powerpoint
... 70% of developers participate in the FLOSS community “to learn and develop new skills” 67% of developers participate in the FLOSS community “to share … knowledge and skills” 30% of developers participate in the FLOSS community “to improve … job opportunities” Over 50% of developers derive inco ...
... 70% of developers participate in the FLOSS community “to learn and develop new skills” 67% of developers participate in the FLOSS community “to share … knowledge and skills” 30% of developers participate in the FLOSS community “to improve … job opportunities” Over 50% of developers derive inco ...
Fujitsu`s Security Technology Based on Practical Knowledge
... too complex since it takes a long time to investigate and understand the situation, or because it is not clear what the necessary actions are to be taken against the detected problems. Behavioral-based detection is designed to identify suspicious phenomena, and it involves probable false positives. ...
... too complex since it takes a long time to investigate and understand the situation, or because it is not clear what the necessary actions are to be taken against the detected problems. Behavioral-based detection is designed to identify suspicious phenomena, and it involves probable false positives. ...
1 Introduction
... Stealth – Some viruses try to trick anti-virus software by intercepting its requests to the operating system. The virus can then return an uninfected version of the file to the antivirus software, so that it seems that the file is “clean”. Self-modification – Most modern antivirus programs try to fi ...
... Stealth – Some viruses try to trick anti-virus software by intercepting its requests to the operating system. The virus can then return an uninfected version of the file to the antivirus software, so that it seems that the file is “clean”. Self-modification – Most modern antivirus programs try to fi ...
RAS
... Accessing a Terminal Server from a Client • Terminal Services client computers can log on using the Remote Desktop Connection (RDC) client • The general steps to start RDC in Windows Vista or Windows Server 2008 are as follows: – Click Start, point to All Programs, and click Accessories – Click Rem ...
... Accessing a Terminal Server from a Client • Terminal Services client computers can log on using the Remote Desktop Connection (RDC) client • The general steps to start RDC in Windows Vista or Windows Server 2008 are as follows: – Click Start, point to All Programs, and click Accessories – Click Rem ...
Build Secure Network Infrastructure and Reduce Risks and Losses
... Due to the flexible policies of the IPS 5500, the solution can be deployed at any number of key areas in the network infrastructure, providing perimeter security, protection of critical servers, remote access and extranet entry points, and inter-departmental segmentation. Corero provides powerful po ...
... Due to the flexible policies of the IPS 5500, the solution can be deployed at any number of key areas in the network infrastructure, providing perimeter security, protection of critical servers, remote access and extranet entry points, and inter-departmental segmentation. Corero provides powerful po ...
Chapter 1
... The attacker attempts to breach a web application. Common attacks of this type are SQL injection and Cross ...
... The attacker attempts to breach a web application. Common attacks of this type are SQL injection and Cross ...
Guide to Operating System Security
... Programs that replicate on the same computer or send themselves to many other computers Can open a back door ...
... Programs that replicate on the same computer or send themselves to many other computers Can open a back door ...
How to Detect Zero-Day Malware And Limit Its Impact
... giving them a platform to test their malware samples against and ensure that they can’t be detected. Some people choose not to use antivirus systems at all, saying that they create a false sense of security. “Good luck with that,” Thompson says, pointing out that majority of malware out in the wild ...
... giving them a platform to test their malware samples against and ensure that they can’t be detected. Some people choose not to use antivirus systems at all, saying that they create a false sense of security. “Good luck with that,” Thompson says, pointing out that majority of malware out in the wild ...
Minimum Standards for ICT Infrastructure and
... is in compliance with minimum or standard versions specified in this document e) Local Area Network Compliance - Ensure that network is built using managed Fast or Gigabit Ethernet switches and compliant with cabling requirements. Ensure that a country office is in compliance with network standards, ...
... is in compliance with minimum or standard versions specified in this document e) Local Area Network Compliance - Ensure that network is built using managed Fast or Gigabit Ethernet switches and compliant with cabling requirements. Ensure that a country office is in compliance with network standards, ...
