Chapter 1/Tutorial
... of incoming messages to the target system essentially forces it to shut down, thereby denying service to the system to legitimate users. select target break into hosts around the network .(botent) send packets toward target from compromised hosts ...
... of incoming messages to the target system essentially forces it to shut down, thereby denying service to the system to legitimate users. select target break into hosts around the network .(botent) send packets toward target from compromised hosts ...
Network Architectures - Computing Sciences
... conversation with an internal device, thus limiting an attacker’s options to cause mischief ...
... conversation with an internal device, thus limiting an attacker’s options to cause mischief ...
Chapter 10
... Router – Device that connects many LANs – More sophisticated than a bridge – Process header information of a packet ...
... Router – Device that connects many LANs – More sophisticated than a bridge – Process header information of a packet ...
the T-Link is
... is the recipient of key industry awards • Communications are secured with AES encryption that is approved by NIST for homeland security applications • T-Link sends very small 80 byte packets of information so there is no real impact on the network • T-Link can be configured to operate as a stand-alo ...
... is the recipient of key industry awards • Communications are secured with AES encryption that is approved by NIST for homeland security applications • T-Link sends very small 80 byte packets of information so there is no real impact on the network • T-Link can be configured to operate as a stand-alo ...
Chapter 7
... 6. Identify the benefits of business mobility 7. Identify the challenges of business mobility ...
... 6. Identify the benefits of business mobility 7. Identify the challenges of business mobility ...
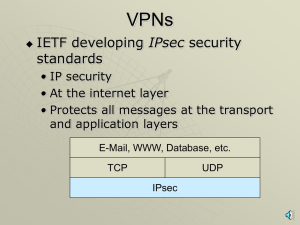
VPNs, PKIs, ISSs, SSLs with narration
... PKI Server Creates Public KeyPrivate Key Pairs • Distributes private keys to applicants securely ...
... PKI Server Creates Public KeyPrivate Key Pairs • Distributes private keys to applicants securely ...
presentation
... In this design, computers are connected via a single cable, but the end nodes also are connected to each other. In this design, the signal circulates through the network until it finds the intended recipient. If a network node is not configured properly, or it is down temporarily for another reason, ...
... In this design, computers are connected via a single cable, but the end nodes also are connected to each other. In this design, the signal circulates through the network until it finds the intended recipient. If a network node is not configured properly, or it is down temporarily for another reason, ...
Trojan Horse - Communications Systems Center
... sources (e.g., PS files, HyperCard files, MS Office documents, Java, ...), if you can help it. Avoid the most common operating systems and email programs, if possible. ...
... sources (e.g., PS files, HyperCard files, MS Office documents, Java, ...), if you can help it. Avoid the most common operating systems and email programs, if possible. ...
lectures1-2
... Basic Service Set (BSS) (aka “cell”) in infrastructure hub, switch mode contains: or router wireless hosts access point (AP): base station AP ad hoc mode: hosts only ...
... Basic Service Set (BSS) (aka “cell”) in infrastructure hub, switch mode contains: or router wireless hosts access point (AP): base station AP ad hoc mode: hosts only ...
About EICTA - Baltic IT&T Review
... Within 15 years: ► Early ’90s: narrowband dialup Internet access (e-mail, ...
... Within 15 years: ► Early ’90s: narrowband dialup Internet access (e-mail, ...
COEN 350
... ml To gain access to packages, use spoofed ARP (Address Resolution Protocol) to reroute traffic. ...
... ml To gain access to packages, use spoofed ARP (Address Resolution Protocol) to reroute traffic. ...
Extreme Networks Supports Wireless Mobility at Patient Bedside for
... Mobile access to patient records or to the hospital information system in the hospital is realized with the Extreme Networks infrastructure with the use of a wireless LAN and laptop PCs. Access to the network and associated resources must be guaranteed in the local ward round area, in particular at ...
... Mobile access to patient records or to the hospital information system in the hospital is realized with the Extreme Networks infrastructure with the use of a wireless LAN and laptop PCs. Access to the network and associated resources must be guaranteed in the local ward round area, in particular at ...
