I/O Kit Drivers for L4
... I/O Kit is an integral component. Microkernel research has gone a long way since Mach was originally designed, and the Darwin system could stand to gain considerable performance improvements if it were ported to L4, a modern, state-of-the-art microkernel. On-going work is being made to port the BSD ...
... I/O Kit is an integral component. Microkernel research has gone a long way since Mach was originally designed, and the Darwin system could stand to gain considerable performance improvements if it were ported to L4, a modern, state-of-the-art microkernel. On-going work is being made to port the BSD ...
Open MP
... A process is created by an operating system contains information about resources process id, file descriptors, ... contains information on the execution state program counter, stack, ... ...
... A process is created by an operating system contains information about resources process id, file descriptors, ... contains information on the execution state program counter, stack, ... ...
Deadlocks
... b) Shared entities (read only files) don't need mutual exclusion (and aren’t susceptible to deadlock.) c) Prevention not possible, since some devices are intrinsically non-sharable. Hold and wait: a) Collect all resources before execution. b) A particular resource can only be requested when no other ...
... b) Shared entities (read only files) don't need mutual exclusion (and aren’t susceptible to deadlock.) c) Prevention not possible, since some devices are intrinsically non-sharable. Hold and wait: a) Collect all resources before execution. b) A particular resource can only be requested when no other ...
3. Implemented Operating System
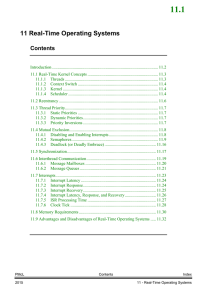
... relevant for this text: (i) task management and scheduling, (ii) (deferred) interrupt servicing, (iii) inter-process communication and synchronization, and (iv) memory management. General-purpose operating systems also have other responsibilities, which are beyond the scope of a real-time operating ...
... relevant for this text: (i) task management and scheduling, (ii) (deferred) interrupt servicing, (iii) inter-process communication and synchronization, and (iv) memory management. General-purpose operating systems also have other responsibilities, which are beyond the scope of a real-time operating ...
On the construction of operating systems for the - UvA-DARE
... machine on April 19th, 1988, I was 8 years old at the time, and I still have memories of sitting in the back of our car with a pile of big boxes. I am convinced that this was a turning point in my life, as without this machine, I would not have ended up where I am today; completing my PhD thesis on ...
... machine on April 19th, 1988, I was 8 years old at the time, and I still have memories of sitting in the back of our car with a pile of big boxes. I am convinced that this was a turning point in my life, as without this machine, I would not have ended up where I am today; completing my PhD thesis on ...
CodeMoctules O O O
... including a partition operating system and a partition user application. The method further includes generating an alarm in one of the partition protection domains; transmit ting the alarm to the core operating system via the partition operating system in said one of the partitions; accessing an ala ...
... including a partition operating system and a partition user application. The method further includes generating an alarm in one of the partition protection domains; transmit ting the alarm to the core operating system via the partition operating system in said one of the partitions; accessing an ala ...
multi-threading
... a processor. It is maintained in this state until the processor is ready (eventually, after preempting current thread). Running: This is the active thread. Its execution ends if it terminates, it is blocked, preempted or its time slice expires. Waiting: This is a thread waiting for I/O operation ...
... a processor. It is maintained in this state until the processor is ready (eventually, after preempting current thread). Running: This is the active thread. Its execution ends if it terminates, it is blocked, preempted or its time slice expires. Waiting: This is a thread waiting for I/O operation ...
Course ”Operating System Security”
... Most software is benign, whether it is written by a good or an incompetent programmer Software is often not trusted, because it is not responsible for enforcing security of the system In environments with extremely sensitive information the benign and malicious software are assigned to a single grou ...
... Most software is benign, whether it is written by a good or an incompetent programmer Software is often not trusted, because it is not responsible for enforcing security of the system In environments with extremely sensitive information the benign and malicious software are assigned to a single grou ...
FreeBSD for the Linux user
... • FreeBSD consists of all the components needed for a complete operating system ...
... • FreeBSD consists of all the components needed for a complete operating system ...
Operating Systems Concepts with Java
... character or a block of characters at a time. Some can be accessed only sequentially, others randomly. Some transfer data synchronously, others asynchronously. Some are dedicated, some shared. They can be read-only or read-write. they vary greatly in speed. In many ways they are also the slowest maj ...
... character or a block of characters at a time. Some can be accessed only sequentially, others randomly. Some transfer data synchronously, others asynchronously. Some are dedicated, some shared. They can be read-only or read-write. they vary greatly in speed. In many ways they are also the slowest maj ...
A Virtual Machine Introspection Based Architecture for Intrusion
... have sought to make user-level IDSes more attack resistant through “stealth,” i.e. by hiding the IDS using techniques similar to those used by attackers to hide their exploits, such as hiding IDS processes by modifying kernel structures and masking the presence of IDS files through the use of stegan ...
... have sought to make user-level IDSes more attack resistant through “stealth,” i.e. by hiding the IDS using techniques similar to those used by attackers to hide their exploits, such as hiding IDS processes by modifying kernel structures and masking the presence of IDS files through the use of stegan ...
Operating System
... Computers are widely employed in almost all the activities of today’s modern man. They are used by people of all ages in a variety of environments. We recognize the computer as a set of devices, such as the main case, monitor, keyboard, mouse, etc., collectively called the hardware. In one session’s ...
