INF1060: Introduction to Operating Systems and Data Communication
... communicate with other processes (on same or another machine) ...
... communicate with other processes (on same or another machine) ...
Sun Fire X2200 M2 Server Operating System Installation Guide
... The OPEN LOOK and Sun™ Graphical User Interface was developed by Sun Microsystems, Inc. for its users and licensees. Sun acknowledges the pioneering efforts of Xerox in researching and developing the concept of visual or graphical user interfaces for the computer industry. Sun holds a non-exclusive ...
... The OPEN LOOK and Sun™ Graphical User Interface was developed by Sun Microsystems, Inc. for its users and licensees. Sun acknowledges the pioneering efforts of Xerox in researching and developing the concept of visual or graphical user interfaces for the computer industry. Sun holds a non-exclusive ...
BUILDING A DEPENDABLE OPERATING SYSTEM: FAULT TOLERANCE IN MINIX 3
... Amsterdam), Michael Hohmuth (Operating System Research Center, AMD), Galen Hunt (Operating Systems Group, Microsoft Research), and Michael Swift (Computer Sciences Department, University of Wisconsin-Madison), for reviewing this thesis. It has been an honor to get direct feedback from some of the le ...
... Amsterdam), Michael Hohmuth (Operating System Research Center, AMD), Galen Hunt (Operating Systems Group, Microsoft Research), and Michael Swift (Computer Sciences Department, University of Wisconsin-Madison), for reviewing this thesis. It has been an honor to get direct feedback from some of the le ...
Operating System
... Computers are widely employed in almost all the activities of today’s modern man. They are used by people of all ages in a variety of environments. We recognize the computer as a set of devices, such as the main case, monitor, keyboard, mouse, etc., collectively called the hardware. In one session’s ...
... Computers are widely employed in almost all the activities of today’s modern man. They are used by people of all ages in a variety of environments. We recognize the computer as a set of devices, such as the main case, monitor, keyboard, mouse, etc., collectively called the hardware. In one session’s ...
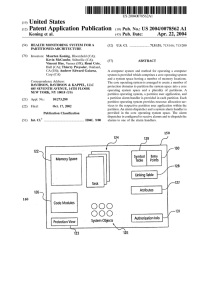
CodeMoctules O O O
... speed, but is de?cient in providing system protection. [0004] In order to improve system protection, it has been proposed to provide an operating system that implements a “protection domain” architecture. VxWorks® AE, marketed by Wind River Systems of Alameda, Calif., is an example of such a protect ...
... speed, but is de?cient in providing system protection. [0004] In order to improve system protection, it has been proposed to provide an operating system that implements a “protection domain” architecture. VxWorks® AE, marketed by Wind River Systems of Alameda, Calif., is an example of such a protect ...
Operating Systems
... per process) timer is created by the kernel on behalf of a thread (or process) when the thread calls the create timer function. In a system that contains more than one clock, the calling thread specifies the clock to which the timer is to be bound; by this, we mean that the timer will keep track of ...
... per process) timer is created by the kernel on behalf of a thread (or process) when the thread calls the create timer function. In a system that contains more than one clock, the calling thread specifies the clock to which the timer is to be bound; by this, we mean that the timer will keep track of ...
Operating Systems ECE344
... the concepts of processes and threads • The thread defines a sequential execution stream within a process (PC, SP, registers) • The process defines the address space and general process attributes (everything but threads of execution) ...
... the concepts of processes and threads • The thread defines a sequential execution stream within a process (PC, SP, registers) • The process defines the address space and general process attributes (everything but threads of execution) ...
Chapter 02: The Need for Security
... program’s access to the targeted computer. The virus-controlled target program then carries out the virus’s plan, by replicating itself into additional targeted systems. A worm is a malicious program that replicates itself constantly, without requiring another program to provide a safe environment f ...
... program’s access to the targeted computer. The virus-controlled target program then carries out the virus’s plan, by replicating itself into additional targeted systems. A worm is a malicious program that replicates itself constantly, without requiring another program to provide a safe environment f ...
The Application Kernel Approach - a Novel Approach for Adding
... were faced with the problem that it was very difficult and costly to make the needed modifications because of the size of the code, the long time during which the code had been developed (this has led to a code structure which is hard to grasp), and the intricate nature of operating system kernels. ...
... were faced with the problem that it was very difficult and costly to make the needed modifications because of the size of the code, the long time during which the code had been developed (this has led to a code structure which is hard to grasp), and the intricate nature of operating system kernels. ...
OpenAFS Quick Start Guide for UNIX
... afs, /usr/vice, etc.), which do not correspond to the normal file system hierarchy on many modern machines; the paths may need to be substituted according to the local software installation. OpenAFS Administration Guide This guide describes the concepts and procedures that a system administrator mus ...
... afs, /usr/vice, etc.), which do not correspond to the normal file system hierarchy on many modern machines; the paths may need to be substituted according to the local software installation. OpenAFS Administration Guide This guide describes the concepts and procedures that a system administrator mus ...
