* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download OPERATINGSYSTEMS 2015
Library (computing) wikipedia , lookup
Copland (operating system) wikipedia , lookup
Plan 9 from Bell Labs wikipedia , lookup
Security-focused operating system wikipedia , lookup
Distributed operating system wikipedia , lookup
Spring (operating system) wikipedia , lookup
Process management (computing) wikipedia , lookup
Burroughs MCP wikipedia , lookup
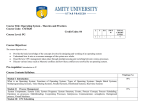
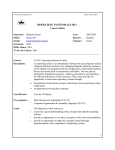
PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet TABLE OF CONTENTS 1. GENERAL INFORMATION 2. WHAT IS THE COURSE ABOUT ? 3. COURSE OBJECTIVES 4. COURSE PRE-REQUISITES 5. LEARNING OUTCOMES 6. VENUE AND HOURS/WEEK 7. FACULTY DETAILS 8. MODULE MAP 9. RECOMMENDED BOOKS/JOURNALS/WEBSITES 10. ASSESSMENT 11. QUESTION BANK 12. BRAIN BANK Dept. Of MCA PESIT BSC 2015 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 1. GENERAL INFORMATION Academic Year Semester Title Operating Systems : : 2015 II Code Duration (Hrs) Lectures 52 Hrs 13MCA24 Seminars 4 Hrs Total 2. 56 Hrs WHAT IS THE COURSE ABOUT ? Operating system (OS) is the most important type of system software in a computer system. Without an operating system, a user cannot run an application program on their computer. Operating systems are found on almost any device that contains a computer – from cellular phones and video game consoles to supercomputers and web servers. The course covers the following essential concepts: Processes, Memory Management, File Systems, I/O Devices and Deadlocks. The module aims to provide the students with an understanding of the role of the operating system as a resource manager and the data structures and algorithms used in the implementation of the operating system. The lab sessions will enable the students to get familiar with the Linux Operating System. 3. 4. COURSE OBJECTIVES To expose students to underlying concepts and design principles of Operating Systems. To familiarise students with the use of operating system primitives such as system calls, files, processes, threads, synchronization and communication mechanisms. Dept. Of MCA PESIT BSC 2015 COURSE PRE-REQUISITES Extensive programming skills in C language, equivalent to Programming Techniques. Understanding of data structures. Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 5. LEARNING OUTCOMES By the end of the course students will be able to describe the basic principles used in the design of modern operating systems. In particular, they will: 6. • be able to distinguish different styles of operating system design. • understand device and I/O management functions in operating systems as part of a uniform device abstraction. • have an understanding of disk organisation and file system structure. • be able to give the rationale for virtual memory abstractions in operating systems. • understand the main principles and techniques used to implement processes and threads as well as the different algorithms for process scheduling. • understand the main mechanisms used for inter-process communication. • understand the main problems related to concurrency and the different synchronization mechanisms available. • have the ability to evaluate security risks in operating systems and understand the role operating systems can and should play in establishing security. VENUE AND HOURS/WEEK All lectures will normally be held on V Floor. Lecture Hours/week: 4Hrs 7. FACULTY DETAILS Name Mr. Dilip Kumar Maripuri Department MCA Designation Associate Professor Room No 509, Fifth Floor Email Address [email protected], [email protected] Dept. Of MCA PESIT BSC 2015 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 8. Class # MODULE MAP Unit # 2 4 5 8 9 10 11 Chapter-2 Operating Systems : System Structures Chapter-3 Process Management 27 51.9% Execution of the Operating System, Security Issues Processes and Threads Principles of Concurrency 26 04 System Generation 18 25 44.2% System Design and Implementation CPU Scheduler and Scheduling 24 06 System Structure, Virtual Machines 17 23 32.6% System Calls, System Programs Symmetric Multiprocessing(SMP), Micro kernels,. 