OpenAFS Quick Start Guide for UNIX
... OpenAFS Administration Guide This guide describes the concepts and procedures that a system administrator must know to manage an AFS cell. It assumes familiarity with UNIX, but requires no previous knowledge of AFS. The first chapters of the OpenAFS Administration Guide present basic concepts and gu ...
... OpenAFS Administration Guide This guide describes the concepts and procedures that a system administrator must know to manage an AFS cell. It assumes familiarity with UNIX, but requires no previous knowledge of AFS. The first chapters of the OpenAFS Administration Guide present basic concepts and gu ...
Slide 1
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
Slide 1
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
Operating Systems
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
INF1060: Introduction to Operating Systems and Data Communication
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
... copy frame pointer into stack pointer - stack top now contains the saved frame pointer pop stack into frame pointer (restore), leaving the return program pointer on top of the stack the RET instruction pops the stack top into the program counter register (EIP), causing the CPU to execute from the "r ...
Improving the Reliability of Commodity Operating Systems
... This dissertation presents an architecture and mechanism for improving the reliability of commodity operating systems by enabling them to tolerate component failures. Improving reliability is one of the greatest challenges for commodity operating systems, such as Windows and Linux. System failures a ...
... This dissertation presents an architecture and mechanism for improving the reliability of commodity operating systems by enabling them to tolerate component failures. Improving reliability is one of the greatest challenges for commodity operating systems, such as Windows and Linux. System failures a ...
CS162 Operating Systems and Systems Programming Lecture 1
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
CS162 Operating Systems and Systems Programming Lecture 1
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
BUILDING A DEPENDABLE OPERATING SYSTEM: FAULT TOLERANCE IN MINIX 3
... ICT Australia. The relaxed atmosphere and top-notch L4 research team made for another pleasant and inspiring stay. I would like to thank my former colleagues and all others who contributed to these experiences. Most of my time was spent at Vrije Universiteit Amsterdam though. Special mention goes th ...
... ICT Australia. The relaxed atmosphere and top-notch L4 research team made for another pleasant and inspiring stay. I would like to thank my former colleagues and all others who contributed to these experiences. Most of my time was spent at Vrije Universiteit Amsterdam though. Special mention goes th ...
Proceedings of the FREENIX Track: 2003 USENIX Annual Technical Conference
... The reason for putting a full kernel in place of the BIOS is simple: Linux does a far better job of detecting and configuring hardware than standard BIOSes do, and its “footprint” in memory is not really that much larger. As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow L ...
... The reason for putting a full kernel in place of the BIOS is simple: Linux does a far better job of detecting and configuring hardware than standard BIOSes do, and its “footprint” in memory is not really that much larger. As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow L ...
NonStop System Glossary
... Legal Notice Confidential computer software. Valid license from HP required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s ...
... Legal Notice Confidential computer software. Valid license from HP required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s ...
What is System Hang and How to Handle it
... the causes of system hang, and accordingly, each study focuses on its own assumptions about the causes of system hang. As a result, it is necessary to study the causes of system hang more comprehensively. Second, most methodologies for detecting system hang need additional assistance, provided by ei ...
... the causes of system hang, and accordingly, each study focuses on its own assumptions about the causes of system hang. As a result, it is necessary to study the causes of system hang more comprehensively. Second, most methodologies for detecting system hang need additional assistance, provided by ei ...
A comprehensive cross-development tool chain and runtime
... benefits of a compact and robust kernel with small memory footprint, combining rich functionality with high performance and true real-time behavior. It is ideal for running on the Microblazes of the programmable logic in the Zynq™-7000. Enea® OSE has a fully pre-emptive kernel, optimized to provide ...
... benefits of a compact and robust kernel with small memory footprint, combining rich functionality with high performance and true real-time behavior. It is ideal for running on the Microblazes of the programmable logic in the Zynq™-7000. Enea® OSE has a fully pre-emptive kernel, optimized to provide ...
