Chap-2-Architecture
... – Can be moved from one place to another – It considers even directories and devices as a single file system The Process is an entity, name given to a file wen its executed as a program – IT also belongs to a separate hierarchical tree structure ...
... – Can be moved from one place to another – It considers even directories and devices as a single file system The Process is an entity, name given to a file wen its executed as a program – IT also belongs to a separate hierarchical tree structure ...
Overview and History
... uses many tools developed as part of Berkeley’s BSD operating system, MIT’s X Window System, and the Free Software Foundation's GNU project Linux kernel is distributed under the GNU General Public License (GPL): free to modify code but cannot make proprietary; also must distribute source code ...
... uses many tools developed as part of Berkeley’s BSD operating system, MIT’s X Window System, and the Free Software Foundation's GNU project Linux kernel is distributed under the GNU General Public License (GPL): free to modify code but cannot make proprietary; also must distribute source code ...
L03_Processes
... A sequentially executing piece of code that runs on one processing unit of the system An asynchronous computational activity (i.e., it proceeds at its own pace, independent of another process) The locus of control of a program in execution A process is: ...
... A sequentially executing piece of code that runs on one processing unit of the system An asynchronous computational activity (i.e., it proceeds at its own pace, independent of another process) The locus of control of a program in execution A process is: ...
Operating System 10CS53 Executing and Loading User Programs
... The shared-memory object acts as a backing store for shared-memory regions in the same way as a file can act as backing store for a memory-mapped memory region ...
... The shared-memory object acts as a backing store for shared-memory regions in the same way as a file can act as backing store for a memory-mapped memory region ...
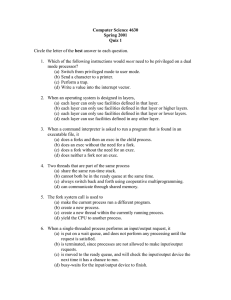
Computer Science 4630 - Department of Computer Science
... (b) cannot both be in the ready queue at the same time. (c) always switch back and forth using cooperative multiprogramming. (d) can communicate through shared memory. 5. The fork system call is used to (a) make the current process run a different program. (b) create a new process. (c) create a new ...
... (b) cannot both be in the ready queue at the same time. (c) always switch back and forth using cooperative multiprogramming. (d) can communicate through shared memory. 5. The fork system call is used to (a) make the current process run a different program. (b) create a new process. (c) create a new ...
Traditional UNIX kernels
... UNIX was taken to University of California Berkley leading to the foundation of the Berkeley Standard Distribution UNIX then opened up the computer industry to many other UNIX type operating systems and more To date, Apple MAC OS X is the most widely used desktop version of UNIX ...
... UNIX was taken to University of California Berkley leading to the foundation of the Berkeley Standard Distribution UNIX then opened up the computer industry to many other UNIX type operating systems and more To date, Apple MAC OS X is the most widely used desktop version of UNIX ...
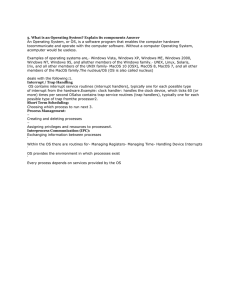
5. What is an Operating System? Explain its components Answer An
... Process Stack (SP) which typically contains temporary data such as subroutine parameter,return address, and temporary variables.· A data section that contains global variables In Process model, all software on the computer isorganized into a number of sequential processes. A process includes PC, reg ...
... Process Stack (SP) which typically contains temporary data such as subroutine parameter,return address, and temporary variables.· A data section that contains global variables In Process model, all software on the computer isorganized into a number of sequential processes. A process includes PC, reg ...
lecture notes
... may set a timer to ensure a process does not run beyond its allotted time To avoid infinite loops, memory ...
... may set a timer to ensure a process does not run beyond its allotted time To avoid infinite loops, memory ...
Overview and History
... uses many tools developed as part of Berkeley’s BSD operating system, MIT’s X Window System, and the Free Software Foundation's GNU project Linux kernel is distributed under the GNU General Public License (GPL): free to modify code but cannot make proprietary; also must distribute source code ...
... uses many tools developed as part of Berkeley’s BSD operating system, MIT’s X Window System, and the Free Software Foundation's GNU project Linux kernel is distributed under the GNU General Public License (GPL): free to modify code but cannot make proprietary; also must distribute source code ...
Answers
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. We will have an in-class discussion on these exercises on 1/23. 1. Who are the two main programmers that wrote UNIX, and what were their r ...