Computer Network - Forman Christian College Wiki
... • A special-purpose computer that directs data traffic when several paths are available • A router examines the destination info in each arriving packet and then routes it through the most efficient path available • The router either delivers the packet to the destination computer across a local net ...
... • A special-purpose computer that directs data traffic when several paths are available • A router examines the destination info in each arriving packet and then routes it through the most efficient path available • The router either delivers the packet to the destination computer across a local net ...
William Stallings, Cryptography and Network Security 3/e
... one of the most famous security models implemented as mandatory policies on system has two key policies: no read up (simple security property) – a subject can only read/write an object if the current security level of the subject dominates (>=) the classification of the object ...
... one of the most famous security models implemented as mandatory policies on system has two key policies: no read up (simple security property) – a subject can only read/write an object if the current security level of the subject dominates (>=) the classification of the object ...
The Need for Security
... Deliberate Software Attacks Malicious code Malicious software Malware First business hacked out of existence Denial-of-service attack Cloudnine British Internet service provider ...
... Deliberate Software Attacks Malicious code Malicious software Malware First business hacked out of existence Denial-of-service attack Cloudnine British Internet service provider ...
Communications and Networking Exam Questions
... local area network, including hub/switches, wireless access points. Explain the different roles of computers in a client-server and peer-to-peer network. ...
... local area network, including hub/switches, wireless access points. Explain the different roles of computers in a client-server and peer-to-peer network. ...
Release notes_1.3
... Switches. From your browser, use your Switch IP address to access the MNS-BB management software, which functions as a GUI-based interface. e.g., http://192.168.1.10. SSL/TLS Secure Sockets Layer (SSL) and Transport Layer Security (TLS) enables the embedded web server of the switch to handle secur ...
... Switches. From your browser, use your Switch IP address to access the MNS-BB management software, which functions as a GUI-based interface. e.g., http://192.168.1.10. SSL/TLS Secure Sockets Layer (SSL) and Transport Layer Security (TLS) enables the embedded web server of the switch to handle secur ...
What is a Network? A network consists of two or more nodes
... Wide Area Networks (WANs) connect larger geographic areas, such as Ontario, Canada, or the world. For instance, Nova Corp. has a plant in Sarnia and a plant in Calgary. Dedicated transoceanic cabling or satellite uplinks may be used to connect this type of network. The largest WAN is the Internet. U ...
... Wide Area Networks (WANs) connect larger geographic areas, such as Ontario, Canada, or the world. For instance, Nova Corp. has a plant in Sarnia and a plant in Calgary. Dedicated transoceanic cabling or satellite uplinks may be used to connect this type of network. The largest WAN is the Internet. U ...
The CyberFence Difference
... Precise processes in most critical-infrastructure networks rely on the undisturbed operation of industrial control systems (ICS). Failures within the ICS can cause critical services to fail, and may result in severe injury to people, property and the environment. In evaluating options for securing v ...
... Precise processes in most critical-infrastructure networks rely on the undisturbed operation of industrial control systems (ICS). Failures within the ICS can cause critical services to fail, and may result in severe injury to people, property and the environment. In evaluating options for securing v ...
Computer Security
... – Carry out manual user authentication – As users are added or changed, more maintenance is required for each script – Usernames and passwords held in one central script Many times in clear text ...
... – Carry out manual user authentication – As users are added or changed, more maintenance is required for each script – Usernames and passwords held in one central script Many times in clear text ...
Hacking - Computer Engineering
... Step 4: Attacker’s site receives request, acts as proxy, forwards it to real website. Step 5: Real website answers, attackers site forwards to victim. ...
... Step 4: Attacker’s site receives request, acts as proxy, forwards it to real website. Step 5: Real website answers, attackers site forwards to victim. ...
Introduction to Computer Networking
... • LAN – Local Area Network – Small local area, a home network for example ...
... • LAN – Local Area Network – Small local area, a home network for example ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.