Forcepoint™ Stonesoft® Next Generation Firewall
... techniques to network traffic, identifying applications and users at a granular level so that security policies can be applied according to business rules. Then it performs specialized deep packet inspection, including advanced techniques such as full stack normalization and horizontal data stream-b ...
... techniques to network traffic, identifying applications and users at a granular level so that security policies can be applied according to business rules. Then it performs specialized deep packet inspection, including advanced techniques such as full stack normalization and horizontal data stream-b ...
Internet Vulnerabilities & Criminal Activity
... Image the hard drive on site Transport computer to lab and image the hard drive Examine image in a lab environment ...
... Image the hard drive on site Transport computer to lab and image the hard drive Examine image in a lab environment ...
BitDefenDer Active virus control:
... The driver for the increase in the volume and complexity of malware has been money. In the past, viruses were created by teenagers in order to earn notoriety; today, malware is created by criminals to earn a living. And there are substantial sums to be made. Spam, phishing, pump-anddump schemes and ...
... The driver for the increase in the volume and complexity of malware has been money. In the past, viruses were created by teenagers in order to earn notoriety; today, malware is created by criminals to earn a living. And there are substantial sums to be made. Spam, phishing, pump-anddump schemes and ...
From Russia with Love: Behind the Trend Micro
... considered “lifestyle” or “productivity” applications such as Microsoft™ Office®, Adobe® Flash®, Java™, and others that aid in viewing websites or processing documents. We chose Microsoft Office 2007 because of its perceived user base. I then downloaded the most recent version of Flash and Java sinc ...
... considered “lifestyle” or “productivity” applications such as Microsoft™ Office®, Adobe® Flash®, Java™, and others that aid in viewing websites or processing documents. We chose Microsoft Office 2007 because of its perceived user base. I then downloaded the most recent version of Flash and Java sinc ...
Unit OS7: Windows Security Components and Concepts
... runs inside Lsass and responds to Microsoft LAN Manager 2 Windows NT (pre-Windows 2000) network logon requests Authentication is handled as local logons are, by sending them to Lsass for verification Netlogon also has a locator service built into it for locating domain controllers WinLogon MSGINA ...
... runs inside Lsass and responds to Microsoft LAN Manager 2 Windows NT (pre-Windows 2000) network logon requests Authentication is handled as local logons are, by sending them to Lsass for verification Netlogon also has a locator service built into it for locating domain controllers WinLogon MSGINA ...
CV (Word) - OoCities
... verification, client liaison, Excel spreadsheet programming & macros, data presentation, data cleansing & integrity checking. West Sussex County Council (9/04 – 4/06) 3 months initial, multiple extensions totalling a year and a half. Ended due to funding cutbacks. Systems Administrator. Administrate ...
... verification, client liaison, Excel spreadsheet programming & macros, data presentation, data cleansing & integrity checking. West Sussex County Council (9/04 – 4/06) 3 months initial, multiple extensions totalling a year and a half. Ended due to funding cutbacks. Systems Administrator. Administrate ...
Unit 27: Planning and Maintaining a Microsoft Windows
... To include: • Plan a DNS namespace design • Plan zone replication requirements • Plan a forwarding configuration • Plan for DNS security • Examine the interoperability of DNS with ...
... To include: • Plan a DNS namespace design • Plan zone replication requirements • Plan a forwarding configuration • Plan for DNS security • Examine the interoperability of DNS with ...
Integrate and Accelerate Endpoint Threat Defense
... methods to keep their endpoints—and data—safe. Even worse, explosive growth in endpoints and mobility have opened new potential attack vectors for cybercriminals and new places for malware to hide. In attempt to head off every potential point of weakness, many organizations now rely on a patchwork o ...
... methods to keep their endpoints—and data—safe. Even worse, explosive growth in endpoints and mobility have opened new potential attack vectors for cybercriminals and new places for malware to hide. In attempt to head off every potential point of weakness, many organizations now rely on a patchwork o ...
