File
... paranoia, a complete nervous breakdown and more. This results in the change of behavior. Sometimes these changes are caused by real life danger to the victim and to his or her‘s loved ones. But where and how do you attract stalkers on the internet? Well you can pick up stalkers wherever you go on th ...
... paranoia, a complete nervous breakdown and more. This results in the change of behavior. Sometimes these changes are caused by real life danger to the victim and to his or her‘s loved ones. But where and how do you attract stalkers on the internet? Well you can pick up stalkers wherever you go on th ...
neutralizing credential theft and abuse
... First, the platform continuously builds out new intelligence against phishing websites with the Palo Alto Networks Threat Intelligence Cloud. Through automated threat intelligence, the protections in PAN-DB URL Filtering block the user’s attempts to reach a phishing site. In addition, the preventiv ...
... First, the platform continuously builds out new intelligence against phishing websites with the Palo Alto Networks Threat Intelligence Cloud. Through automated threat intelligence, the protections in PAN-DB URL Filtering block the user’s attempts to reach a phishing site. In addition, the preventiv ...
Essential Computer Concepts - MCST-CS
... PC and be able to use it. – Nonvolatile memory: it remains even if the computer turned off. • Complementary metal oxide semiconductor memory (CMOS): have a rechargeable battery and store the date and time. it changes every time you add or remove a hardware Semipermanent memory. Essential Computer Co ...
... PC and be able to use it. – Nonvolatile memory: it remains even if the computer turned off. • Complementary metal oxide semiconductor memory (CMOS): have a rechargeable battery and store the date and time. it changes every time you add or remove a hardware Semipermanent memory. Essential Computer Co ...
secure operating system
... A secure operating system is an operating system where its access enforcement satisfies the reference monitor concept The reference monitor concept defines the necessary and sufficient properties of any system that securely enforces a mandatory protection system, consisting of three guarantees: 1. C ...
... A secure operating system is an operating system where its access enforcement satisfies the reference monitor concept The reference monitor concept defines the necessary and sufficient properties of any system that securely enforces a mandatory protection system, consisting of three guarantees: 1. C ...
What is Beta Testing? - KV Institute of Management and Information
... Employees may use e-mail messages to transmit valuable trade secrets, financial data or confidential customer information to unauthorized recipients. ...
... Employees may use e-mail messages to transmit valuable trade secrets, financial data or confidential customer information to unauthorized recipients. ...
PowerPoint Slides
... Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
... Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
GCE Holding AB
... GCE Holding AB is Europe's leading company in the field of gas-control equipment. In addition to its headquarters in Malmö, Sweden, and main production site in Chotebor, Czech Republic, the company operates 15 international sales companies around the world. GCE has 4 business areas—cutting and weldi ...
... GCE Holding AB is Europe's leading company in the field of gas-control equipment. In addition to its headquarters in Malmö, Sweden, and main production site in Chotebor, Czech Republic, the company operates 15 international sales companies around the world. GCE has 4 business areas—cutting and weldi ...
Computer Security, Ethics, and Privacy
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? ...
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? ...
Protection & Security
... • Each file has associated with it a domain bit (setuid bit). • When file is executed and setuid = on, then user-id is set to owner of the file being executed. When execution completes user-id is reset. ...
... • Each file has associated with it a domain bit (setuid bit). • When file is executed and setuid = on, then user-id is set to owner of the file being executed. When execution completes user-id is reset. ...
Discovering Computers Fundamentals 4th Edition
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? ...
... Hardware Theft and Vandalism What are hardware theft and hardware vandalism? ...
NS2-M3C22S1_-_Computers_and_the_Internet
... A computer is a device that can carry out a finite set of arithmetic or logical instructions. The electronic digital computer always contains a central processing unit(CPU) and some form of memory. It may also have other internal components, and/or peripheral devices which are attached either wirele ...
... A computer is a device that can carry out a finite set of arithmetic or logical instructions. The electronic digital computer always contains a central processing unit(CPU) and some form of memory. It may also have other internal components, and/or peripheral devices which are attached either wirele ...
MYDIGIPASS for Healthcare
... 2015-2017 milestone of 65% of health care organizations permit patient access to patient portals via username and password plus knowledge-based attributes or emerging technologies in lieu of passwords to reduce vulnerabilities in identity theft. HHS’s 2018-2020 milestone is to have at least 50% of h ...
... 2015-2017 milestone of 65% of health care organizations permit patient access to patient portals via username and password plus knowledge-based attributes or emerging technologies in lieu of passwords to reduce vulnerabilities in identity theft. HHS’s 2018-2020 milestone is to have at least 50% of h ...
Lecture12
... items and processes that operate on those data items. The key data type in the Clark-Wilson model is a Constrained Data Item (CDI). An Integrity Verification Procedure (IVP) ensures that all CDIs in the system are valid at a certain state. Transactions that enforce the integrity policy are represent ...
