Document
... Ref: http://userhome.brooklyn.cuny.edu/irudowdky/OperatingSystems.htm & Silberschatz, Gagne, & Galvin, Operating Systems Concepts, 7th ed, Wiley (ch 1-3) ...
... Ref: http://userhome.brooklyn.cuny.edu/irudowdky/OperatingSystems.htm & Silberschatz, Gagne, & Galvin, Operating Systems Concepts, 7th ed, Wiley (ch 1-3) ...
the thread - Bilkent University Computer Engineering Department
... Linux Threads • Linux refers to them as tasks rather than threads • Thread creation is done through clone() system call • clone() allows a child task to share the address space of the parent task (process) ...
... Linux Threads • Linux refers to them as tasks rather than threads • Thread creation is done through clone() system call • clone() allows a child task to share the address space of the parent task (process) ...
IPv6 Security Eric Vyncke, Distinguished Engineer @evyncke
... iACL: edge ACL denying packets addressed to your routers Easy with IPv6 because new addressing scheme J http://www.insinuator.net/2013/03/ipv6-neighbor-cache-exhaustion-attacks-risk-assessment-mitigation-strategies-part-1 © 2014 Cisco and/or its affiliates. All rights reserved. ...
... iACL: edge ACL denying packets addressed to your routers Easy with IPv6 because new addressing scheme J http://www.insinuator.net/2013/03/ipv6-neighbor-cache-exhaustion-attacks-risk-assessment-mitigation-strategies-part-1 © 2014 Cisco and/or its affiliates. All rights reserved. ...
Chapter16-PresentationDistilled
... In addition to the triad, there are ISO standards ISO/IEC 27002-270037 that speak directly (and thoroughly) about security techniques and are routinely adopted by governments and corporations the world over. These standards are very comprehensive, outlining the need for risk assessment and managemen ...
... In addition to the triad, there are ISO standards ISO/IEC 27002-270037 that speak directly (and thoroughly) about security techniques and are routinely adopted by governments and corporations the world over. These standards are very comprehensive, outlining the need for risk assessment and managemen ...
ppt
... °If user programs could access device directly? • could destroy each others data, ... • might break the devices, … CS61C L14 Interrupts © UC Regents ...
... °If user programs could access device directly? • could destroy each others data, ... • might break the devices, … CS61C L14 Interrupts © UC Regents ...
Chapter 4: Threads
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
FREE Sample Here
... A computer virus consists of segments of code that perform malicious actions. This code behaves very much like a virus pathogen attacking animals and plants, using the cell’s own replication machinery to propagate and attack. The code attaches itself to the existing program and takes control of that ...
... A computer virus consists of segments of code that perform malicious actions. This code behaves very much like a virus pathogen attacking animals and plants, using the cell’s own replication machinery to propagate and attack. The code attaches itself to the existing program and takes control of that ...
Threads, Introduction to Synchronization
... “non-deterministic:” don’t know what the output will be, and it is likely to be different across runs Hard to detect: too many possible schedules Hard to debug: “heisenbug,” debugging changes timing so hides bugs (vs “bohr bug”) ...
... “non-deterministic:” don’t know what the output will be, and it is likely to be different across runs Hard to detect: too many possible schedules Hard to debug: “heisenbug,” debugging changes timing so hides bugs (vs “bohr bug”) ...
Threads and Multi-threaded Programming
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
Threads and Multi-threaded Programming
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
... Examples (nearly all modern OSs): Windows, Linux, … – All these kernels have threading support. They can schedule processes and their threads (not only processes) ...
RADIUS Implementation and Deployment Best Practices
... access client and the authenticating server (the RADIUS server) that can vary based on the parameters of the connection. The conversation consists of requests for authentication information and the responses. The length and detail of the authentication conversation is dependent upon the EAP type. Ar ...
... access client and the authenticating server (the RADIUS server) that can vary based on the parameters of the connection. The conversation consists of requests for authentication information and the responses. The length and detail of the authentication conversation is dependent upon the EAP type. Ar ...
CS162 Operating Systems and Systems Programming Lecture 1
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
... • Problem: Run multiple applications in such a way that they are protected from one another • Goal: ...
OS Portal: an economic approach for making an embedded kernel
... Section 3. The performance results are given in Section 4. Section 5 shows the research efforts that are related to ours. We describe the limitations of the OSP framework in Section 6. Finally, conclusions and future works are given in Section 7. ...
... Section 3. The performance results are given in Section 4. Section 5 shows the research efforts that are related to ours. We describe the limitations of the OSP framework in Section 6. Finally, conclusions and future works are given in Section 7. ...
DNS Security Considerations and the Alternatives to BIND
... (Authoritative for Zone, the SOA), and Resolving Name Servers (resolver, caching, or to answer recursion DNS queries) [7]. In the presentation “Securing an Internet Name Server” by Cricket Liu (http://www.verisigngrs.com/dns/securing_an_internet_name_server.pdf), he has demonstrated the splitservice ...