22 06 System Components, Operating – System Services 16 21 21.1% Handheld Systems, Feature Migration, Computing Environments Process Description, Process Control 20 05 Distributed Systems, Clustered Systems, Real Time Systems 13 19 11.5% Introduction to Operating System, Mainframe Systems, Desktop Systems, Multiprocessor Systems Process, Process States 15 06 I/O Communication Techniques 12 14 Cum. % Interrupts, The Memory Hierarchy, Cache Memory Chapter-1 Introduction : Computer and Operating Systems 6 7 Ref. Chap Basic Elements, Processor Registers, Instruction Execution 1 3 Topic Outline % Portions Covered Mutual Exclusion Chapter-4 Hardware Support , Semaphores Mutual Execution and Monitors Synchronization Message Passing Dept. Of MCA PESIT BSC 2015 Readers/Writes Problem Principles of Deadlock Chapter-5 Deadlock and Starvation Perservance Deadlock Prevention, Deadlock Avoidance Deadlock Detection, An Integrated Deadlock Strategy Dining Philosophers Problem Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet Class # Unit # Topic Outline 28 Memory Management strategies: Background, 29 Swapping, Contiguous Memory Allocation 30 Paging, Structure of the page table 31 32 Chapter-6 Memory Management 34 Page Replacement (Continued) 35 Allocation of Frames, Thrashing 36 File Concept 37 Access Methods, Directory Structure 40 Directory Implementation, Allocation Methods 42 Free space management 44 45 Chapter- 8 Secondary Storage, Computer Security Linux History, Design principles 51 52 80.7% 04 88.4% 06 100% The Security Problem, User Authentication 47 50 07 Disk Scheduling, Disk management Program Threats, System Threats. 49 67.3% Mass Storage Structures: Disk Structure, Disk Attachment 46 48 08 Chapter-7 File system mounting, File sharing File system, Protection Implementation of File System File system structure, File system implementation 41 43 Cum. % Virtual Memory Management: Background, Demand Paging Page Replacement 39 Ref. Chap Segmentation 33 38 % Portions Covered Kernel modules Chapter- 9 Case Study: The Process management, Scheduling Linux OS Memory management Dept. Of MCA PESIT BSC 2015 File systems Input and Output, Inter-process communication 9. RECOMMENDED BOOKS/JOURNALS/WEBSITES a.PRESCRIBED TEXTBOOK a.Text Book 1 - Operating System Principles: A. ,Silberschatz, P. Galvin, G. Gagne, 8 th Edition, Wiley – India, 2009 b.Text Book 2 -“Operating Systems – Internals and Design Principles”, William Stallings, Pearson, 6th edition, 2012 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet b.REFERENCE BOOKS a.R1 (Reference Book 1) - Operating Systems-A Concept based Approach: D.M. Dhamdhere, 2 nd Edition, Tata McGraw-Hill, 2002. b.R2 (Reference Book 2) - Introduction to Operating systems- Concepts and Practice: P.C.P Bhatt, 2 nd Edition, PHI, 2008. c.R3 (Reference Book 3) - Operating Systems: Harvey M Deital, 3 Edition,Pearson Education , 1990. 10. rd ASSESSMENT a.WRITTEN EXAMINATION QUESTION PAPER STRUCTURE No.of Questions 8 Main Questions No. of Questions to be answered 5 Examination Date November 2013 Paper Duration 3 Hrs Total Marks 100 Pass Marks 40 b.CONTINUOUS ASSESSMENT Weighting (%) Assignment(s):5 Marks (10%) Seminar(s) 5 Marks (10%) Test(s) 40 Marks (80%) Total Marks 50 Marks Dept. Of MCA PESIT BSC 2015 c.INTERNAL TEST PORTIONS Test 1:Chap. 1, 2, 3 Test 2:Chap. 3, 4, 5 Test 3 :Chap. 6, 7, 8, 9 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 11. QUESTION BANK Chapter 1: Introduction to operating system, System Structures Objective: This chapter gives an introduction about the operating system,how they are designed and constructed. The common features of an operating system are discussed. 1.What is an operating system? What are the functionalities of an OS? 2.Explain various components of an OS. 3.What are the services provided by an OS? 4.Explain the following types of OS: i.Batch ii. Real–Time iii. Time–Sharing iv. Distributed systems v.Multimedia systems 5.Briefly explain the layered approach to the structuring of an OS. 6.Discuss the need for an operating system. 7.What is Multiprogramming? What are the main advantages of multiprogramming? 8.Differentiate between multiprogramming and time sharing. 9.List the operating system components. 10. What is a thread? Mention the benefits of multithreaded programming. 11. Discuss the microkernel briefly. 12. Explain the following: i.Tightly coupled system ii. Loosely coupled system 13. Explain the following: i.Multiprocessor Systems ii. Clustered Systems 14. What are system calls? Explain. 