... Computers are widely employed in almost all the activities of today’s modern man. They are used by people of all ages in a variety of environments. We recognize the computer as a set of devices, such as the main case, monitor, keyboard, mouse, etc., collectively called the hardware. In one session’s ...
OperatingSystems_FA15_5_Scheduling
... In Short term scheduling, predict the next CPU burst value. Preemptive SJF takes CPU when arrived process burst time is less than the remaining time of current process. NonPreemptive SJF allows current process to complete burst time before scheduling next process based on burst time. Length of CPU b ...
... In Short term scheduling, predict the next CPU burst value. Preemptive SJF takes CPU when arrived process burst time is less than the remaining time of current process. NonPreemptive SJF allows current process to complete burst time before scheduling next process based on burst time. Length of CPU b ...
Chapter 4: Threads
... other threads vanish in the child. No thread-specific data destructors or cleanup handlers are executed. Problems: The global data may be inconsistent: ...
... other threads vanish in the child. No thread-specific data destructors or cleanup handlers are executed. Problems: The global data may be inconsistent: ...
Module 7: Process Synchronization
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
a. Real Time Operating Systems Notes
... using 8, 16, or 32 bits, respectively. The actual size depends on the kernel used. Along with the semaphore's value, the kernel also needs to keep track of threads waiting for the semaphore's availability. Generally, only three operations can be performed on a semaphore: Create(), Wait(), and Signal ...
... using 8, 16, or 32 bits, respectively. The actual size depends on the kernel used. Along with the semaphore's value, the kernel also needs to keep track of threads waiting for the semaphore's availability. Generally, only three operations can be performed on a semaphore: Create(), Wait(), and Signal ...
The Spring Kernel: A New Paradigm for Real
... modifications to our previously reported work have been made for implementing distributed scheduling on SpringNet. Most notably, the code for tasks is now replicated at various nodes, so tt~at (~nlv signals, partial state informatinn, or input to the tasks need be transmitted when distributed schedu ...
... modifications to our previously reported work have been made for implementing distributed scheduling on SpringNet. Most notably, the code for tasks is now replicated at various nodes, so tt~at (~nlv signals, partial state informatinn, or input to the tasks need be transmitted when distributed schedu ...
Multics
... bid in 1963. Folklore has it that IBM was not interested in Project MAC’s ideas for paging and segmentation, so instead General Electric (GE) was chosen to build the hardware for the project, the eventual GE 645. Bell Labs joined the software development in 1965. The Multics project had very ambitio ...
... bid in 1963. Folklore has it that IBM was not interested in Project MAC’s ideas for paging and segmentation, so instead General Electric (GE) was chosen to build the hardware for the project, the eventual GE 645. Bell Labs joined the software development in 1965. The Multics project had very ambitio ...
Electrical Engineering and Computer Science Department Technical
... hybrid runtimes (HRTs), runtimes that run as kernels, and that enjoy full hardware access and control over abstractions to the machine. The primary claim of this dissertation is that the hybrid runtime model can provide significant benefits to parallel runtimes and the applications that run on top ...
... hybrid runtimes (HRTs), runtimes that run as kernels, and that enjoy full hardware access and control over abstractions to the machine. The primary claim of this dissertation is that the hybrid runtime model can provide significant benefits to parallel runtimes and the applications that run on top ...
Module 7: Process Synchronization
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
9 th Edition
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
Dancing with Giants: Wimpy Kernels for On-demand Isolated I/O
... Central to on-demand isolation of I/O channels is the notion of the wimpy kernel, which constructs these channels without affecting the underlying TCB; i.e., without modifying its security properties and increasing the verification effort [39, 66]. The wimpy kernel is an add-on trustworthy service t ...
... Central to on-demand isolation of I/O channels is the notion of the wimpy kernel, which constructs these channels without affecting the underlying TCB; i.e., without modifying its security properties and increasing the verification effort [39, 66]. The wimpy kernel is an add-on trustworthy service t ...
Vulnerability Detection in Device Drivers
... experiments also revealed a potential implementation problem of the TCP-IP stack by the use of disassociation frames when the target device was associated and authenticated with a Wi-Fi access point. Next, we developed a tool capable of registering and instrumenting the interactions between a DD and ...
... experiments also revealed a potential implementation problem of the TCP-IP stack by the use of disassociation frames when the target device was associated and authenticated with a Wi-Fi access point. Next, we developed a tool capable of registering and instrumenting the interactions between a DD and ...
deadlocks - Mohamed Nafas
... b) Shared entities (read only files) don't need mutual exclusion (and aren’t susceptible to deadlock.) c) Prevention not possible, since some devices are intrinsically non-sharable. Hold and wait: a) Collect all resources before execution. b) A particular resource can only be requested when no other ...
... b) Shared entities (read only files) don't need mutual exclusion (and aren’t susceptible to deadlock.) c) Prevention not possible, since some devices are intrinsically non-sharable. Hold and wait: a) Collect all resources before execution. b) A particular resource can only be requested when no other ...
Document
... Solution to Critical-Section Problem • Design a protocol such that each process must request permission to enter its critical section • The section of code implementing this request is the entry section ...
... Solution to Critical-Section Problem • Design a protocol such that each process must request permission to enter its critical section • The section of code implementing this request is the entry section ...