Power Point XP - FSU Computer Science
... Thread system can advice kernel scheduler on preemptions Kernel needs to notify the thread system of various events (e.g., blocking) via upcalls Kernel needs to make a kernel thread available to activate user-level scheduler ...
... Thread system can advice kernel scheduler on preemptions Kernel needs to notify the thread system of various events (e.g., blocking) via upcalls Kernel needs to make a kernel thread available to activate user-level scheduler ...
Chapter 1: Introduction
... Usually slightly faster to service a request with an existing thread than create a new thread Allows the number of threads in the application(s) to be bound to the size of the pool ...
... Usually slightly faster to service a request with an existing thread than create a new thread Allows the number of threads in the application(s) to be bound to the size of the pool ...
Reboots are for Hardware: Challenges and Solutions to
... Using this data, we performed two types of analysis. First, we used automatically-computed contextual information to determine which transactions changed only code inside dynamically-updatable objects and could therefore be developed into dynamic updates. Second, we randomly selected transactions fr ...
... Using this data, we performed two types of analysis. First, we used automatically-computed contextual information to determine which transactions changed only code inside dynamically-updatable objects and could therefore be developed into dynamic updates. Second, we randomly selected transactions fr ...
Operating System Concepts
... mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or ...
... mapping is that a process's threads cannot simultaneously execute on multiple processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or ...
01 - Quick Heal
... • When it runs, it copies itself to the %APPDATA% directory using a randomly generated 16-character file name. • It modifies certain registry entries to ensure it runs each time the infected machine is started. ...
... • When it runs, it copies itself to the %APPDATA% directory using a randomly generated 16-character file name. • It modifies certain registry entries to ensure it runs each time the infected machine is started. ...
Operating System Concepts
... Responsiveness - allow a program to continue running even if part of it is blocked (e.g. In a browser, multiple threads are working simultaneously to increase responsiveness) Resource sharing - threads share the memory and resources of the process (lower main memory requirement) Economy - it is more ...
... Responsiveness - allow a program to continue running even if part of it is blocked (e.g. In a browser, multiple threads are working simultaneously to increase responsiveness) Resource sharing - threads share the memory and resources of the process (lower main memory requirement) Economy - it is more ...
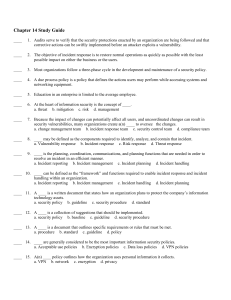
File - Information Technology Security
... ____ 16. A policy that addresses security as it relates to human resources is known as a(n) ____ policy. a. VPN b. acceptable use c. security-related human resource d. technical ____ 17. ____ are a person’s fundamental beliefs and principles used to define what is good, right, and just. a. Morals b ...
... ____ 16. A policy that addresses security as it relates to human resources is known as a(n) ____ policy. a. VPN b. acceptable use c. security-related human resource d. technical ____ 17. ____ are a person’s fundamental beliefs and principles used to define what is good, right, and just. a. Morals b ...
Threads (and more on Processes)
... thread management • Operation are very efficient (procedure calls) • Space efficient and all in user space (TCB) • Task switching is very fast ...
... thread management • Operation are very efficient (procedure calls) • Space efficient and all in user space (TCB) • Task switching is very fast ...
Figure 5.01
... Linux Threads Linux refers to them as tasks rather than threads Thread creation is done through clone()system call clone() allows a child task to share the address ...
... Linux Threads Linux refers to them as tasks rather than threads Thread creation is done through clone()system call clone() allows a child task to share the address ...
STUDY GUIDE FOR THE MIDTERM EXAM of Tuesday November 3
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
... 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical sections after a process has made a request to enter its critical section and before that request is ...
Mac OS 8 Revealed
... useful to some readers, but not to others. Look at “Mac OS Heritage” boxes like the one below for discussions of earlier versions of Mac OS technologies. MAC OS HERITAGE Look in These Sections for Historical Background Information If you have little experience with the Mac OS, you’ll find sections l ...
... useful to some readers, but not to others. Look at “Mac OS Heritage” boxes like the one below for discussions of earlier versions of Mac OS technologies. MAC OS HERITAGE Look in These Sections for Historical Background Information If you have little experience with the Mac OS, you’ll find sections l ...
Power Point XP
... Thread system can advice kernel scheduler on preemptions Kernel needs to notify the thread system of various events (e.g., blocking) via upcalls Kernel needs to make a kernel thread available to activate user-level scheduler ...
... Thread system can advice kernel scheduler on preemptions Kernel needs to notify the thread system of various events (e.g., blocking) via upcalls Kernel needs to make a kernel thread available to activate user-level scheduler ...
