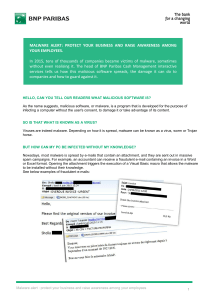
MALWARE ALERT: PROTECT YOUR BUSINESS AND RAISE
... they can spy on your firm. But to get straight to the most important point, I'll mention the three main threats that are likely to strike businesses today: transfer fraud, extortion of funds and data theft. Transfer fraud In this case, the malware creates a beneficiary account on your online banking ...
... they can spy on your firm. But to get straight to the most important point, I'll mention the three main threats that are likely to strike businesses today: transfer fraud, extortion of funds and data theft. Transfer fraud In this case, the malware creates a beneficiary account on your online banking ...
This is a printed page that we have put on our
... directly attached. This allows the scanner to become a "shared scanner." RemoteScan is then installed on the Windows Terminal Services / Citrix Server, and any other computer or Thin Client appliance where a user needs to access the shared scanner. For RemoteScan to function properly, it is necessar ...
... directly attached. This allows the scanner to become a "shared scanner." RemoteScan is then installed on the Windows Terminal Services / Citrix Server, and any other computer or Thin Client appliance where a user needs to access the shared scanner. For RemoteScan to function properly, it is necessar ...
IPSEC Presentation
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
... • A collection of protocols for securing Internet Protocol (IP) communications by encrypting and authenticating all IP packets1 • Progressive standard • Defined in RFC 2401 thru 2409 • Purpose: – To protect IP packets – To provide defense against network attacks 1: From wikipedia.org ...
Chapter 3
... Let's say your computer looks like it is infected by a virus or by adware, but a scan doesn't reveal anything. The solution might lie in a rootkit. A Rootkit is a technology which hides itself and other programs and prevents their detection. ...
... Let's say your computer looks like it is infected by a virus or by adware, but a scan doesn't reveal anything. The solution might lie in a rootkit. A Rootkit is a technology which hides itself and other programs and prevents their detection. ...
Security Tools: Superscan 3 Superscan is a program that scans a
... port scan are displayed. Any messages that are sent back from the machine are also displayed along with what port and service it came from. ...
... port scan are displayed. Any messages that are sent back from the machine are also displayed along with what port and service it came from. ...
Network Adapters - Microsoft Center
... File and Print Hyper-V server virtualization Virtual Private Network (VPN) – SSTP support ...
... File and Print Hyper-V server virtualization Virtual Private Network (VPN) – SSTP support ...
Malicious Software
... trapdoor, is a hidden feature or command in a program that allows a user to perform actions he or she would not normally be allowed to do. • When used in a normal way, this program performs completely as expected and advertised. • But if the hidden feature is activated, the program does something un ...
... trapdoor, is a hidden feature or command in a program that allows a user to perform actions he or she would not normally be allowed to do. • When used in a normal way, this program performs completely as expected and advertised. • But if the hidden feature is activated, the program does something un ...
Windows Rootkit Overview
... The term rootkit originally referred to a collection of tools used to gain administrative access on UNIX operating systems. The collection of tools often included well-known system monitoring tools that were modified to hide the actions of an unauthorized user. An unauthorized user would replace the ...
... The term rootkit originally referred to a collection of tools used to gain administrative access on UNIX operating systems. The collection of tools often included well-known system monitoring tools that were modified to hide the actions of an unauthorized user. An unauthorized user would replace the ...
IIS 7.0: a robust Web & Application Server
... Windows PowerShell New Command-line shell & Scripting Language ...
... Windows PowerShell New Command-line shell & Scripting Language ...
Essentials of Security
... Containing the Effects of the Attack Shut down affected servers Remove affected computers from the network Block inbound and outbound network traffic Take precautionary measures to protect ...
... Containing the Effects of the Attack Shut down affected servers Remove affected computers from the network Block inbound and outbound network traffic Take precautionary measures to protect ...
A+ Guide to Software, 4e - c-jump
... If necessary upgrade hardware and software If BIOS is not current, flash your BIOS Backup files and scan for viruses If drive is compressed, uncompress the drive Inset the Windows XP Upgrade CD Select the upgrade type and Select the partition to install Windows XP ...
... If necessary upgrade hardware and software If BIOS is not current, flash your BIOS Backup files and scan for viruses If drive is compressed, uncompress the drive Inset the Windows XP Upgrade CD Select the upgrade type and Select the partition to install Windows XP ...
