ppt 2
... whole system for embedded Linux systems • Access control mechanism plays an essential role for OS security • Vulnerability is the main reason that causes threat of confidentiality and integrity • The main content for security mechanisms of the OS • Discretionary access control (DAC) is a simple acce ...
... whole system for embedded Linux systems • Access control mechanism plays an essential role for OS security • Vulnerability is the main reason that causes threat of confidentiality and integrity • The main content for security mechanisms of the OS • Discretionary access control (DAC) is a simple acce ...
Assignment #8 In a word document answer the following questions
... Describe a Monad in your own understanding of the concept (At least 2 paragraphs. Each paragraph must have at least 5 sentences. 50 points) Monad is use to mathematical computations in terms of values and sequences. Monads allow programmers to build up sequence computations. It is also determines ho ...
... Describe a Monad in your own understanding of the concept (At least 2 paragraphs. Each paragraph must have at least 5 sentences. 50 points) Monad is use to mathematical computations in terms of values and sequences. Monads allow programmers to build up sequence computations. It is also determines ho ...
Assignment Sheet 10
... shall operate on two input variables ξ1 and ξ2 . In detail, implement the following steps: a) Enable the user to enter the ranges for ξ1 , ξ2 and for η. b) Implement an interface s.t. the user can specify linguistic terms for a given variable. c) Implement a routine that partitions a variable by let ...
... shall operate on two input variables ξ1 and ξ2 . In detail, implement the following steps: a) Enable the user to enter the ranges for ξ1 , ξ2 and for η. b) Implement an interface s.t. the user can specify linguistic terms for a given variable. c) Implement a routine that partitions a variable by let ...
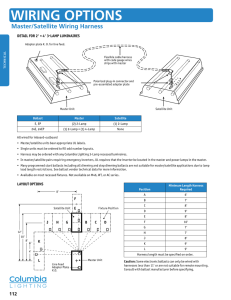
Wiring OptiOns - Columbia Lighting
... All wired for inboard-outboard • Master/satellite units bear appropriate UL labels. • Single units must be ordered to fill odd number layouts. • Harness may be ordered with any Columbia Lighting 3-Lamp recessed luminaires. • In master/satellite pairs requiring emergency inverters, UL requires th ...
... All wired for inboard-outboard • Master/satellite units bear appropriate UL labels. • Single units must be ordered to fill odd number layouts. • Harness may be ordered with any Columbia Lighting 3-Lamp recessed luminaires. • In master/satellite pairs requiring emergency inverters, UL requires th ...
Introduction to Transport Layer
... the receiver can immediately handle any packet it receives. In other words, the receiver can never be overwhelmed with incoming packets. Figure 23.17 shows the layout for this protocol. ...
... the receiver can immediately handle any packet it receives. In other words, the receiver can never be overwhelmed with incoming packets. Figure 23.17 shows the layout for this protocol. ...
Resources - CSE, IIT Bombay
... (a) which block to pick, (b) which to stack, (c) which to unstack, (d) whether to stack a block or (e) whether to unstack an already stacked block. These options have to be searched in order to arrive at the right sequence of actions. ...
... (a) which block to pick, (b) which to stack, (c) which to unstack, (d) whether to stack a block or (e) whether to unstack an already stacked block. These options have to be searched in order to arrive at the right sequence of actions. ...
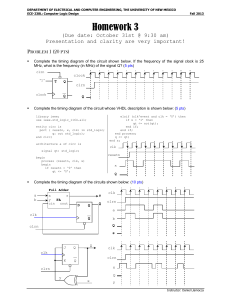
Homework 3 - Daniel Llamocca
... This output is then connected to the enable input of every flip flop, counter, and register whose rate of operation we would like to modify. This way, we get the same effect as modifying the clock frequency to 1 Hz. And we get to use the 100 MHz clock for all the flip flops. The figure below depicts ...
... This output is then connected to the enable input of every flip flop, counter, and register whose rate of operation we would like to modify. This way, we get the same effect as modifying the clock frequency to 1 Hz. And we get to use the 100 MHz clock for all the flip flops. The figure below depicts ...
Verifiable Shuffling
... prover. While this assumption may be reasonable in some cases, when applied to the multi-authority election setting, it results in an election protocol that is not universally verifiable. This is because a subset of authorities can collude to reconstruct the election private key, and then use this i ...
... prover. While this assumption may be reasonable in some cases, when applied to the multi-authority election setting, it results in an election protocol that is not universally verifiable. This is because a subset of authorities can collude to reconstruct the election private key, and then use this i ...