... (Authoritative for Zone, the SOA), and Resolving Name Servers (resolver, caching, or to answer recursion DNS queries) [7]. In the presentation “Securing an Internet Name Server” by Cricket Liu (http://www.verisigngrs.com/dns/securing_an_internet_name_server.pdf), he has demonstrated the splitservice ...
bca502 : core – 19 : operating systems
... b) system storage state c) operating system d) resources Answer: a 63) . A memory buffer used to accommodate a speed differential is called a) stack pointer b) cache c) accumulator d) disk buffer Answer:b 64) . Which one of the following is the address generated by CPU? a) physical address b) absolu ...
... b) system storage state c) operating system d) resources Answer: a 63) . A memory buffer used to accommodate a speed differential is called a) stack pointer b) cache c) accumulator d) disk buffer Answer:b 64) . Which one of the following is the address generated by CPU? a) physical address b) absolu ...
1764-UM001 - Rockwell Automation
... The illustrations, charts, sample programs and layout examples shown in this guide are intended solely for purposes of example. Since there are many variables and requirements associated with any particular installation, Allen-Bradley does not assume responsibility or liability (to include intellect ...
... The illustrations, charts, sample programs and layout examples shown in this guide are intended solely for purposes of example. Since there are many variables and requirements associated with any particular installation, Allen-Bradley does not assume responsibility or liability (to include intellect ...
Vulnerability Detection in Device Drivers
... dreams, keeping always a smile for me when we were face to face in different computer screens and receiving me with wide arms open every time I arrived home. This work was my desert crossing! “Space Shuttle Discovery (…) is one of the orbiters from NASA's Space Shuttle program and the third of five ...
... dreams, keeping always a smile for me when we were face to face in different computer screens and receiving me with wide arms open every time I arrived home. This work was my desert crossing! “Space Shuttle Discovery (…) is one of the orbiters from NASA's Space Shuttle program and the third of five ...
OperatingSystems_FA15_4_Threads
... thread to service the request. Data sharing between threads handling requests faster than using kernel message queues. Foreground/Background: Spreadsheet process could display menus and read user input. Another thread execute commands and updates the spreadsheet. Asynchronous: Word processor writes ...
... thread to service the request. Data sharing between threads handling requests faster than using kernel message queues. Foreground/Background: Spreadsheet process could display menus and read user input. Another thread execute commands and updates the spreadsheet. Asynchronous: Word processor writes ...
ch4
... On a system with a single computing core, concurrency means that the execution of the threads will be interleaved over time. On a system with multiple cores, however, concurrency means that some threads can run in parallel, because the system can assign a separate thread to each core ...
... On a system with a single computing core, concurrency means that the execution of the threads will be interleaved over time. On a system with multiple cores, however, concurrency means that some threads can run in parallel, because the system can assign a separate thread to each core ...
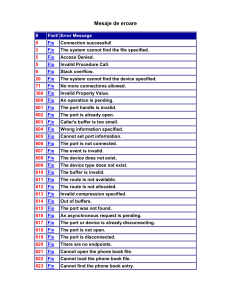
Mesaje de eroare
... Network Address Translation (NAT) is currently installed as a 782 N/A routing protocol, and must be removed before enabling Internet Connection Sharing Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disc ...
... Network Address Translation (NAT) is currently installed as a 782 N/A routing protocol, and must be removed before enabling Internet Connection Sharing Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disc ...
AdvancedSQLInjection
... Audit Log – Logging every query sent by the application allows identifying and analyzing attacks after they occur, and are important for compliance with most security/privacy regulations ...
... Audit Log – Logging every query sent by the application allows identifying and analyzing attacks after they occur, and are important for compliance with most security/privacy regulations ...
1763-UM001 - Rockwell Automation
... The examples and diagrams in this manual are included solely for illustrative purposes. Because of the many variables and requirements associated with any particular installation, Rockwell Automation, Inc. cannot assume responsibility or liability for actual use based on the examples and diagrams. N ...
... The examples and diagrams in this manual are included solely for illustrative purposes. Because of the many variables and requirements associated with any particular installation, Rockwell Automation, Inc. cannot assume responsibility or liability for actual use based on the examples and diagrams. N ...
Operating Systems: Internals and Design Principles (2
... FreeBSD is a widely used system that incorporates many state-of-the-art features. Solaris is a widely used commercial version of UNIX. • Linux: An open-source version of UNIX that is now widely used. These systems were chosen because of their relevance and representativeness. The discussion of the e ...
... FreeBSD is a widely used system that incorporates many state-of-the-art features. Solaris is a widely used commercial version of UNIX. • Linux: An open-source version of UNIX that is now widely used. These systems were chosen because of their relevance and representativeness. The discussion of the e ...