View the graphic
... Cisco Advanced Malware Protection (AMP) helps you: • Discover, investigate, analyze, block, and remediate advanced malware outbreaks and advanced persistent threats (APTs) • Speed response times and automate remediation to prevent future attacks, mitigate damage, and eliminate the risk of reinfectio ...
... Cisco Advanced Malware Protection (AMP) helps you: • Discover, investigate, analyze, block, and remediate advanced malware outbreaks and advanced persistent threats (APTs) • Speed response times and automate remediation to prevent future attacks, mitigate damage, and eliminate the risk of reinfectio ...
The Taidoor Campaign: An In-Depth Analysis
... The binary downloads but does not execute files from the C&C server. ...
... The binary downloads but does not execute files from the C&C server. ...
lesson08
... – A Web-based tool for managing and distributing software updates that resolve known security vulnerabilities or otherwise improve performance. – For Microsoft Windows XP, Windows Vista, Microsoft Windows Server 2003, and Windows Server 2008 operating systems. – The latest version of WSUS (WSUS 3.0 ...
... – A Web-based tool for managing and distributing software updates that resolve known security vulnerabilities or otherwise improve performance. – For Microsoft Windows XP, Windows Vista, Microsoft Windows Server 2003, and Windows Server 2008 operating systems. – The latest version of WSUS (WSUS 3.0 ...
Word Template
... management system providing key inputs such as infected machine/user, bot name, bot actions (such as communication with command & control and spam sending), amount of data sent/received, infection severity and more. In addition, the solution includes a comprehensive ThreatWiKi enabling security team ...
... management system providing key inputs such as infected machine/user, bot name, bot actions (such as communication with command & control and spam sending), amount of data sent/received, infection severity and more. In addition, the solution includes a comprehensive ThreatWiKi enabling security team ...
IT TECHNICIAN – JOB SPECIFICATION
... including software checks, firmware upgrades etc. to ensure the smooth running of the Company IT infrastructure. ...
... including software checks, firmware upgrades etc. to ensure the smooth running of the Company IT infrastructure. ...
Abstract - Compassion Software Solutions
... attacks emerge as spoofed E-Mails appearing as legitimate ones which make the users to trust and divulge into them by clicking the link provided in the E-Mail. Detection of malicious URLs and identification of threat types are critical to thwart these attacks. Knowing the type of a threat enables es ...
... attacks emerge as spoofed E-Mails appearing as legitimate ones which make the users to trust and divulge into them by clicking the link provided in the E-Mail. Detection of malicious URLs and identification of threat types are critical to thwart these attacks. Knowing the type of a threat enables es ...
Defending Office 365 Against Denial-of-Service Attacks
... Microsoft is a large and common target for hackers and other malicious individuals. In fact, for the last several years, Microsoft has been continuously and persistently under some form of cyber-attack. At just about any given time, at least one of Microsoft’s Internet properties is experiencing som ...
... Microsoft is a large and common target for hackers and other malicious individuals. In fact, for the last several years, Microsoft has been continuously and persistently under some form of cyber-attack. At just about any given time, at least one of Microsoft’s Internet properties is experiencing som ...
Sentinel SuperPro™
... SuperPro allows you to use the Advanced Encryption Standard (AES) to secure your applications. Support for the AES-based algorithm engine enables use of this industry leading algorithm to generate unique query/responses. AES fortifies your defenses against today’s most common hacking threats such as ...
... SuperPro allows you to use the Advanced Encryption Standard (AES) to secure your applications. Support for the AES-based algorithm engine enables use of this industry leading algorithm to generate unique query/responses. AES fortifies your defenses against today’s most common hacking threats such as ...
Get a WIF of this!
... President TejadaNET Software Consultant Author, Trainer & Speaker Microsoft Influencer & CSD Advisor 10+ years experience Architecture SIG CS Degree Stanford University ...
... President TejadaNET Software Consultant Author, Trainer & Speaker Microsoft Influencer & CSD Advisor 10+ years experience Architecture SIG CS Degree Stanford University ...
Slides - Channel 9
... Apps are deployed to User or Device Groups as required or available: Required – Apps are targeted to users or devices Available - Available Apps are deployed to the user in the Company Portal App ...
... Apps are deployed to User or Device Groups as required or available: Required – Apps are targeted to users or devices Available - Available Apps are deployed to the user in the Company Portal App ...