Secure Virtual Architecture: Security for Commodity Software Systems
... memory safety attacks such as buffer overflows, and they can be tricked into dynamically loading malicious code. Worse yet, commodity operating system kernels are highly privileged; exploitation of the kernel results in compromise of all applications on the system. This work describes the Secure Virt ...
... memory safety attacks such as buffer overflows, and they can be tricked into dynamically loading malicious code. Worse yet, commodity operating system kernels are highly privileged; exploitation of the kernel results in compromise of all applications on the system. This work describes the Secure Virt ...
Developing Interfaces and Interactivity for DSpace with
... – Basic understanding will help diagnose problems – Many skill levels represented here • Some really NEED this knowledge (and may already have it) • Will help others UNDERSTAND their tech people ...
... – Basic understanding will help diagnose problems – Many skill levels represented here • Some really NEED this knowledge (and may already have it) • Will help others UNDERSTAND their tech people ...
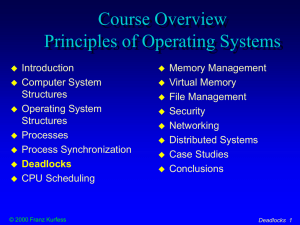
Deadlocks
... process holds a resource and waits to acquire other resources currently held by other processes the processes doesn’t release its current resources may be necessary, or a consequence of bad ...
... process holds a resource and waits to acquire other resources currently held by other processes the processes doesn’t release its current resources may be necessary, or a consequence of bad ...
Chaps_1-13_v5.0
... The system administrators have privileges on all the UNIX systems beyond that of any user. They can do anything to any of the systems or the network. Setting up a complex UNIX networking environment requires more technical knowledge and sophistication than an equivalent Windows environment (which is ...
... The system administrators have privileges on all the UNIX systems beyond that of any user. They can do anything to any of the systems or the network. Setting up a complex UNIX networking environment requires more technical knowledge and sophistication than an equivalent Windows environment (which is ...
Operating Systems: Internals and Design Principles (2
... This book is about the concepts, structure, and mechanisms of operating systems. Its purpose is to present, as clearly and completely as possible, the nature and characteristics of modern-day operating systems. This task is challenging for several reasons. First, there is a tremendous range and vari ...
... This book is about the concepts, structure, and mechanisms of operating systems. Its purpose is to present, as clearly and completely as possible, the nature and characteristics of modern-day operating systems. This task is challenging for several reasons. First, there is a tremendous range and vari ...
Installation and Configuration Guide for Linux
... To upgrade the software without updating the hardware or OS: 1 Install the DKU and the AJA OEM-2K firmware (page 25) 2 Upgrade projects to the current version (page 41) Unnecessary if you are upgrading to a service pack of the same application version or to a service pack of the same extension. 3 Li ...
... To upgrade the software without updating the hardware or OS: 1 Install the DKU and the AJA OEM-2K firmware (page 25) 2 Upgrade projects to the current version (page 41) Unnecessary if you are upgrading to a service pack of the same application version or to a service pack of the same extension. 3 Li ...
Deadlocks
... Release any resource already being held if the process can't get an additional resource. b) Allow preemption - if a needed resource is held by another process, which is also waiting on some resource, steal it. Otherwise wait. Circular wait: a) Number resources and only request in ascending order. b) ...
... Release any resource already being held if the process can't get an additional resource. b) Allow preemption - if a needed resource is held by another process, which is also waiting on some resource, steal it. Otherwise wait. Circular wait: a) Number resources and only request in ascending order. b) ...
a High-performance Endsystem Architecture for Real
... work to date focuses on them. Consequently, while the architectural features and optimizations discussed in this paper are applicable to soft real-time systems, (including constrained latency multimedia systems), most of the discussion centers on hard real-time systems. This paper is organized as fo ...
... work to date focuses on them. Consequently, while the architectural features and optimizations discussed in this paper are applicable to soft real-time systems, (including constrained latency multimedia systems), most of the discussion centers on hard real-time systems. This paper is organized as fo ...