A Scalable, Commodity Data Center Network Architecture
... • Using same ip on dual homed servers • Allowing growth of server farms. ...
... • Using same ip on dual homed servers • Allowing growth of server farms. ...
dc9798.PDF
... Discuss the ISO 7-layered model and show how different network types, such as Ethernet, Token Ring and FDDI, fit with networking protocols, such as SPX/IPX, TCP/IP, and NetBEUI. Give some examples of practical networks and the protocols that they use. ...
... Discuss the ISO 7-layered model and show how different network types, such as Ethernet, Token Ring and FDDI, fit with networking protocols, such as SPX/IPX, TCP/IP, and NetBEUI. Give some examples of practical networks and the protocols that they use. ...
Routing
... • Split horizon with poison reverse – B sends update (D, inf., A) to A, since it learned from A. – prevents two-node loops ...
... • Split horizon with poison reverse – B sends update (D, inf., A) to A, since it learned from A. – prevents two-node loops ...
HW2
... Chapter 4, part 1 in the notes). Suppose that shortest hop routing is used in both inter-AS and intra-AS routing. For inter-AS routing, this means that a packet that is to be routed at the inter-AS level to a destination in network X will be routed to the closest (shortest number of hops) inter-AS r ...
... Chapter 4, part 1 in the notes). Suppose that shortest hop routing is used in both inter-AS and intra-AS routing. For inter-AS routing, this means that a packet that is to be routed at the inter-AS level to a destination in network X will be routed to the closest (shortest number of hops) inter-AS r ...
A Router
... hardware designed to allow computers to communicate over a computer network. • Provides a low-level addressing system through the use of MAC addresses. It allows users to connect to each other either by using cables or wirelessly. • The NIC is both an OSI layer 1 (physical layer) and layer 2 (data l ...
... hardware designed to allow computers to communicate over a computer network. • Provides a low-level addressing system through the use of MAC addresses. It allows users to connect to each other either by using cables or wirelessly. • The NIC is both an OSI layer 1 (physical layer) and layer 2 (data l ...
Broadcast Routing - UCLA Computer Science
... Routing to another LAN A creates IP packet with source A, destination B A uses ARP to get R’s physical layer address for 111.111.111.110 A creates Ethernet frame with R's MAC address as destination A’s data link layer sends the Ethernet frame ...
... Routing to another LAN A creates IP packet with source A, destination B A uses ARP to get R’s physical layer address for 111.111.111.110 A creates Ethernet frame with R's MAC address as destination A’s data link layer sends the Ethernet frame ...
Brief Announcement: A Conjecture on
... two terminals, and if there were many paths between the same two nodes, there would be multiple nodes with the same distances to both terminals. What of odd rings? In any ring, there are two paths between any two nodes a and c; if we take rings with a third node b, there is a path from a to c passin ...
... two terminals, and if there were many paths between the same two nodes, there would be multiple nodes with the same distances to both terminals. What of odd rings? In any ring, there are two paths between any two nodes a and c; if we take rings with a third node b, there is a path from a to c passin ...
Solution - Rab Nawaz Jadoon
... b. What is source based tree? Discuss its major bottleneck? Solution: Source Based Tree In the source-based tree approach, each router needs to have one shortest path tree for each group. The shortest path tree for a group defines the next hop for each network that has loyal member(s) for that grou ...
... b. What is source based tree? Discuss its major bottleneck? Solution: Source Based Tree In the source-based tree approach, each router needs to have one shortest path tree for each group. The shortest path tree for a group defines the next hop for each network that has loyal member(s) for that grou ...
ECE544Lec4-5DR07
... • Each node assumed to know state of links to its neighbors • Step 1: Each node broadcasts its state to all other nodes • Step 2: Each node locally computes shortest paths to all other nodes from global state ...
... • Each node assumed to know state of links to its neighbors • Step 1: Each node broadcasts its state to all other nodes • Step 2: Each node locally computes shortest paths to all other nodes from global state ...
ShapeShifter - Computer Science
... maintain a mesh of low-latency unicast links and use its minimal spanning tree for distribution. Also showed costs relative to IP Multicast are not excessive. Overcast: A core group of well-placed nodes uses end-system multicast to distribute bulk content internally, in order to eventually provide ...
... maintain a mesh of low-latency unicast links and use its minimal spanning tree for distribution. Also showed costs relative to IP Multicast are not excessive. Overcast: A core group of well-placed nodes uses end-system multicast to distribute bulk content internally, in order to eventually provide ...
PeerNet: Pushing Peer-to-Peer Down the Stack
... • each node controls a range of addresses • responding node splits its range in half – joining node gets the lower half – joining node’s address is the lowest address in that range – nodes get evenly distributed in the address space ...
... • each node controls a range of addresses • responding node splits its range in half – joining node gets the lower half – joining node’s address is the lowest address in that range – nodes get evenly distributed in the address space ...
Medium Time Metric
... each node is willing to forward data for other nodes, and so the determination of which nodes forward data is made dynamically based on the network connectivity which allocates transmission capacity flexibly to connections ...
... each node is willing to forward data for other nodes, and so the determination of which nodes forward data is made dynamically based on the network connectivity which allocates transmission capacity flexibly to connections ...
Protocol Suites - York Technical College
... TCP/IP - Transmission Control Protocol/Internet Protocol ...
... TCP/IP - Transmission Control Protocol/Internet Protocol ...
Lecture 8: Routing I Distance-vector Algorithms
... Write (input id, output id, next hop) into each router on path Flexible (one path per flow) Send packet with path id Router looks up input, swaps for output, forwards on next hop Repeat until reach destination Table lookup for forwarding (faster than IP lookup?) ...
... Write (input id, output id, next hop) into each router on path Flexible (one path per flow) Send packet with path id Router looks up input, swaps for output, forwards on next hop Repeat until reach destination Table lookup for forwarding (faster than IP lookup?) ...
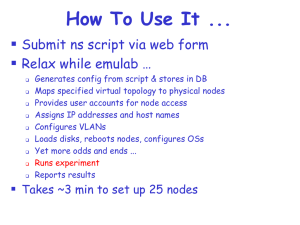
emulab.net: A Network Emulation and Distributed Systems Testbed
... “The authors ignore interrupt handling overhead in their evaluation, which likely dominates all other costs.” “You have to know the right people to use the cluster.” “The cluster is hard to use.” “ runs FreeBSD 2.2.x.”
“February’s schedule for is…”
“ is ...
... “The authors ignore interrupt handling overhead in their evaluation, which likely dominates all other costs.” “You have to know the right people to use the cluster.” “The cluster is hard to use.” “
Network Layer
... and learning their names. 2. Each router constructs a link state packet (LSP) which consists of a list of names and cost for each of its neighbors. 3. The LSP is transmitted to all other routers. Each router stores the most recently generated LSP from each other router. 4. Each router uses complete ...
... and learning their names. 2. Each router constructs a link state packet (LSP) which consists of a list of names and cost for each of its neighbors. 3. The LSP is transmitted to all other routers. Each router stores the most recently generated LSP from each other router. 4. Each router uses complete ...