* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download lecture6.1
Survey
Document related concepts
Wiles's proof of Fermat's Last Theorem wikipedia , lookup
Foundations of mathematics wikipedia , lookup
Model theory wikipedia , lookup
Principia Mathematica wikipedia , lookup
Proofs of Fermat's little theorem wikipedia , lookup
List of first-order theories wikipedia , lookup
Mathematics of radio engineering wikipedia , lookup
List of prime numbers wikipedia , lookup
Topological quantum field theory wikipedia , lookup
List of important publications in mathematics wikipedia , lookup
Transcript
Lecture 6.1: Misc. Topics:
Number Theory
CS 250, Discrete Structures, Fall 2011
Nitesh Saxena
Course Admin -- Homework 5
Due at 11am this Wednesday
Covers the chapter on Graphs (lecture 5.*)
Has a 10-pointer bonus problem too
Please submit on time
Lecture 6.1 -- Number Theory
Course Admin -- Homework 4
Grades posted on BB
Distributing today
Solution posted
Lecture 6.1 -- Number Theory
Course Admin -- Final Exam
Thursday, December 8, 10:45am1:15pm, lecture room
Heads up!
Please mark the date/time/place
Emphasis on post mid-term 2 material
Coverage:
65% post mid-term 2 (lectures 4.*, 5.*, 6.*), and
35% pre mid-term 2 (lecture 1.*. 2.* and 3.*)
Our last lecture will be on December 6
We plan to do a final exam review then
Lecture 6.1 -- Number Theory
Outline
Number Theory
Modular Arithmetic
Application -- cryptography
Lecture 6.1 -- Number Theory
Divisors
x divides y (written x | y) if the remainder is 0
when y is divided by x
1|8, 2|8, 4|8, 8|8
The divisors of y are the numbers that divide
y
divisors of 8: {1,2,4,8}
For every number y
1|y
y|y
Lecture 6.1 -- Number Theory
Prime numbers
A number is prime if its only divisors are 1
and itself:
2,3,5,7,11,13,17,19, …
Fundamental theorem of arithmetic:
For every number x, there is a unique set of
primes {p1, … ,pn} and a unique set of positive
exponents {e1, … ,en} such that
x p1
e1
* ... *
pn
en
How to prove? We studied it earlier!
Lecture 6.1 -- Number Theory
Common divisors
The common divisors of two numbers x,y are
the numbers z such that z|x and z|y
common divisors of 8 and 12:
intersection of {1,2,4,8} and {1,2,3,4,6,12}
= {1,2,4}
greatest common divisor: gcd(x,y) is the
number z such that
z is a common divisor of x and y
no common divisor of x and y is larger than z
gcd(8,12) = 4
Lecture 6.1 -- Number Theory
Recall: Recursive Functions: gcd
Euclid’s algorithm makes use of the fact that
gcd(x,y ) = gcd(y, x mod y)
x , if y 0
gcd( x , y )
gcd( y , x mod y ), otherwise
(here we assume that x > 0)
10/04/2011
Lecture 3.3 -- Recursion
9
Euclidean Algorithm: gcd(r0,r1)
Main idea: If y = ax + b then gcd(x,y) = gcd(x,b)
r0 q1r1 r2
r1 q2 r2 r3
...
rm 2 qm 1rm 1 rm
rm 1 qm rm 0
gcd(r0 , r1 ) gcd(r1 , r2 ) ... gcd(rm 1 , rm ) rm
Lecture 6.1 -- Number Theory
Example – gcd(15,37)
37 = 2 * 15 + 7
15 = 2 * 7 + 1
7=7*1+0
gcd(15,37) = 1
Lecture 6.1 -- Number Theory
Relative primes
x and y are relatively prime if they have no
common divisors, other than 1
Equivalently, x and y are relatively prime if
gcd(x,y) = 1
9 and 14 are relatively prime
9 and 15 are not relatively prime
Lecture 6.1 -- Number Theory
Modular Arithmetic
Definition: x is congruent to y mod m, if m
divides (x-y). Equivalently, x and y have the
same remainder when divided by m.
Notation: x y (mod m)
Example: 14 5(mod 9)
We work in Zm = {0, 1, 2, …, m-1}, the group
of integers modulo m
Example: Z9 ={0,1,2,3,4,5,6,7,8}
We abuse notation and often write = instead
of
Lecture 6.1 -- Number Theory
Addition in Zm :
Addition is well-defined:
if
x x' (mod m)
y y ' (mod m)
then
x y x' y ' (mod m)
3 + 4 = 7 mod 9.
3 + 8 = 2 mod 9.
Lecture 6.1 -- Number Theory
Additive inverses in Zm
0 is the additive identity in Zm
x 0 x(mod m) 0 x(mod m)
Additive inverse of a is -a mod m = (m-a)
Every element has unique additive inverse.
4 + 5= 0 mod 9.
4 is additive inverse of 5.
Lecture 6.1 -- Number Theory
Multiplication in Zm :
Multiplication is well-defined:
if
x x' (mod m)
y y ' (mod m)
then
x y x' y ' (mod m)
3 * 4 = 3 mod 9.
3 * 8 = 6 mod 9.
3 * 3 = 0 mod 9.
Lecture 6.1 -- Number Theory
Multiplicative inverses in Zm
1 is the multiplicative identity in Zm
x 1 x(mod m) 1 x(mod m)
Multiplicative inverse (x*x-1=1 mod m)
SOME, but not ALL elements have unique
multiplicative inverse.
