* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Datanet Studiu de caz
Wake-on-LAN wikipedia , lookup
TV Everywhere wikipedia , lookup
Computer network wikipedia , lookup
Computer security wikipedia , lookup
Distributed firewall wikipedia , lookup
Wireless security wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Airborne Networking wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
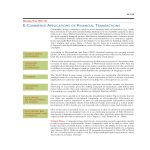
Case study: UniCredit Tiriac Bank deploys Cisco Network Admission Control Bogdan Zamfir, CISM – Head of IT Function, ICT Security, UniCredit Tiriac Bank Victor Alazaroae – Presales Consultant, Datanet Systems AGENDA § UNICREDIT TIRIAC BANK PROFILE § CISCO NETWORK ADMISSION CONTROL SOLUTION OVERVIEW § Initial situation § Business objectives § Architecture deployment § Phases § RESULTS § WHY DATANET SYSTEMS? § NEXT STEPS 2 PROFILE 3 About UniCredit Tiriac Bank q Being in the top 5 on the Romanian market, UniCredit Tiriac Bank offers to its customers, through over 235 branches and over 3.000 employees, financial solutions for the needs of individuals, SMEs, corporations, freelancers. q UniCredit Tiriac Bank at a glance (as at 31 December 2010) q Total assets: RON 20.8 billion q Total revenues: RON 1,363 million q Net profit: RON 171 million q Customers: over 500,000 q UniCredit is a major international financial institution with strong roots in 22 European countries and an international network present in approximately 50 markets, with 9,585 branches and more than 161,000 employees. In the CEE region, UniCredit operates the largest international banking network with around 4,000 branches and outlets. 4 SOLUTION OVERVIEW 5 Initial Situation: Figures q 235 + branches q 3500 online users accessing the network with their laptops and desktops: q internal employees (fix and mobile workstations) q consultants q partners q 3000 + passive devices connected on the network like: q IP phones q Printers q FAXes q ATMs q Video surveillance equipments 6 Initial Situation: Access methods q Closed network q Access control into the network infrastructure is actually based on MAC address manual restriction q User/PC authentication using dot1x 7 Initial Situation: Main Issues q Administrative and operational tasks to permit user and device to access the network are slow and heavy due to: q q q q New users Mobility New devices (printers, IP phones, FAXes, etc.) There is no tool available to check the compliance level of the PC s accessing the network infrastructure like: q q q Windows updates AV updated Mandatory desktop software 8 Business Objectives q Reduce administrative and operational cost using a scalable/automated solution that: q automatically enforce security policies on all devices q controls access on the network q minimize the effort of the network administrators q Increase the operational efficiency using a scalable/ automated solution that: q discovers and identifies dynamically all passive devices q controls the access of passive devices on the network infrastructure q minimize the effort of the infrastructure administrators 9 Business Objectives (2) q Minimize the security risks associated with noncompliant and non-authorized devices accessing the network: q minimize number of security incidents q reducing loss and leakage of information q minimize the administrative/operational effort 10 Architecture Deployment 11 Phases q q Phase 1 q Local Testing q Pilot q Requirements Phase 2 q extending the solution across all Bank s infrastructure 12 Phase 1: Local and Pilot testing q Local Testing q q 16 testing scenarios Pilot Testing q implementing the solution in a branch for one month 13 Phase 1: Local Testing and Pilot Results q Requirements for access, changes and configuration in the network infrastructure q Requirements for AV checks and enforcements q Requirements for Windows Update checks and enforcements 14 Phase 1: Network infrastructure requirements q q User authentication before accessing network resources: q Role base access for HQ users q Fix access for Branch users Automatic discovery, identify and monitoring of the passive devices and assigning to the right VLAN: q IP Phone q Printers q FAXes q ATMs q Video Surveillance Equipments 15 Phase 1: Network infrastructure requirements (2) q Changes and configuration in the network infrastructure q Branch and HQ access switches configuration (authentication VLAN, SNMP) q Branch WAN routers configuration (routing, ACLs, SNMP, Netflow) 16 Phase 1: Requirements for AV checks and enforcements q AV Symantec Endpoint Protection Version 11.0.5002.301 q AV services: q Symantec Endpoint Protection q Symantec Event Manager q Symantec Management Client q Symantec Settings Manager q AV definition 17 Phase 1: Requirements for Microsoft Windows checks and enforcements q Windows AD integration and SSO user authentication q Automatic Update service is started q Latest Windows updates patches installed on client machine q Update patches accordingly with the WSUS update policy 18 Phase 2 q Deploying the NAC solution across all Bank infrastructure gradually: q Preparing the network infrastructure (routers, switches) q Distributing the agent software to client workstations q User authentication to access the network resource without checks and enforcement q User authentication to access the network resource with checks but without enforcement q User authentication to access the network resource with checks and enforcement. 19 RESULTS 20 How user authentication, checks and enforcement happens? 21 How headless (passive) device are accessing the network? 22 NEXT STEPS q Adding more checks and application enforcement on desktops beside AV and Windows Update q Integrating with the existing SIEM platform 23 WHY DATANET SYSTEMS? q Long term relationship with the Bank q Competence of the technical team q Expertise in network security solutions q Knowledge of the needs of the banking sector q Flexibility in order to accommodate to the bank needs 24 DATANET SYSTEMS – Profile and experience q Cisco Gold Partner since 2004, q Cisco Learning Partner since 2008 q Datanet is Cisco Advanced Security specialized partner = certified specialists in Cisco security technologies + lab + professional services portfolio q Datanet personnel includes 9 CCIE R&S and Security, CISM, Cisco and Ironport security specialist certifications q 13 years experience in network security projects for banks, service providers, enterprises. CISCO NAC Key Ingredients Cisco Network Admission Control How do you record and track headless devices in your environment? How do you centrally provision and manage guests who access your network? How do you centrally provision and manage guests who access your network? Guest User Account Detail Delivery Installed Agent, Web Agents, or Agent-less Datanet Systems – professional and financial services q Proof of concept q Low level design q Installation and commissioning q Outsourced operations (monitoring, reporting, MAC) q 24x7 rapid on-site service and technical support q Financial services – leasing or rental Datanet Systems – Application customization and remediation Datanet Systems – device profile identification customization Thank you! Q&A 36