Electrical Engineering and Computer Science Department Technical
... hybrid runtimes (HRTs), runtimes that run as kernels, and that enjoy full hardware access and control over abstractions to the machine. The primary claim of this dissertation is that the hybrid runtime model can provide significant benefits to parallel runtimes and the applications that run on top ...
... hybrid runtimes (HRTs), runtimes that run as kernels, and that enjoy full hardware access and control over abstractions to the machine. The primary claim of this dissertation is that the hybrid runtime model can provide significant benefits to parallel runtimes and the applications that run on top ...
Configuring Security Access Control Lists
... outbound) to the parts of your network specified in the entry. Each entry also contains a filter element that is based on criteria such as the source address, the destination address, the protocol, and protocol-specific parameters such as ports and so on. An implicit deny-all entry exists at the end ...
... outbound) to the parts of your network specified in the entry. Each entry also contains a filter element that is based on criteria such as the source address, the destination address, the protocol, and protocol-specific parameters such as ports and so on. An implicit deny-all entry exists at the end ...
Introduction to the New Mainframe: z/OS Basics
... Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. ...
... Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. ...
Ingate Firewall & SIParator Training
... What Other IP-PBXs Vendors Do Most all IP-PBX vendors recommend the use of some sort of “SIP-Aware Firewall” for deployment ...
... What Other IP-PBXs Vendors Do Most all IP-PBX vendors recommend the use of some sort of “SIP-Aware Firewall” for deployment ...
Technical Presentation
... What Other IP-PBXs Vendors Do Most all IP-PBX vendors recommend the use of some sort of “SIP-Aware Firewall” for deployment ...
... What Other IP-PBXs Vendors Do Most all IP-PBX vendors recommend the use of some sort of “SIP-Aware Firewall” for deployment ...
Chapter 4: Threads
... Implements the one-to-one mapping, kernel-level Each thread contains A thread id Register set Separate user and kernel stacks Private data storage area The register set, stacks, and private storage area are known as the context of the threads The primary data structures of a thread include: ...
... Implements the one-to-one mapping, kernel-level Each thread contains A thread id Register set Separate user and kernel stacks Private data storage area The register set, stacks, and private storage area are known as the context of the threads The primary data structures of a thread include: ...
Proceedings of the FREENIX Track: 2003 USENIX Annual Technical Conference
... As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow Linux to boot another operating system. The result is that LinuxBIOS can load a kernel over any device, network, protocol, and file system that Linux supports– compelling reasons to use Linux as a boot program. Even with th ...
... As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow Linux to boot another operating system. The result is that LinuxBIOS can load a kernel over any device, network, protocol, and file system that Linux supports– compelling reasons to use Linux as a boot program. Even with th ...
Chapter 4
... • One or more threads may reside in the same process. • When a parent process forks a child process, the child process has its own address spaced its own copy of all data of the parent process. • The child has its own copies of global variables and resources such as descriptors to open files; for ex ...
... • One or more threads may reside in the same process. • When a parent process forks a child process, the child process has its own address spaced its own copy of all data of the parent process. • The child has its own copies of global variables and resources such as descriptors to open files; for ex ...
3.2. Android Programming Language
... industry. Such companies include Motorola and Sony Ericsson, which for many years have been developing their own mobile operating systems. When the iPhone was launched, many of these manufacturers had to scramble to find new ways of revitalizing their products. These manufacturers see Android as a s ...
... industry. Such companies include Motorola and Sony Ericsson, which for many years have been developing their own mobile operating systems. When the iPhone was launched, many of these manufacturers had to scramble to find new ways of revitalizing their products. These manufacturers see Android as a s ...
MODERN OPERATING SYSTEMS Third Edition ANDREW S. …
... • A capability supported by some operating systems that allows one process to communicate with another process. • The processes can be running on the same computer or on different computers connected through a network. • IPC enables one application to control another application, and for several app ...
... • A capability supported by some operating systems that allows one process to communicate with another process. • The processes can be running on the same computer or on different computers connected through a network. • IPC enables one application to control another application, and for several app ...
Malware Removal Guide
... Currently there are thousands of new computer viruses or other types of malware discovered each month. Many of these threats are designed to resist detection, and removal, and may disable the execution of your antivirus software, and your computer’s ability to connect to online scanning that can pro ...
... Currently there are thousands of new computer viruses or other types of malware discovered each month. Many of these threats are designed to resist detection, and removal, and may disable the execution of your antivirus software, and your computer’s ability to connect to online scanning that can pro ...
20740A_08
... Ensure that unauthorized users do not have physical access to failover cluster nodes Ensure that you use antimalware software Ensure that your intra-cluster communication authenticates with Kerberos version 5 ...
... Ensure that unauthorized users do not have physical access to failover cluster nodes Ensure that you use antimalware software Ensure that your intra-cluster communication authenticates with Kerberos version 5 ...
VPN: Virtual Private Network
... • Easy to add/remove users • Reduced long-distance telecommunications ...
... • Easy to add/remove users • Reduced long-distance telecommunications ...