LECT03
... o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several jobs executing simultaneously is created ...
... o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several jobs executing simultaneously is created ...
Lecture 3 - The College of New Jersey
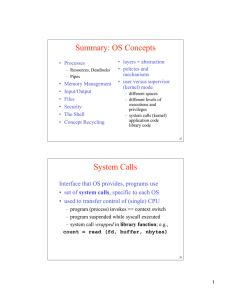
... operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between processes executing either on the same computer or on different systems tied toge ...
... operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between processes executing either on the same computer or on different systems tied toge ...
I/O subsystem
... which separates the rest of the kernel from the complexities of managing I/O devices. To encapsulate the details and oddities of different ...
... which separates the rest of the kernel from the complexities of managing I/O devices. To encapsulate the details and oddities of different ...
Introduction and Overview - William & Mary Computer Science
... • use a hardware timer that generates a periodic interrupt • before it transfers to a user program, the OS loads the timer with a time to interrupt – “quantum” – how big should it be set? ...
... • use a hardware timer that generates a periodic interrupt • before it transfers to a user program, the OS loads the timer with a time to interrupt – “quantum” – how big should it be set? ...
Introduction to Unix
... Handles the communication between the terminal and the server (main computer). You also need a “windows manager” to handle how the windows will look on your computer. ...
... Handles the communication between the terminal and the server (main computer). You also need a “windows manager” to handle how the windows will look on your computer. ...
Evolution of Operating System
... o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several jobs executing simultaneously is created ...
... o At end of time slice current job is set aside and a new one starts o By rapidly shuffling jobs, illusion of several jobs executing simultaneously is created ...
ppt
... Runs most of the operating system services at the user space. Parts that require privilege (IPC, etc) are in kernel mode and other critical parts (FS, Network Stack) in user mode. Example: L4 microkernel Performance issue ! ...
... Runs most of the operating system services at the user space. Parts that require privilege (IPC, etc) are in kernel mode and other critical parts (FS, Network Stack) in user mode. Example: L4 microkernel Performance issue ! ...
Replication, Load-balancing, and QoS
... Kernel can give the process fewer bytes, user process must check the byteCount to see how ...
... Kernel can give the process fewer bytes, user process must check the byteCount to see how ...
01-intro
... Write, compile, debug, and execute C programs that correctly use system interfaces provided by UNIX (or a UNIXlike operating system). ...
... Write, compile, debug, and execute C programs that correctly use system interfaces provided by UNIX (or a UNIXlike operating system). ...
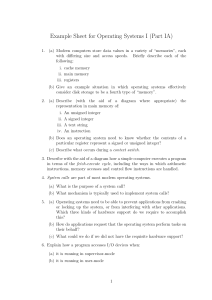
Example Sheet for Operating Systems I (Part IA)
... snapshot to the new one. However to save disk space, hardlinks are used in place of actual copies. Once the ‘copy’ is complete, the new snapshot is used as the new root. To what extent will this scheme provide the functionality the system administrator hopes for? What advantages and disadvantages do ...
... snapshot to the new one. However to save disk space, hardlinks are used in place of actual copies. Once the ‘copy’ is complete, the new snapshot is used as the new root. To what extent will this scheme provide the functionality the system administrator hopes for? What advantages and disadvantages do ...
Summary: OS Concepts System Calls
... Exokernels - similar to VM, but split machine resources (e.g., disk portions) – saves one mapping layer (e.g., disk addresses) ...
... Exokernels - similar to VM, but split machine resources (e.g., disk portions) – saves one mapping layer (e.g., disk addresses) ...
History of UNIX a short version
... The spread of UNIX In 1974, Ritchie and Thompson published a paper about UNIX Many universities were interested AT&T licensed UNIX for a modest fee Releases were distributed as C source code By 1977, more than 500 sites (125 universities) were running UNIX ...
... The spread of UNIX In 1974, Ritchie and Thompson published a paper about UNIX Many universities were interested AT&T licensed UNIX for a modest fee Releases were distributed as C source code By 1977, more than 500 sites (125 universities) were running UNIX ...
CIS 721 - Lecture 1
... • A UNIX command file doesn’t need to have a special extension like .exe and .com. • There’s hardly a practical restriction on length either; a command can be up to 255 characters long – a limit set for any file of the file system. • UNIX is sensitive to case. ...
... • A UNIX command file doesn’t need to have a special extension like .exe and .com. • There’s hardly a practical restriction on length either; a command can be up to 255 characters long – a limit set for any file of the file system. • UNIX is sensitive to case. ...
Virtual Memory Systems
... The _________short term scheduler_________ in an Operating System attempts to select a new process, switch to it quickly and start running it on the CPU. ...
... The _________short term scheduler_________ in an Operating System attempts to select a new process, switch to it quickly and start running it on the CPU. ...
Chapter 3: System Software
... Copy files Move files System/file backup Rename files Erase files ...
... Copy files Move files System/file backup Rename files Erase files ...
EECE 432– Operating Systems
... a) Three 50-minute lectures per week or two 75 minutes per weel. b) Use of computer lab or personal computer is needed for working on the projects. Course outcomes: At the end of the course students should be able to: 1. Understand operating system concepts. 2. Read and understand kernel code. 3. Bu ...
... a) Three 50-minute lectures per week or two 75 minutes per weel. b) Use of computer lab or personal computer is needed for working on the projects. Course outcomes: At the end of the course students should be able to: 1. Understand operating system concepts. 2. Read and understand kernel code. 3. Bu ...
installing debian
... • Not officially allowed. The University only wants .liu.edu names for machines in the University network. And of course they own the domain and operate the server. • Nevertheless, I could demonstrate how this could work. • Probably next week . ...
... • Not officially allowed. The University only wants .liu.edu names for machines in the University network. And of course they own the domain and operate the server. • Nevertheless, I could demonstrate how this could work. • Probably next week . ...
lecture1
... the kernel. Some older operating systems had a rendezvous style of providing these services - the process would request a service and wait at a particular point, until a kernel task came along and serviced the request on behalf of the process. UNIX works very differently. Rather than having kernel t ...
... the kernel. Some older operating systems had a rendezvous style of providing these services - the process would request a service and wait at a particular point, until a kernel task came along and serviced the request on behalf of the process. UNIX works very differently. Rather than having kernel t ...