Centralized Management and Processing Policy for Log Files
... system resource and network throughput to detect network problems, monitoring users’ actions by recording service conditions to prevent users from exceeding their authority and warn of questionable conduct, diagnosing abnormal events, determining the intrusion range, providing help for system recove ...
... system resource and network throughput to detect network problems, monitoring users’ actions by recording service conditions to prevent users from exceeding their authority and warn of questionable conduct, diagnosing abnormal events, determining the intrusion range, providing help for system recove ...
Providing Dynamic Update in an Operating System
... unplanned down-time of computing infrastructure to apply updates, combined with the demand for continuous availability, provides strong motivation to investigate dynamic update techniques for operating systems. In addition to the above mentioned impact on availability, dynamically updatable systems ...
... unplanned down-time of computing infrastructure to apply updates, combined with the demand for continuous availability, provides strong motivation to investigate dynamic update techniques for operating systems. In addition to the above mentioned impact on availability, dynamically updatable systems ...
1- intro to rts
... • A real-time system is any information processing system which has to respond to externally generated input stimuli within a finite and specified period – the correctness depends not only on the logical result – but also the time it was delivered – failure to respond is as bad as the wrong response ...
... • A real-time system is any information processing system which has to respond to externally generated input stimuli within a finite and specified period – the correctness depends not only on the logical result – but also the time it was delivered – failure to respond is as bad as the wrong response ...
3 Responding to Incidents
... 1.6.3 Unauthorized Utilization of Resources It is not always necessary to access another user's account in order to attack an IS. An intruder can access information or plant Trojan horse programs simply by misusing available services or via social engineering. 1.6.4 Disruption of Denial of Services ...
... 1.6.3 Unauthorized Utilization of Resources It is not always necessary to access another user's account in order to attack an IS. An intruder can access information or plant Trojan horse programs simply by misusing available services or via social engineering. 1.6.4 Disruption of Denial of Services ...
File - BS
... interactive process and non-interactive process. The interactive process generally require much faster response time than non interactive process. These process can be separated and can be scheduled separately. The interactive process should be scheduled more quickly than non interactive process. ...
... interactive process and non-interactive process. The interactive process generally require much faster response time than non interactive process. These process can be separated and can be scheduled separately. The interactive process should be scheduled more quickly than non interactive process. ...
The Architecture of a Worldwide Distributed System
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
... period of learning as much as you can in as many different subjects that are interesting. In this respect I took full advantage of my Ph.D.: I did work ranging from programming my own EEPROMs, to secure network objects, digital video on demand, and a full blown new operating system with its own TCP/ ...
Processes
... If P and Q wish to communicate, they need to: z establish a communication link between them z exchange messages via send/receive Implementation of communication link z physical (e.g., shared memory, hardware bus) z logical (e.g., logical properties) z ...
... If P and Q wish to communicate, they need to: z establish a communication link between them z exchange messages via send/receive Implementation of communication link z physical (e.g., shared memory, hardware bus) z logical (e.g., logical properties) z ...
The Internet and Its Uses
... Consists of mostly inexperienced individuals using easily available hacking tools such as shell scripts and password crackers. Even unstructured threats that are only executed with the intent of testing and challenging a hacker’s skills can still do serious damage to a company. ...
... Consists of mostly inexperienced individuals using easily available hacking tools such as shell scripts and password crackers. Even unstructured threats that are only executed with the intent of testing and challenging a hacker’s skills can still do serious damage to a company. ...
chapter 1 - University of Virginia
... In simulation, the researcher creates a model of the proposed microprocessor. The researcher enters the model into a simulator to create a virtual microprocessor. The simulator executes a piece of benchmark code on the virtual microprocessor. The simulator monitors the execution and generates statis ...
... In simulation, the researcher creates a model of the proposed microprocessor. The researcher enters the model into a simulator to create a virtual microprocessor. The simulator executes a piece of benchmark code on the virtual microprocessor. The simulator monitors the execution and generates statis ...
Threads
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the ...
... Linux refers to them as tasks rather than threads Thread creation is done through clone() system call clone() allows a child task to share the address space of the ...
12_Pthreads
... instructions that can be scheduled to run as such by the operating system. • But what does this mean? • The concept of a "procedure" that runs independently from its main program may best describe a thread. • Imagine a main program (a.out) that contains a number of procedures. • Then imagine all of ...
... instructions that can be scheduled to run as such by the operating system. • But what does this mean? • The concept of a "procedure" that runs independently from its main program may best describe a thread. • Imagine a main program (a.out) that contains a number of procedures. • Then imagine all of ...
Figure 5.01 - Texas A&M University
... running even if part of it is blocked or is performing a lengthy operation. Resource Sharing. The benefit of sharing code and data is that it ...
... running even if part of it is blocked or is performing a lengthy operation. Resource Sharing. The benefit of sharing code and data is that it ...