HSARPA Cyber Security R&D
... of new emerging systems; To develop new and enhanced technologies for the detection of, prevention of, and response to cyber attacks on the nation’s critical information infrastructure. To facilitate the transfer of these technologies into the national infrastructure as a matter of urgency. ...
... of new emerging systems; To develop new and enhanced technologies for the detection of, prevention of, and response to cyber attacks on the nation’s critical information infrastructure. To facilitate the transfer of these technologies into the national infrastructure as a matter of urgency. ...
Organizations That Use TLS/SSL
... certification authority, attesting to the certificate's validity. Organizations can also create their own certificates, known as self-signed certificates, although these will not be inherently trusted by a web browser if installed on a web server and will usually display a security warning for any u ...
... certification authority, attesting to the certificate's validity. Organizations can also create their own certificates, known as self-signed certificates, although these will not be inherently trusted by a web browser if installed on a web server and will usually display a security warning for any u ...
Irish Collegiate Programming Competition 2017 Problem Set
... his troubled tirade into a tremendous talk. Luckily for you, you charge for each correction, and there are plenty of corrections to make. Every character added, removed, or changed increases your fee. However, as an honest person, you intend to make the minimal number of changes. Your task is to com ...
... his troubled tirade into a tremendous talk. Luckily for you, you charge for each correction, and there are plenty of corrections to make. Every character added, removed, or changed increases your fee. However, as an honest person, you intend to make the minimal number of changes. Your task is to com ...
Условия задач X Открытого чемпионата по программированию
... inserted between any two other matches. The + and = removing one match turns into -, shifting one match in V moves in X and vice versa X goes into V. You can not "glue" match adjacent characters: XX after the removal of two matches is not converted to V. For example XXIVI can not be converted to VI ...
... inserted between any two other matches. The + and = removing one match turns into -, shifting one match in V moves in X and vice versa X goes into V. You can not "glue" match adjacent characters: XX after the removal of two matches is not converted to V. For example XXIVI can not be converted to VI ...
Week 07 Lecture
... Step 1: With Power off, Pulse the node with a pulser and monitor various inputs and the output of G1 with a current tracer. If no current activity is seen at point B but a large current activity is seen at the output of G1, then G1 output is shorted internally to ground. Step 2: If no current activ ...
... Step 1: With Power off, Pulse the node with a pulser and monitor various inputs and the output of G1 with a current tracer. If no current activity is seen at point B but a large current activity is seen at the output of G1, then G1 output is shorted internally to ground. Step 2: If no current activ ...
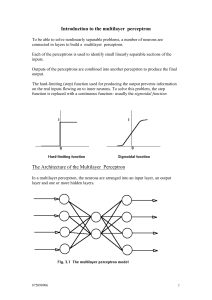
Introduction to the multilayer perceptron
... Remedies such as the "momentum term" add to computational cost Other remedies: using estimates of transfer functions using transfer functions with easy to compute derivatives using estimates of error values, eg., a single global error value for the hidden layer 3. Scaling problem Do not scale up wel ...
... Remedies such as the "momentum term" add to computational cost Other remedies: using estimates of transfer functions using transfer functions with easy to compute derivatives using estimates of error values, eg., a single global error value for the hidden layer 3. Scaling problem Do not scale up wel ...
Problem Set 8 The getting is
... The secret ofgetting ahead is getting started. The secret ofgetting start is breaking your complex overwhelming tasks into small manageable tasks, and then starting on the first one. --Mark Twain ...
... The secret ofgetting ahead is getting started. The secret ofgetting start is breaking your complex overwhelming tasks into small manageable tasks, and then starting on the first one. --Mark Twain ...
Public Presentation - Academic Conferences
... SW subversion steals credit/debit card data “an ‘illicit and unauthorized computer program’ was secretly installed at every one of its 300-plus stores.” ...
... SW subversion steals credit/debit card data “an ‘illicit and unauthorized computer program’ was secretly installed at every one of its 300-plus stores.” ...