... items and processes that operate on those data items. The key data type in the Clark-Wilson model is a Constrained Data Item (CDI). An Integrity Verification Procedure (IVP) ensures that all CDIs in the system are valid at a certain state. Transactions that enforce the integrity policy are represent ...
answer-sheet-7540-040-7630-345-b_
... time spam emails will look like they are from a company or a legit source and they will send emails claiming that you owe them money. This is bad because it will slow down rate of work at a workplace if employees keep getting spam, also it slows down your email system. Phishing – this is where someo ...
... time spam emails will look like they are from a company or a legit source and they will send emails claiming that you owe them money. This is bad because it will slow down rate of work at a workplace if employees keep getting spam, also it slows down your email system. Phishing – this is where someo ...
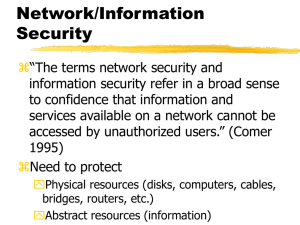
Powerpoint Slides
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
... Public key encryption scheme can also handle the problem of privacy. Sender uses the receiver’s public key to encode the message. Receiver uses it’s private key to decode the message. Messages can be encoded twice to authenticate the sender and to enforce privacy. First with the sender’s private ...
Security Considerations for RemotelyAnywhere
... System administrators can configure RemotelyAnywhere so that users with certain roles have access only to a subset of tools offered by RemotelyAnywhere; for example, the Helpdesk department can be configured to only view a computer’s screen and performance data, but not actually take over the mouse ...
... System administrators can configure RemotelyAnywhere so that users with certain roles have access only to a subset of tools offered by RemotelyAnywhere; for example, the Helpdesk department can be configured to only view a computer’s screen and performance data, but not actually take over the mouse ...
ppt 2
... • Security problems for embedded systems often make them counterproductive • Security very important in many embedded systems ...
... • Security problems for embedded systems often make them counterproductive • Security very important in many embedded systems ...
How Organizations Are Using Fortscale`s User Behavior Analytics
... A unique aspect of Fortscale is the ability to provide rich context for the analyst by automatically labeling users and machines based on many observed behaviors, helping analysts to quickly prioritize events for investigation. One account label applied is “service” which indicates an account whose ...
... A unique aspect of Fortscale is the ability to provide rich context for the analyst by automatically labeling users and machines based on many observed behaviors, helping analysts to quickly prioritize events for investigation. One account label applied is “service” which indicates an account whose ...
CS590: Privacy Constraints on Cloud Services
... has taken a major importance. This review paper will provide a look at current status of the online properties along with a study of possible threats/attacks and some ways to counter these. ...
... has taken a major importance. This review paper will provide a look at current status of the online properties along with a study of possible threats/attacks and some ways to counter these. ...
File
... – Firewalls prevent networked devices from unauthorized threats, however, it also prevents legitimate devices from communicating as well. • Sharing files • Sharing printers • Playing games ...
... – Firewalls prevent networked devices from unauthorized threats, however, it also prevents legitimate devices from communicating as well. • Sharing files • Sharing printers • Playing games ...
CS590F Software Reliability
... Given a software program, with or without inputs, identify and fix defects in the program. ...
... Given a software program, with or without inputs, identify and fix defects in the program. ...
Slide 1 - IITK - Indian Institute of Technology Kanpur
... • Hide the Service Set ID or SSID :Sometimes changing the SSID is also not full proof as hackers have advanced methods to intrude into a wireless network if the SSID is known. To prevent such cases the SSID needs to be hidden. Router configuration softwares allow the SSID to be hidden and the steps ...
... • Hide the Service Set ID or SSID :Sometimes changing the SSID is also not full proof as hackers have advanced methods to intrude into a wireless network if the SSID is known. To prevent such cases the SSID needs to be hidden. Router configuration softwares allow the SSID to be hidden and the steps ...
How does it get written up?
... • My goal: to distribute information on the sorts of things I’d be willing to get paged at 3am about • i.e.. only send an alert when something is an immediate threat, or requires immediate action • implies that alerts ought to include recommendations for action! ...
... • My goal: to distribute information on the sorts of things I’d be willing to get paged at 3am about • i.e.. only send an alert when something is an immediate threat, or requires immediate action • implies that alerts ought to include recommendations for action! ...
Protecting privacy in software agents: Lessons from the
... information was entered (third input screen) ...
... information was entered (third input screen) ...
Security – A Big Question for Big Data
... “Cracker gained user‐level access to modify the download file. . . . you pray never happens, but it did.” – WordPress, reported on wordpress.org, March 2, 2007 ...
... “Cracker gained user‐level access to modify the download file. . . . you pray never happens, but it did.” – WordPress, reported on wordpress.org, March 2, 2007 ...