15. What is virtual machine? Explain VMware architecture? Chapter 2: Process Management Objective: This chapter describes the process concept and concurrency of modern operating systems. Topics under this chapter also cover methods for process scheduling and interprocess communication. Dept. Of MCA PESIT BSC 2015 16. What is a process? With the help of a diagram, explain the different states of a process. 17. Explain the process control block , in detail. 18. What is CPU Scheduling? What is the difference between preemptive and non- preemptive scheduling? 19. What are the various reasons for allowing concurrent execution of processes? 20. What is thread? Explain the concept of multithreading and their various models. 21. Discuss the benefits of multithreaded programming. 22. What is CPU Scheduling? 23. What is a scheduler? Explain different types of schedulers. 24. Explain the different criteria to select a scheduling algorithm. 25. Explain First Come First Serve Scheduling Algorithm. 26. Explain Shortest Job First Scheduling Algorithm. 27. Explain Round Robin Scheduling Algorithm. Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 28. Explain Priority Scheduling Algorithm. 29. Explain multilevel queue scheduling and multilevel feedback queue scheduling with illustration. 30. Differentiate between direct communication and indirect communication. 31. Describe the use of mailboxes in inter process communication 32. Explain the concept of messages with reference to inter process communication. 33. 5 batch jobs A, B, C, D, E arrive at a computer center at almost the same time. They have estimated running times of 10,6,2,4 and 8 seconds. Their priorities are 3,5,2,1 and 4 respectively. For each of the following draw Gantt Chart and compute turnaround time. (i) RR (Quantum time 1 sec) (ii) FCFS (iii) Priority (iv) SJF 34. What is context switching? Explain process context switching with process state diagram. Also discuss short term and long term scheduler. 35. Describe some of the CPU scheduling algorithm evaluation methods. 36. Consider the following set of processes, which have arrived at the ready queue with the burst time and the arrival time given in milliseconds as shown below: Processes Burst Time in milliseconds Arrival Time in milliseconds P1 8 0 P2 4 1 P3 9 2 P4 5 3 Draw the Gantt chart and calculate the average waiting time using the following algorithms (I) First Come First Serve (FCFS) (II) Shortest Job First (SJF – pre-emptive). 37. Consider the following set of processes: Processes Burst Time in milliseconds Burst Time P1 8 3 P2 5 1 P3 12 2 Dept. Of MCA PESIT BSC 2015 P4 4 4 The processes are assumed to have arrived in the order P1, P2, P3, P4 all at time 0. Obtain the Gantt chart, average waiting time using (i) First Come First Serve (ii) Non Pre-emptive Shortest Job First (iii) Non Pre-emptive priority-scheduling schemes. Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 38. Consider the following processes which have arrived the ready queue with the burst time and the arrival time given in milliseconds as shown Processes Burst Time in milliseconds Arrival Time in milliseconds P1 34 0 P2 12 1 P3 5 2 P4 6 3 Construct the Gantt chart and calculate the average waiting time using the FCFS and SJF (preemptive). 39. Consider the following set of processes, with the length of the CPU burst given in milliseconds. Processes Burst Time in milliseconds Arrival Time in milliseconds Priority P1 10 0 4 P2 12 2 3 P3 14 3 5 P4 16 6 1 P5 5 30 1 1.Draw a Gantt chart that illustrates the execution of these processes using the preemptive priority scheduling algorithm (a smaller priority number implies a higher priority). 2.Calculate the average waiting time. 40. Suppose the following jobs arrive for processing at the times indicated,each job will run the listed amount of time. Arrival Time Burst Time Processes in milliseconds in milliseconds P1 0 10 P2 1 15 P3 2 17 P4 3 20 Dept. Of MCA PESIT BSC 2015 1.Draw a Gantt chart that illustrates the execution of these processes using the preemptive priority scheduling algorithm (a smaller priority number implies a higher priority). 2.Calculate the average waiting time. What is your conclusion? 