ISi-L - BSI
... The mentioned basic protocols do not offer any functions that ensure the confidentiality and integrity of the transmitted data. For that reason, such functions must be implemented by the respective applications in their own protocols. The protocol version 6 (IPv6) has been available for quite some t ...
... The mentioned basic protocols do not offer any functions that ensure the confidentiality and integrity of the transmitted data. For that reason, such functions must be implemented by the respective applications in their own protocols. The protocol version 6 (IPv6) has been available for quite some t ...
wire
... wand w; // a scalar net of type “wire and” reg [3:0] v; // a 4-bit vector register from msb to lsb reg [7:0] m, n; // two 8-bit registers tri [15:0] busa; // a 16-bit tri-state bus wire [0:31] w1, w2; // Two 32-bit wires with msb being the 0 bit, not recommended ...
... wand w; // a scalar net of type “wire and” reg [3:0] v; // a 4-bit vector register from msb to lsb reg [7:0] m, n; // two 8-bit registers tri [15:0] busa; // a 16-bit tri-state bus wire [0:31] w1, w2; // Two 32-bit wires with msb being the 0 bit, not recommended ...
TotalPT - Department of Computer Engineering
... adjust weights connecting links between input and output until it obtains the correct response to the training patterns. But biological learning is not a single process: some forms are very quick and others relatively slow. Short-term biological memory, in particular, works very quickly, so slow neu ...
... adjust weights connecting links between input and output until it obtains the correct response to the training patterns. But biological learning is not a single process: some forms are very quick and others relatively slow. Short-term biological memory, in particular, works very quickly, so slow neu ...
Speech Title Here
... DREAD potential D Damage What are the consequences of a successful exploit? R Reproducibility Would an exploit work every time or only under certain circumstances? E Exploitability How skilled must an attacker be to exploit the vulnerability? users A Affected How many users would be affected by a s ...
... DREAD potential D Damage What are the consequences of a successful exploit? R Reproducibility Would an exploit work every time or only under certain circumstances? E Exploitability How skilled must an attacker be to exploit the vulnerability? users A Affected How many users would be affected by a s ...
assign - inst.eecs.berkeley.edu - University of California, Berkeley
... – Can contain many statements including if, for, while, case – Statements in the always block are executed sequentially » (Continuous assignments <= are executed in parallel) – The entire block is executed at once – The final result describes the function of the circuit for current set of inputs » i ...
... – Can contain many statements including if, for, while, case – Statements in the always block are executed sequentially » (Continuous assignments <= are executed in parallel) – The entire block is executed at once – The final result describes the function of the circuit for current set of inputs » i ...
Carry look-ahead adder
... Si = Pi ⊕ Ci-1 Ci+1= Gi + PiCi These equations show that a carry signal will be generated in two cases: 1) if both bits Ai and Bi are 1 2) if either Ai or Bi is 1 and the carry-in Ci is 1. Let's apply these equations for a 4-bit adder: ...
... Si = Pi ⊕ Ci-1 Ci+1= Gi + PiCi These equations show that a carry signal will be generated in two cases: 1) if both bits Ai and Bi are 1 2) if either Ai or Bi is 1 and the carry-in Ci is 1. Let's apply these equations for a 4-bit adder: ...
Security Risks
... • Designed to keep information private • Many encryption forms exist • Provides assurances – Data not modified between being sent and received – Data can be viewed only by intended recipient – Data was not forged by an intruder ...
... • Designed to keep information private • Many encryption forms exist • Provides assurances – Data not modified between being sent and received – Data can be viewed only by intended recipient – Data was not forged by an intruder ...
CASTLE KIT Section 1 Study Guide KEY After completing Section 1
... After completing Section 1, you should be able to: • Explain why bulbs will not light if there is a break in a continuous closed loop. • Identify loops in which bulbs will and will not light by inspecting diagrams. • Based on compass observations, explain why there is a one-way direction of flow in ...