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. We will have an in-class discussion on these exercises on 1/23. 1. Who are the two main programmers that wrote UNIX, and what were their r ...
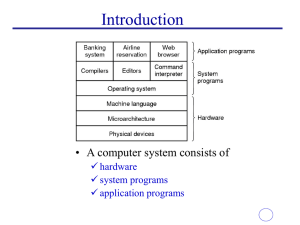
What is an operating system?
... • Two modes of process execution: user mode and kernel mode • Normally, a process executes in the user mode. When a process executes a system call, the mode of execution changes from user mode to kernel mode. The bookkeeping operations related to the user process (interrupt handling, process schedul ...
... • Two modes of process execution: user mode and kernel mode • Normally, a process executes in the user mode. When a process executes a system call, the mode of execution changes from user mode to kernel mode. The bookkeeping operations related to the user process (interrupt handling, process schedul ...
Chapter 2 Operating System Overview
... to communicate via RPCs • Provides base for distributed computing ...
... to communicate via RPCs • Provides base for distributed computing ...
Answers
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. 1. Who are the two main programmers that wrote UNIX, and what were their roles? Dennis Ritchie – primary inventor of the C language, co-in ...
... Note: At this point, these exercises do not have to be turned in. The point of the exercises is to help you reflect on and better understand the course material. 1. Who are the two main programmers that wrote UNIX, and what were their roles? Dennis Ritchie – primary inventor of the C language, co-in ...
Homework 1 Solutions
... write() is a system call, while fprintf() is a library function. This fact can lead to major differences in the process which is triggered on either of the above calls. When write() is called, a trap is always made to kernel mode and the output is written without delay. On the other hand, fprintf() ...
... write() is a system call, while fprintf() is a library function. This fact can lead to major differences in the process which is triggered on either of the above calls. When write() is called, a trap is always made to kernel mode and the output is written without delay. On the other hand, fprintf() ...
The Contiki Operating System
... Event occurs: kernel Kernel invokes event handler Event handler runs to completion ...
... Event occurs: kernel Kernel invokes event handler Event handler runs to completion ...
Mid1_Revision
... minimal functions in the kernel and implement higher level OS features in other modules (running either in user mode or kernel mode). As monolithic kernel if it can be made bug free can on average perform better than a microkernel system that has some additional communication overhead between compon ...
... minimal functions in the kernel and implement higher level OS features in other modules (running either in user mode or kernel mode). As monolithic kernel if it can be made bug free can on average perform better than a microkernel system that has some additional communication overhead between compon ...
Unix – Linux
... and users of a computer. – Requires a file system for organizing files – Must maintain its viability to prevent other programs, hardware, users, etc, from impeding its operation. Unix and its variants will accomplish the above. ...
... and users of a computer. – Requires a file system for organizing files – Must maintain its viability to prevent other programs, hardware, users, etc, from impeding its operation. Unix and its variants will accomplish the above. ...
[Lecture 1, part 3] Kernel interaction with the hardware: Interrupt
... [Lecture 1, part 3] Kernel interaction with the hardware: Interrupt: Like input / output, user input, between kernel and device driver. Devices call back by interrupts. They are serviced immediately. And they are user transparent. Implementation: Each device only has limited number of interrupt even ...
... [Lecture 1, part 3] Kernel interaction with the hardware: Interrupt: Like input / output, user input, between kernel and device driver. Devices call back by interrupts. They are serviced immediately. And they are user transparent. Implementation: Each device only has limited number of interrupt even ...
The UNIX Operating System - Niagara College Technology
... Each UNIX command can get its input from any data source and send its output to any data destination. ...
... Each UNIX command can get its input from any data source and send its output to any data destination. ...
Assignment 1 Solution
... simultaneously. This situation can result in various security problems. a. What are two such problems? b. Can we ensure the same degree of security in a time-shared machine as we have in a dedicated machine? Explain your answer. a. Stealing or copying one’s programs or data; using system resources ( ...
... simultaneously. This situation can result in various security problems. a. What are two such problems? b. Can we ensure the same degree of security in a time-shared machine as we have in a dedicated machine? Explain your answer. a. Stealing or copying one’s programs or data; using system resources ( ...



![[Lecture 1, part 3] Kernel interaction with the hardware: Interrupt](http://s1.studyres.com/store/data/014183875_1-7af0f6b03bedcfbf8972c6054b446a98-300x300.png)