41. Consider the following set of processes : Burst Time Processes Priority in milliseconds Perservance P1 6 3 P2 4 1 P3 10 2 P4 13 4 Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet The processes have arrived in the order P1, P3, P2 and P4. Obtain the Gantt chart, waiting time using (i) SJF (ii) Pre-emptive priority-scheduling schemes. Chapter 3: Process Synchronization Objective: This chapter discusses the various mechanisms to ensure the orderly execution of processes that share a logical address space, so that data consistency is maintained. Various methods of process synchronization are discussed. 42. What do you mean by semaphore? How do you access a semaphore? 43. What is a semaphore? Explain the role of semaphores in solving mutual exclusion problem. 44. Define critical section problem and explain the requirements to be met by a solution to the critical section problem. 45. Discuss any two classic problems of synchronization. 46. Explain the following terms: i) Mutex ii) Race condition 47. Explain the Readers-Writers problem in detail. 48. Explain Dining-Philosophers problem and its solution. 49. Define the bounded buffer problem and its solution. 50. List out the properties and characteristics of semaphores. 51. Give a solution to n-process critical section problem using “Test-and-set” and show its correctness. Chapter 4: Deadlocks Objective: This chapter discusses about the deadlocks, various conditions necessary for deadlock and different methods that an operating system can use to prevent or deal with deadlocks. 52. What is deadlock? Explain four necessary conditions for a deadlock. 53. List different methods for handling deadlock. Explain deadlock prevention in detail. 54. What is a safe state in a system? 55. Explain in detail with neat diagrams the resource allocation graph technique to detect deadlock in a system. 56. What is a deadlock? Describe the necessary conditions for a dead lock. Explain how deadlock can be prevented. 57. What is racing and deadlock? Why do they occur? 58. Consider the following snapshot of a system: ALLOCATION REQUEST AVAILABLE A P0 0 P1 1 P2 2 P3 0 Dept. Of MCA PESIT BSC 2015 B C A B C 1 0 1 0 1 2 1 2 2 1 3 0 1 2 3 1 1 1 4 3 A B C 1 0 2 a. What is the content of need matrix? b. Is the system in SAFE state? If so, give the safe sequence. Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 59. Consider the following snapshot of a system: ALLOCATION REQUEST AVAILABLE A B C A B C P0 0 1 0 7 5 3 P1 2 0 0 3 2 2 P2 3 0 2 9 0 2 P3 2 1 1 2 2 2 P4 0 0 2 4 3 3 A B C 3 3 2 a. What is the content of need matrix? b. Is the system in SAFE state? If so, give the safe sequence. 60. With an example, illustrate Banker’s Algorithm for Dead lock avoidance. Explain briefly about the deadlock avoidance. Chapter 5: Memory Management Objective: This chapter deals with main memory management during the execution of a process. The different memory management schemes such as paging and segmentation are discussed. 61. Explain the following with respect to memory management: i) First Fit ii) Best Fit iii) Worst Fit 62. Bring out the difference between internal and external fragmentation. 63. What is page fault? What action does the operating system take when a page fault occurs? 64. Explain paging with illustration. 65. Explain paging with demand scheme in handling virtual memory and how it handles memory requests. 66. Define the structure of a page table. 67. Explain the following: i) Hierarchical paging ii) Inverted page table 68. Explain segmentation illustrating segmentation hardware. 69. Explain the concept of virtual memory. 70. Explain an implementation of LRU replacement policy. 71. When do page faults occur? 72. Discuss the steps in handling a page fault with the help of a neat diagram. 73. Explain the following page replacement algorithms. (i) FIFO page replacement (ii) Optimal page replacement 74. Show how Translation Look aside Buffer (TLB) improves the performance of paged system. 75. Discuss demand paging. Explain copy-on-write. 76. For the following reference string 1, 6, 2, 4, 3, 1, 2, 5, 6, 5, 1, 2, 3, 7, 3, 2, 1, 6, 4 How many page faults would occur for the page replacement algorithms: LRU,FIFO and Optimal. Trace these algorithms for 3 frames. What is your comment on these algorithms? Dept. Of MCA PESIT BSC 2015 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 77. Consider following reference string 7,0,1,2,0,3,0,4,2,3,0,3,2,1,2,0,1,7,0,1 How many page faults would occur for the page replacement algorithms: LRU,FIFO and Optimal. Trace these algorithms for 3 frames. What is your comment on these algorithms? Note that initially all the frames are empty. 