
AccessControlSimulation
... IRS has implemented an access authorization control for a system used to process electronic tax payment information; however, users had the capability to circumvent this control and gain access to this system’s server. ...
... IRS has implemented an access authorization control for a system used to process electronic tax payment information; however, users had the capability to circumvent this control and gain access to this system’s server. ...
download
... collaboration among universities and scientists. They trusted each other. No security was built into the internet. • Problem: the internet is open-access and is used by some people who are not trustworthy, who take advantage of the lack of built-in safeguards. • Problem: Most people connect to the i ...
... collaboration among universities and scientists. They trusted each other. No security was built into the internet. • Problem: the internet is open-access and is used by some people who are not trustworthy, who take advantage of the lack of built-in safeguards. • Problem: Most people connect to the i ...
Internet and World Wide Web: Amazing Developments
... join discussion groups- Discuss virtually any topic online participate in games and simulations obtain free software (downloads) ...
... join discussion groups- Discuss virtually any topic online participate in games and simulations obtain free software (downloads) ...
Acronym
... versatility across a variety of computer platforms. According to NIST, Rijndael was selected because it had the best combination of security, performance, efficiency, implementability and flexibility. A technical analysis of the AES candidates is posted on NIST's Web site. http://csrc.nist.gov/encry ...
... versatility across a variety of computer platforms. According to NIST, Rijndael was selected because it had the best combination of security, performance, efficiency, implementability and flexibility. A technical analysis of the AES candidates is posted on NIST's Web site. http://csrc.nist.gov/encry ...
Slide 1
... access to a portal on the Internet (or whatever the entity) by the most appropriate means. The user will not have to know which network provides the service. The smart device can analyze its environment and choose the best available service provider and technology (service discovery). Contd…. ...
... access to a portal on the Internet (or whatever the entity) by the most appropriate means. The user will not have to know which network provides the service. The smart device can analyze its environment and choose the best available service provider and technology (service discovery). Contd…. ...
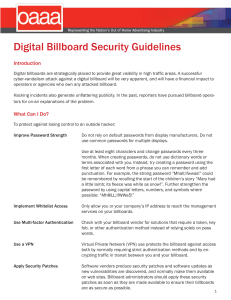
Digital Billboard Security Guidelines
... Intrusion Detection System (IDS): An IDS will monitor computer network communications to identify potentially malicious traffic. The actions taken by an IDS could be to simply alert security personnel to the communications or to block the communications to protect the billboard. Multi-factor Authent ...
... Intrusion Detection System (IDS): An IDS will monitor computer network communications to identify potentially malicious traffic. The actions taken by an IDS could be to simply alert security personnel to the communications or to block the communications to protect the billboard. Multi-factor Authent ...
Lecture 8 Term 2
... PDAs, wireless keyboards and mice, PCs, and printers, to interact wirelessly with each other within a small 30-foot (10meter) area. In addition to the links shown, Bluetooth can be used to network similar devices to send data from one PC to another, for example. ...
... PDAs, wireless keyboards and mice, PCs, and printers, to interact wirelessly with each other within a small 30-foot (10meter) area. In addition to the links shown, Bluetooth can be used to network similar devices to send data from one PC to another, for example. ...
security
... • An information packet sent from a server to a browser and thereafter sent back by the browser each time it access the server • Creation of a user profile to improve user experience of the web or invasion of privacy? • Can be blocked (Browser settings) ...
... • An information packet sent from a server to a browser and thereafter sent back by the browser each time it access the server • Creation of a user profile to improve user experience of the web or invasion of privacy? • Can be blocked (Browser settings) ...
08_chapter 1
... Computer network consists of two or more autonomous computers that are linked together in order to share the resources and allow electronic communication to increase the productivity. There are two broad categories of computer networks, namely, wired networks and wireless networks. In wired networks ...
... Computer network consists of two or more autonomous computers that are linked together in order to share the resources and allow electronic communication to increase the productivity. There are two broad categories of computer networks, namely, wired networks and wireless networks. In wired networks ...
Cross layer design for Wireless networks
... Channel changes as users move around Signal blocked by objects (cars, people, etc.) Broadcast medium – everyone interferes ...
... Channel changes as users move around Signal blocked by objects (cars, people, etc.) Broadcast medium – everyone interferes ...
Risks Associated with Transmission and Hardware
... Physical, Data Link, Network layer security risks Require more technical sophistication Risks inherent in network hardware and design Transmission interception Man-in-the-middle attack Eavesdropping Networks connecting to Internet via leased public lines Sniffing Network hubs broadcasting tr ...
... Physical, Data Link, Network layer security risks Require more technical sophistication Risks inherent in network hardware and design Transmission interception Man-in-the-middle attack Eavesdropping Networks connecting to Internet via leased public lines Sniffing Network hubs broadcasting tr ...
Next Generation National Infocomm Infrastructure
... The carrier-neutral, totally-wired network, or the National Broadband Network (NBN) will have ultra-high access speeds capable of beyond 1 Gbps or more than 500 times the common speed of 2 Mbps today. However, in the initial years of deployment, the access speed may be lower but gradually throttled ...
... The carrier-neutral, totally-wired network, or the National Broadband Network (NBN) will have ultra-high access speeds capable of beyond 1 Gbps or more than 500 times the common speed of 2 Mbps today. However, in the initial years of deployment, the access speed may be lower but gradually throttled ...
Liberty-i Wireless Glossary
... Access Point (AP) A device that transmits and receives data in a wireless local area network (WLAN). Also referred to as “Base Station”, or “Wireless Hub”, it connects users to other users within the wireless network and also can serve as the point of interconnection between the WLAN and a fixed wir ...
... Access Point (AP) A device that transmits and receives data in a wireless local area network (WLAN). Also referred to as “Base Station”, or “Wireless Hub”, it connects users to other users within the wireless network and also can serve as the point of interconnection between the WLAN and a fixed wir ...
Netreg-LTS-Staff-Meeting
... Was great, but technology had advanced quite a bit in 10 years. Determined time for a replacement. ...
... Was great, but technology had advanced quite a bit in 10 years. Determined time for a replacement. ...
Slide 1
... undersea cable systems like Se-Me-Wea-3 and i2i and are having public / private peering relationship with large Tier 1 ISPs and content providers at more than 15 Internet Exchange points across the globe. There also exists peering relationship with other popular domestic ISPs on STM-1 bandwidth leve ...
... undersea cable systems like Se-Me-Wea-3 and i2i and are having public / private peering relationship with large Tier 1 ISPs and content providers at more than 15 Internet Exchange points across the globe. There also exists peering relationship with other popular domestic ISPs on STM-1 bandwidth leve ...
Slide 1
... • Network software on many other devices that you are not aware of • DNS Server • Router • Possibly many others ...
... • Network software on many other devices that you are not aware of • DNS Server • Router • Possibly many others ...
Network Management
... • Confirmed Vulnerability Engine -- Active Uses well-known exploitation techniques to fully confirm each suspected vulnerability and to identify vulnerabilities not detected during passive mapping ...
... • Confirmed Vulnerability Engine -- Active Uses well-known exploitation techniques to fully confirm each suspected vulnerability and to identify vulnerabilities not detected during passive mapping ...
Slide 1
... – they both operate in the same 2.4 GHz ISM band. – They both are capable of creating ad-hoc networks – They both connect electronic devices without any wires ...
... – they both operate in the same 2.4 GHz ISM band. – They both are capable of creating ad-hoc networks – They both connect electronic devices without any wires ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.