Security & Cryptography
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
Foundations of Cryptography Lecture 2
... • Alice would want to send a message m {0,1}n to Bob – Set-up phase is secret ...
... • Alice would want to send a message m {0,1}n to Bob – Set-up phase is secret ...
An IPSec-based Host Architecture for Secure
... Join/leave interaction done via standard point-to-point secure connection (such as IPSec, SSL) with the center. - Receives key updates from controller and updates MSA -Key updates assume a “reliable multicast shim”. (Can be implemented by any general RM protocol or by a special purpose protocol.) ...
... Join/leave interaction done via standard point-to-point secure connection (such as IPSec, SSL) with the center. - Receives key updates from controller and updates MSA -Key updates assume a “reliable multicast shim”. (Can be implemented by any general RM protocol or by a special purpose protocol.) ...
Ibrahim Aljubayri`s presentation on Secure Network Channel among
... needed for SOSTC into kernel memory at the system boot-time. The initial data are an encryption key for packet encryption, an authentication key for packet authentication and IP addresses of secure OS to be applied to SOSTC. An encryption key and an authentication key are self-encoded within kernel ...
... needed for SOSTC into kernel memory at the system boot-time. The initial data are an encryption key for packet encryption, an authentication key for packet authentication and IP addresses of secure OS to be applied to SOSTC. An encryption key and an authentication key are self-encoded within kernel ...
Slide 1
... Internet is made up of a wide variety of computers, from supercomputers to personal computers. Each of these computers has its type of software and application running. How do all of these computers understand each other and work together ? ...
... Internet is made up of a wide variety of computers, from supercomputers to personal computers. Each of these computers has its type of software and application running. How do all of these computers understand each other and work together ? ...
Securing Distribution Automation
... The issue of field device password management has been identified by the NIST CyberSecurity Coordination Task Group as one of the issues that needs to be addressed for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that ...
... The issue of field device password management has been identified by the NIST CyberSecurity Coordination Task Group as one of the issues that needs to be addressed for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that ...
Chapter 28
... • Often some repeated interactions would help. Consider the punishment strategies. Each firm produces half of the monopoly output and gets profit m. If there is any cheating in the past, switch to Cournot competition forever and each gets c. So if a firm deviates, it can at best get d for one s ...
... • Often some repeated interactions would help. Consider the punishment strategies. Each firm produces half of the monopoly output and gets profit m. If there is any cheating in the past, switch to Cournot competition forever and each gets c. So if a firm deviates, it can at best get d for one s ...
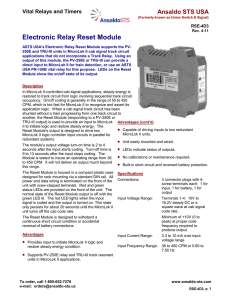
Electronic Relay Reset Module
... MicroLok II logic controller input circuits in parallel for redundant systems. Unit easily mounted and wired. The module’s output voltage turn-on time is 2 to 4 seconds after the input starts coding. Turn-off time is LEDs indicate status of outputs. 9 to 13 seconds after the input stops coding. The ...
... MicroLok II logic controller input circuits in parallel for redundant systems. Unit easily mounted and wired. The module’s output voltage turn-on time is 2 to 4 seconds after the input starts coding. Turn-off time is LEDs indicate status of outputs. 9 to 13 seconds after the input stops coding. The ...
Chapter 08
... the Secure Sockets Layer (SSL) protocol to allow secure ecommerce transactions Kerberos provides a network-wide user and service authentication scheme to limit network access to authorized ...
... the Secure Sockets Layer (SSL) protocol to allow secure ecommerce transactions Kerberos provides a network-wide user and service authentication scheme to limit network access to authorized ...
A Secure Anti-Collusion Data Sharing Scheme for
... security guarantees for the sharing data files since they are outsourced. Unfortunately, because of the frequent change of the membership, sharing data while providing privacy-preserving is still a challenging issue, especially for an untrusted cloud due to the collusion attack. Moreover, for existi ...
... security guarantees for the sharing data files since they are outsourced. Unfortunately, because of the frequent change of the membership, sharing data while providing privacy-preserving is still a challenging issue, especially for an untrusted cloud due to the collusion attack. Moreover, for existi ...
Intro to Verilog
... ◦ Include space for lots of logic gates ◦ Can be programmed… …and reprogrammed ~100,000 times ...
... ◦ Include space for lots of logic gates ◦ Can be programmed… …and reprogrammed ~100,000 times ...