78. What is fragmentation? List the schemes for minimizing fragmentation. 79. Write short notes on Thrashing. Chapter 6: File System, Implementation of File System Objective: This chapter describe how the file system, mass storage and I/O are handled in a modern computer system. 80. What is acyclic graph directory structure? Explain with example. Explain the following: i) File Operations ii) Files Types iii) File attributes 81. Explain different file access method. 82. What is access matrix? How is access matrix implemented? 83. Write a note on: (i) Sequential Access (ii) Direct Access 84. Write a note on: i) Single-level directory ii) Two-level directory iii) Tree-structured directories iv) Acyclic-Graph directories 85. What is a mount point? How a file is mounted and unmounted? 86. Discuss disk free space management. 87. Discuss directory implementation using: (i) Linear list (ii) Hash table 88. Describe the variable partition scheme with the allocation policies–first fit, best fit and worst fit. Mention a disadvantage of best fit. 89. Explain the different disk space allocation methods and compare them. 90. Name the different file allocation methods. Explain the linked allocation method giving merits and demerits. Dept. Of MCA PESIT BSC 2015 Chapter 7: Secondary Storage Structures, Protection Objective: This chapter discusses access to data and programs residing on the disks. It also discusses how the processes in an operating system are protected from one another’s activities. It also discusses the mechanism for controlling the access of programs, processes or users to the resources defined by a computer system. 91. What is disk scheduling? Explain FCFS disk scheduling algorithm. 92. Briefly explain the following disk scheduling policies and compare them : (i) FCFS (II) SSTF (III) SCAN Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 93. 94. 95. 96. Show that SCAN scheduling is not starvation free. Compare SCAN and C-SCAN disk scheduling policies. Compare LOOK and C-LOOK disk scheduling policies. Write short note on: i) Rotational Latency ii) Swap Space Management 97. Suppose that a disk drive has 200 cylinders numbered 0 to 199. the disk is currently serving a request at cylinder 53, and previous request was at cylinder 65. The queue of pending requests in FIFO order is 98, 183, 37, 122, 14, 124, 65, 67. What is the total distance (in cylinders) that the disk arm move to satisfy all the pending requests for each of the below disk scheduling algorithms? Explain each with neat diagram. i) FCFS ii) SSTF iii) SCAN 98. Explain the following. i) Boot Block ii) Bad Block 99. Differentiate between protection and security in the file system, Explain access matrix implementation. 100. What is meant by denial of service? 101. What is authentication? Explain any two approaches for authentication. 102. What are the goals of protection? 103. Explain capability-based system with an example. 104. What is protection concept in OS, explain its Domain & Domain Structure? 105. What is access matrix? Explain with neat figure. Explain any one of the implementation method of access matrix. 106. Write short notes on the following: i) Fragmentation ii) Swap space management. iii) Global table implementation of access matrix. Chapter 8: Case Study: The Linux Operating System Objective: This chapter presents an in-depth examination of the linux operating system. It discuss the internal methods by which Linux implements the interfaces. 107. With a diagram explain the components of the Linux system. 108. Discuss various kernel modules in Linux. 109. Explain process management and process scheduling in Linux operating system. 110. Explain memory management and File systems in Linux operating system. 111. Explain Interprocess communication in Linux operating system. 112. Explain Input-Output in Linux operating system. Dept. Of MCA PESIT BSC 2015 Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet 12. BRAIN BANK EXERCISE 1: The command “man” in Unix systems allows the online display of the manual for the commands and system calls. Further the re-direction operator “>” allows the display to be sent to a file instead of the terminal. Eg. “man fork > file1” will send manual information about fork to the file file1. Use it to obtain such information and get a print-out of the file to be used for this exercise. 