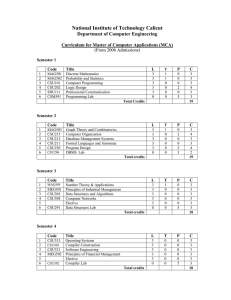
National Institute of Technology Calicut
... PLAs, .PLA minimization, PLA folding, design for testability, Counters and shift registers: excitation tables, ripple counters, synchronous counters, up-down counters, design of sequential circuits, shift registers and their applications. Clock mode sequential machines. Module III (11 + 10 Hours) Mi ...
... PLAs, .PLA minimization, PLA folding, design for testability, Counters and shift registers: excitation tables, ripple counters, synchronous counters, up-down counters, design of sequential circuits, shift registers and their applications. Clock mode sequential machines. Module III (11 + 10 Hours) Mi ...
No Slide Title
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash. The log is stored in the third metadata file at the beginning of the ...
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash. The log is stored in the third metadata file at the beginning of the ...
ch22
... select any entry in the page directory, or in a page table This property is used when translating a virtual address pointer to a bye address in physical memory A page can be in one of six states: valid, zeroed, free standby, modified and bad ...
... select any entry in the page directory, or in a page table This property is used when translating a virtual address pointer to a bye address in physical memory A page can be in one of six states: valid, zeroed, free standby, modified and bad ...
No Slide Title
... interrupts are generated by hardware of software. Exceptions that cannot be handled by the trap handler are handled by the kernel's exception dispatcher. The interrupt dispatcher in the kernel handles interrupts by calling either an interrupt service routine (such as in a device driver) or an in ...
... interrupts are generated by hardware of software. Exceptions that cannot be handled by the trap handler are handled by the kernel's exception dispatcher. The interrupt dispatcher in the kernel handles interrupts by calling either an interrupt service routine (such as in a device driver) or an in ...
ch22
... manger supervises the use of all the objects. Generates an object handle Checks security. ...
... manger supervises the use of all the objects. Generates an object handle Checks security. ...
Chapter 3 Operating-System Structures 2
... Networking (Distributed Systems) • A distributed system is a collection processors that do not share memory or a clock. Each processor has its own local memory. • The processors in the system are connected through a communication network. • A distributed system provides user access to various syste ...
... Networking (Distributed Systems) • A distributed system is a collection processors that do not share memory or a clock. Each processor has its own local memory. • The processors in the system are connected through a communication network. • A distributed system provides user access to various syste ...
6-up pdf
... Windows 95 peer networking and Windows for Workgroups; used when XP wants to share resources with these networks operating systems and hardware platforms PPTP (Point-to-Point Tunneling Protocol) is used to communicate ...
... Windows 95 peer networking and Windows for Workgroups; used when XP wants to share resources with these networks operating systems and hardware platforms PPTP (Point-to-Point Tunneling Protocol) is used to communicate ...
ch21
... name, which may be either permanent or temporary. Object names are structured like file path names in MSDOS and UNIX. 2000 implements a symbolic link object, which is similar to symbolic links in UNIX that allow multiple nicknames or aliases to refer to the same file. A process gets an object handle ...
... name, which may be either permanent or temporary. Object names are structured like file path names in MSDOS and UNIX. 2000 implements a symbolic link object, which is similar to symbolic links in UNIX that allow multiple nicknames or aliases to refer to the same file. A process gets an object handle ...
Windows 2000
... name, which may be either permanent or temporary. Object names are structured like file path names in MSDOS and UNIX. 2000 implements a symbolic link object, which is similar to symbolic links in UNIX that allow multiple nicknames or aliases to refer to the same file. A process gets an object handle ...
... name, which may be either permanent or temporary. Object names are structured like file path names in MSDOS and UNIX. 2000 implements a symbolic link object, which is similar to symbolic links in UNIX that allow multiple nicknames or aliases to refer to the same file. A process gets an object handle ...
Lecture4
... If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
... If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
2.01 - Czech Technical University in Prague
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
Chapter 2: Operating
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
Operating-System Structures
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
2.01 - Tamkang University
... Although MS-DOS has some structure, its interfaces and levels of functionality are not well separated ...
... Although MS-DOS has some structure, its interfaces and levels of functionality are not well separated ...
Operating-System Structures
... control use of that information, concurrent processes should not interfere with each other Protection involves ensuring that all access to system resources is controlled Security of the system from outsiders requires user ...
... control use of that information, concurrent processes should not interfere with each other Protection involves ensuring that all access to system resources is controlled Security of the system from outsiders requires user ...
Module 3: Operating
... small to accommodate all data and programs permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following act ...
... small to accommodate all data and programs permanently, the computer system must provide secondary storage to back up main memory. Most modern computer systems use disks as the principle on-line storage medium, for both programs and data. The operating system is responsible for the following act ...
Chapter 2: Operating-System Structures
... If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
... If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
Operating-System Structures Chapter 2
... Most usersʼ view of the operation system is defined by system ...
... Most usersʼ view of the operation system is defined by system ...
Porting a SAS/AF Application from PC to a MAC
... and data sets are moved from the PC to the Macintosh. As changes are made to the master copy, the associated catalogs need to be ported over to the Macintosh. The porting tool provides us a pointand-click interface to select the catalog entries to transport, the final location of the transport file ...
... and data sets are moved from the PC to the Macintosh. As changes are made to the master copy, the associated catalogs need to be ported over to the Macintosh. The porting tool provides us a pointand-click interface to select the catalog entries to transport, the final location of the transport file ...
No Slide Title
... compression units, which are blocks of 16 contiguous clusters. For sparse files, NTFS uses another technique to save space. – Clusters that contain all zeros are not actually allocated or stored on disk. – Instead, gaps are left in the sequence of virtual cluster numbers stored in the MFT entry for ...
... compression units, which are blocks of 16 contiguous clusters. For sparse files, NTFS uses another technique to save space. – Clusters that contain all zeros are not actually allocated or stored on disk. – Instead, gaps are left in the sequence of virtual cluster numbers stored in the MFT entry for ...
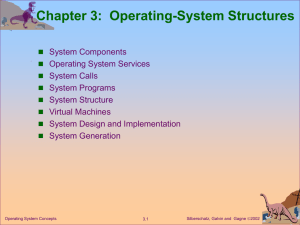
Chap3
... – Systems programs – The kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a ...
... – Systems programs – The kernel Consists of everything below the system-call interface and above the physical hardware Provides the file system, CPU scheduling, memory management, and other operating-system functions; a ...
Chapter 2: Operating
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
2.01
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
System Call
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...
... resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. A virtual-machine system is a perfect vehicle for operating-systems ...