In Z9 : 3*0=0, 3*1=3, 3*2=6, 3*3=0, 3*4=3,
3*5=6, …, so 3 does not have a multiplicative
inverse (mod 9)
On the other hand, 4*2=8, 4*3=3, 4*4=7,
4*5=2, 4*6=6, 4*7=1, so 4-1=7 (mod 9)
Lecture 6.1 -- Number Theory
Which numbers have inverses?
In Zm, x has a multiplicative inverse if and
only if x and m are relatively prime or
gcd(x,m)=1
E.g., 4 in Z9
Lecture 6.1 -- Number Theory
Extended Euclidian: a-1 mod n
Main Idea: Looking for inverse of a mod n means
looking for x such that x*a – y*n = 1.
To compute inverse of a mod n, do the following:
Compute gcd(a, n) using Euclidean algorithm.
Since a is relatively prime to m (else there will be no
inverse) gcd(a, n) = 1.
So you can obtain linear combination of rm and rm-1 that
yields 1.
Work backwards getting linear combination of ri and ri-1 that
yields 1.
When you get to linear combination of r0 and r1 you are
done as r0=n and r1= a.
Lecture 6.1 -- Number Theory
Example – 15-1 mod 37
37 = 2 * 15 + 7
15 = 2 * 7 + 1
7 = 7 * 1 + 0
Now,
15 – 2 * 7 = 1
15 – 2 (37 – 2 * 15) = 1
5 * 15 – 2 * 37 = 1
So, 15-1 mod 37 is 5.
Lecture 6.1 -- Number Theory
Modular Exponentiation:
Square and Multiply method
Usual approach to computing xc mod n is
inefficient when c is large.
Instead, represent c as bit string bk-1 … b0
and use the following algorithm:
z = 1
For i = k-1 downto 0 do
z = z2 mod n
if bi = 1 then z = z* x mod n
Lecture 6.1 -- Number Theory
Example: 3037 mod 77
z = z2 mod n
if bi = 1 then z = z* x mod n
i
b
z
5
1
30
=1*1*30 mod 77
4
0
53
=30*30 mod 77
3
0
37
=53*53 mod 77
2
1
29
=37*37*30 mod 77
1
0
71
=29*29 mod 77
0
1
2
=71*71*30 mod 77
Lecture 6.1 -- Number Theory
Euler’s totient function
Given positive integer n, Euler’s totient
function (n) is the number of positive
numbers less than n that are relatively prime
to n
Fact: If p is prime then ( p ) p 1
{1,2,3,…,p-1} are relatively prime to p.
Lecture 6.1 -- Number Theory
Euler’s totient function
Fact: If p and q are prime and n=pq then
(n) ( p 1)( q 1)
Each number that is not divisible by p or by q
is relatively prime to pq.
E.g. p=5, q=7: {1,2,3,4,-,6,-,8,9,-,11,12,13,-,,16,17,18,19,-,-,22,23,24,-,26,27,-,29,,31,32,33,34,-}
pq-p-(q-1) = (p-1)(q-1)
Lecture 6.1 -- Number Theory
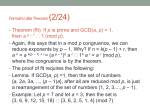
Euler’s Theorem and Fermat’s Theorem
If a is relatively prime to n then
a
(n)
1 mod n
If a is relatively prime to p then
ap-1 = 1 mod p
Proof : follows from a well-known theorem --
Lagrange’s Theorem (we won’t study in this
course)
Lecture 6.1 -- Number Theory
Euler’s Theorem and Fermat’s Theorem
EG: Compute 9100 mod 17:
p =17, so p-1 = 16. 100 = 6·16+4. Therefore,
9100=96·16+4=(916)6(9)4 . So mod 17 we have
9100 (916)6(9)4 (mod 17) (1)6(9)4 (mod 17)
(81)2 (mod 17) 16
Lecture 6.1 -- Number Theory
An Application of Number Theory
Cryptography: foundation of secure
communication. EX: Public-Key Cryptography
Lecture 6.1 -- Number Theory
RSA Crypto: Key Generation
Alice wants people to be able to send her encrypted
messages.
She chooses two (large) prime numbers, p and q and
computes n=pq and (n) . [“large” =512 bits +]
She chooses a number e such that e is relatively
prime to (n) and computes d, the inverse of
e in Z (n )
(i.e., ed =1 mod (n) )
She publicizes the pair (e,n) as her public key.(e is
called RSA exponent, n is called RSA modulus).
She keeps d secret and destroys p, q, and (n)
Plaintext and ciphertext messages are elements of Zn
and e is the encryption key.
Lecture 6.1 -- Number Theory
RSA: Encryption
Bob wants to send a message x (a number
relatively prime to n) to Alice.
He looks up her encryption key, (e,n), in a
directory.
The encrypted message is
y E ( x) x e mod n
Bob sends y to Alice.
Lecture 6.1 -- Number Theory
RSA: Decryption
To decrypt the message
y E ( x) x mod n
e
she’s received from Bob, Alice computes
D( y) y mod n
d
Claim: D(y) = x
Lecture 6.1 -- Number Theory
Why does it all work?
D( y ) y mod n
d
( x e mod n) d
( x ) mod n
e d
x ed mod n
x
t ( n ) 1
(x
mod n
Because ed 1 mod ( n)
(n) t
) x mod n
1 x mod n x mod n
t
From Euler’s Theorem
Lecture 6.1 -- Number Theory
Tiny RSA example.
Let p = 7, q = 11. Then n = 77 and
(n) 60
Choose e = 13. Then d = 13-1 mod 60 = 37.
Let message = 2.
E(2) = 213 mod 77 = 30.
D(30) = 3037 mod 77=2
Lecture 6.1 -- Number Theory
Today’s Reading
Rosen 4
Lecture 6.1 -- Number Theory