Global Information Assurance Certification (GIAC) develops and administers the premier
... (GSE). For good reason. It’s the most prestigious, most demanding certification in the information security industry. The GSE’s performancebased, hands-on nature sets it apart from any other certification in the IT security industry. Those who earn the GSE master the wide variety of skills, across m ...
... (GSE). For good reason. It’s the most prestigious, most demanding certification in the information security industry. The GSE’s performancebased, hands-on nature sets it apart from any other certification in the IT security industry. Those who earn the GSE master the wide variety of skills, across m ...
Unit OS7: Windows Security Components and Concepts
... runs inside Lsass and responds to Microsoft LAN Manager 2 Windows NT (pre-Windows 2000) network logon requests Authentication is handled as local logons are, by sending them to Lsass for verification Netlogon also has a locator service built into it for locating domain controllers WinLogon MSGINA ...
... runs inside Lsass and responds to Microsoft LAN Manager 2 Windows NT (pre-Windows 2000) network logon requests Authentication is handled as local logons are, by sending them to Lsass for verification Netlogon also has a locator service built into it for locating domain controllers WinLogon MSGINA ...
Lesson 11a - Malicious Software (Malware)
... Bot and Botnet • Case study: Storm Botnet • By Sep 2007 running on between 1 and 50 million computers worldwide (at one point 8% of all Windows malware) • Vector was XSS – used phishing to get users to activate Web link • Used in variety of criminal activities, including DDOS and spam • Has displaye ...
... Bot and Botnet • Case study: Storm Botnet • By Sep 2007 running on between 1 and 50 million computers worldwide (at one point 8% of all Windows malware) • Vector was XSS – used phishing to get users to activate Web link • Used in variety of criminal activities, including DDOS and spam • Has displaye ...
FAKEM RAT: Malware Disguised as Windows Messenger and
... After exploitation, an .EXE file packed with UPX is dropped.6 After initially dropping the malicious file named hkcmd.exe to the %Temp% folder, the malware typically copies itself using the name, tpframe.exe, to the %System% folder. It then adds the following registry entry to enable its automatic e ...
... After exploitation, an .EXE file packed with UPX is dropped.6 After initially dropping the malicious file named hkcmd.exe to the %Temp% folder, the malware typically copies itself using the name, tpframe.exe, to the %System% folder. It then adds the following registry entry to enable its automatic e ...
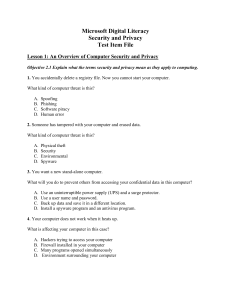
Question Info
... Objective 4.1 Explain the purpose of different security settings on your computer. 45. Jim discovers that his son visits Web sites that are inappropriate for his age. Jim wants to restrict access to these sites. Which of the following security settings will help Jim to block these sites? A. B. C. D. ...
... Objective 4.1 Explain the purpose of different security settings on your computer. 45. Jim discovers that his son visits Web sites that are inappropriate for his age. Jim wants to restrict access to these sites. Which of the following security settings will help Jim to block these sites? A. B. C. D. ...
Tenable Malware Detection
... newly created malware that does not register on traditional security products. SCCV leverages direct vulnerability scans, passive network monitoring and log collection and correlation to find sophisticated attacks. Host assessment detects malicious processes running on the host. Direct assessment al ...
... newly created malware that does not register on traditional security products. SCCV leverages direct vulnerability scans, passive network monitoring and log collection and correlation to find sophisticated attacks. Host assessment detects malicious processes running on the host. Direct assessment al ...
yosemite server backup
... Data encryption protects your data at-rest, and data compression makes the most of your media. With heterogeneous support for disk-to-disk backup, tape drives, tape autoloaders, robotic tape libraries, and CD/DVD, Yosemite Server Backup offers industry-leading backup performance by supporting concur ...
... Data encryption protects your data at-rest, and data compression makes the most of your media. With heterogeneous support for disk-to-disk backup, tape drives, tape autoloaders, robotic tape libraries, and CD/DVD, Yosemite Server Backup offers industry-leading backup performance by supporting concur ...