1. Write a program that reads 10 integers from the terminal and places them in an array. The program should then fork. The parent process should display the values in all the odd numbered elements while the child displays values in the even numbered elements. For each display the process displaying should indicate whether it is the parent or the child. 2. Modify the above programs such that after the fork, the child modifies values in all odd numbered elements. Each process should now display all its elements. EXERCISE 2: The system call pthread_create allows the creation of threads in Linux systems. The following program creates a thread, the parent executes a loop 1000 times, then displays a message, sleeps for 2 seconds the whole is repeated 10 times. The created thread is similar to the parent except that it sleeps for 1 second instead of 2. #include <pthread.h> void * funct1(void * arg); main() { pthread_t threadid; int i,j; Dept. Of MCA PESIT BSC 2015 int x=1; pthread_create(&threadid,NULL,funct1,(void *)&x); for (j=0; j <10; j++) { for (i=0; i<1000; i++); printf("Hi I'm the parent\n"); sleep(2); } } Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet void * funct1(void * arg) { int i,j; for (j=0;j<10; j++) { for (i=0; i<1000; i++); printf("Hi I'm the created thread\n"); sleep(1); } } 1. Type in the program, compile and execute it. The command for compilation is: cc <programname.c> -lpthread –o <objectfilename> 2. Modify the program so that the created thread executes the loop 1000 times and exit, whereas the parent creates a new thread each time it wakes up. The parent should pass as parameter a number (from 1 to 5) indicating the sequence number of the created thread and the child thread should display its sequence number. Note that the sequence number should be cast as void when being passed to pthread_create and cast back to integer within the thread. 3. Modify the initial program so that it declares a global variable, I, initialized as 0. Both the parent and child thread should increment I each time they go into the loop. I should be protected by the use of mutex locks. Note: To use a mutex lock, it has to be declared of type pthread_mutex_t. Eg. pthread_mutex_t mylock; Dept. Of MCA PESIT BSC 2015 The mutex lock has to be initialized. This can be achieved at declaration time using the macro PTHREAD_MUTEX_INITIALIZER. Eg. pthread_mutex_t mylock = PTHREAD_MUTEX_INITIALIZER; The commands pthread_mutex_lock and pthread_mutex_unlock perform the locking and unlocking of mutex lock types. Eg.pthread_mutex_lock(&mylock); pthread_mutex_unlock(&mylock); Perservance Excellence Service © Dilip Maripuri PESIT BANGALORE SOUTH CAMPUS Module Specification Sheet EXERCISE 3: The following system calls are used for dealing with files in Unix systems: open() read() write() close() seek() (or lseek()) Using man, find out how to use these system calls. 1. Write a program that allows entry of information for a number of students. The information for each student should consist of the student’s names, address and course name. The information should be stored in a file. 2. Write a program that reads the information stored in the file in Question 1 and displays them on the screen, one line per student. 3. A company needs to store the following information about its employees: Employee No. (an integer generated automatically), Employee name (a string of 20 characters), Date of Birth (a string of 8 characters), position (a string of 20 characters). Write a program that reads in the name, date of birth and position of 10 employees from the terminal, generates the employee number (this is just a sequence of integers starting from 1 and incrementing for each employee) and writes the data in a file. Please note that all fields in the record are of fixed length. Hence use blank characters to fill up the sizes of character arrays as required. 4. Write a program that reads an employee number (between 1 and 10) from the terminal, uses seek (or lseek) to go to the appropriate position in the file created in Question 3 and retrieves and displays the information for the employee. Dept. Of MCA PESIT BSC 2015 Perservance Excellence Service © Dilip Maripuri