... After completing Section 1, you should be able to: • Explain why bulbs will not light if there is a break in a continuous closed loop. • Identify loops in which bulbs will and will not light by inspecting diagrams. • Based on compass observations, explain why there is a one-way direction of flow in ...
1- Single Neuron Model
... 2- A learning sample is presented at the input, which will cause arbitrary outputs to be peaked. Sigmoid nonlinearities are used to find the output of each node. 3- Topmost layer’s weights are changed to force the outputs to desired values. 4- Moving down the layers, each layers weights are updated ...
... 2- A learning sample is presented at the input, which will cause arbitrary outputs to be peaked. Sigmoid nonlinearities are used to find the output of each node. 3- Topmost layer’s weights are changed to force the outputs to desired values. 4- Moving down the layers, each layers weights are updated ...
Avaya™ G700 Media Gateway Security - Issue 1.0
... 5) Firewalls and Routers that implement, and are managed by, an SNMPv3-based network management system are recommended (vs. SNMPv1 or SNMPv2) because the security of SNMPv3 can prevent unauthorized updates to the routing tables and access control list by an intruder. Layer 2 switches are preferred t ...
... 5) Firewalls and Routers that implement, and are managed by, an SNMPv3-based network management system are recommended (vs. SNMPv1 or SNMPv2) because the security of SNMPv3 can prevent unauthorized updates to the routing tables and access control list by an intruder. Layer 2 switches are preferred t ...
Coding for Interactive Communication
... In the standard (noiseless) communication complexity model, the argument (input) z = (ZA]z g ) of a function f ( z ) is split between two processors A and B, with A receiving Z A and B receiving z g ; the processors compute f ( z ) (solve the communication problem f ) by exchanging bits over a noise ...
... In the standard (noiseless) communication complexity model, the argument (input) z = (ZA]z g ) of a function f ( z ) is split between two processors A and B, with A receiving Z A and B receiving z g ; the processors compute f ( z ) (solve the communication problem f ) by exchanging bits over a noise ...
PPT - Purdue Computer Science
... – key transport: one party creates, and securely transfers it to the other(s). – key agreement: key establishment technique in which a shared secret is derived by two (or more) parties ...
... – key transport: one party creates, and securely transfers it to the other(s). – key agreement: key establishment technique in which a shared secret is derived by two (or more) parties ...
Virtual Private Network
... • Remote-access VPNs permit secure, encrypted connections between a company's private network and remote users through a third-party service provider ...
... • Remote-access VPNs permit secure, encrypted connections between a company's private network and remote users through a third-party service provider ...
II.I Selected Database Issues: 1
... 2. Integrity: it has not been changed during transmission 3. Authenticity: the receiver can be sure it came from the sender 4. Non-fabrication: the sender can be sure the receiver is genuine 5. non-repudiation: the sender cannot deny he or she sent it II.I Selected Database Issues: 1 - Security ...
... 2. Integrity: it has not been changed during transmission 3. Authenticity: the receiver can be sure it came from the sender 4. Non-fabrication: the sender can be sure the receiver is genuine 5. non-repudiation: the sender cannot deny he or she sent it II.I Selected Database Issues: 1 - Security ...
Section3
... (b) If is not be lower than -13 V. find the maximum allowed value for (c) If , is varied in the range 100Ω to 1 KΩ what is the corresponding change in and ? Solution (a) ...
... (b) If is not be lower than -13 V. find the maximum allowed value for (c) If , is varied in the range 100Ω to 1 KΩ what is the corresponding change in and ? Solution (a) ...
Circuit Training
... 90 seconds of resistance exercise. In the past, people typically performed three sets of each strength exercise, resting two to three minutes between successive sets for sufficient muscle recovery. Of course, this resulted in relatively long training sessions , with much more time spent resting than ...
... 90 seconds of resistance exercise. In the past, people typically performed three sets of each strength exercise, resting two to three minutes between successive sets for sufficient muscle recovery. Of course, this resulted in relatively long training sessions , with much more time spent resting than ...